Chapter 1. Brief on the risk
In phishing email attacks worldwide, Covid-19 is still an important topic. With the increasing availability of epidemic prevention material supplies in various countries and the transparency of news channels, attackers have begun to look for “hot issues” from other perspectives that may attract people’s attention.
With the impact of the pandemic, some companies have also begun to adjust their working systems, including the use of remote working. In this case, some companies need to notify every employee of the revised system and remote office network access methods. Naturally, attackers will not let go of this huge “opportunity”.
Consistent with the trend of real phishing attacks received internally by our company, external phishing attacks are gradually shifting from malicious links to malicious attachments. In order to prevent them from being intercepted by email security products or being checked and killed by anti-virus software on computers, more and more attackers are using a “multi-stage” attack mode, that is, malicious attachments in phishing emails only function for downloading and running malicious files. The actual malicious code is located in malicious files downloaded from the Internet.
In addition to new attack forms, attackers continue to innovate in attack technology. For example, in this quarter, attackers used new “zero font”, “hexadecimal IP address” and other methods to attack external users. In the third chapter of the report, the principles of these new attack techniques will also be discussed.
Chapter 2. Top 3 Real Cases
2.1 Using Covid-19 topics for attraction
The Covid-19 epidemic in many countries continues to be severe. A common practice of phishing email attackers is to use people’s attention to hot topics to carefully construct related phishing emails. Different from other entertainment and sports information, the topic of the pandemic can let everyone pay attention to it in a short time, and can easily trigger stress, panic and other emotions.
When the epidemic just broke out, resources including masks, alcohol, medicine, medical equipment, etc. were all in a short supply. The attackers at the time grasped this issue in time and made up a lot of phishing emails like “Preventive drug procurement”, “Ways to purchase masks” or “Urgent notice on community infectionsâ€, etc. This kind of phishing emails mainly takes advantage of people’s nervousness that is easy to trigger when the available information is incomplete and the material are insufficient, inducing the recipient to click on the malicious Word document in the attachment or directly click on the malicious link. This type of attack is not only aimed at individuals, it is also possible to target companies, and attacks against companies may bring in higher profit for attackers. For example, the following is a new type of phishing email, which is aimed at a medical equipment manufacturer, falsely claiming that it needs to purchase a large amount of goods, and inducing the other party to open the attached file attached.

It contains a malicious Word attachment named “Meducal Inquiry-L.A.B. Equipment.doc”, which exploits the Office formula editor (CVE-2017-11882) vulnerability. Once the recipient believes that it is true and opens it, the document will download a malicious executable file from the address specified by the attacker to further implement attacks such as information theft.
As the epidemic continues to spread, some people have become less sensitive to such news as the medical, pharmaceutical, and protective equipment industries continue to produce prevention equipment and supply problems have been resolved. Now, people can easily buy masks, hand sanitizers and other items, so the previous idea of phishing emails no longer works. However, these difficulties did not prevent attackers from continuing to use this global pandemic. In a phishing email discovered, the attacker spoofed the email with the subject of the “Covid-19 Fund Award”, notifying the recipient that he was selected as the winner of the United NationsCovid-19 Fund, and promised to give a generous reward.
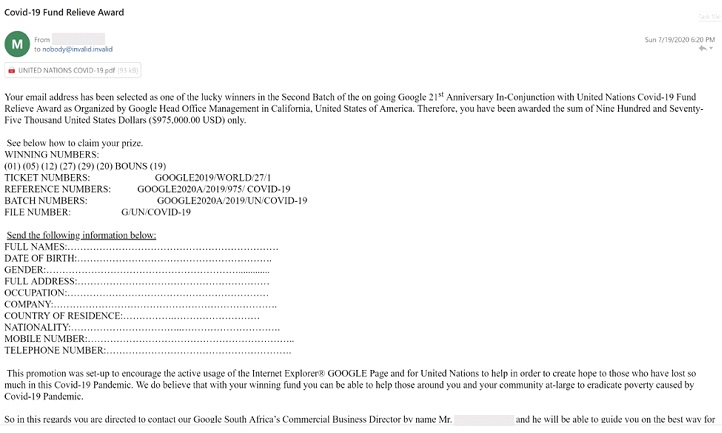
Once the recipient deems it is true, he is possible to actively provide detailed personal information to the attacker. The attacker can use the collected information to carefully design the scam and launch further attacks on the recipient.
