Produced by: NSFOCUS Security Labs
In early January 2021, NSFOCUS Security Labs captured an unknown malicious program called “out.py” via its real-time data platform, which is usually spread with the domain name “gxbrowser.net”. NSFOCUS Security Labs conducted an in-depth research on the samples and payloads of the malware and compared the malware with NSFOCUS threat intelligence, concluding that the malware belonged to a new type of botnet family.
In mid- and late January 2021, many companies also detected the malware. Since it was called out.py and associated with the attacker dubbed Freak, it was named FreakOut. The malware was spread exploiting three vulnerabilities:
- CVE-2020-28188 (TerraMaster TOS unauthorized remote command execution (RCE)
- CVE-2020-7961 (Liferay Portal code execution vulnerability)
- CVE-2021-3007 (Zend Framework deserialization vulnerability)
Disclosed around January 3, 2021, the vulnerability assigned CVE-2021-3007 was quickly exploited by hacking groups within a week. A further analysis reveals the operator and seller behind the malware. This article elaborates on how FreakOut-related information was associated and how the group behind the malware evolved.
Attacker
By tracing, we found that FreakOut is not a new malicious family but a product of years’ evolution. necro.py, a version recently used by the attacker, retained comments and revealed names of the botnet and attacker.
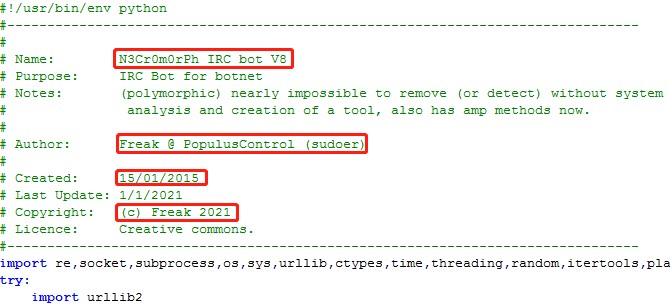
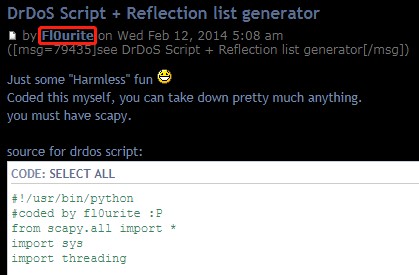
The attacker group behind the FreakOut campaign has years of history. As a Trojan for distributed denial of service (DDoS) attacks written in Python, FreakOut is only one of the numerous hacking tools developed or used by the attacker group. Early in 2014, the attacker with the screen name Fl0urite wrote DDoS Trojans in Python at HackThisSite. In 2015, they published a post at HackThisSite with the same name, which mentioned the N3cr0m0rph IRC botnet. It can be seen that the botnet had begun to take shape at that time. Afterwards, the attacker name Fl0urite was rarely seen probably due to some changes.

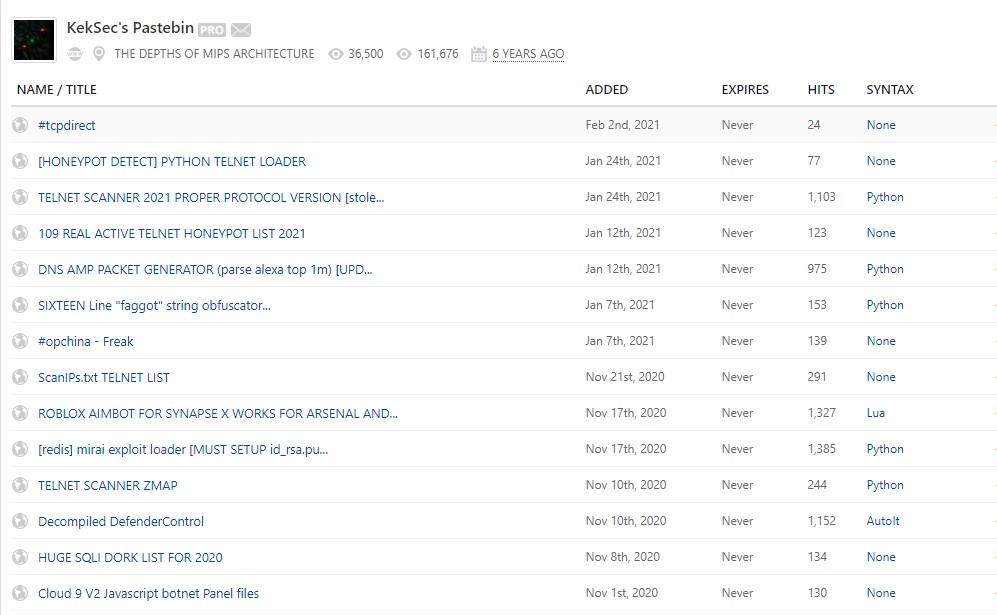
Besides, the attacker registered an account N3Cr0M0rPh at Stackoverflow. The Pastebin page linked from a post stored botnet-related tools and Trojan code, which are still active.
