Overview
Recently, NSFOCUS CERT discovered that the Qualys research team disclosed a local privilege escalation vulnerability (CVE-2021-33909, aka Sequoia) in the filesystem layer in the Linux kernel. It is a size_t-to-int type conversion vulnerability in the seq_file interface in the Linux kernel. fs/seq_file.c’s improper restriction of the seq buffer allocation may cause an integer overflow, out-of-bounds write, and privilege escalation. Attackers with arbitrary user privileges may exploit this vulnerability in default configurations to gain root privileges of the affected host. This vulnerability affects all Linux kernel versions that have been released since 2014. Currently, PoC is made publicly available and related users should take precautions as soon as possible.
Reference link:
https://www.qualys.com/2021/07/20/cve-2021-33909/sequoia-local-privilege-escalation-linux.txt
Scope of Impact
Affected Versions
- 3.16 <= Linux kernel < 5.13.4
Unaffected Versions
- Linux kernel => 5.13.4
Check for the Vulnerability
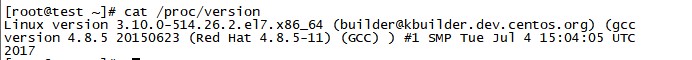
Version Check
Users of the Linux system could run the following command to check the current version to determine whether it is vulnerable:
cat /proc/version
Mitigation
Official Fix
Currently, this vulnerability has been fixed in the latest version. If you are affected by this vulnerability, please upgrade your installation as soon as possible. The official patch download link is https://www.kernel.org/.
Workarounds
If users cannot upgrade their system for the time being, they can take the following steps to fix specific vulnerabilities in Qualys for temporary protection:
1. Set /proc/sys/kernel/unprivileged_userns_clone to 0 to prevent attackers from mounting a long directory in a user namespace.
2. Set /proc/sys/kernel/unprivileged_bpf_disabled to 1 to prevent attackers from loading the eBPF program to the kernel.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA). A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.