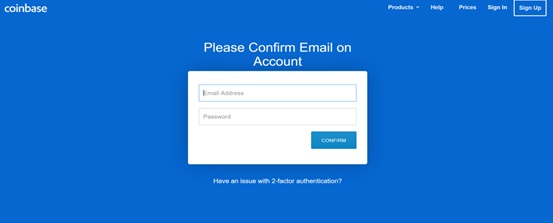
The outbreak of the epidemic has undoubtedly affected the economies of many countries. They have taken measures such as issuing vouchers to restore the economy. The attackers are also paying attention to this. For example, in the phishing email shown in the figure below, the attacker claimed that the user had obtained a $500 “coupon” and asked the user to click the link in the email to receive it.
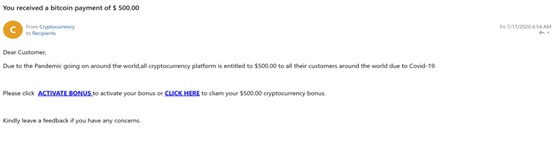
Once the user clicks the link, he will be redirected to a fake page that requires the user to enter the password of the Bitcoin account and email account. Subsequently, the attacker can use the information entered by the user to steal the encrypted currency originally stored in the Bitcoin wallet or log in to the mailbox to carry out further attacks.
In addition to promising bonuses, attackers may also imitate bank notification emails, in the name of providing low-interest loans to users during the epidemic, to attract recipients to open attachments to view detailed information about low-interest loan plans.

In recent years, the use of phishing emails to spread ransomware has also been increasing. In addition, this quarter, a large number of attackers sent phishing emails with the topic of Covid-19. These ransomware viruses may be located in links in the content of the email or in attachments, such as NetWalker, Ransomware-GVZ, and CoViper. In particular, CoViper will rewrite the computer’s master boot record (MBR) before encrypting the data, further reducing the possibility to recover data.
In addition, most ransomware will not provide a real “decryption key” after paying the ransom, and there is basically no way to recover data. Another part of the ransomware will demand high rewards, and some attackers will pretend to be “data recovery company” to provide decryption services, but in fact these so-called “data recovery companies” cooperate with the attackers and use specific decryption keys to decrypt the data.
In general, all kinds of traditional phishing emails are likely to disguise themselves by Covid-19, using people’s nervousness, fear and curiosity to seize topics such as shortage of materials and economic downturn, and attack a large number of individuals and companies. In order to prevent such threats, what we need to do is to remain calm to all changes. Treat all emails related to the epidemic vigilantly and avoid being credulous. For the attachments in the email, it is recommended to use the anti-virus software installed on the computer or the cloud detection service provided by some manufacturers (for example: VirusTotal) to check it before opening it, and avoid opening the files from unknown.
2.2 Counterfeit notification emails from corporate IT or HR departments
Recently, some companies have adjusted their employees’ vacation and work-from-home systems. Some companies have been seriously affected by the economic situation at present, and attackers took this advantage to conduct phishing emails from corporate IT or HR departments.
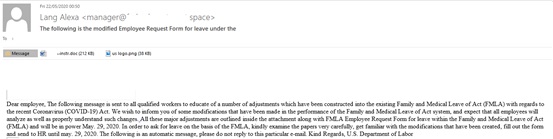
For example, in the following email, the attacker pretended to be an HR department staff and claimed in the text that the US Department of Labor had adjusted the latest policy on maternity leave and sick leave, attaching a Word document and a PNG image file. Once an employee opens the attachment, he will be infected with the virus.
