Mirai
At present, Mirai is among the biggest IoT botnet families which have the most variants and infect the most devices to impose the most extensive impact. In 2019, NSFOCUS Security Labs captured 10,635 Mirai samples in total (excluding the repetitive malware arising from cross compilation), identified 1660 C&C addresses, and detected more than 40 exploits.
2019 saw three improvements introduced to Mirai variants:
- Constantly updating/replacing exploits
- Adding or optimizing DDoS attack approaches
- Using Tor as a proxy for C&C communications
The following DDoS methods are updated in Mirai variants:
- TCP reset attack
- Small UDP packet attack
- Abnormal TCP packet attack
- HTTP POST attack
- HTTP GET attack
- DNS reflection attack
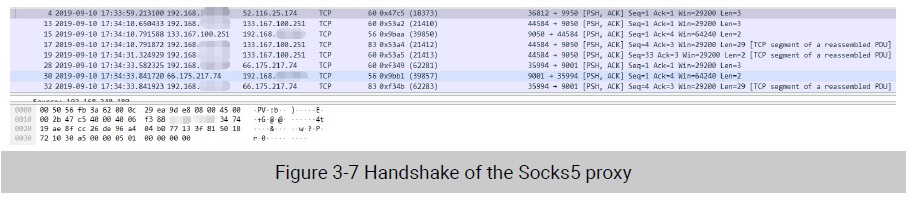
Following is the procedure of communications of Mirai variants using Tor as the proxy:
Mirai variants contain hard-coded proxy IP addresses in varying amounts. Such a variant first sends a Socks5 handshake message to connect to the proxy server before establishing a connection to the C&C server. Upon the receipt of the message, the proxy server will return a response, indicating that it is just the proxy server that can connect to the Tor network. After that, the variant will connect to the C&C server in the dark web to receive instructions.
The following is the global distribution of attack targets of Mirai. Obviously, North America and Europe were most severely attacked. Also, coastal areas of some countries in East Asia, Oceania, and South America were greatly affected by Mirai.
As the author of Mirai released all code of Mirai, it can be deployed in an automatic way. However, most Mirai operators, when deploying Mirai, overlooked a fact that Mirai’s report service requires setup of a MySQL database. They deployed the C&C server and report program on the same VPS and opened port 3306 for public access, making it possible for others to access data on the VPS.
Meanwhile, our data comparison suggests that our captured attack instructions only made up a small portion of all attack instructions in the same period. Therefore, it can be inferred that a number of C&C servers of Mirai were deployed on the same VPS server, controlling different numbers of zombies and used different database accounts and passwords. In doing so, the hacker could prevent his or her botnet from being taken down because some C&C server was detected.
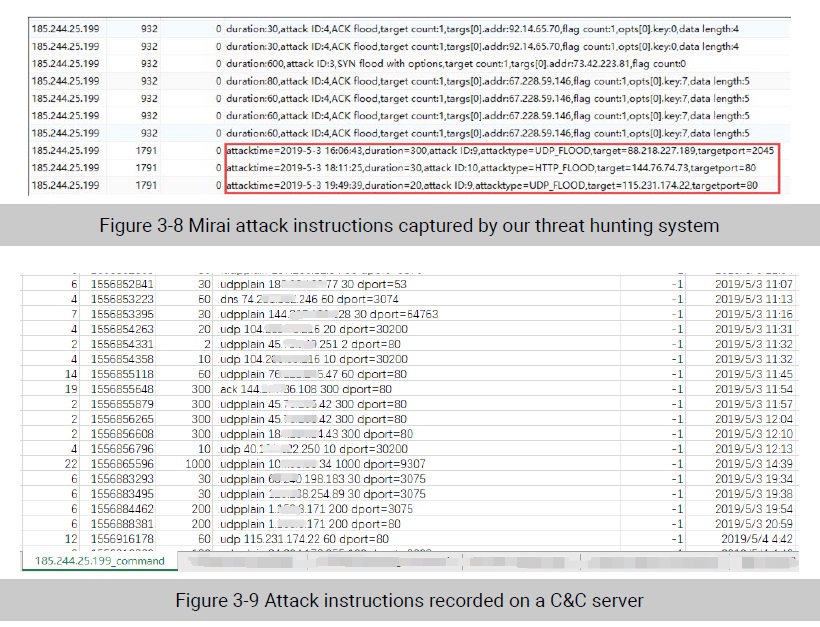
There is no overlap between our captured control instructions and attack instructions recorded on the actual C&C server in the same period. However, the IP address of the main control server is consistent.
