With the increasing complexity and frequency of cybersecurity threats, organizations face many network threats. The importance of threat intelligence has become increasingly prominent.
During this year’s RSA Conference, Sierra Stanczyk, the Senior Manager of Global Threat intelligence at PwC, and Allison Wikoff, the Director of Global Threat Intelligence for the Americas at PwC, shared “Connecting the Dots: Threat Intelligence, Cyber Incidents, and Materiality,” introducing the application of threat intelligence in the process of responding to cybersecurity incidents based on some practical cases.
Their insights resonate with our core beliefs at NSFOCUS, where we advocate for a proactive approach to safeguarding digital assets:
- The Importance of Context: Stanczyk and Wikoff highlighted how threat intelligence provides the essential context in incident response, enabling a more strategic and informed approach to cybersecurity.
- Regulatory Compliance: With new SEC regulations requiring prompt disclosure of significant cybersecurity incidents, accurate and timely threat intelligence is paramount.
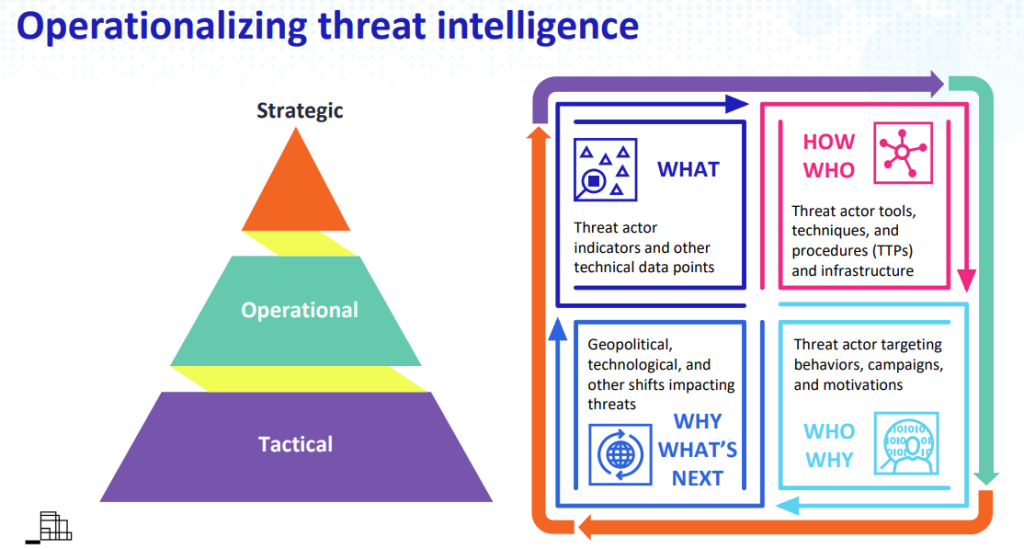
- Layered Threat Intelligence: The speakers proposed a pyramid model that categorizes threat intelligence into tactical, operational, and strategic levels, each offering unique insights for effective cybersecurity measures.
- Proactive Defense: By using threat intelligence to connect the dots between various security events, organizations can move from a reactive to a proactive stance, anticipating and mitigating threats before they escalate.
Here is a portion of the content from the speech.
I. Connecting the Dots
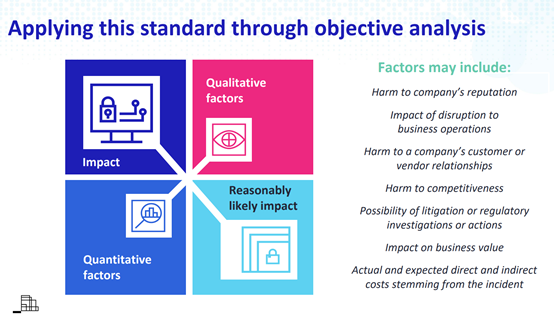
Stanczyk and Wikoff’s sharing began with the new regulations from the SEC (US Security and Exchange Commission). In December 2023, the SEC proposed a regulation on the disclosure of cybersecurity incidents. According to the regulation, when a significant cybersecurity incident occurs, organizations are required to submit detailed information about the incident and its potentially significant impact within four working days. However, the regulation does not clearly define the criteria for significant events. Therefore, the two sharers proposed that threat intelligence can be used in this link to assess the importance of events.
Stanczyk used a pyramid model to divide threat intelligence into three levels: Tactical, Operational, and Strategic. Tactical threat intelligence focuses on threat actor indicators and other data details, helping to predict or identify attack behavior as early as possible; Operational threat intelligence focuses on recording the attack methods (TTPs) of threat actors, helping to fully understand the implementation of attack activities and formulate response strategies; Strategic threat intelligence involves the behavior, motives of threat actors, and their possible next actions.