If the analysis of policy adjustments is still difficult to attract everyone’s attention, then another kind of counterfeit email can undoubtedly increase the urgency of the recipient. In this email, the attacker disguised as an HR manager and sent an email titled “YOUR EMPLOYMENT STATUS”. It was stated in the text that due to the economic recession, the company was forced to lay off employees, and employees were required to fill in the attachment form to receive two months’ salary for termination of employment. Obviously, this attached document also contains malware.

In this quarter, common email headers also include:
- Microsoft: Preview your Microsoft 365 Business Basic receipt
- Human Resources Department: Policy update during the epidemic
- IT reminder: remote access method
- Exchange ActiveSync service is disabled
- Human Resources Department: Corporate Profit Report
- Wage deduction table
- Please check the leave application regulations
- Update of remote work plan during the epidemic
- Your team shared with you the “remuneration policy revised during the COVID-19 pandemic” through OneDrive
The above-mentioned phishing emails mainly use the recipient’s concerns about their own interests (including personal itinerary arrangements, company benefits, etc.), or use their curiosity about relevant notification documents to induce employees of the company to click on links or open attachments. In order to prevent such risks, it is necessary to first check whether the sender’s address is from a corporate mailbox when receiving working emails. Don’t trust emails from publicly registered email addresses on the Internet, and don’t trust emails from strange senders. If necessary, you should confirm with the relevant department contact person via telephone or corporate WeChat.
2.3 Macro viruses in malicious Office documents
In the above two types of phishing email cases, malicious Office documents are involved. With the continuous strengthening of the detection mechanism of phishing emails, the hyperlinks contained in the body text are very likely to be intercepted by the mail gateway.
Therefore, attackers are more likely to use malicious attachments to carry out the attacks. The design of malicious attachments is also very special: if a virus is directly carried in a malicious attachment, not only the mail will have a certain probability of being discovered by the anti-virus function of the gateway, but also there will be a certain probability of being killed by installed anti-virus software on the local computer when the recipient opens the attachment.
Therefore, many attackers, including the APT organization, have begun to adopt a “multi-stage” model. For example, the attacker sends an email asking the recipient to view and fill in the attached Word document as soon as possible. Once the user obeys the requirements of the email body and opens the Word document, you will see the following interface.
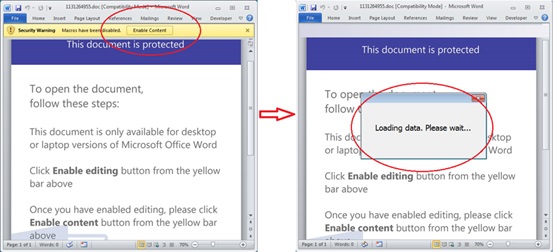
In the Word document, a prompt message of “This document is protected ” is displayed. The user is required to manually click the yellow “Enable Editing” button, and then the “Enable Content” button. In fact, these two steps are carefully designed for the purpose of phishing emails.
In Outlook, the “Trust Center” function is enabled by default, including some security features to prevent malicious Office documents. For example, if the Office file comes from the Internet or is an attachment from an Outlook email, the “Protected View” function is enabled by default, and only allows users to view the general content in the document. You need to manually click “Enable Editing” to view the complete content and perform editing and other operations. In addition, all macros in Office documents are also disabled by default, requiring users to manually click the “Enable Content” button to run the macros.
After understanding the above security features, we have clearly discovered the reason why the attacker asked to click “Enable editing” and “Enable content” in the message.
As far as this email is concerned, after clicking the two buttons, the malicious VBA code contained in the macro will be executed in the backend. The code will download the malicious Trojan from 5 network locations to the local, and then run the Trojan.
The above case is a very typical malicious Office document phishing email.
