Background
Some time ago, some researchers detected a code injection vulnerability (CVE-2020-7475), which could cause Schneider’s Programmable Logic Controllers (PLCs) to operate like worms. If successfully exploited, this vulnerability could allow a PLC to act as a mini PC to carry out malicious network activities or as an intranet springboard or a network scanner to penetrate into industrial systems in a more covert manner.
Design Flaw
The vulnerability is caused by obvious design flaws. The following paragraphs will elaborate on the root cause of the vulnerability from the perspective of configuration program design in Siemens and Schneider PLCs.
Siemens PLCs
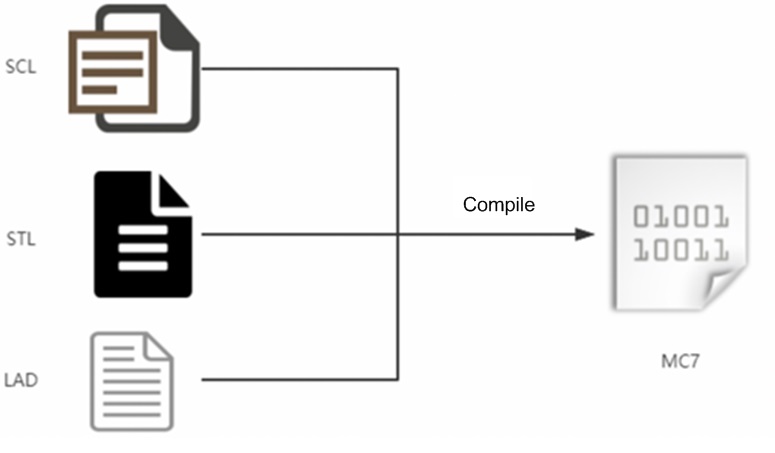
Siemens S7 PLCs provide different ways of PLC configuration programming, such as schematic expression in the Ladder Diagram (LAD) or Function Block Diagram (FBD), Pascal-like Structured Control Language (SCL), and assembly-like Statement List (STL). Regardless of the types of input sources, the PLC program will be compiled into MC7 bytecode, an even lower-level representation of STL.
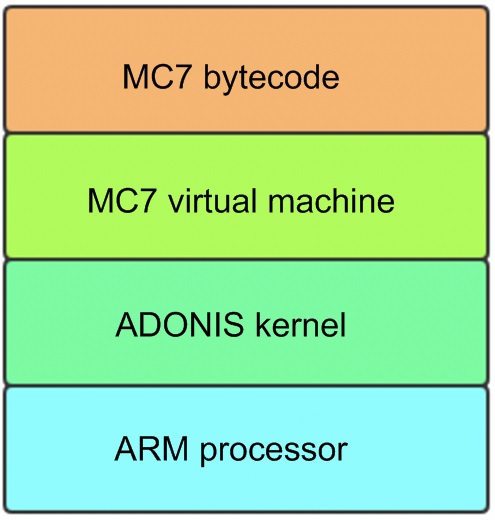
After being compiled by configuration software, project files (in MC7 format) are downloaded and installed into a PLC via Siemens’s S7COMM/S7COMM-PLUS protocol. Then, the MC7 virtual machine in the PLC will dispatch the files and interpret and execute MC7 bytecode. Since the virtual machine can restrict the resources accessed by programs, the complied bytecode can only be used for access to the resources provided by the virtual machine rather than direct hardware operation, such as establishing Transmission Control Protocol (TCP) connections via TCON and TDISCON in FB blocks to send and receive data. This is to say, complied configuration programs are capable of launching malicious network activities.
