2.3 Vulnerabilities in ICS Assets
Most ICS security mechanisms are short of authentication, encryption, and audits, and therefore such ICS assets are rather vulnerable. When connecting to the Internet, ICSs are susceptible to external probes or identification via special fields included in information returned through public or private communication protocols, web services, telnet, and FTP. In this way, ICS assets can be easily controlled by attackers. In addition, more and more ICS vulnerabilities are identified by researchers, leaving ICS assets exposed on the Internet rather vulnerable.
2.3.1 More ICS Assets Exposed
To minimize the chance of industrial control devices being hit by cyberattacks, ICSs should run in a physically isolated environment. However, this is not the case in the actual production environment. In July 2016, Kaspersky released a report indicating that 188,019 ICS hosts in 170 countries around the world were found connected to the Internet.
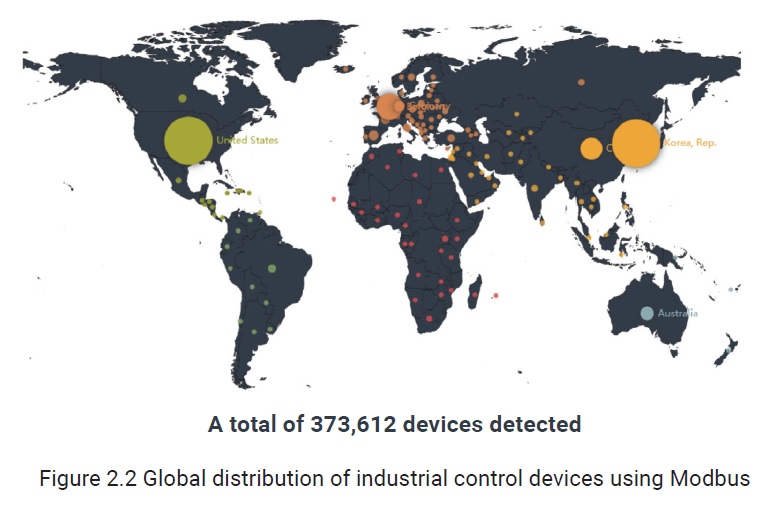
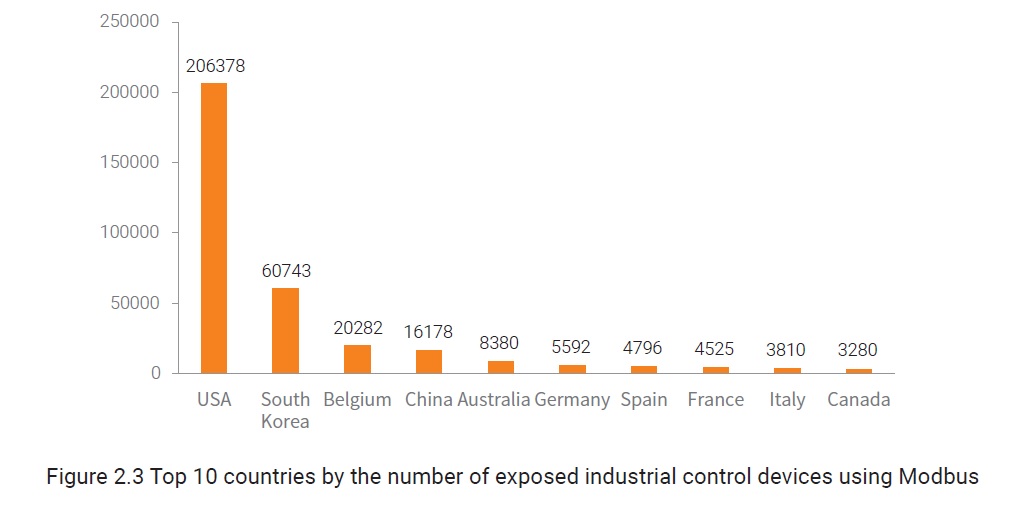
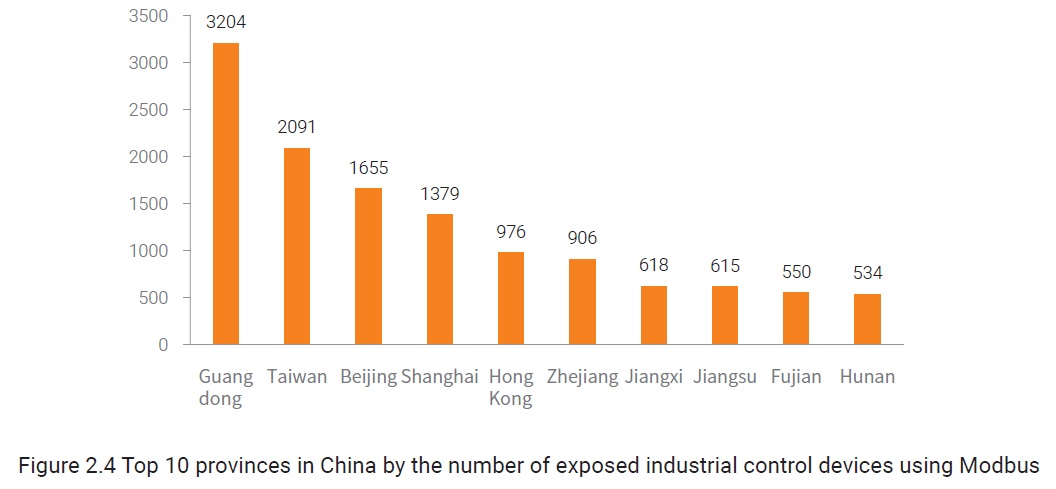
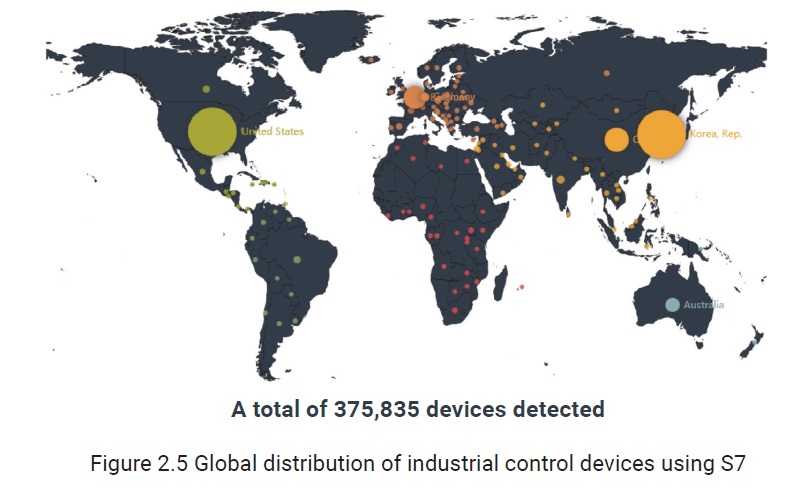
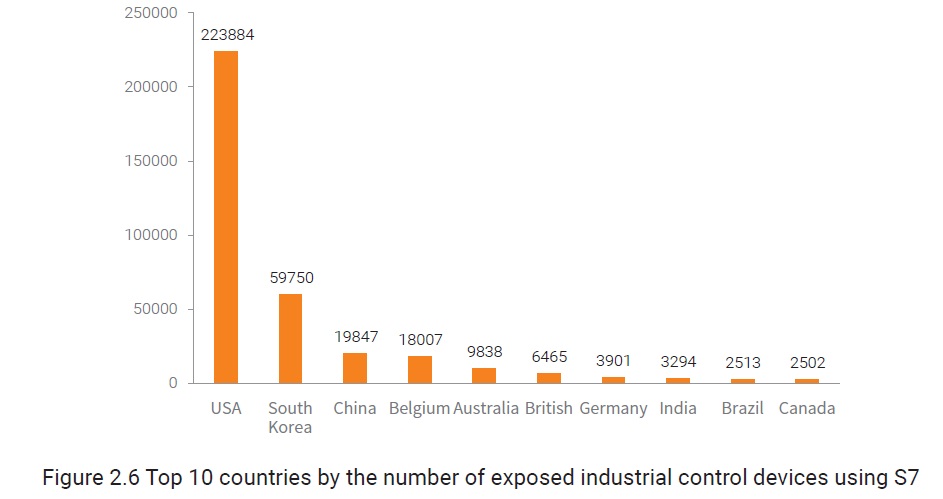
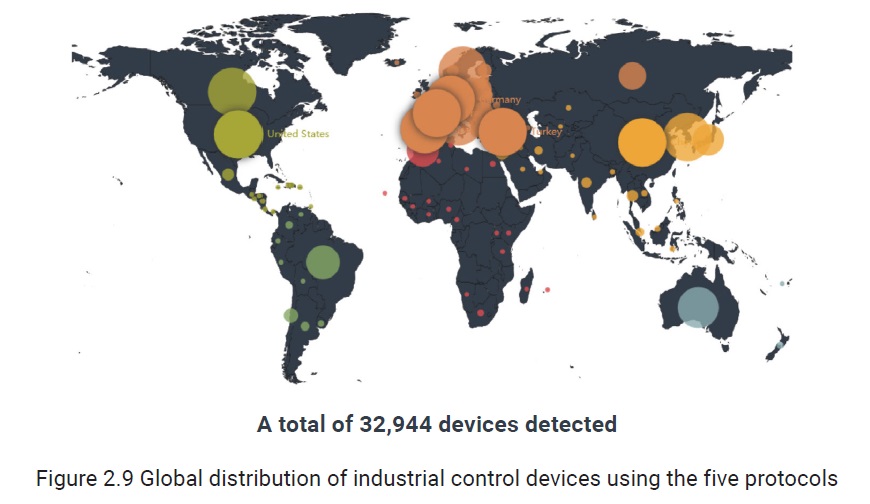
The following figures show the exposure of global assets on the Internet detected by NSFOCUS Threat Intelligence (NTI) using multiple protocols. The figures below take Modbus and the