As an increasing mature technical system in the security domain, DevSecOps, in nature, inherits the concept of shifting security to the left during the security development lifecycle (SDL). Simply speaking, DevSecOps is capability integration, continuous learning, and cultural blending. In fact, the concept of “blending” is also reflected by the theme of the DevSecOps Day at RSAC 2019, namely, “DevOps Connect”. The concept calls for CI/CD (continuous integration and continuous delivery and effective measurement to improve the efficiency.
At RSA Conference 2019, cultural blending and various conflicts are focal topics of speakers. Conflicts include the conflict between the red team culture and developers, conflict between technical and non-technical staff (including functional departments, such as the HR department), and conflict between managers and those that are managed. For example, the red team tends to create a “surprise” (disclosing high-risk vulnerability without providing a solution) and obtain “confidential information” (namely, the red team covering for privacy data theft), which can hardly be accepted by developers and organizations.
Cultural conflict
A large number of practitioners have recognized the cultural conflicts brought by the implementation of DevSecOps and actively try to solve this problem, with cultural transformation as an importance means. In this context, Larry Maccherone put forward the Dev[Sec]Ops manifesto at RSA Conference 2019 as follows:
- We should create the security but not just rely on the security.
- In addition to security experts, we should rely on empowered engineering teams.
- We should securely perform functions but not just security function.
- We should study continuously, but not advance behind closed doors.
- We should take some special or general best practices rather than “pseudo” comprehensive measures.
- We should take cultural changes as a basis, but not merely rely on rules and regulations.
The establishment and transformation of cultures require not only the use of such means as training and publicity, and conference communication, but also a reshuffle of the organization. For example, instead of building a closed department, we should build an open organization by integrating security personnel into every development team. This makes the personnel with security capabilities well distributed in business, development, and operation and maintenance (O&M) fields. As a result, DevSecOps can really create values, avoiding becoming an efficiency bottleneck.
Automation and measurement are also important during the resolution of conflicts. As the speaker pointed out, automating everything simple allows us to focus on complex things. According to this principle, enterprises can gradually establish and carry out the implementation roadmap and milestones of DevSecOps by improving the automation and integration of “simple fields” and focusing on complex business issues (business knowledge, organization, and management and control process).
| Milestone | |
| 3 months | Deploy and implement the CI/CD process. |
| Reassess the current security tools and focus on automation and integration. | |
| Research on every team and assess the gaps together with these teams. | |
| 6 months | Automate and integrate the penetration test and API test. |
| Improve the enterprise’s organization, for example, by assigning security personnel into each development team. |
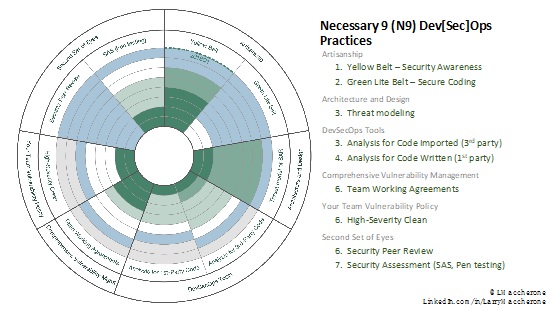
At RSA Conference 2019, we can see that the measurement mechanism is widely used by organizations and speakers who put DevSecOps into practice. The advantage of the measurement mechanism is that the efficiency improvements can be quantified, which is an effective way to reduce conflicts. As for the implementation roadmap and measurement concept of DevSecops, Larry Maccherone came up with nine necessary practices and seven stages of cultural acceptance.
The nine necessary practices are:
- Security awareness
- Secure coding
- Threat modelling
- Analysis of imported code from a third party
- Analysis of code written
- Team working agreements
- High-severity clean
- Security peer review
- Security assessment
Nine key DevSecOps practices
The Nnine key practices are divided into seven stages, which are intuitively displayed with different colors, indicating the practice and acceptance of DecSecOps in the organization. This provides the enterprise with a landscape of its security development capability and development status, thereby laying a good foundation for continuous and in-depth improvement in the future.
Seven stages from resistance to cultural integration
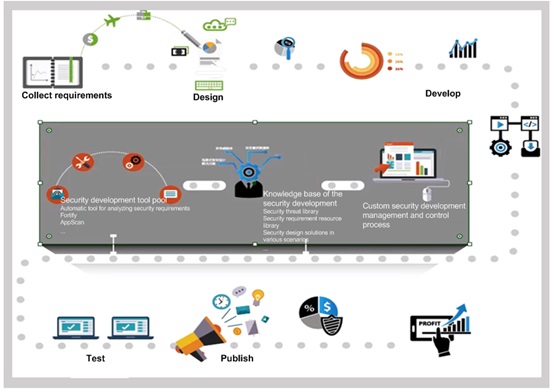
Based on years of practical experience in finance, enterprise, and carrier industries, the NSFOCUS security team has summarized the following five key success factors for enhancing the ability of organizational security development based on DevSecOps:
- Security development management and control process
- Security development knowledge base and tools
- Security personnel
- Metrics and evaluation indicators
- Continuous optimization
Based on the preceding success factors, the NSFOCUS security team has designed a security development capability improvement service methodology and framework based on SDL and DevSecOps. In addition, the security development capability platform is built to aid the implementation of security services, thereby integrating, managing, and controlling various security development resources:
- Integrating DevOps tool chains, such as Jenkins and Gitlab.
- Customizing and sorting out six code auditing tools and over 3000 rules.
- Expert-level knowledge base
- Threat modeling-based threat library
- Security requirement library with 900+ requirements, covering application security, communication security, system deployment and O&M security, and typical business security scenarios.
- Security design library covering 82 scenarios and 540 security designs.
The security development capability platform allows us to maximally advance the management and control time, thereby solving the code security issue at the continuous integration stage and reducing organizations’ security capability requirements for development, security, and operations personnel. In addition, NSFOCUS has experienced security service consultants to provide onsite guidance, assisting enterprises in building the cross-platform security culture and processes and finally forming a closed loop of security development.
About the DevSecOps Community
DevSecOps vendors
DevSecOps readings
DevSecOps poster, available at the following link: https://www.devsecopsdays.com/resources/devsecopoly-board-poster-v01)