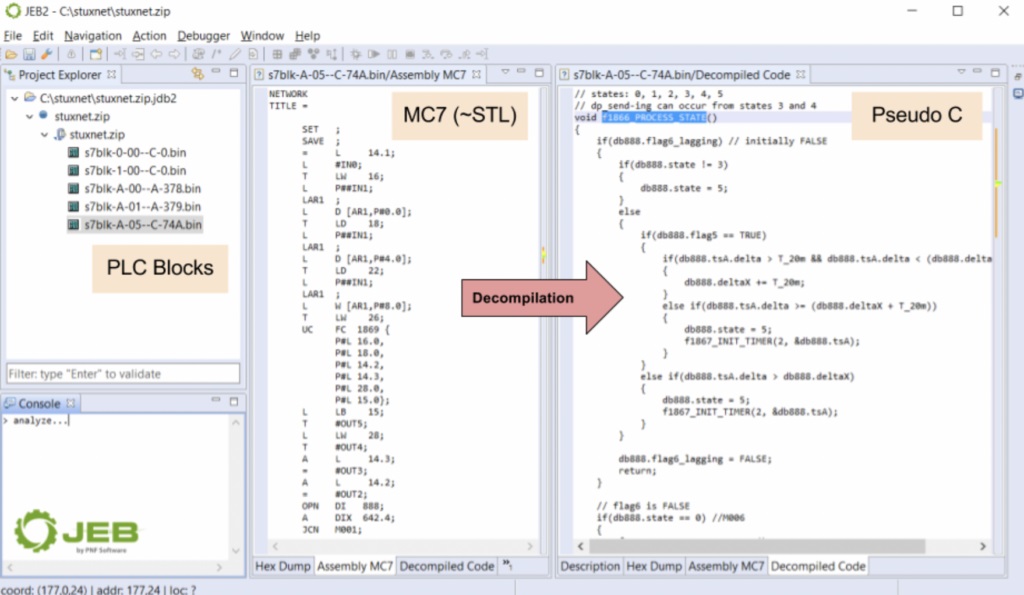
Siemens does not document MC7 bytecode, of which assembly instructions can only be understood upon reverse engineering. Fortunately, a JEB plug-in has been developed to disassemble and even decompile MC7 files to figure out code logic in configuration programs. This works especially well in analyzing Stuxnet and other worm viruses targeting Siemens devices.
Schneider PLCs
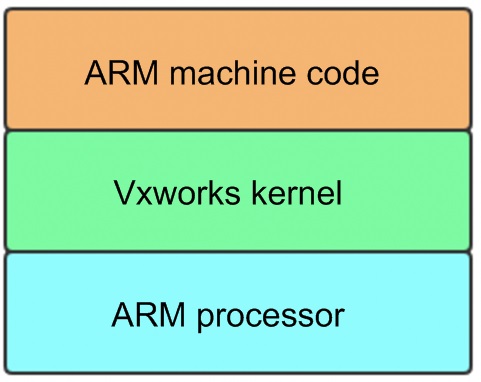
In Schneider PLCs, the Ladder Diagram (LAD), Structured Text (ST), and FBD are compiled into Architecture Reference Manual (ARM) machine code that is directly executed by an ARM processor, thus providing full access to both software and hardware resources in the PLCs.
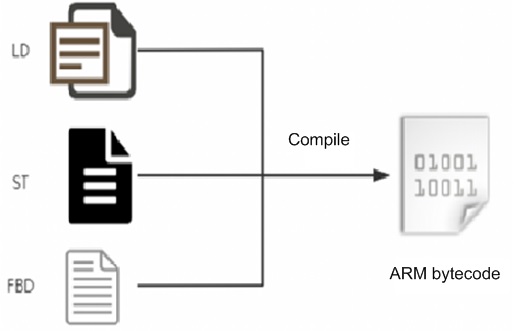
After being compiled by configuration software of Schneider, project files can be directly downloaded and installed into a PLC via Schneider’s ModBus 90 function code (UMAS protocol). After being enabled, the PLC will execute the compiled ARM machine code. If injecting malicious code into ARM bytecode, attackers can totally control the PLC and gain control over the access to critical resources, such as the network, file system, and hardware IO.
Vulnerability Details
The root cause of the vulnerability is that Schneider PLCs directly compile configuration programs into ARM machine code and do not restrict the resources accessed by the programs during code execution. Therefore, worm viruses targeting Schneider PLCs may be more covert and destructive.
