Analysis of IoT Attack Sources
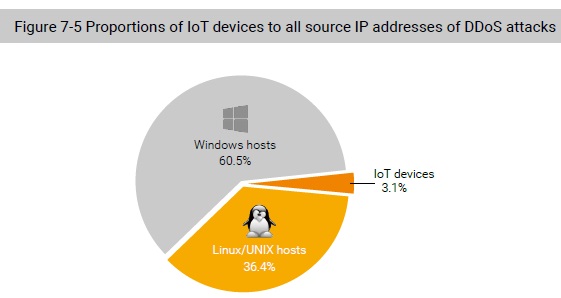
From NSFOCUS’s IoT threat intelligence, we can associate DDoS attack events with IoT devices. Further analysis of IoT devices compared to source IP addresses of DDoS attacks found that 3.14% of DDoS attackers are IoT devices. Though this proportion is relatively small, the number of DDoS source IP addresses is so staggering large that DDoS attacks based on IoT devices is a very significant threat.
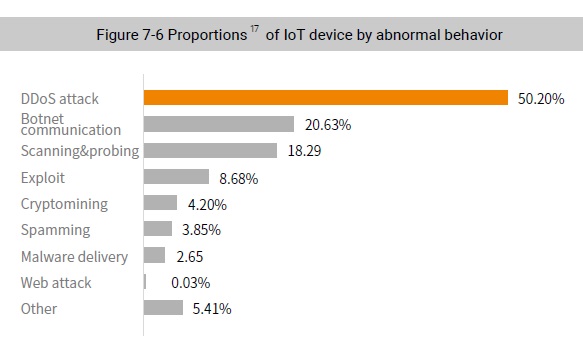
We found the total number of abnormal IoT devices was 408,685 worldwide, accounting for 0.94% of global IoT devices. Of those, 205,167 IoT devices were involved in DDoS attacks, making up 50.20% of the total number of abnormal IoT devices. As shown in Figure 7-6, DDoS attacks top the list of major malicious behaviors performed by IoT devices.
Conclusion
It is no surprise that threats keep coming. The nature and specifics may change but the threats do not stop. Most troubling about this is the interval between disclosure of a vulnerability and successful exploitation of the vulnerability no longer occurring in days or weeks but now within hours. This is becoming one of the greatest challenges to traditional security operations.
The number of DDoS attacks decreased in 2018 but their sizes and destructive effect increased almost exponentially. Attackers are becoming more efficient in their operations so we can expect much bigger attacks. Coupled with the growing availability of 5G networks, it is easy to imagine massive powerful bot armies available in the near future.
DDoS attacks themselves are changing. With governmental action, reflection attacks have ben greatly mitigated but other attack types quickly filled the void. How else will DoS attacks going forward?
Vulnerabilities are on the rise especially for IoT devices. More devices with more unaddressed vulnerabilities mean more threats coming. This is an area that needs greater attention and priority.
It is concerning that the threats are ever increasing but much of that is due to lack of oversight, lack of controls, and lack of attention from security vendors. If you build unsecure products, they will come and exploit them.