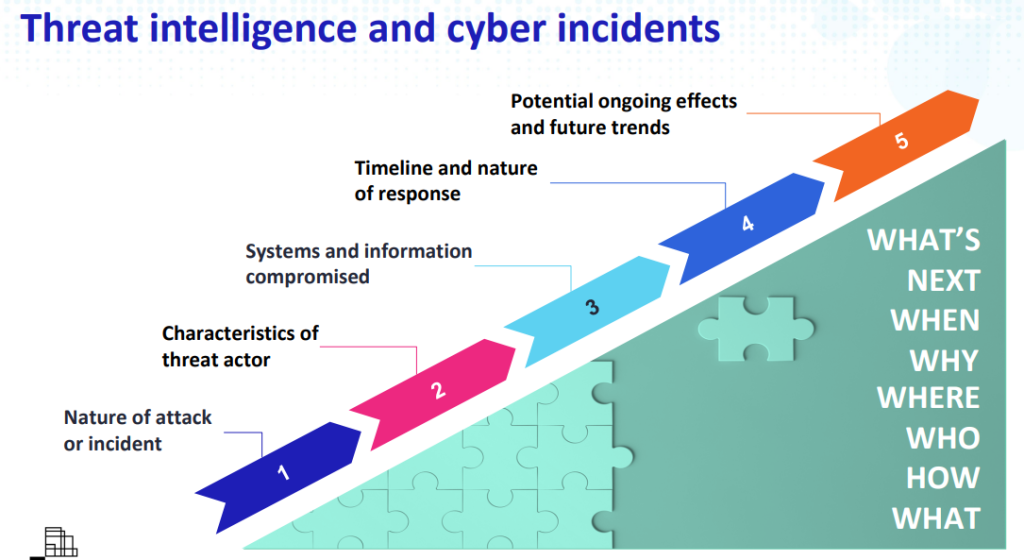
By connecting a large amount of fragmented information, the intelligence at these three levels runs through the entire process of incident analysis, providing five aspects of information for responders, including:
- Nature of the attack or incident
- Characteristics of the threat actors
- Systems and information compromised
- Timeline and nature of response
- Potential ongoing effects and future trends
Using these five types of information, responders can quickly understand the ins and outs of cybersecurity incidents.
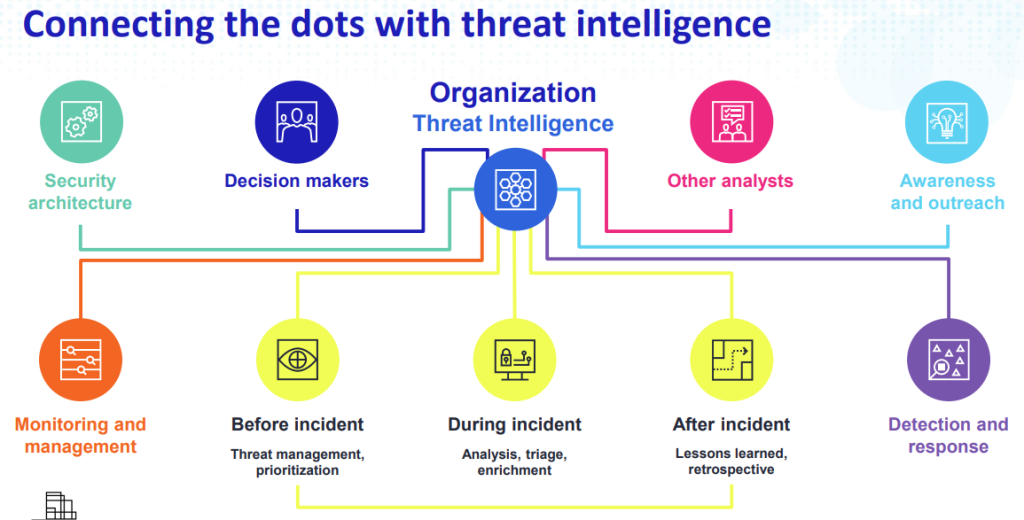
Stanczyk stated that in a company or organization, the value of threat intelligence can be reflected in many links. Including threat management before and after the incident handling process, prioritization, analysis, correlation, and other tasks like daily monitoring, detection, security architecture design, decision-making, etc. The three levels of threat intelligence can provide valuable information to all roles from security responders to decision-makers.
Then, Stanczyk and Wikoff used five cases to demonstrate the value of threat intelligence in analyzing and judging the importance of cybersecurity incidents. Here is one of them.
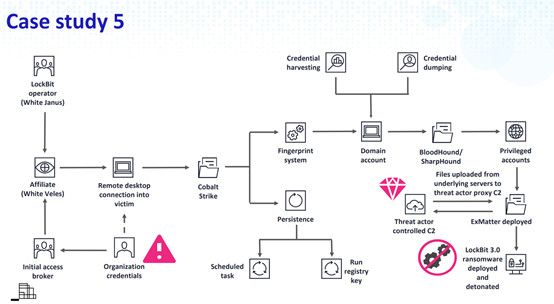
If traces of internal network penetration tools are found in a company’s system, and some strange scheduled tasks are also found, how to judge whether the company is currently under attack? What kind of handling strategy should be adopted? Is this incident a significant event that needs to be reported?