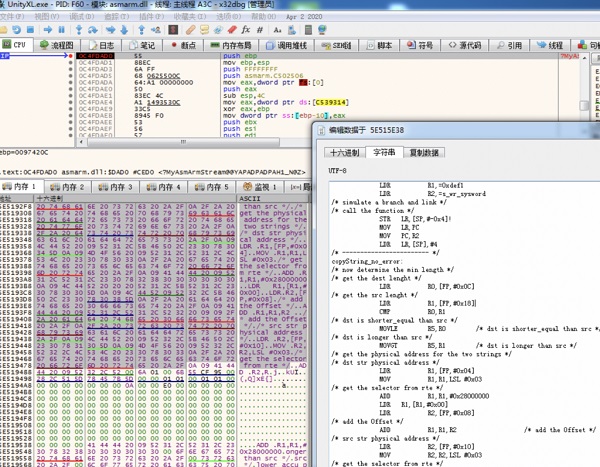
Unity Pro Reverse Engineering
Unity Pro is configuration programming software designed for Schneider PLCs. Places for code compilation should be first found to inject code into the compiled ARM code. As shown in the following figure, the exported function MyAsmArmStream of asmarm.dll compiles ARM assembly code into ARM machine code.
When the first parameter of the function points to the ARM assembly string, the compiled ARM machine code data is returned:
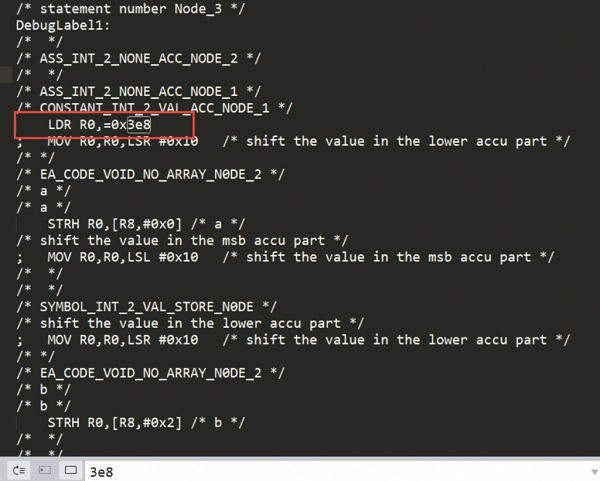
Test code can be written to locate the code written by users in ARM assembly.
The code generated will definitely contain the immediate operand 1000 (0x3e8). Find the immediate operand, and you will quickly locate user code in configuration programs and obtain corresponding assembly code.
Hook the function and modify the uploaded assembly code, and you can execute arbitrary code in Schneider PLCs.
Code Writing
Schneider PLCs use Vxworks operating system, which provides the functions needed. All that is needed is to find the function addresses (such as network access, account management, and file access) in the firmware and directly invoke the functions in ARM assembly.
