1 Vulnerability Overview
Recently, a security researcher found a logical bug in WinRAR using the WinAFL fuzzer and exploited it to gain full control over a victim’s computer. An attacker could exploit this vulnerability by crafting an archive and then tricking victims into downloading it by means of a phishing email, net disk, or forum. When a victim opens this malicious file with WinRAR, the attack is complete.
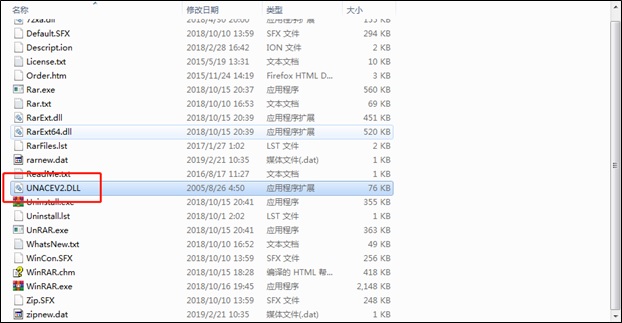
The vulnerability exists in UNACEV2.dll in WinRAR, which does not properly sanitize file names when decompressing .ace files, leading to directory traversal. This indicates that an attacker could write a malicious file to an arbitrary path, thus making it possible to plant a backdoor trojan. This vulnerability has been in WinRAR for more than 19 years. Now WinRAR has to completely stop supporting the vulnerable format (.ace).
WinRAR is a Windows data compression/decompression tool that can be used to create and view RAR or ZIP compression files and decompress files of various compression formats. As the most popular compression tool, WinRAR has more than 500 million users around the world.
Reference link:
https://research.checkpoint.com/extracting-code-execution-from-winrar/
2 Scope of Impact
- Affected versions:
WinRAR < 5.70 Beta 1
- Unaffected versions:
WinRAR 5.70 Beta 1
Our inspection finds that some other compression tools also incorporate UNACEV2.dll and are therefore possibly affected by this vulnerability. Users of these tools should also check for official upgrade notices or delete UNACEV2.dll. Following is an incomplete list of compression tools incorporating UNACEV2.dll.
| Affected Version | |
| Bandizip | < = 6.2.0.0 |
| Haozip (2345) | < = 5.9.8.10907 |
| 360Zip | < = 4.0.0.1170 |
3 Recommended Solution
3.1 Version Upgrade
WinRAR 5.70 Beta 1 deletes UNACEV2.dll so as not to decompress .ace files. Therefore, users can upgrade WinRAR to this version to protect against this vulnerability.
- 32-bit: http://win-rar.com/fileadmin/winrar-versions/wrar57b1.exe
- 64-bit: http://win-rar.com/fileadmin/winrar-versions/winrar-x64-57b1.exe
3.2 Deletion of the Vulnerable File
Users who cannot upgrade to the latest version for the time being can protect against this vulnerability by deleting UNACEV2.DLL from the WinRAR installation directory.
Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.