Event Overview
Since February 2021, NSFOCUS’s emergency response team has found that several provinces in China saw multiple SMS phishing events using fake bank domain names. As these events bear a striking resemblance in the phishing playbook, attack means, and phishing website pages, we can largely determine that these attacks were launched by the same hacking group. The phishing SMS message claims that the victim’s online banking account is about to expire or be suspended. Also, such message contains a fake domain name of the phishing website which has a highly similar login interface to the intended mobile banking service, tricking users into typing sensitive information such as the identity card numbers, mobile numbers, and login password, SMS verification code, and transaction password of the mobile banking service. Currently, many users have suffered identity theft on a bank account numbers, and therefore the public should study alert and take precautions.
What to Learn
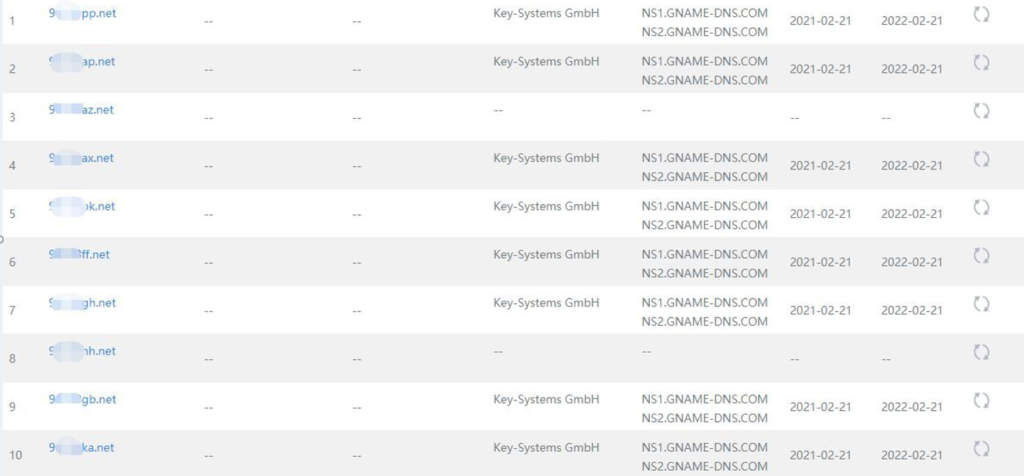
The attacker registered a lot of irregular domain names with an overseas domain name registrar. Those domain names that are 6 to 8 characters long are frequently changed during attacks, but all are resolved into the IP address of the virtual private server (VPS) purchased by the attacker outside of China.
The phishing website will first check the user’s browser information and then trick the user into accessing the malicious website via a mobile browser. The fake website has a web login interface that is built to look like that of a mobile bank, asking the victim to type the user name and password for login. After the login credentials are typed, the fake login progress will be displayed.
Meanwhile, the website background will invoke the identity authentication interface to verify the login credentials typed by the user and return a phishing page, depending on the verification results. If the user fails the login authentication, a fake error page will be displayed.
If the user is authenticated, a page is shown to ask the user to type the transaction password and the SMS verification code received by the mobile phone. After the user’s transaction password and SMS verification code are submitted, a fake account activation progress is displayed. At the same time, the attacker, however, has conducted illegal transfers via the mobile bank in the background.
Prior to illegal transfers, the attacker obtains the victim’s image through an interface and uses the face swap technique to bypass face recognition. Aided by certain identity authentication flaws in the transfer function of the mobile bank, the attacker finally completes illegal transfers.
Attack Profiling
Feature 1: Specialized attack group
Prior to the attack, this malicious group has done a lot of reconnaissance work to have a good grasp of the business system, business logic, and security vulnerabilities of the intended mobile bank. Besides, the attacker has taken security hardening measures for its phishing website and VPS.
Feature 2: Definite target
This attack group mainly targets regional banks and sends a phishing SMS message to users with mobile numbers registered in the same region as the targeted bank.
Feature 3: Accurate and efficient attack
Unlike the traditional phishing websites, this phishing website will invoke an interface of the intended bank to authenticate the victim’s login credentials to filter out irrelevant information, finally transferring money from the victim’s account in real time.
Feature 4: Rapid transfer
After stealing some users’ savings deposited in the target bank, the attacker usually rapidly changes its domain name and VPS’s address to prevent further analysis and trackback, before setting its sight on another bank.
Security Recommendations
- Perform security checks on the identity authentication process of the mobile banks, WeChat banks, banks on PC, e-banks, and other electronic channel systems and conduct security hardening and rectification for systems that contain authentication flaws or vulnerable functions.
- Use a risk control system to audit, alert for, and block users’ abnormal business behaviors like frequent login, remote login, device switching, and login to one device using multiple accounts.
- Update the face recognition component version to make face recognition more efficient. Alternatively, employ two-factor authentication or multi-factor authentication besides face recognition.
- Educate customers about protective measures against phishing fraud through SMS, WeChat official accounts, mobile apps to help them raise cybersecurity awareness.
Appendix
Following are some IP addresses of the VPS used by the attack group:
41.216.177.89
203.78.140.153
41.216.177.30
41.216.177.52
156.253.11.4
156.226.23.29
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyberattacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.
