POLITICO - GOOGLE EMAIL SECURITY GURU SPEAKS — MC recently caught up with Mark Risher, director of product management at Google with an emphasis on security and privacy. A few highlights: — Election security threats are broader than one country or one group of people, Risher said. “One of the...
Ano: 2018
New Report from NSFOCUS Analyzes 27 Million Attacks in H1 Cybersecurity Insights Report
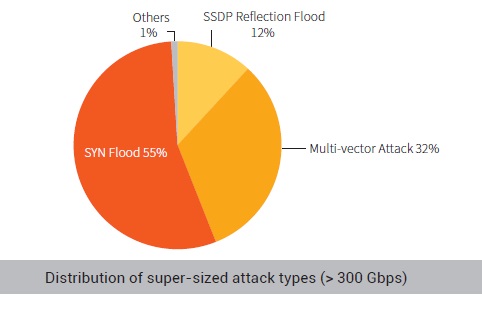
SANTA CLARA, Calif., October 18, 2018 – NSFOCUS, a leader in holistic hybrid security solutions, today released its H1 Cybersecurity Insights report, which highlights the observations of the NSFOCUS Threat Intelligence center, a security research organization created by NSFOCUS for implementing an intelligent security 2.0 strategy and improving the cybersecurity...
XBash Malware Security Advisory
On September 17, 2018, Unit42 researchers published an analysis of a new malware family XBash on its official blog. According to them, XBash was developed by the Iron Group, a cybercrime organization that has been active since 2016. The malware was named XBash based on the name of the malicious...
Git RCE Vulnerability (CVE-2018-17456)Security Advisory
1 Vulnerability Overview Recently, the Git project disclosed CVE-2018-17456, a vulnerability in Git that can cause arbitrary code execution when a user clones a malicious repository. An attacker can take control of a target host by exploiting this vulnerability and at the same time using social engineering methods such as...
NuggetPhantom Analysis Report
1.1 Executive Summary In a recent emergency response activity, NSFOCUS Threat Intelligence center (NTI) discovered a security event that featured NuggetPhantom, a modularized malware toolkit. According to our observation, the organization behind this event made its debut at the end of 2016 in the blue screen of death (BSOD) event...
Thoughts on the Application of the Micro Honeypot System in the Financial Sector
Overview According to the Emerging Technology Analysis: Deception Techniques and Technologies Create Security Technology Business Opportunities released by Gartner in 2015, "Deception technologies are defined by the use of deceit and/or feints designed to thwart or throw off an attacker's cognitive processes, disrupt an attacker's automation tools, delay an attacker's...