In 2019, ransomware was still a major type of threats that haunted people around the world. As an infamous botnet family, GandCrab generated more than USD 2 billion in ransom payments, simulating the rapid increase of other ransomware.
Overview
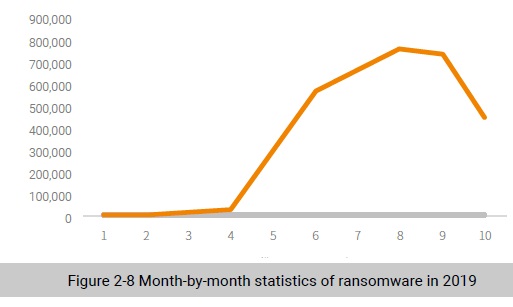
Figure shows the number of ransomware captured by NSFOCUS Security Labs in each month in 2019. We can see that August saw a rapid increase.
Most ransomware demand payments in cryptocurrency. Figure 2-9 illustrates the trend of Bitcoin prices in 2019.
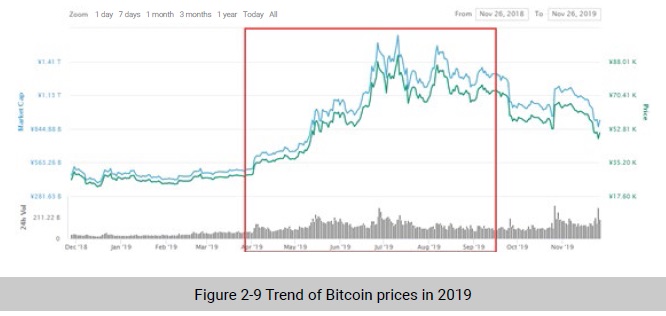
As shown in Figure 2-9, the Bitcoin price rose rapidly from early April and dwindle from September. This trend is consistent with the quantitative distribution of captured ransomware. Therefore, NSFOCUS Security Labs concluded that the prevalence of ransomware had something to do with the value of cryptocurrency.
In 2019, NSFOCUS Security Labs found that its captured ransomware spread mainly through weak password cracking and auxiliary means such as phishing emails, spam, and deceptive links.
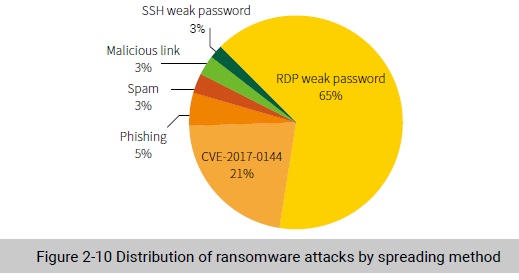
In addition, some ransomware families propagate themselves via botnets (such as banking Trojans). This makes up for poor mobility of ransomware and implements attacks in a more targeted way via banking Trojans.
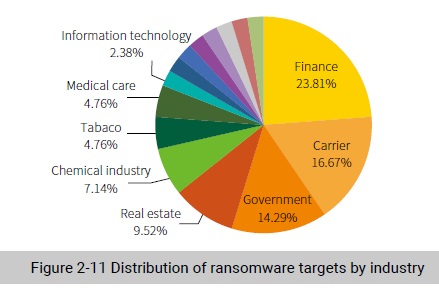
According to statistics on ransomware attack targets, 15 industries were infected with ransomware, including finance, telecom, and real estate that are highly likely to pay ransom.
Three prominent families, GlobeImposter, GandCrab, and WannaCry, were extremely active and had far more variants than others.
GandCrab made its debut in early 2018. After this ransomware wreaked havoc in a reckless and manner for one year and a half, the organization behind this ransomware announced that it stopped operations in June 2019. Prior to that, this organization alleged/claimed that he had earned a high ransom and legalized the income. GandCrab’s outrageous behavior is an overt provocation to jurisdictions and other hackers began to follow suit.
Sodinokibi shares great similarities with GandCrab in the code structure and so regarded as the successor of the latter.
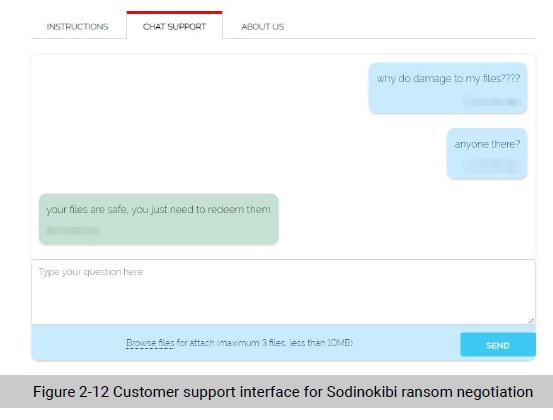
After encryption, a ransom note is displayed, asking the user to visit the dark web or a specific website to contact related personnel and pay the requested Bitcoin ransom.
To our astonishment, the website even provides a customer support platform for both parties to negotiate the ransom amount, exhibiting a high level of industrialization.
Ransomware as a Service (RaaS) is maturing, enabling cyber criminals to do evil at an increasingly low cost. Moreover, inspired by their predecessors who have been successful in getting rich quick, more people are attracted to this lucrative business, giving birth to more diversified ransomware.
To be continued.