Attacker Footprints
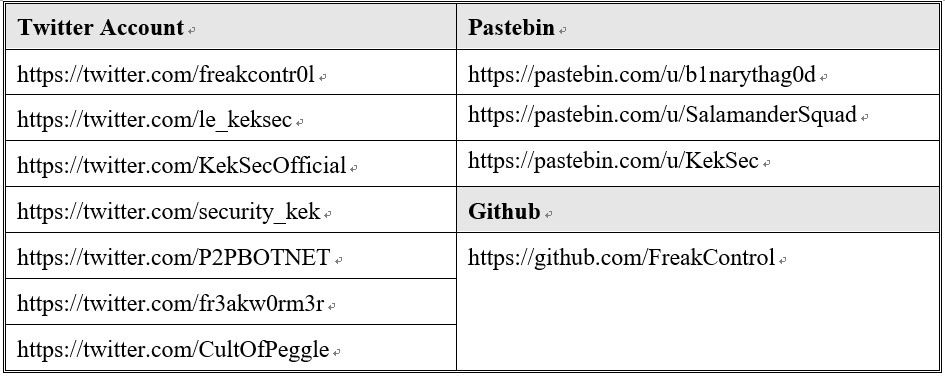
By analyzing the files shared at Pastebin, we obtained the following IDs that had been used by the attacker and the related group:
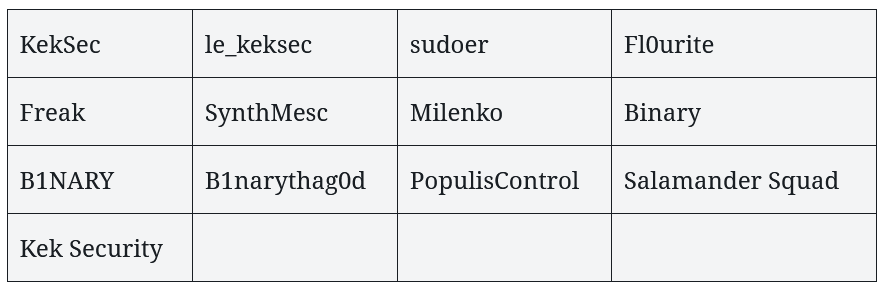
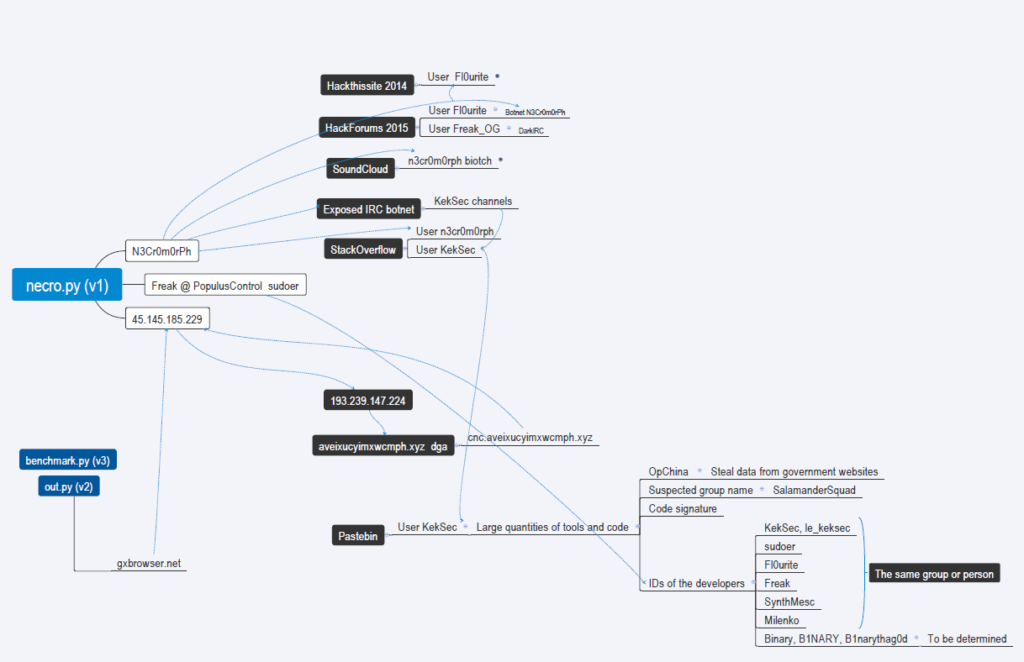
Based on these IDs and information found in Trojan programs, we got an association map as shown below.
Through the association, we confirmed that FreakOut developers acted in the following three groups:
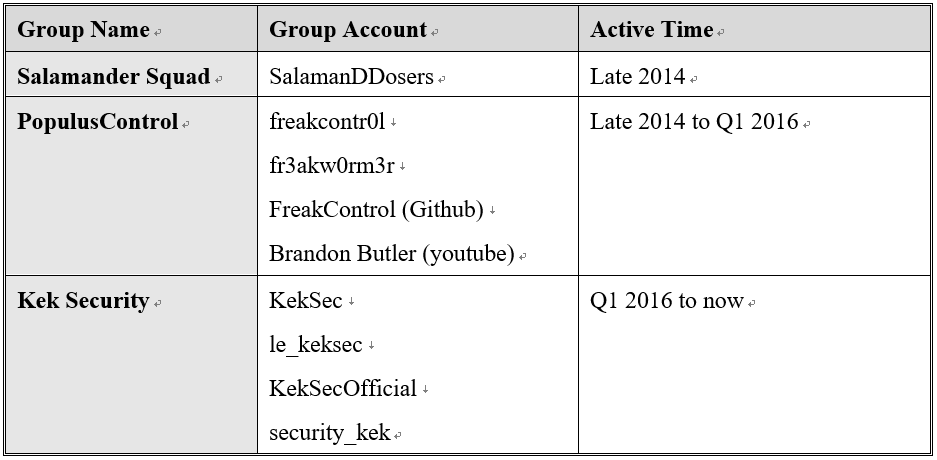
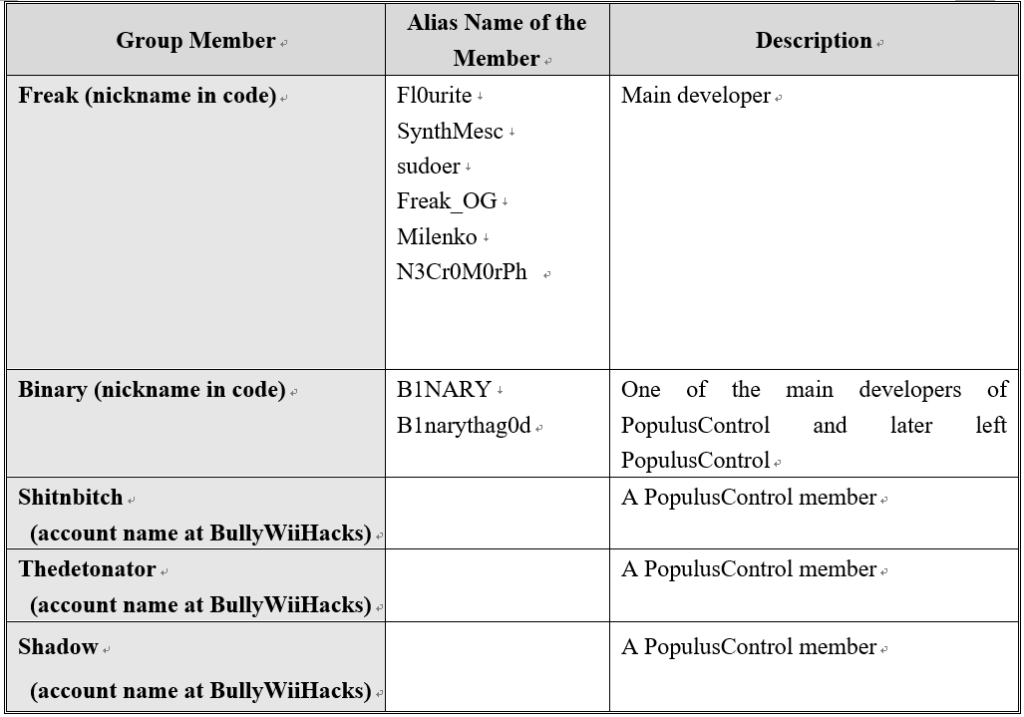
In terms of active time, Salamander Squad, PopulusControl, and Kek Security showed a clear iterative relationship, which may be related to changes in the group’s main developers. In addition, we confirmed some members of the preceding groups:
Therefore, we can confirm the development path of the group behind FreakOut.
