This section analyzes WS-Discovery reflection attacks. For details about the WS-Discovery service, see section 1.6 WS-Discovery First Found to Be Abused for DDoS Reflection Attacks.
Viewpoint 5: Since security researchers from Baidu disclosed that the Web WS-Discovery protocol could be exploited for DDoS reflection attacks, there has been a notable increase in reflection attack events based on this protocol in the latter half of 2019. Since mid-August, WS-Discovery reflection attacks captured by us had been on the rise. Worse still, September witnessed a sharp increase in such attacks. All parties concerned, including security vendors, service providers, and telecom carriers, should pay due attention to this type of threats.
Exposure of the WS-Discovery Service
To accurately delineate WS-Discovery reflection attacks, we, on the one hand, surveyed the WSDiscovery service exposed on the Internet, and on the other hand, used NSFOCUS’s threat hunting system to detect WS-Discovery reflection attacks. Data obtained using the two methods is analyzed respectively in the following sections.
Finding 6: Around the world, about 910,000 IP addresses (80% of which (730,000) were video surveillance devices) provided the WS-Discovery service and were thus at risk of being exploited to launch DDoS attacks.
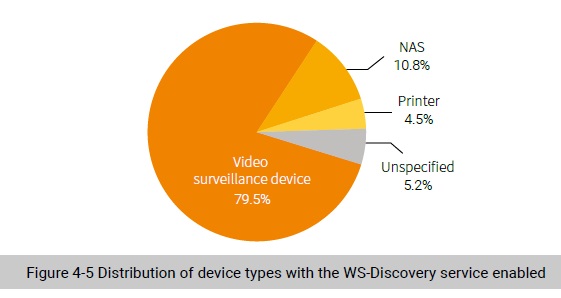
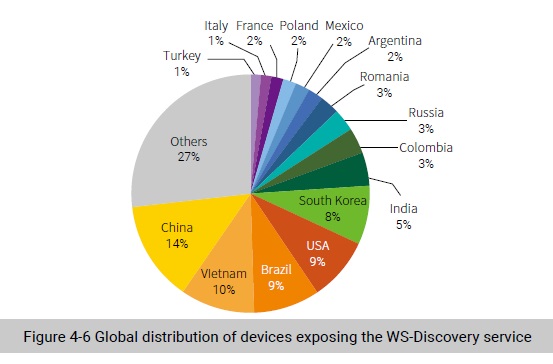
As shown in Figure 4-6, the top 5 countries with the most devices that had the WS-Discovery service enabled were China, Vietnam, Brazil, the USA, and South Korea.
About 24% of devices responded to WS-Discovery request packets via a random port other than 3702, posing a new challenge to traditional DDoS protection based on source port filtering.
According to A10 Networks’ WS-Discovery security research report 35, about 46% of devices respond via a random port. According to our data, about 24% of devices did not respond to WS-Discovery requests via port 3702. Besides, we found that not all of these ports were random and some of them were repeatedly used (such as port 1024).
Responding via a random port poses a great challenge to the mitigation mechanism of WS-Discovery reflection attacks. Unlike the mitigation policy for other reflection attacks, WS-Discovery reflection attacks cannot be prevented simply by creating a rule for blocking traffic from source port 3702.
WS-Discovery Reflection Attacks
In this section, through analysis of log messages generated by NSFOCUS’s threat hunting system over a 74-day period from July 10 to September 21, 2019, we will delve into the threat situation of WSDiscovery reflection attacks from three dimensions: attack vector, attack event, and victim.
Attack Vectors
In this section, we will analyze attack vectors used by attackers from the perspective of attack payload length. In a blog post, we have discussed the distribution of source ports of attack traffic and the distribution of victims’ IP addresses by network segment.
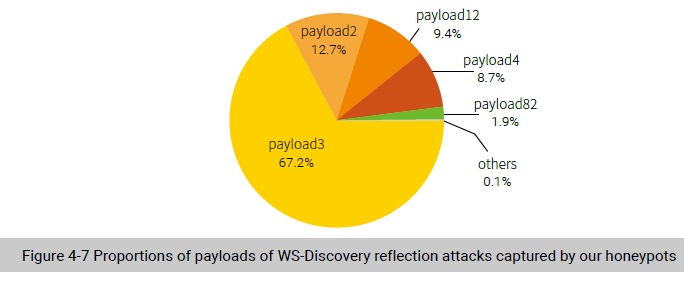
Finding 7: During a WS-Discovery reflection attack, attackers usually try to craft very short payloads to hit the target, instead of using legitimate service discovery packets as attack payloads. Most attack payloads contain only three bytes, registered in two-thirds of attack log messages. The average bandwidth amplification factor achieved by such payloads was 443.
Figure 4-7 shows our statistics on packet payloads indicated in WS-Discovery reflection attack log data. In order not to make attack packets known to other hackers, we name attack payloads by using the attack length. For example, if an attack packet’s application-layer length is three bytes, we name it payload3. According to our statistics, the top 5 payloads together represented over 99% of all attack traffic. We also found that none of these five types of payloads were legitimate service discovery packets and the smallest ones contained only two bytes. Most attack payloads contained three bytes, accounting for about two-thirds of the total attack packets.
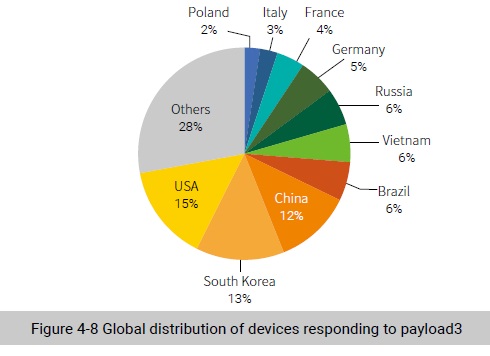
A network-wide probe of payload3 packets revealed that not all WS-Discovery services responded to them. Altogether there were 28,918 IP addresses responding to these requests.
Figure 4-8 shows the global distribution of devices responding to payload3. We can see that the top 3 countries hosting the most responding devices were the USA, South Korea, and China. In terms of device types, video surveillance devices and printers dominated, with the former accounting for 75% of the total devices.
Response packets captured by our honeypots varied from hundreds to thousands of bytes in length, averaging out at 1330 bytes. Thus, the average bandwidth amplification factor (BAF) stood at 443.
Attack Incidents
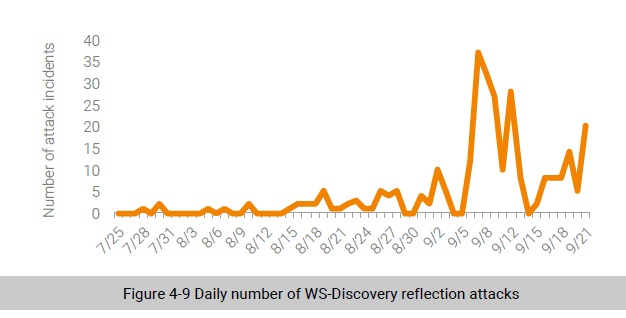
We analyzed attack incidents captured by NSFOCUS’s threat hunting system. Here, all attack records about one IP address in one day add up to an attack incident. Figure 4-9 shows the daily number of attack incidents. At a glance, WS-Discovery reflection attack incidents fluctuated all the time, but have been on the rise generally since mid-August, especially in September. This indicates that WS-Discovery reflection attacks have been gradually adopted as a regular weapon of DDoS attacks, to which all parties concerned, including security vendors, service providers, and telecom operators, should pay due attention.
Victims
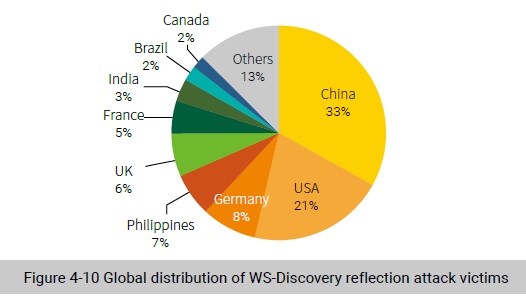
Figure 4-10 shows the global distribution of WS-Discovery reflection attack victims. We observed that up to 24 countries and regions were hit by this kind of attack. China was most targeted by WS-Discovery reflection attacks, home to 33% of victim IP addresses, followed by the USA (21%).
To be continued.
