Powered by NSFOCUS Threat Intelligence (NTI), NSFOCUS ADS can block IP addresses that pose serious threats and high risks.
To ensure data reliability, ADS updates intelligence data daily and provides available update time frames for users to select. For the purpose of preventing IP blocking by mistake, you can configure IP exceptions to exclude a list of IP addresses from being blocked by the threat intelligence module. However, these IP addresses are still protected by other protection modules.
Besides, ADS provides Threat Intelligence Search capabilities that allow users to search local intelligence packages or search cloud-side NTI for IP intelligence data. It also supports the offline import of threat intelligence packages. Currently, only B-Package Indicators can be imported. Threat intelligence packages can be downloaded from update.nsfocusglobal.com after device licenses are imported.
Considering customers may use threat intelligence to conduct fine-grained control over some destination IP addresses, ADS allows users to configure a global NTI protection policy or for a specific protection group.
Note: When discovering suspected attacks but cannot find anomalous source IP addresses or signatures, you can try to find IP addresses from which a large amount of traffic originates and query the intelligence data of these IP addresses. You can check whether these IP addresses hit the intelligence database and what their threat type and level are. After IP addresses from which some DDoS attacks come pass the authentication of common algorithms and are added to the trust list, IP addresses are protected through the trust-based rate limit, which may affect some business traffic. It is difficult to identify DDoS attacker clients, for they have the capabilities of normal clients. In this case, you can enable the threat intelligence function to check whether intelligence IP addresses are hit and attack logs are generated.
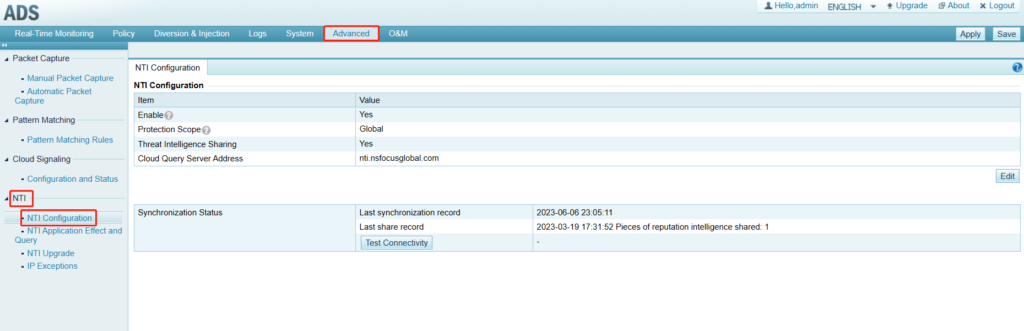
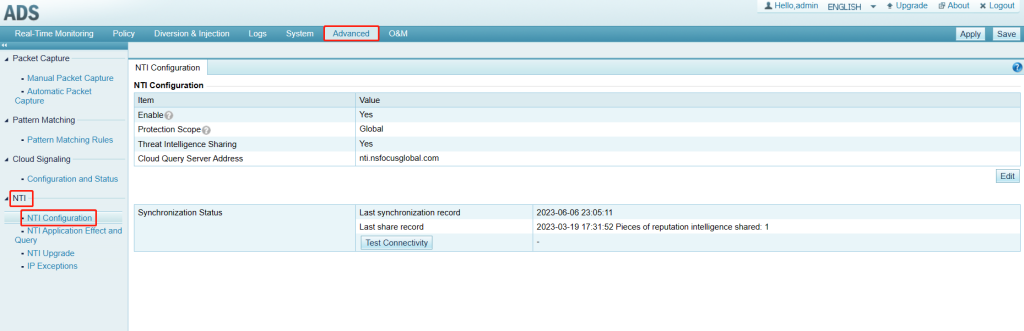
I. Global Threat Intelligence Configuration
Choose Advanced > NTI > NTI Configuration, enable the NTI function, and configure Protection Scope, Threat Intelligence Sharing, and Cloud Query Server Address. On this page, you can also view synchronization and sharing records and test the connectivity of the query server.
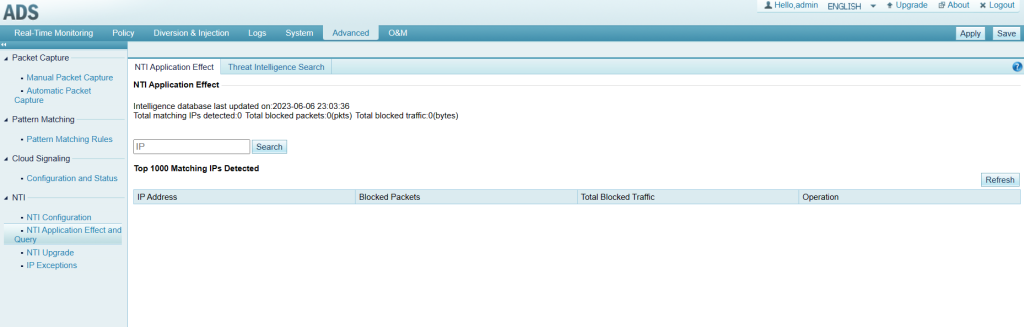
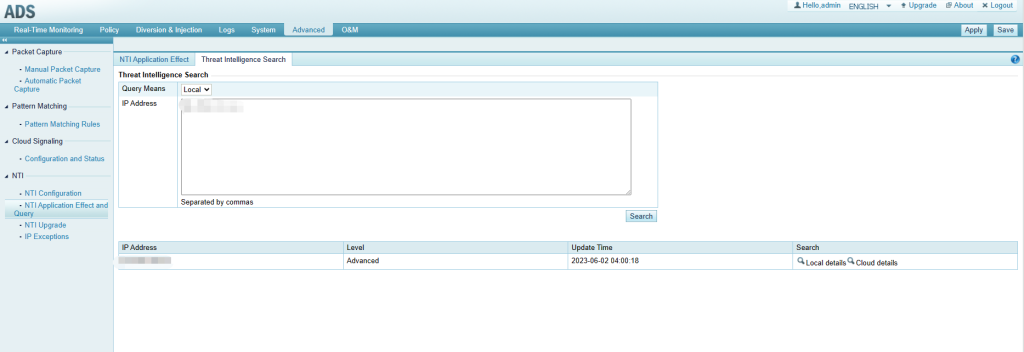
Under Advanced > NTI > NTI Application Effect and Query, there are two tab pages: NTI Application Effect and Threat Intelligence Search.
(1) The NTI Application Effect tab page displays up to 1000 matching IPs ranked by the number of times packets are hit. If more than 1000 IPs are matched, not all IPs will be displayed in the list, and you can type the IP in the search box to view matching details.
(2) The Threat Intelligence Search tab page allows users to search the local or cloud-side intelligence database for intelligence for specified IP addresses. Some intelligence data of the IP addresses will be displayed. If you want to view more intelligence data, you can click Local details or Cloud details. Cloud details are redirected to another web page.
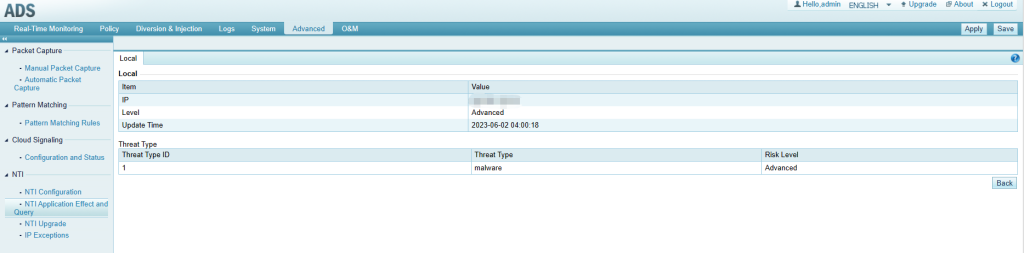
Click Local details, and you can view more information.
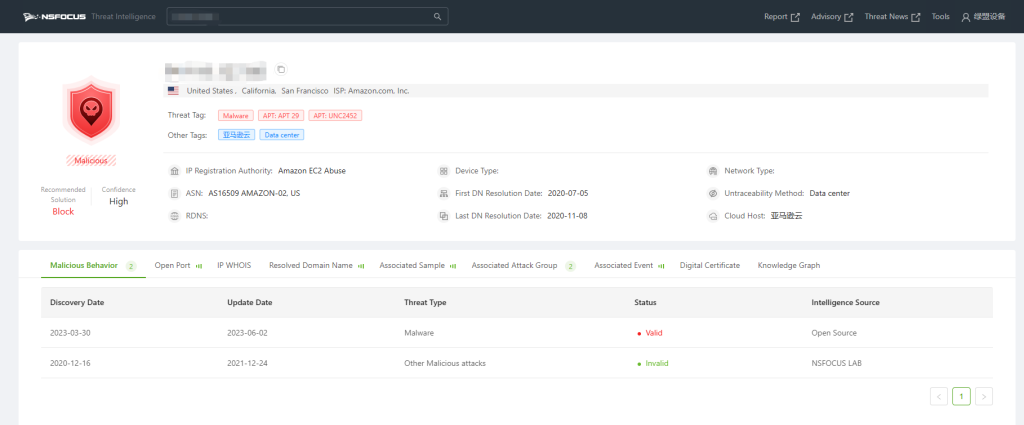
Click Cloud details, and you will be redirected to the web page of NSFOCUS Threat Intelligence.
II. NTI Upgrade
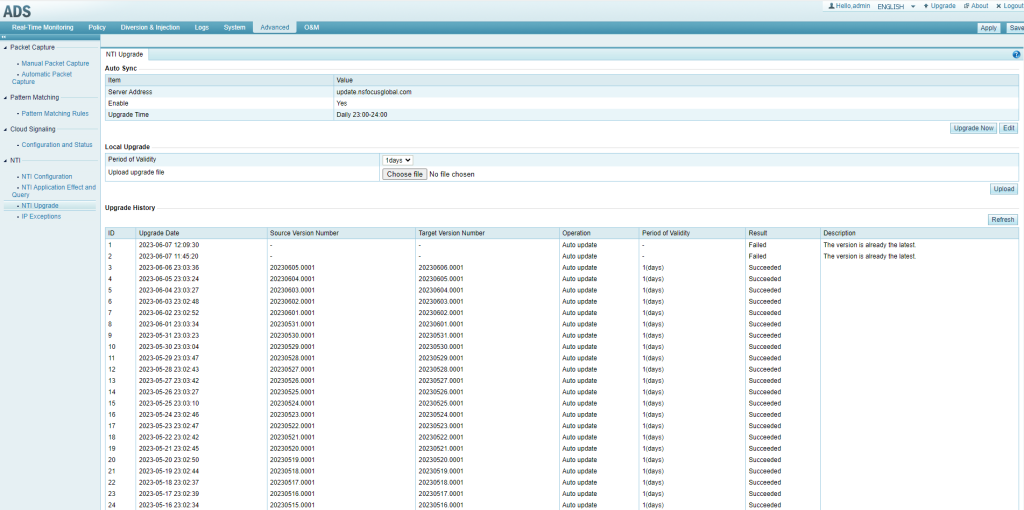
Under Advanced > NTI > NTI Upgrade:
(1) You can update the NTI. Note that after the intelligence function is enabled in NTI configuration, if you want to automatically download intelligence data from the cloud, enable Auto Sync on this page. If ADS cannot connect to extranets, you can go to update.nsfocusglobal.com to import the device license and download an offline package (B-Package Indicator only).
(2) You can select upgrade time.
(3) Customers in China use update.nsfocus.com, and customers outside China use update.nsfocusglobal.com.
(4) Intelligence data automatically downloaded and dispatched to the engine has a validity period of 24 hours by default, which cannot be changed. For manually uploaded intelligence data, you can select the period of validity, and the NTI upgrade does not require any restart. The upgrade history module tracks only all upgrades after the system starts, which will be automatically cleared after a restart.
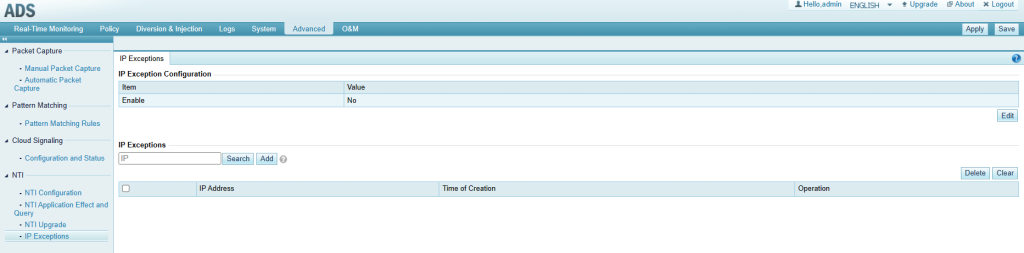
III. NTI IP Exceptions
Under Advanced > NTI > IP Exceptions:
IP exceptions, once enabled, can keep IP addresses or IP segments added to exceptions from being protected against threat intelligence.