Attackers are targeting Citrix ADC (Application Delivery Controller) and utilize it to launch amplification attacks. However, no official patch has been released yet.
“Since 19 December 2020 7pm CET we see a possible worldwide DDOS amplify attack against Citrix Gateway UDP:443 DTLS EDT services.†wrote Hofmann, a German IT system administrator. Many other victims also claimed the same attack.
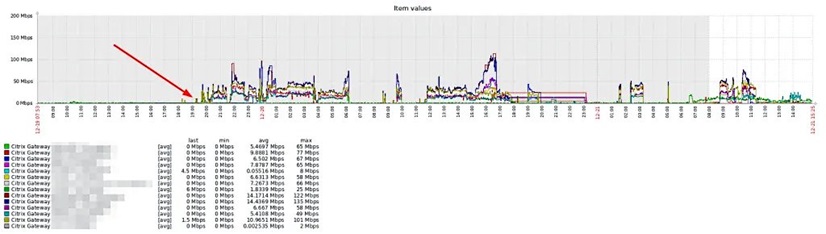
(source:Marco Hofmann)
Citrix has confirmed the DTLS Amplification DDoS attack impacting Citrix ADC on 12 Dec 2020. According to ZDNet, victims of these DDoS attacks are mostly online gaming services.
Datagram Transport Layer Security (DTLS) is a communications protocol for securing datagram-based applications to prevent eavesdropping, tampering, or message forgery.
On Citrix ADC, DTLS is implemented on EDT(Enlightened Data Transport), which is set to enabled by default.
Just like all UDP-based protocols, DTLS is spoofable and can be used as a DDoS amplification vector. For past DDoS attacks, the amplification factor of DTLS was known to be 4 or 5 times the original packet. But Hofmann reported the DTLS implementation on Citrix ADC devices reaches a 36 amplification factor.
Attack Impact & Temporary Mitigation
Citrix published an advisory says “As part of this attack, an attacker or bots can overwhelm the Citrix ADC DTLS network throughput, potentially leading to outbound bandwidth exhaustion. The effect of this attack appears to be more prominent on connections with limited bandwidth.â€
Beyond that, what alarms us more is that attackers can send small DTLS packets to the Citrix ADC and get way larger packets to a spoofed IP address (the DDoS attack victim).
Citrix plans to release a version on 12 Jan, 2021 to eliminate the susceptibility to this attack. Before that, a temporary action is suggested.
Disable DTLS on a ADC by issuing the following command:
set vpn vserver -dtls OFF
The company adds “Disabling the DTLS protocol may lead to limited performance degradation to real time applications using DTLS in your environment. The extent of degradation depends on multiple variables. If your environment does not use DTLS, disabling the protocol temporarily will have no performance impactâ€.
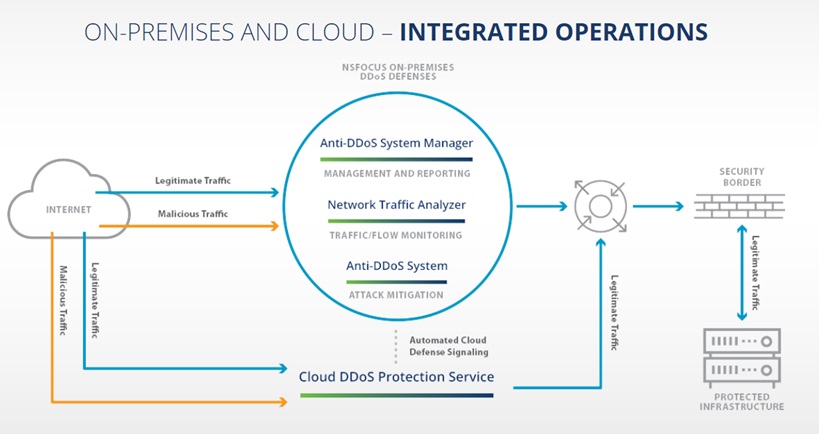
NSFOCUS Escorts Your Security
The industry’s leading NSFOCUS Anti-DDoS solution can effectively protect against DTLS amplification attacks and ensure your network stability and service availability.
NSFOCUS customers can customize DDoS attack alert rules on Network Traffic Analyser(NTA)to realize real-time detection and alert of DTLS amplification attacks.
NTA can divert the malicious traffic to Anti-DDoS System (ADS) for mitigation.
The protection action on ADS could be set as drop, drop and add to blacklist and rate-limiting.