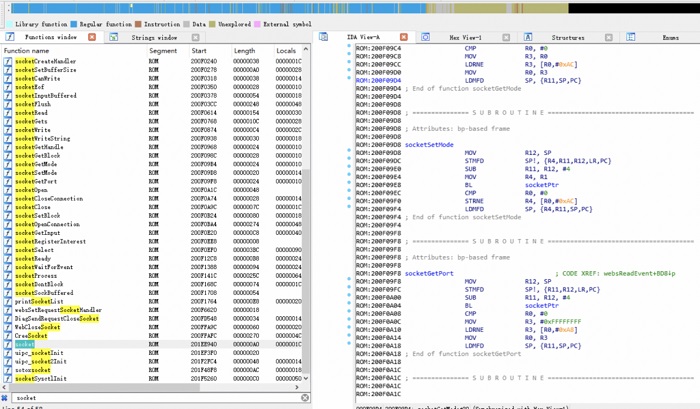
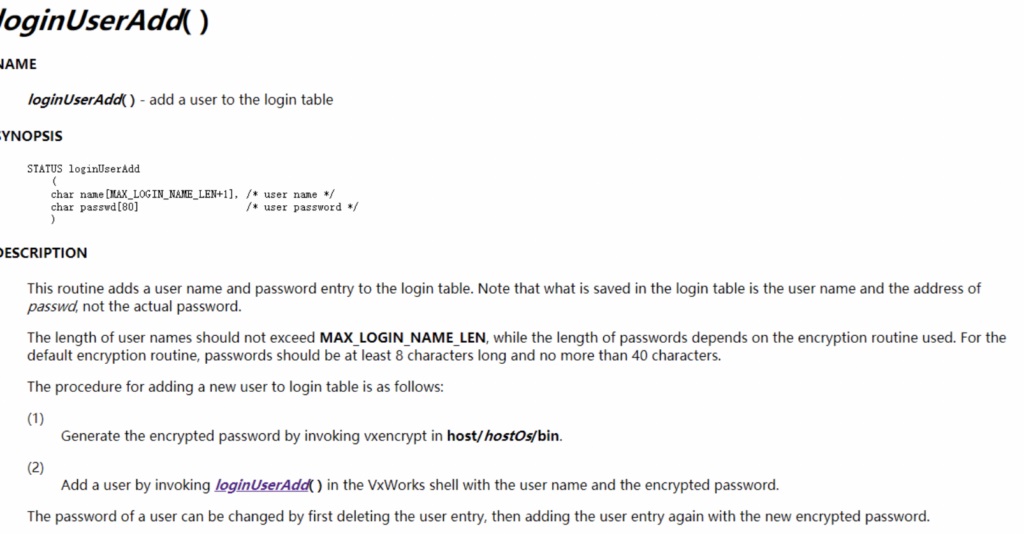
Documents about prototypes of these functions are available on the official website. All that is needed is to construct parameters properly before invocation. For example, the loginUserAdd function in the following figure allows adding an account. Attackers could add a backdoor account to a PLC via the function.
Exploitation Procedure
- Rename the original asmArm.dll to asm_Arm.dll to facilitate invoking the custom dynamic-link library (DLL).
- Put malicious asmArm.dll (this DLL mainly hijacks MyAsmArmStream, modifies the uploaded ARM assembly code, and invokes the original asmArm.dll) into the Unity file folder.
- Run Unity and load the PLC project.
- Recompile the project.
- Stop PLCs.
- Upload the project to the PLCs.
- Malicious code will be executed after PLCs are started.
Vulnerability Fixing
Schneider has released a security advisory that provides security patches and recommendations. Repair of the SCADA mainly involves the check of the integrity of components. If a certain component is modified, the software will not be started and must be reinstalled.
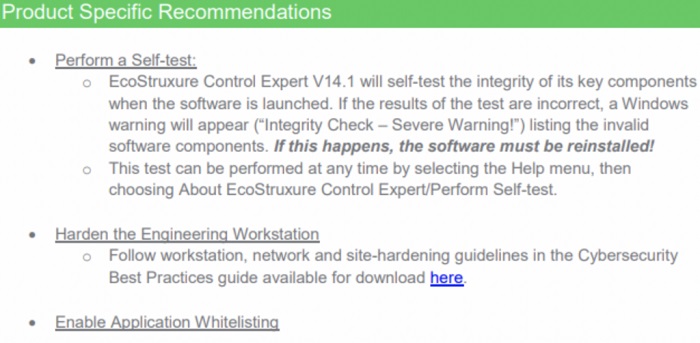
Strictly speaking, this is only a mitigation measure. Since many techniques could bypass security checks, it is not easy to repair design flaws by means of software.
Summary
The article mainly discusses the root cause of the vulnerability (CVE-2020-7475) affecting Schneider’s PLCs and briefly describes the vulnerability principle and some ideas about vulnerability exploitation. Predictably, it is not easy to eradicate the vulnerability, and it is possible to work around the vulnerability via other technical methods. This also indicates that security needs to be considered in the implementation and preliminary design of industrial control systems and throughout the whole life cycle.
Reference link:
