2.3.2 ICS Vulnerability Trend
As industrial control has been delving deeper in recent years, more and more ICS vulnerabilities are discovered by researchers. As vulnerabilities publicly available are only a small portion of those hidden in ICSs, the possibility of ICS vulnerabilities being stashed as potential cyber weapons cannot be ruled out. The following sections analyze the trend of ICS vulnerabilities by reference to data publicly available.
Statistics of Vulnerabilities Assigned CVE IDs
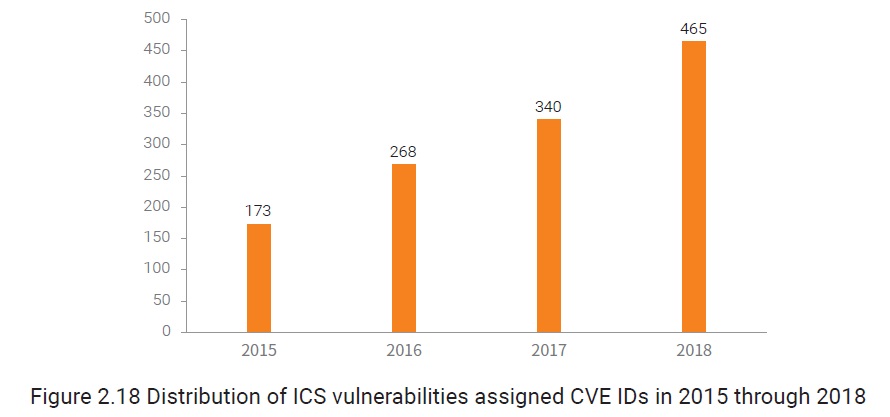
Some ICS vulnerabilities are given CVE IDs. In the light of the influence of CVE, we collect statistics on ICS vulnerabilities assigned CVE IDs.
Note: It takes a long time to fix ICS vulnerabilities (most ICS vulnerabilities are not addressed until six months later and a few remain unfixed within one year). By December 13, 2018, some of ICS vulnerabilities discovered in 2017 and 2018 were still not solved. Those unpatched vulnerabilities are not covered in statistics.
Since the occurrence of the Stuxnet incident, ICS security has begun to draw attention of more and more countries. Many companies and institutions are discovering ICS vulnerabilities, more and more ICS vulnerabilities are detected year by year.
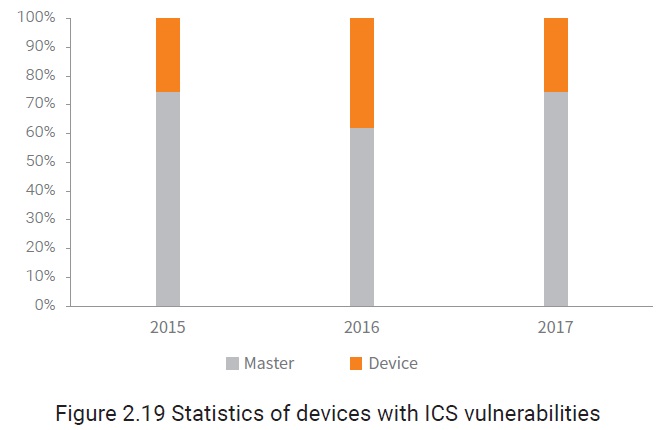
We divide vulnerable devices into HMIs and devices and show their proportions in the following figure.
According to statistics, a large portion of ICS vulnerabilities stem from HMIs which usually use web systems and database systems that are susceptible to security issues. ICS vulnerabilities related to application software running on PCs can be easily identified by traditional security companies. By contrast, discovering vulnerabilities in industrial control devices entails greater difficulties because ICSs tend to be embedded systems and industrial control software and hardware are highly customized and tailored. In addition, ICS vendors seldom make firmware updates publicly downloadable, and so only a smaller number of vulnerabilities are spotted on industrial control devices. However, as security vendors are setting about to go deep into industrial control device security, more and more vulnerabilities will be revealed.
Security Risks Brought by ICS Vulnerabilities
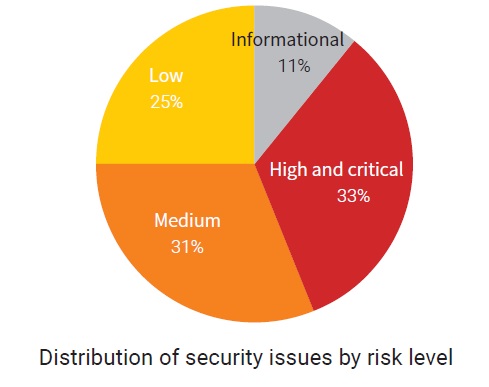
More and more vulnerabilities are exposed each year. So, how do those vulnerabilities affect the ICS industry? Now, we will explain the impact by reference to the data sourced from Mandiant ICS Healthchecks of FireEye. Mandiant ICS Healthchecks have assessed network security risks facing organizations in multiple sectors to determine the risk level of vulnerabilities by identifying the exploitability and the impact of a given issue, and cross-referencing the results. Our statistics show that at least 33% of security issues discovered in ICS organizations are rated high-risk or critical.
This means that attackers are highly likely to exploit these issues to gain control of the target system and compromise other systems and networks, cause disruption of services, disclose unauthorized information, or result in other significant negative consequences.
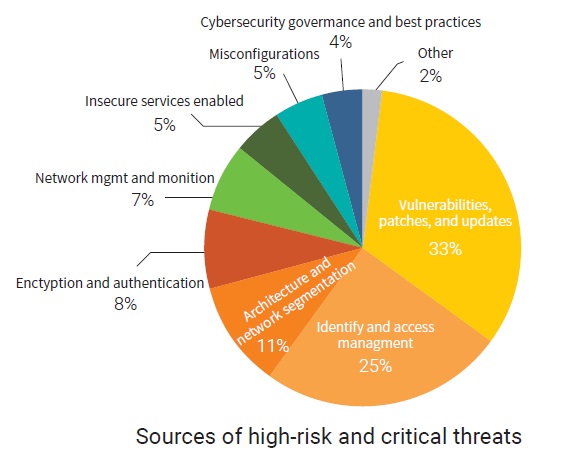
Of the high-risk and critical security issues (33%), most of them are related to vulnerabilities.
The preceding statistical results match the statistics of numerous ICS incidents that have occurred in recent years. That highlights the fact that a core section in security incidents is exploiting ICSÂ vulnerabilities to compromise the entire ICS system.
Here, we take the Stuxnet virus first discovered in June 2010 as an example. Stuxnet is a virus specially made to target infrastructure (in the energy sector) in the real world by exploiting four 0-day vulnerabilities, i.e., shortcut file parsing vulnerability (MS10-046), print spooler service vulnerability (MS10-061), kernel-mode driver vulnerability (MS10-073), and Task Scheduler vulnerability (MS10-092).
At the end of 2014, the refined BlackEnergy malware exploited a recently patched flaw in SIMATIC WinCC (sub-process monitoring system from Siemens) to attack the SCADA HMI system.
In 2017, the TRISIS (also known as TRITON) was found to exploit the 0-day vulnerability in Schneider Electric’s Triconex safety instrumented system (SIS) to initiate a cyberattack against an oil and gas factory in the Middle East, causing machines in this factory to cease to function. As the first kind of malware against SISs, TRISIS can cause factories to close down or result in personal injuries, and no doubt, a big threat.
The Threat Landscape Report for Q2 2018 released by Fortinet suggests that the most prevalent exploit attempt in the quarter involved backdoor access in Schneider’s Quantum Ethernet Module. As the default account uses a hard-coded password, a remote attacker could gain access to the device with this account through FTP access. A buffer overflow vulnerability in Siemens Automation License Manager came in second, followed by another overflow vulnerability in Advantech WebAccess. The two overflow vulnerabilities are caused by improper input sanitization and can allow arbitrary code execution.
Security vulnerabilities in industrial control networks can lead to a wide range of consequences from factory shutdown to nuclear plant explosion and nationwide power outage. Therefore, discovering and fixing vulnerabilities in ICSs to improve these systems before hackers successfully target ICSs is an important means to ensure secure operating of ICSs and increase security robustness of enterprises.
To be continued.