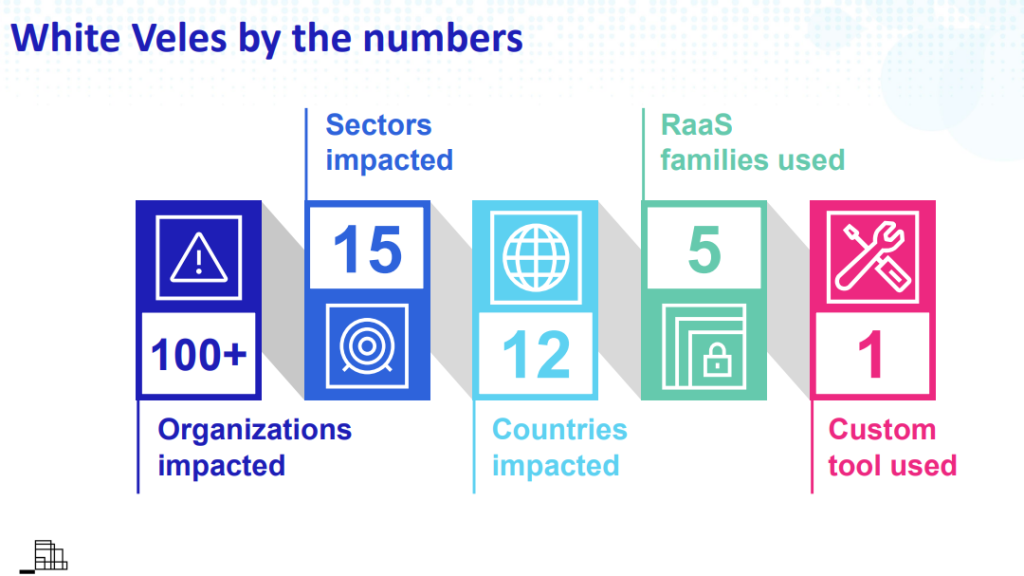
The figure above shows a typical ransomware attack process. Before the attack occurs, the victim can only find a few clues in the few links in the figure. Based on these few pieces of information, it is difficult to make a global judgment. In fact, this may be a ransom attack from a notorious hacker group, and many companies have already suffered from ransom, resulting in huge losses. The company’s network has been invaded and has become the next ransom target of the hacker group. With the aid of threat intelligence, known clues can be associated with the hacker group’s preferred attack tools, so as to discover and handle them in time.
In addition to the above case study, the speakers also listed four other typical scenarios, including Phishing, APT attacks, identity theft with the help of AI, and dark web data leaks. Threat intelligence can be of great help in dealing with these typical issues.
Then, Stanczyk shared how to build a threat intelligence capability foundation, which mainly includes five steps: forming a threat intelligence team, establishing close internal communication, granting appropriate internal authority, setting intelligence priorities, and obtaining rich external intelligence sources.
Finally, the speakers concluded that the context of an event is the key to the process of event handling, and threat intelligence plays an important role in providing context.
II. From Reactive to Proactive: Transforming Cyber Defense with Threat Intelligence
As cyber-attacks get more complicated, organizations can struggle to handle cybersecurity problems. Threat intelligence collects a lot of information from different places. This helps make sense of what’s happening during an incident, like piecing together a puzzle. It’s like helping someone who can’t see the whole picture to understand what’s really going on. This can not only be reflected in the process of judging the importance of events shared by Stanczyk and Wikoff but also greatly help organizations adopt a more proactive defense strategy.
