Introduction
This chapter analyzes IoT threats from the perspective of protocols. According to the data from NSFOCUS’s threat hunting system, Telnet services (port 23) were targeted most frequently1. Therefore, we first analyze the attacks launched via Telnet. WS-Discovery reflection attacks are a new type of DDoS reflection attacks emerging in 2019 and will be described in section 4.3 WS-Discovery. In the 2018 Annual IoT Security Report, we analyzed UPnP-based reflection attacks. In this document, we update related data and add some new findings.
Telnet
Viewpoint 4: IoT devices, especially cameras and routers, were the major targets of Telnet bruteforcing. Meanwhile, with a pickup in cryptocurrency prices, attackers are inclined to divert compromised devices to cost-efficient cryptomining activities for the purpose of quickly cashing in on network resources under their control.
Telnet brute-forcing is one of the most common attack methods used by the Mirai botnet. Based on the Telnet-related data captured by NSFOCUS’s threat hunting system (from March 2019 to October 2019), we analyzed the activity and geographical locations of attack sources, their device types based on open ports, and then weak passwords to find out the reason why these devices were compromised.
Activity of Attack Sources
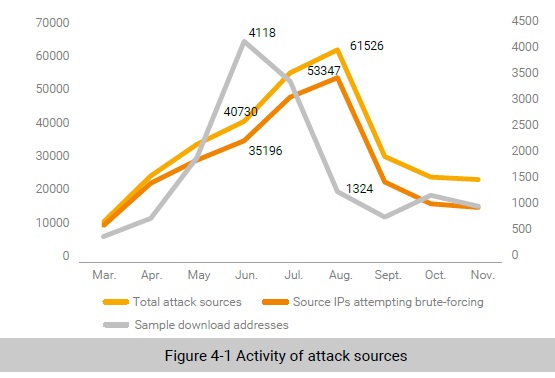
The logs record all Telnet-related malicious activities and IP addresses, each of which represents an attack source. According to our statistics, there were a total of 118,527 attack sources. Figure 4-1 shows the activity of attack sources over a nine-month period. As shown in the figure, Telnet exploits increased month by month in 2019. August saw the most attack sources, reaching 61,526, including 53,347 involved in brute-forcing. Most sample downloads (4118) occurred in June. Overall, attack sources were on the decline in the latter half of 2019.
Global Distribution of Attack Sources
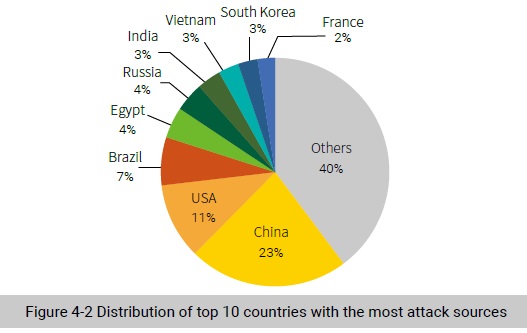
We analyzed attack sources from the geographical perspective and obtained top 10 countries with the most attack sources, as shown in Figure 4-2. Apparently, China and the USA took top two spots.
Distribution of Open Ports Used by Attack Sources
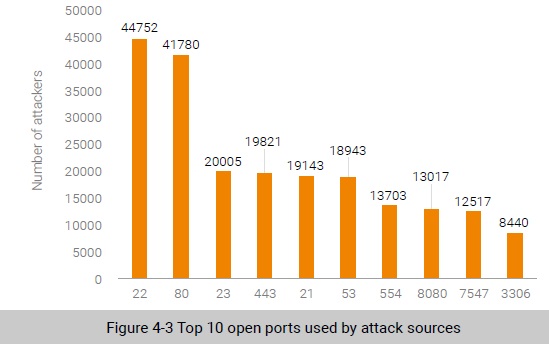
Most IoT devices exposed on the Internet have ports 22 and 23 open for providing services, which invites more security risks to these ports. Therefore, we conducted an analysis of open ports used by attack sources. As shown in Figure 4-3, top 10 open ports were 22, 80, 23, 443, 21, 53, 554, 8080, 7547, and 3306. Attack sources exposing ports 22 and 23 accounted for 55% of all attack sources. Therefore, it can be inferred that many attack sources were compromised after suffering brute-force attacks.
Distribution of Device Types Exploited to Launch Attacks
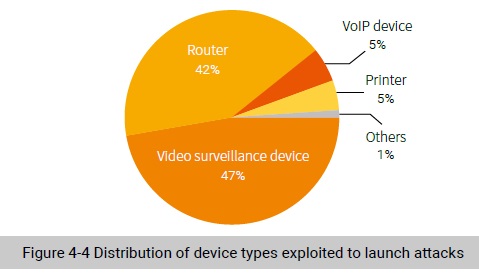
According to the asset intelligence data available on NTI, 22% of attack sources were IoT devices. As shown in Figure 4-4, video surveillance devices (47%) and routers (42%) dominate the types of such IoT devices. Arguably, they are most easily controlled by threat actors.
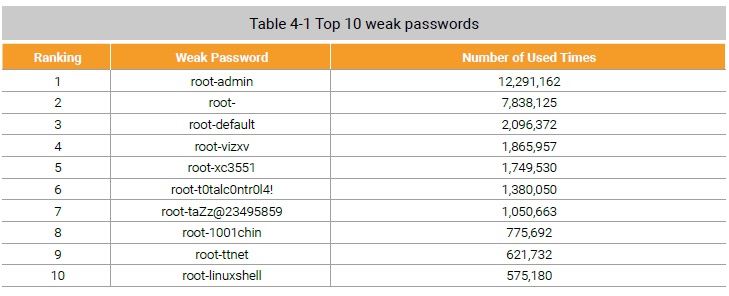
Weak Passwords That Enable Brute-Force Attacks
The weak password “root-vizxv” was found useful for direct login to the background of security surveillance devices from Dahua; “root t0talc0ntr0l4!” was the default access credential of smart home devices of Control4; “root-taZz@23495859” was one of the weak passwords most frequently used by Asher, a Mirai variant, to infect routers. We made an analysis of weak passwords tried for bruteforcing and found that many IoT devices were compromised because of using weak passwords. As listed in Table 4-1, in addition to some common weak passwords, IoT device-related weak passwords mentioned above made it into top 10.
Attack Behaviors
By clustering attack behaviors performed by threat actors that used Telnet extensively for intrusion and conducting a correlative analysis of the related list of weak passwords and malicious samples, we identified a botnet that mined Monero. This botnet first broke into a host by cracking a weak password and then planted an RSA public key or bot program to gain control privileges before using a downloader to download a Monero cryptomining virus to execute the script matching the host type for malicious cryptomining. In this way, the hacker behind this botnet turned network resources in hand into money.
According to a rough estimate, this botnet controlled around 10 thousand zombies and was found most active in July in which the highest recorded number of zombies hit nearly 600 in a single day in 2019.
Most zombies resided in China (2119) and the USA (1335). A total of 6681 zombies opened port 22, making up 65% of the total. According to asset intelligence, 12% of these zombies were identified as IoT devices, with routers and cameras as dominant players. As for weak passwords, this botnet used nprocnproc most frequently. While related samples can no longer be downloaded from the sample server, the botnet displays an increasing level of activity, though rather slowly.
To be continued.