Siemens S7 protocol as an example to show the exposure and distribution of industrial control devices around the world (statistics are not collected for a particular year).
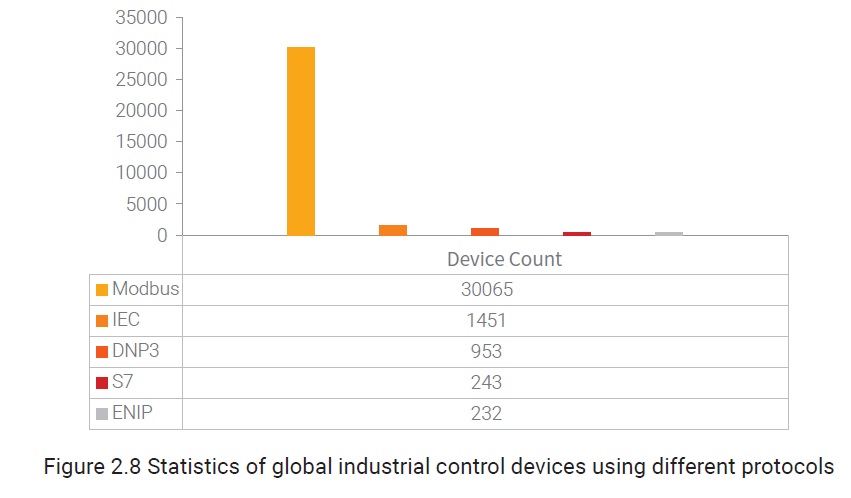
The following figure shows the number of industrial control devices using Modbus, S7, DNP3, ENIP, and IEC around the world in 2018.
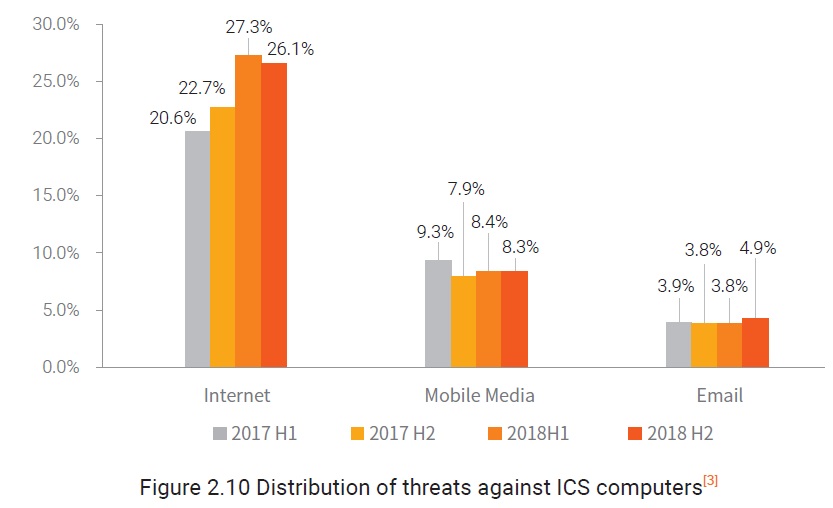
As more and more industrial control systems and devices worldwide are connected to the Internet, they will be exposed to more security risks. According to statistics from Kaspersky, in 2017 H1, 20.6% of threats against ICS computers were sourced from the Internet and this figure was increased to 27.3% in 2018 H1.
It seems to attackers that these industrial control devices exposed on the Internet make it possible for them to infect industrial control networks. If certain industrial control devices contain unpatched vulnerabilities and certain vulnerabilities within ICS software and hardware are shared and made publicly available, vulnerabilities in these devices will become attackers’ most likely point of entry into the industrial control networks.
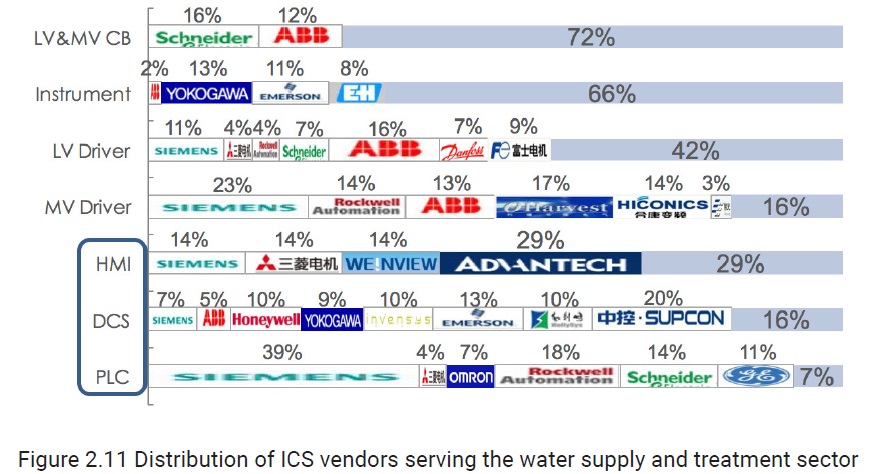
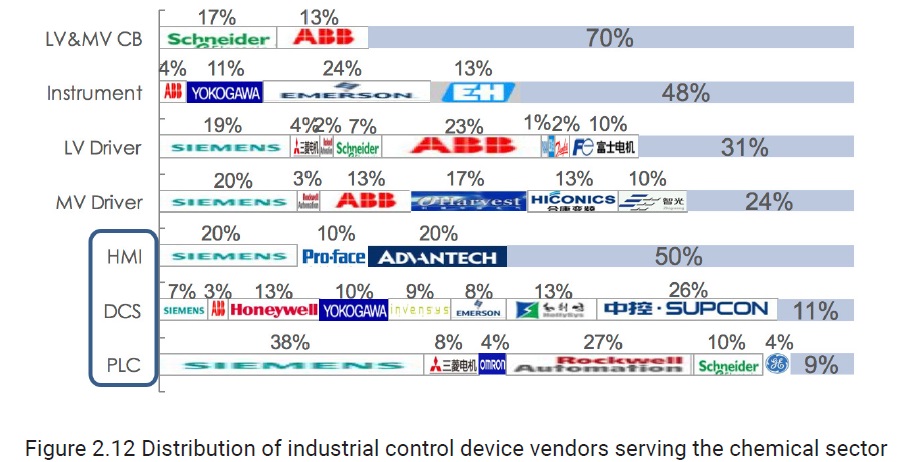
In addition, we have worked out the distribution of industrial control device vendors serving different sectors, as shown in the following figures. As HMIs, DCSs, and PLCs need to run operating systems and software, vulnerabilities tend to occur in the three types of devices. Therefore, we mainly focus on these types of devices here.
To be continued.