Introduction
This chapter analyzes IoT threats from the perspective of vulnerabilities. We first analyze the change trends of IoT vulnerabilities and exploits 1 in the NVD and Exploit Database (Exploit-DB) in 2019 and then IoT exploits captured by NSFOCUS’s threat hunting system. The following dwells upon some representative exploits.
IoT Vulnerabilities and Exploits
We speculate that attacks against IoT devices have a lot to do with the vulnerabilities and proof of concepts (PoCs) available on the Internet. We collected statistics on vulnerabilities and exploits from the NVD and Exploit-DB and analyzed their change trends in recent years.
Finding 3: Seen from vulnerabilities on the Internet, the number of IoT vulnerabilities changed slightly and they did not necessarily account for attacks against IoT devices. The number of exploits against IoT devices was stable, but its proportion increased generally.
NVD Vulnerabilities
The two numbers were small in 2019 because only vulnerabilities in January to October were collected. In addition, the proportion of IoT vulnerabilities fluctuated slightly between 10% and 15% except in 2006 and 2007.
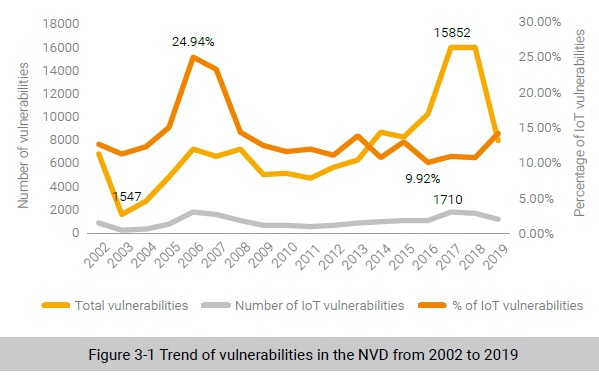
Seen from vulnerabilities on the Internet, the number of IoT vulnerabilities changed slightly and they did not necessarily account for attacks against IoT devices.
PoCs of Vulnerabilities in the Exploit-DB
A vulnerability assigned a CVE ID does not necessarily mean it deserves more attention. Sometimes, even its exploitability is questionable. We speculate that attackers targeting IoT devices are more interested in available PoCs. To prove this, we analyze the trend of exploits in the Exploit-DB, as shown in Figure 3-2.
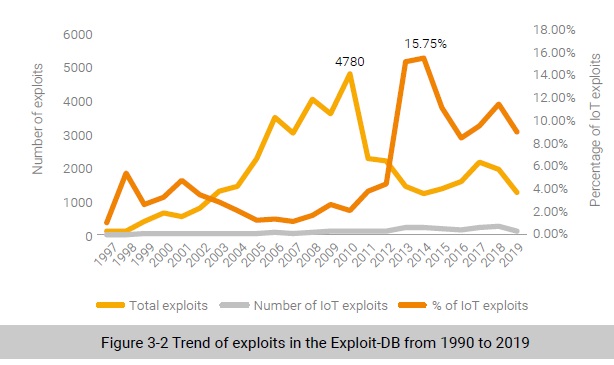
From 1997 to 2010, the number of exploits was on the rise, peaking at approximately 5000. However, the exploits eased back from 2010, fluctuating between 1000 and 2500. Overall, exploits slowed down in recent years.
Unlike the situation in 2010, IoT exploits were continuously on the rise from 1997 to 2018 and have increased significantly since 2013. This indicates that exploits against IoT devices were on an uptrend. Last but not the least, from 1997 to 2012, the share of IoT exploits in total exploits fluctuated but maintained below 6% from 1997 to 2012. However, from 2013, their share rose obviously, peaking at 15.75%.
On the whole, the total number of exploits fluctuated greatly, but IoT exploits were on the rise most of the time in both the absolute number and proportion, which accorded with the uptrend of attacks against IoT devices in recent years.
To be continued.