In this “multi-stage” mode the attacker’s logic is very clear:
1. Use inducing texts in the email subject and body to trick users into opening the attached Office document;
2. Use inducing pictures or texts in Office documents to trick users into enabling Office macro codes;
3. The macro code is responsible for downloading and running malicious files from the URL appointed by the attacker;
4. Once the malicious file runs successfully, the malicious operation designed by the attacker can be executed.
Since the actual function of the attachment is only to download and run the file, it does not contain the typical features of common Trojan viruses. In addition, the macro code of the third step may adopt certain encoding and obfuscation strategies to perform complex obfuscation of external URL addresses. Therefore, such phishing emails may not be detected by mail gateways and anti-virus software.
In order to deal with such threats, we need to pay special attention to avoid opening email attachments from unknown sources, set in the Office “Trust Center”, enable protected views and disable macros by default. In the daily process, pay attention to the “Enable Editing” and “Enable Content” buttons contained in the document, especially to avoid clicking the “Enable Content” button at any time.
Chapter 3. Research on new attack methods
3.1 Use Zero Font to hide specific text in emails
Using “zero font” technology, malicious attackers can hide specific text in emails. HTML is also a commonly used web page format, which supports a very rich style content, but also creates some potential security risks. As more and more emails now begin to adopt HTML format, the original attack methods aimed at website users have also been migrated to the email user community.
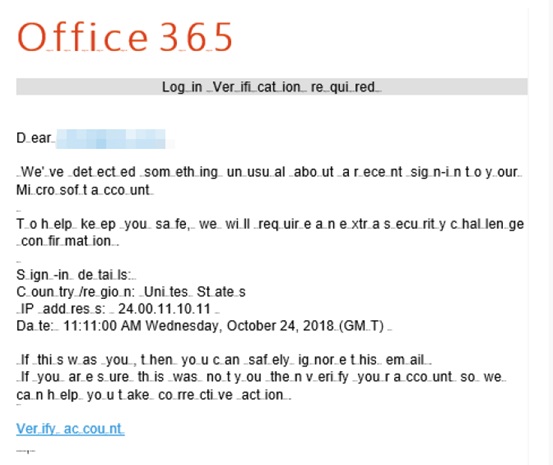
We use a practical case to illustrate this attack method. For example, the following figure shows a typical phishing email that faked as an Office 365 remote login reminder. The email is edited in HTML format.
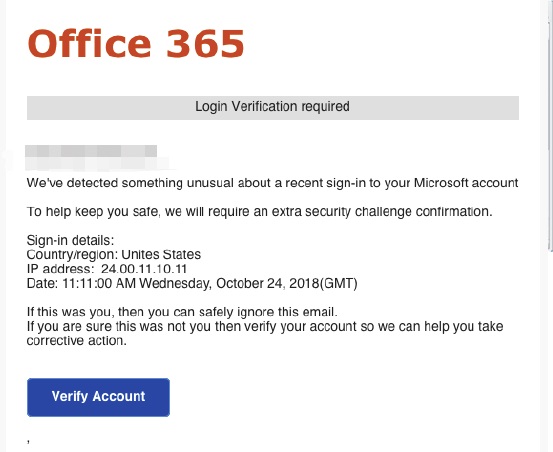
To defend against such phishing emails, the mail gateway can add corresponding filtering rules. For example, if suspicious keywords such as “Office 365”, “verify your account”, and “Login verification” are detected in the email body text, it can be identified as suspicious phishing emails.
But in fact, if an attacker uses zero font technology, this kind of filtering rules that rely on keywords will become invalid. Take the most eye-catching “Office 365” string as an example. If we look at the HTML code in the corresponding position in this phishing email, we can see:
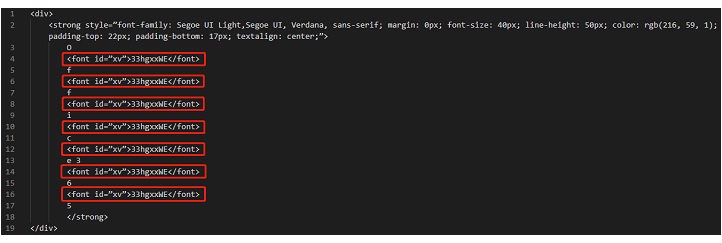
A string of “33hgxxWE” is inserted between each character of the string of “Office 356”, and the font id of the string is “xv”.