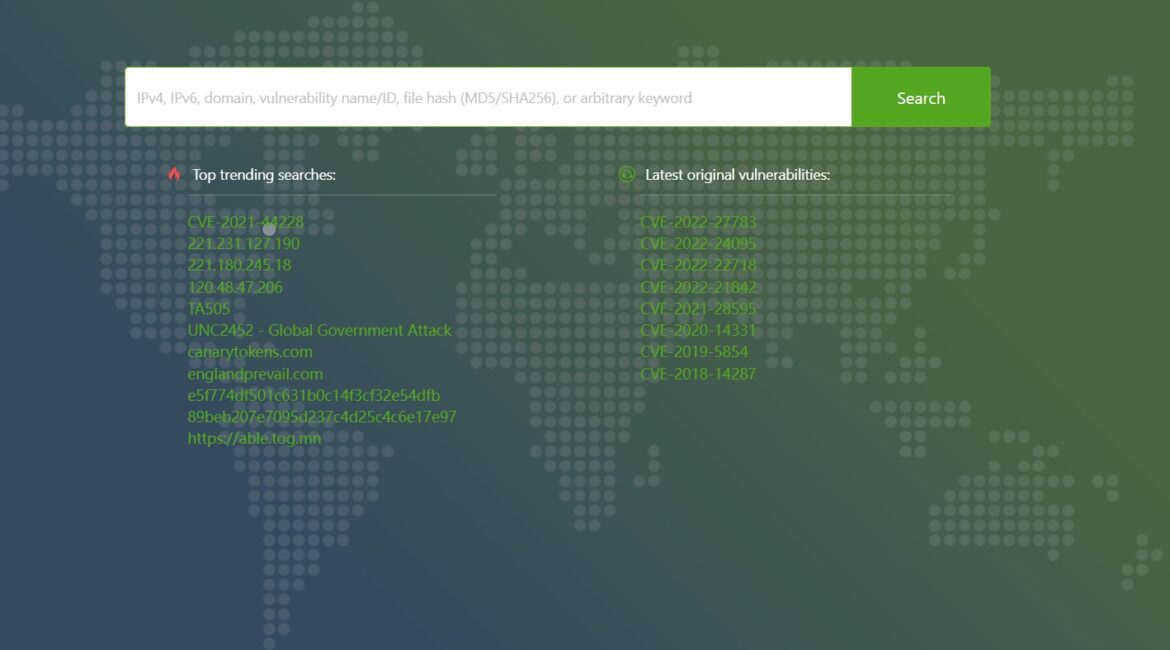
For example, in phishing attacks, threat intelligence can be used to associate and retrieve malicious links and samples after receiving a phishing email, in conjunction with cyberspace mapping, to carry out batch blocking in a more proactive manner.
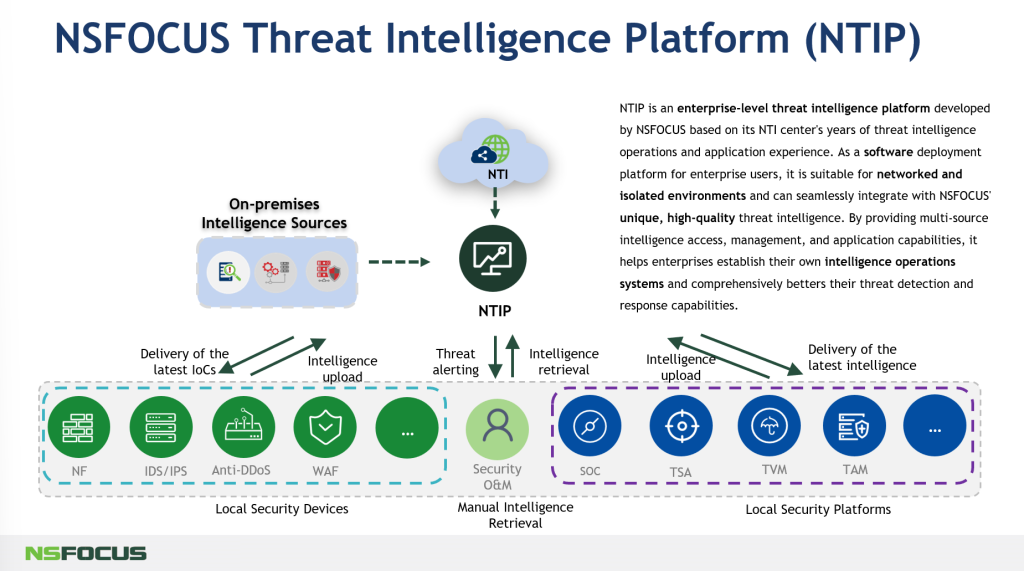
NSFOCUS Threat Intelligence (NTI) service and NSFOCUS Threat Intelligence Platform (NTIP) provide intelligence data on the current hotspots of cybersecurity events, including APT, mining, anti-fraud, ransom, dark web, and compromised intelligence, to realize intelligence-driven monitoring of key cybersecurity events and enhance proactive defense capabilities.
NSFOCUS’s TI service and platform empowers organizations to:
- Assess Incidents Quickly: With real-time intelligence, organizations can rapidly evaluate the significance of cybersecurity events and respond accordingly.
- Prioritize Threats: By understanding the context and potential impact, our platform helps prioritize threats based on their severity and likelihood.
- Enhance Decision-Making: Leveraging multi-sourced intelligence, our platform equips decision-makers with the data needed to make informed choices about their security posture.
- Implement Strategic Defenses: By anticipating future trends and potential attack vectors, NSFOCUS Threat Intelligence Platform supports the development of strategic defenses that stay one step ahead of threats.
For inquiries regarding NSFOCUS Threat Intelligence Platform (NTIP), don’t hesitate to reach out to us.