Vulnerability Description
On November 5, local time, Squid officially released a security bulletin to fix multiple vulnerabilities, including a high-risk buffer overflow vulnerability that could lead to code execution (CVE-2019-12526), ​​an information disclosure vulnerability (CVE-2019-18679) And HTTP request splitting problem (CVE-2019-18678).
Squid is a popular open source Internet proxy and web caching application. It can be used to reduce bandwidth usage and demand on web servers, filter network traffic, and accelerate web access by caching common resources locally. Squid supports a variety of network protocols, including HTTP, FTP, and Gopher. Squid supports proxy forwarding. Clients on the internal network connect to servers on the external network through Squid. Clients on the reverse proxy external network connect to servers on the internal network through Squid.
CVE-2019-12526: This vulnerability allows a remote attacker to write large amounts of arbitrary data to the heap due to incorrect buffer management, which may result in arbitrary code execution. On systems with memory access protection, the Squid process may be terminated abnormally, causing a denial of service to all clients that use the proxy.
CVE-2019-18679: Due to incorrect data management, Squid may leak information when processing HTTP digest authentication. The leaked information will weaken ASLR protection and may help attackers to implement remote code execution attacks.
CVE-2019-18678: Squid is prone to HTTP request splitting due to incorrect message parsing, with relatively low risk and impact.
References:
http://www.squid-cache.org/Advisories/SQUID-2019_11.txt
http://www.squid-cache.org/Advisories/SQUID-2019_10.txt
http://www.squid-cache.org/Advisories/SQUID-2019_7.txt
Scope of Impact
Affected Versions
- Squid 3.0 <= 3.5.28
- Squid 4.x <= 4.8
Unaffected Versions
- Squid = 4.9
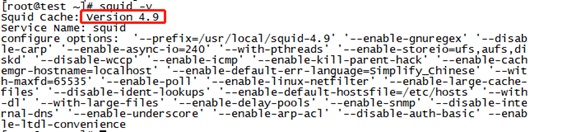
Vulnerability Detection
Manual Detection
The user can use the command squid –v to view the currently installed version.
There may be a risk if the current version is within the affected range.
Mitigation
The above vulnerability has been fixed in the latest version, and affected users should upgrade to Squid 4.9 as soon as possible.
Official link: http://www.squid-cache.org/Versions/
The installation command is as follows:
| wget http://www.squid-cache.org/Versions/v4/squid-4.9.tar.gz
tar -zxvf squid-4.9.tar.gz cd squid-4.9 ./configure make && make install |
The screenshot of the successful installation is as follows:
Other Protective Measures
If the relevant users are temporarily unable to upgrade, the following measures can also be used to protect the corresponding vulnerabilities.
- The patch corresponding to the installation vulnerability
| VCVE No. | Patch download link |
| CVE-2019-12526 | http://www.squid-cache.org/Versions/v4/changesets/squid-4-7aa0184a720fd216191474e079f4fe87de7c4f5a.patch |
| CVE-2019-18678 | http://www.squid-cache.org/Versions/v4/changesets/squid-4-671ba97abe929156dc4c717ee52ad22fba0f7443.patch |
| CVE-2019-18679 | http://www.squid-cache.org/Versions/v4/changesets/squid-4-671ba97abe929156dc4c717ee52ad22fba0f7443.patch |
Note: If you are using a pre-packaged version of Squid, please contact the package vendor for confirmation.
- Take protective measures against the vulnerability
CVE-2019-12526:
Reject urn: protocol URI that is represented by all clients
acl URN proto URN
http_access deny URN
CVE-2019-18679:
(1) Remove the “auth_param digest …” setting from the configuration file squid.conf.
(2) Add the parameter –disable-auth-basic when compiling Squid
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.