Freak, one of the main developers of FreakOut, was a member of Salamander Squad as early as 2014, a DDoS botnet operating team. Before long, this person joined (or founded) PopulusControl, to which the developer nicknamed Binary belonged, to continue operating the DDoS botnet.
When PopulusControl prevailed, its members were active at a hacker forum called BullyWiiHacks and kept in contact with one another via the IRC channel. Registered users of BullyWiiHacks, such as shitnbitch, thedetonator, and shadow, were also PopulusControl members.
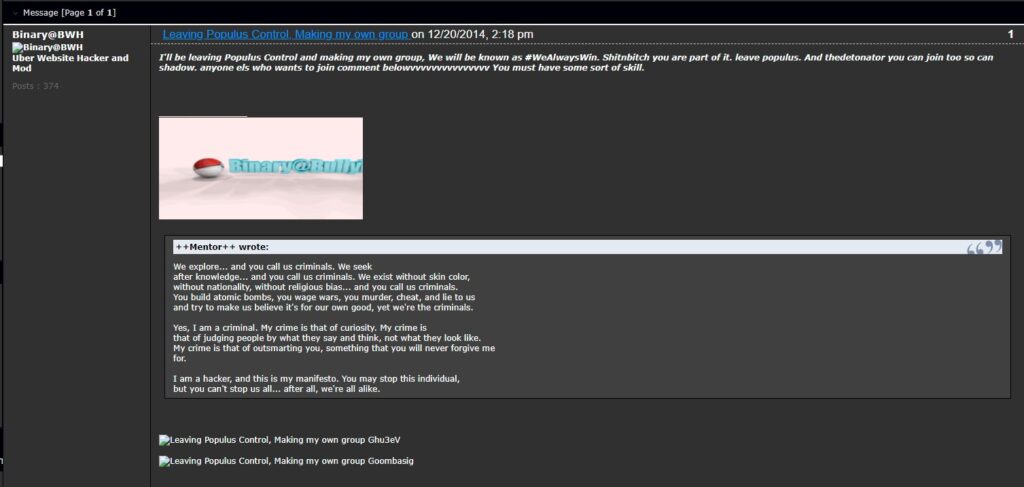
At the end of 2014, Binary claimed to leave PopulusControl to start his/her own business and took away some of the members. Since then, Freak undertook most development tasks of PopulusControl. During this period, Freak updated multiple versions of CancerNet and n3cr0m0rph Python IRC bot programs, which were the predecessors of the FreakOut Trojan.
In 2016, Freak joined (or founded) KeK Security (Keksec), a hacker group. Apart from continuing botnet operations, Keksec carried out blatant hacking activities, including hacking billboards (https://hacked.wtf/hacker-news/keksec-on-billboard-security/2019/09/17/) and boasting of its intrusion results at Twitter. The following figure displayed a tweet that Keksec copied to a billboard one tweet of John McAfee, the founder of McAfee, and forwarded another tweet of John McAfee online.

Freak created variants of multiple open-source IoT Trojans and put them into use. Such variants were usually named keksec.[platform], such as keksec.x86 and keksec.arm7.
Page information of relevant groups is as follows:
Group Business Behaviors
Freak and Kek Security mainly seek profits by selling hacking software and DDoS resources. The sales activities of Freak and relevant groups can be found in their forum movements.
In 2020, a user named Freak_OG of Hackforums published a post on June 17, 2020, claiming to provide free installation packages for private cryptomining. On December 6, 2020, the user attempted to sell one silent Miner for USD 25.

The cryptomining tool using XMRIG v6.6.2 contained various types of properties and supported multiple terms of payment. In order to promote the tool, the user posted some screenshots to prove its profitability.
On December 1, 2020, Freak_OG published a post to sell a botnet Trojan called DarkHTTP Loader for USD 50. The Trojan provided a control panel and fulfilled multiple functions, such as spreading via intranets, file theft, and spreading via USB. It could also conduct brute-force attacks on SMB/MSSQL/MYSQL protocols.

