1 Vulnerability Overview
Recently, ThinkPHP 5.0-5.0.23 was found to have a remote code execution (RCE) vulnerability. The NSFOCUS Falcon Team carried out tests and found that ThinkPHP 5.0-5.0.23, 5.1.0-5.1.31, and 5.2.* were also prone to this vulnerability, which could be triggered in both Linux and Windows systems.
This vulnerability occurs because the method in the Request class does not properly handle user-controlled data. Overriding variables, an attacker could invoke any functions in the Request class. Crafting a request, he or she can overwrite the attribute value of the Request class. All related users should stay wary and take precautions as soon as possible.
The test result is as follows:
2 Scope of Impact
Affected Versions
- ThinkPHP < 5.0.24
- ThinkPHP < 5.1.32
- ThinkPHP 5.2.*
Unaffected Versions
- ThinkPHP 5.0.24
- ThinkPHP 5.1.32
3 Vulnerability Check
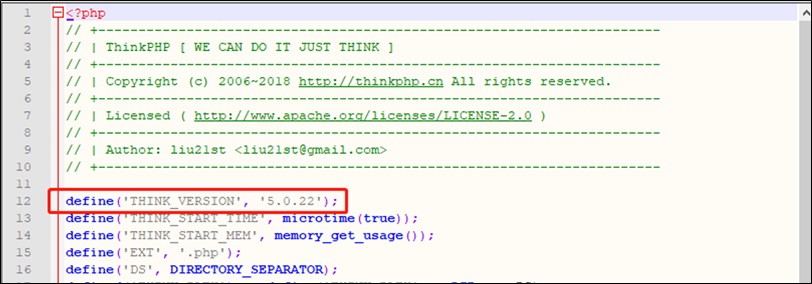
3.1 Version Check
Use a text editor to open thinkphp\base.php and then you can find the version number of the current framework from the section of code on constant definitions.
If the version is vulnerable, please take precautions as soon as possible to fix the vulnerability.
In addition, from V5.1.20, ThinkPHP adds a command to show the framework version. Users can run the following command to view the framework version.
4 Vulnerability Protection
4.1 Code Fix
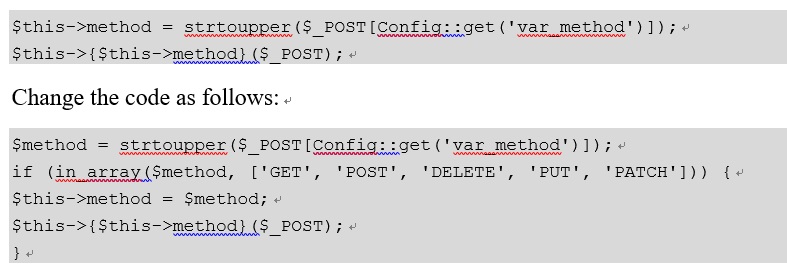
- ThinkPHP 5.0.*
Users of ThinkPHP 5.0.* can fix this vulnerability by modifying code. For details, visit the following link:
https://github.com/top-think/framework/commit/4a4b5e64fa4c46f851b4004005bff5f3196de003
Use the editor to open \thinkphp\library\think\Request.php and locate the code in lines 525 and 526:
Save the changes.
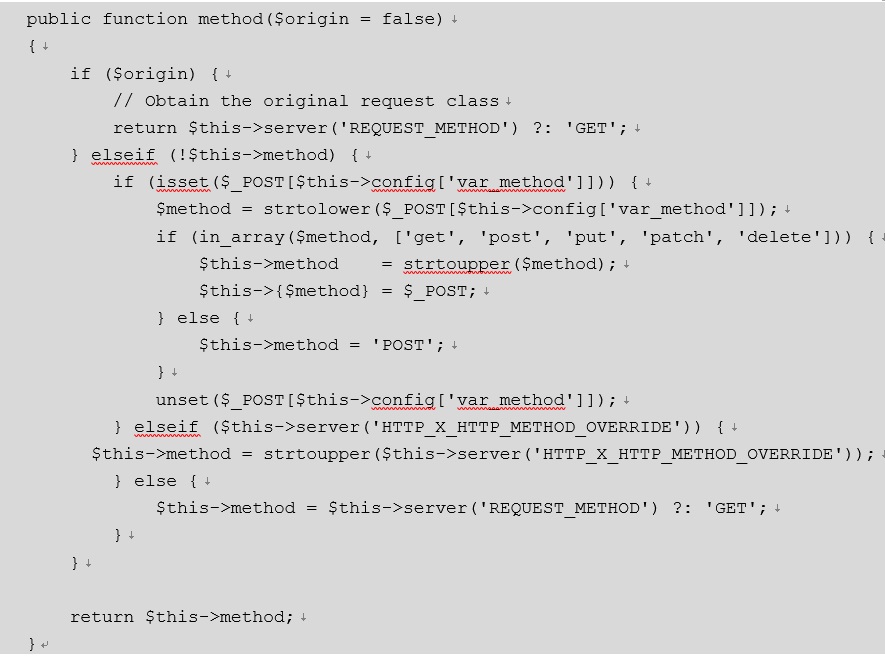
- ThinkPHP 5.1.* and 5.2.*
Users of ThinkPHP 5.1.* and 5.2.* can fix this vulnerability by performing the following steps:
Use the editor to open \thinkphp\library\think\Request.php and locate the method function and then change it to the following code:
4.2 Deployment of Security Products
NSFOCUS security protection products can be used for protecting against this vulnerability. For users who have deployed NSFOCUS NIPS, they can fix this vulnerability by updating rules as follows:
| Product | ThinkPHP Version | Rule Base Version | Rule ID |
| NIPS | ThinkPHP 5.0.* | Ÿ 5.6.7.752
Ÿ 5.6.8.756 Ÿ 5.6.9.19516 Ÿ 5.6.10.17650 |
24375 |
| Ÿ ThinkPHP 5.1.*
Ÿ ThinkPHP 5.2.* |
To be released | To be released |
To update rules, visit the following link:
- NSFOCUS NIPS: http://update.nsfocus.com/update/listIps
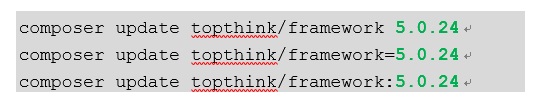
4.3 Version Upgrade
New versions of 5.0.* and 5.1.* have been released to patch the vulnerability in question. Affected users are advised to upgrade to the latest versions as soon as possible. ThinkPHP 5 allows users to use Composer for installation and upgrade. Users are advised to back up applications and modified directories, open a Command Prompt window in the root directory and then execute one of the following commands.
Note: If the user uses an early ThinkPHP 5 version, a compatibility problem may arise during the upgrade. In this case, it is recommended that the user perform the upgrade according to the upgrade procedure described in the official user guide. To obtain the user guide, visit the following link:
- https://www.kancloud.cn/manual/thinkphp5/163239
- https://www.kancloud.cn/manual/thinkphp5_1/354155
 Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.