In its corresponding CSS style, search for “xv”, you can see the following code:
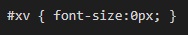
Since the font-size is set to 0px, all “33hgxxWE” strings contained in the body of the email will be displayed as zero pixels. As the name suggests, this is the “zero font” used in this type of attack.
Currently, common mail protection products do not identify based on font size, but only filter based on the actual string content contained in the mail. Therefore, the red “Office 365” that looks very obvious to the recipient will be recognized by some mail protection products as “O33hgxxWEf33hgxxWEf33hgxxWEi33hgxxWEc33hgxxWEe”, which obviously does not trigger the keyword rule.
From the perspective of email protection products, this phishing email, which is faked as an Office 365 remote login reminder, is similar to the following format:
From this case, we can see that as email security products become more powerful, attackers are also looking for a variety of new attack methods to bypass email security products, showing mutual promotion and spiraling trend between offense and defense. Therefore, when preventing phishing emails, do not rely solely on the protection capabilities of your internal mail gateway, and should also strengthen manual screening. In some scenarios, no matter how powerful a machine is, people’s good security awareness is always the most important key.
3.2 Use non-decimal IP addresses to build phishing links
There are two forms of most common URLs, one is a domain name address, such as https://work.nsfocus.com (NSFOCUS operating platform), and the other is an IP address, such as http://221.122.179.15 (NTI Threat Intelligence Center).
Especially for the form of the IP address, according to the RFC protocol and the current browser’s implementation, the browser URL not only supports the default decimal IP address, but also supports the octal and hexadecimal system to represent the IP address.
Taking the NTI Center as an example, in addition to accessing http://221.122.179.15, we can also access http://0xdd7ab30f in hexadecimal notation, or http://0033536531417 in octal notation. Both URL addresses are equivalent to regular IP addresses, and the target site can be successfully accessed using browsers such as Chrome and Firefox.
In cases of telephone fraud, scammers often take advantage of people’s unfamiliar features of foreign number formats, use overseas mobile phone numbers to call, and disguise themselves as the number of a certain national agency or special department. Similarly, we expect that phishing email attackers are likely to use such IP address URL variants in the future to insert such links in phishing emails, and then set specific inducing descriptions to attract users to click on such addresses.
As a precautionary measure, we recommend that you take a cautious attitude when encountering strangely formatted hyperlinks, attachment formats, and body content. Do not trust the misleading description of the email body text, and seek for professional security advice when necessary.
Chapter 4. Summary
Looking at the world right now, the pandemic has not shown any signs of ending. It is difficult to have a topic like the pandemic that can arise interest from people regardless of gender, age, or nationality. Therefore, we can predict that in the future, attackers will not give up on such hot topics and will construct various new attack modes and techniques. As a precautionary measure, after we see the “Covid-19”-related emails, we must be extra careful and screen each element of the email in detail to avoid risks.
References:
[1] https://www.fortinet.com/blog/threat-research/scammers-using-covid-19-coronavirus-lure-to-target-medical-suppliers
[2] https://www.fortinet.com/blog/threat-research/latest-covid-19-variants-from-the-ridiculous-to-the-malicious
[3] https://securelist.com/spam-and-phishing-in-q2-2020/97987/
[4] https://www.knowbe4.com/press/q3-2020-knowbe4-finds-coronavirus-related-phishing-email-attacks-still-prevalent
[5] https://healthitsecurity.com/news/report-phishing-campaign-uses-hidden-text-to-bypass-email-security
[6] https://www.inky.com/understanding-phishing-hidden-text-and-zero-font