Therefore, we can infer that database records obtained by NSFOCUS Security Labs were attack instructions issued by different C&C servers on the same main control server, rather than C&C servers under the monitoring of NSFOCUS Security Labs.
Nitol
Nitol has been a long standing active DDoS family on Windows platforms. It has a variety of variants due to the disclosure of source code in early years. In 2019, NSFOCUS Security Labs captured a total of 16 Nitol variants which included eight active ones, still mainly targeting various black and gray industries.
One of distinctive characteristics of the Nitol family is to deliver other malware mainly through update. In 2019, NSFOCUS Security Labs’ threat hunting system captured a total of over 6900 downloads by many Nitol variants, nearly 50% of which are related to self-update. The following figure shows the distribution of malicious families downloaded by Nitol.
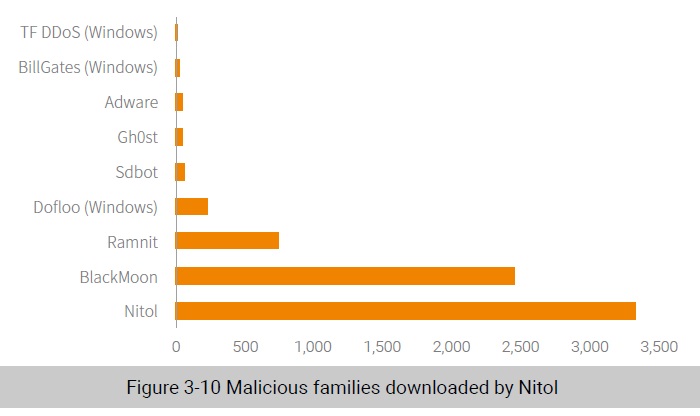
Nitol download platforms were largely located in China and also found in the USA, South Korea, and India. Statistics of malicious families of different types suggest that Nitol is correlated with various malware families.
More often than not, Nitol infection events are attributed to illegitimate software sources. Cracked software, tag-on software of games, various activation tools, and rogue software are hotbeds of Nitol and contribute to the spreading of this malicious family. Also, attackers, through vulnerability scanning, looked for devices with weak passwords and vulnerable remote access protocols, and then launched brute-force attacks against them in a bid to capture them in batches for Nitol propagation.
Conclusion
Malicious DDoS families like Gafgyt, Mirai, Nitol can wreak havoc on their target platforms:
- Botnets are being evolved into the model of botnet as a service (BaaS) which has attracted more attack service buyers.
- C&C servers are easier and quicker to deploy on cloud hosts and can be switched more flexibly.
- Botnet developers are more concerned about weaknesses of various platform environments and good at exploiting them. So many vulnerabilities in IoT platforms account for the activity of Gafgyt and Mirai. Also, the Windows-based network ecology breeds malicious families such as Nitol.
- Source code, once disclosed, can be modified arbitrarily to form a huge number of variants to exert a broader influence.
Besides, GoBrut is a brute-forcing family with the sole motive of seeking for vulnerable nodes on the public network. Its attack results will serve the front end of the kill chain, setting the scene for further attack events. This reveals the trend of current malicious botnet families with well-defined
responsibilities. Meanwhile, Persistently studying those botnet families with clearly assigned responsibilities is of great value to security event attribution.
To be continued.