In addition, Freak_OG sold a Windows Trojan called DarkIRC for USD 75. The Trojan was spread via WebLogic vulnerabilities and could perform malicious behaviors, such as launching DDoS attacks, logging keystrokes, downloading executables, executing shell commands, stealing browser credentials, and hijacking Bitcoin transactions.
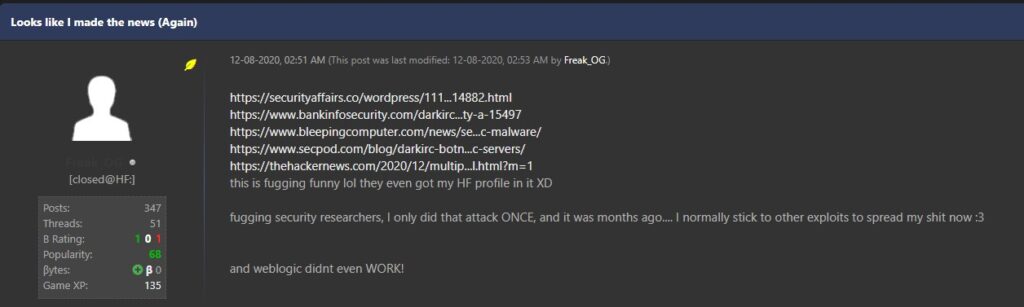
However, the group failed to keep covert and attracted the attention of researchers. In a post, the user commented on researchers revealing his behaviors and admitted having sold Trojans and launched the attack.
Anyway, Kek Security has been seeking methods to cash in on its own resources.
Links with Other Botnet Families
Besides such a Python DDoS family as FreakOut, Freak and KeK Security operate other botnet families and share C&C infrastructure.
KeK Security exploits IRCBot and Tsunami IRC families for DDoS activities. It also uses Freak, keksec, or kek as the name of an IRC channel that had a maximum capacity of 1214 users, most of whom came from the USA.
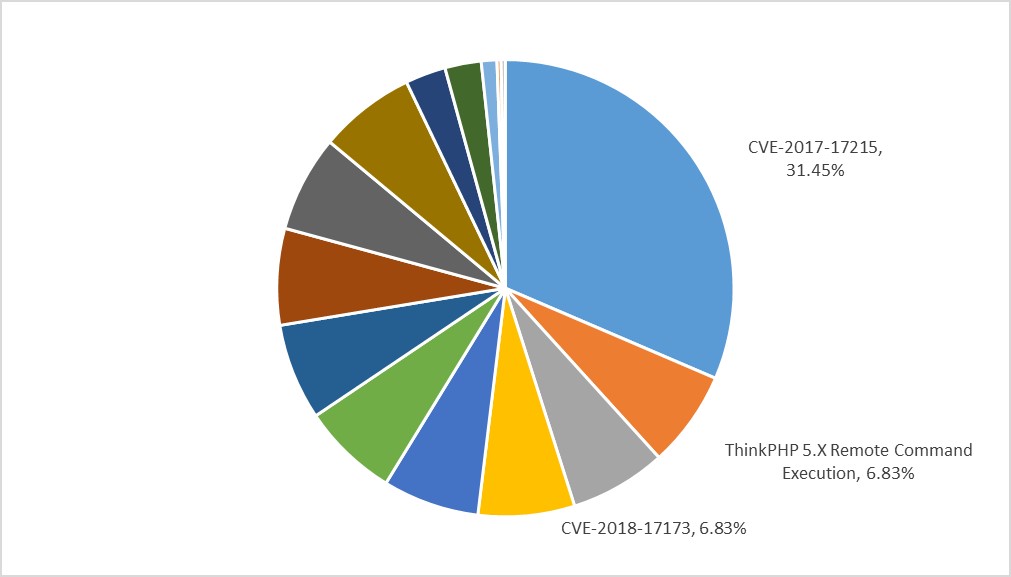
Kek Security operates HybridMQ-keksec, a botnet created with Trojan programs. HybridMQ-keksec is a DDoS Trojan program obtained by combining and modifying the source code of Mirai and Gafgyt. It mainly uses Huawei HG532 router command injection and ThinkPHP remote command execution vulnerabilities for propagation.
Some HybridMQ-keksec Trojan programs have new functions and could check raw TCP network traffic received. If HTTP, FTP, and SMTP services are involved, these programs transmit port and data information to C&C servers. Such an operation is rare in DDoS families on Linux and IoT platforms. This allows attackers to exploit the victim’s host to conduct DDoS attacks and steal unencrypted communication data from the victim’s host to facilitate potential intranet infiltration or targeted attacks.
Read the second part:
