1. Abstract
In March 2020, Tencent published an article about a DVR being used for reflection attacks. Service port of this DVR is 37810, we named it DHDiscover service as there was DHDiscover shown in it. In the reflection attacks captured by Tencent, the scale of attack traffic exceeded 50G, and the reflection source regions were concentrated in many countries and regions in America, Asia, and Europe, with South Korea and Brazil being the hardest hit areas. Based on the network-wide surveying and mapping data of NSFOCUS Threat Intelligence (NTI) and the captured data of NSFOCUS Threat Capture System, this article provides analisys on its network-wide exposure, reflection attack trends, attack methods commonly used by attackers, and reflection attack bandwidth amplification factors.
Key findings of this article are as follows:
– About 310,000 IPs worldwide have activated the DHDiscover service with a risk of being exploited for DDoS attacks.
– The five countries with the largest number of exposed assets for opening DHDiscover services are South Korea, Brazil, Vietnam, China and the United States in order.
– By analyzing the log data of accessing port 37810 captured by the NSFOCUS Threat Capture System from June 1, 2020 to August 18, 2020, the attacks showed an upward trend from early June to early August, and a slight decrease in the middle of August. , The maximum number of data packets captured by a single honeypot in a single day reached 900,000.
– The length of attack packets captured by the NSFOCUS threat capture system are mainly 4 bytes (54.7%) and 62 bytes (44.9%).
– We adopted two methods to evaluate the bandwidth amplification factor of DHDiscover: one is to send a 62-byte message, and the average bandwidth amplification factor of DHDiscover is 11.4; the other is to send a 4-byte message, and the average bandwidth amplification factor of DHDiscover is 178.8. About 53.6% of DHDiscover services will respond to this message. The bandwidth amplification factor of nearly 200 times is worthy of attention.
– Data from NSFOCUS threat capture system shows that the United States is the country most affected by the DHDiscover reflection attack, and US IP accounts for 42% of all victim IPs.
– The sample with DHDiscover reflection attack capability first appeared on December 7, 2019. Now there are already at least 5 samples with this reflection attack capability. As the attacker discovers that its actual magnification can reach nearly 200 times, we believe that more samples will have this reflection attack capability built in.
Last, we also raise our thoughts on the design of device discovery services. The original intention of the device discovery protocol is to facilitate the discovery of devices in the local area network. Therefore, the multicast address is mostly used for device discovery. Therefore, we believe that the ideal response strategy for device discovery message is:
- Respond to multicast messages.
- If it is a unicast message, check whether the sender’s IP is in the same network segment as the device’s IP, reply if it is. This strategy can also be changed into determining whether the sender’s IP is a LAN IP.
- If 1 & 2 do not meet the case, it will not reply. At the same time, the device should add Replying to Any Unicast Message function, which can be activated by the user when needed, but this function is turned off in factory setting.
2. Introduction of DHDiscover
In March 2020, Tencent published an article about a DVR being used for reflection attacks. Service port of this DVR is 37810, we named it DHDiscover service as there was DHDiscover shown in it.
The length of the DHDiscover service detection packet is 62 bytes. The content returned by the device is shown below. You can see lots of information about the device, such as MAC address, device type, device model, HTTP Port, device serial number, device version, etc. Therefore, we speculate that this service is used for device discovery:
'\x00\x00\x00DHIP\x00\x00\x00\x00\x00\x00\x00\x00\xa6\x02\x00\x00\x00\x00\x00\x00\xa6\x02\x00\x00\x00\x00\x00\x00
{"mac":"38:af:29:26:f8:80","method":"client.notifyDevInfo","params":{"deviceInfo":
{"AlarmInputChannels":16,"AlarmOutputChannels":3,"DeviceClass":"HCVR","DeviceType":"DH-********-
*","Find":"BD","HttpPort":80,"IPv4Address":
{"DefaultGateway":"192.168.0.1","DhcpEnable":true,"IPAddress":"192.168.0.19","SubnetMask":"255.255.255.0"},"IPv6Address":
{"DefaultGateway":"","DhcpEnable":null,"IPAddress":"\\/64","LinkLocalAddress":"fe80::3aaf:29ff:fe24:****\\/64"},
"Init":166,"MachineName":"XVR","Manufacturer":"Private","Port":37777,"RemoteVideoInputChannels":0,
"SerialNo":"4D019B8PAZ4****","Vendor":"Private","Version":"4.000.10****.0","VideoInputChannels":16,"VideoOutputChannels":0}}}\n\x00'
We searched keywords related to DHDiscover on AlienVault OTX, a threat intelligence platform, using Google: DHDiscover.search site:otx.alienvault.com/. As shown in Figure 1.1, there are five records corresponding to five samples, which means at least five samples have been put into the reflection attack weapon arsenal.
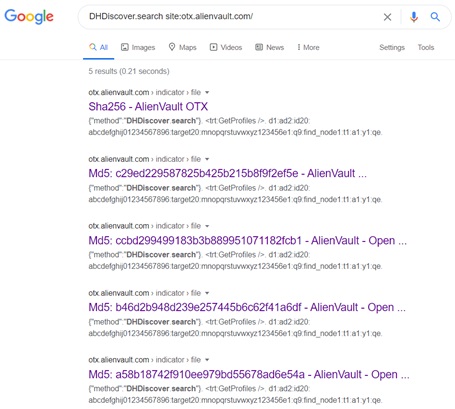
Figure 1.1 Search records of DHDiscover in AlienVault OTX (August 19, 2020)
We conducted a brief analysis of the timeline of these five samples, and found that one sample appeared on December 7, 2019[i] at the earliest, and this sample is continuously active. One sample appeared on March 3, 2020, And three more samples appeared on April 13, 2020.
Table 1.1 Related samples and appearance time
| Sample MD5 | URL | Appearance time |
| 73697e97fb48df3d9b52a4fa4d97c074 | http://144.217.34.147/jug7 http://ip04.montreal01.cloud.hosthavoc.com/jug7 | 2019/12/7-2020/8/18 |
| ccbd299499183b3b889951071182fcb1 | http://104.168.215.223/jibmips | 2020/3/3 |
| b46d2b948d239e257445b6c62f41a6df | http://103.214.6.199/fuk.mips64 | 2020/4/13 |
| a58b18742f910ee979bd55678ad6e54a | http://103.214.6.199/fuk.mips | 2020/4/13 |
| c29ed229587825b425b215b8f9f2ef5e | http://103.214.6.199/fuk.spc | 2020/4/13 |
3. Analysis of DHDiscover service exposure
In this part, we analyzed the exposure of the DHDiscover service, using data from NTI in June 2020.
About 310,000 IPs worldwide have activated the DHDiscover service with a risk of being exploited for DDoS attacks.
In the data from NSFOCUS threat capture system, we not only captured the detection on DHDiscover service on port 37810, but also a small amount of detection on port 23000. Therefore, we conducted a round of mapping for these two ports. After filtering out irrelevant data, we found that 300,000 IPs have opened port 37810, and more than 7,000 IPs have opened port 23000.
The five countries with the largest number of exposed assets that open DHDiscover services are South Korea, Brazil, Vietnam, China and the United States in order.
Figure 2.1 is the distribution of assets in countries that open DHDiscover services. In the reflection attacks captured by Tencent, the distribution of reflection sources is concentrated in many countries and regions in the Americas, Asia, and Europe, with South Korea and Brazil being the hardest hit areas. Based on the distribution data we have, South Korea and Brazil also have the largest number of exposures.
[i] The appearance time of the first sample comes from AlienVault OTX, the time data of other samples and the download URL data of all samples come from VirusTotal.
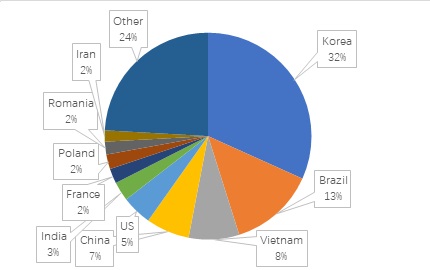
Figure 2.1 Country distribution of assets that open DHDiscover service
We calculated statistics on the Vendor, DeviceClass and Version fields in the surveying and mapping data. Figure 2.2 shows the distribution of Vendor fields. It can be seen that apart from Private and General that cannot be determined, related vendors include Intelbras, CPPLUS, QSee, etc. However, since the service detection messages of these devices are consistent with DHDiscover included, and the returned message shows port 37777, it can be basically confirmed that these devices are related to a video surveillance manufacturer.

Figure 2.2 Vendor field distribution
Figure 2.3 is the distribution of the DeviceClass field. We don’t know much about the classification of video surveillance equipment, only know about IPC, NVR, DVR, and 43.1% of the device categories are HCVR
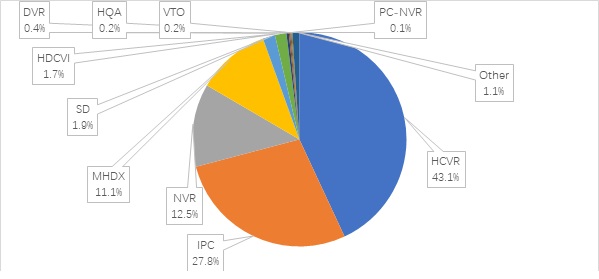
Figure 2.3 DeviceClass field distribution
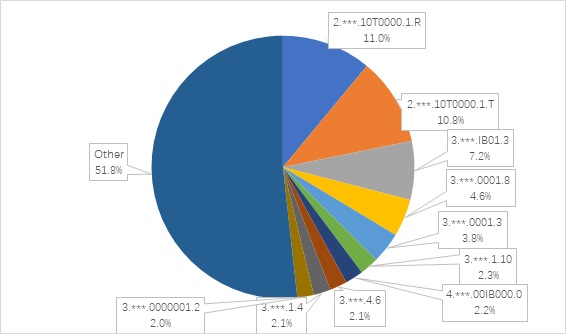
Figure 2.4 is the distribution of the Version field with thousands of types.
