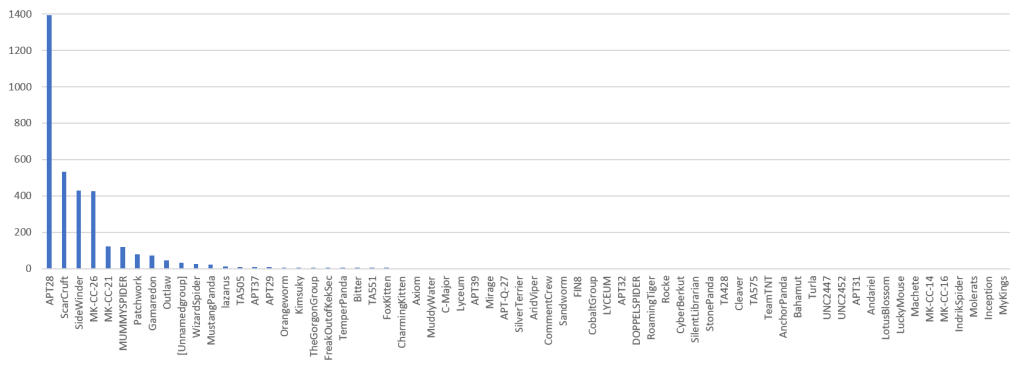
From December 5, 2022 to December 18, 2022, NSFOCUS Security Labs found activity clues of 66 APT groups, 3 malware families (MoonBounce Trojans, Razy Trojans and the CoinMinder), and 509 threat actors targeting critical infrastructure.
APT Groups
Among the 66 discovered APT groups, the APT28 affected the most significant number of hosts from December 5 to December 18, 2022.
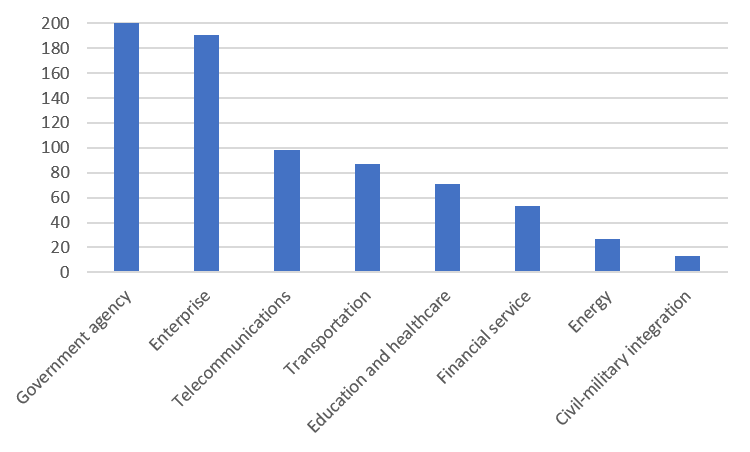
Threat Actors Targeting Critical Infrastructure
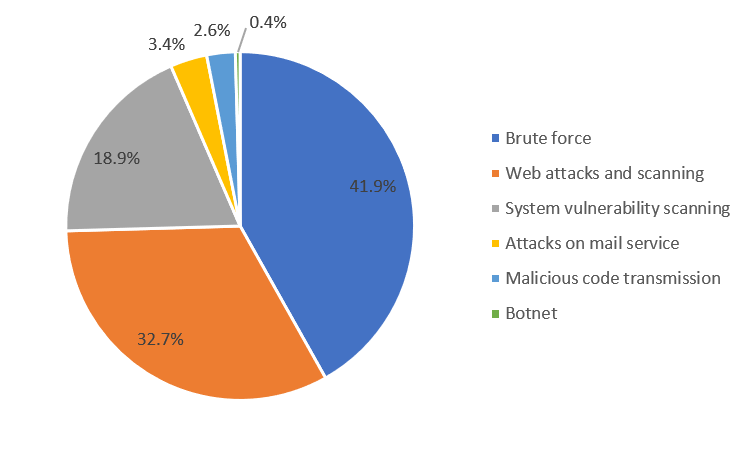
A total of 509 threat actors targeting critical infrastructure remained active in this period.
Knowledge Graphs of Highlighted APT Groups
APT28
First Discovery Time: 2020-11-13 07:38:40
Description: APT28 is a famous cyber espionage group. Some researchers believe this organization belongs to the GRU of the Russian Federation. APT 28 is also known as Sofacy Group and STRONGIUM, and its main targets are aviation, national defense, government agencies and international organizations.
Geolocation of Threat Actor: RussiaÂ
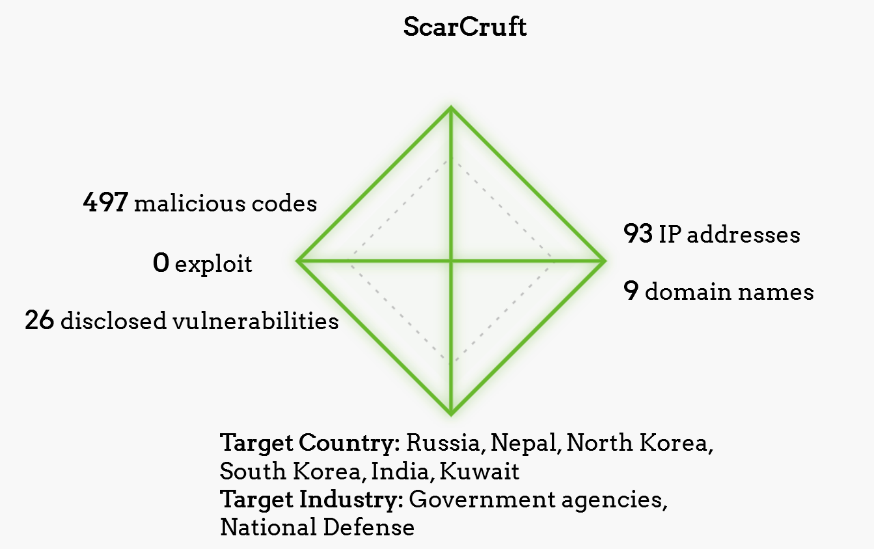
ScarCruft
First Discovery Time: 2018-12-10 16:00:00
Description: ScarCruft is a relatively new APT group; victims have been observed in several countries, including Russia, Nepal, South Korea, India, Kuwait and Romania. The group used to use spear phishing attacks to gain profits. ScarCruft has exploited multiple vulnerabilities, including zero-day vulnerability (CVE-2016-0147) exploitation for attacks on Adobe Flash and Microsoft Internet Explorer.
Geolocation of Threat Actor: North KoreaÂ
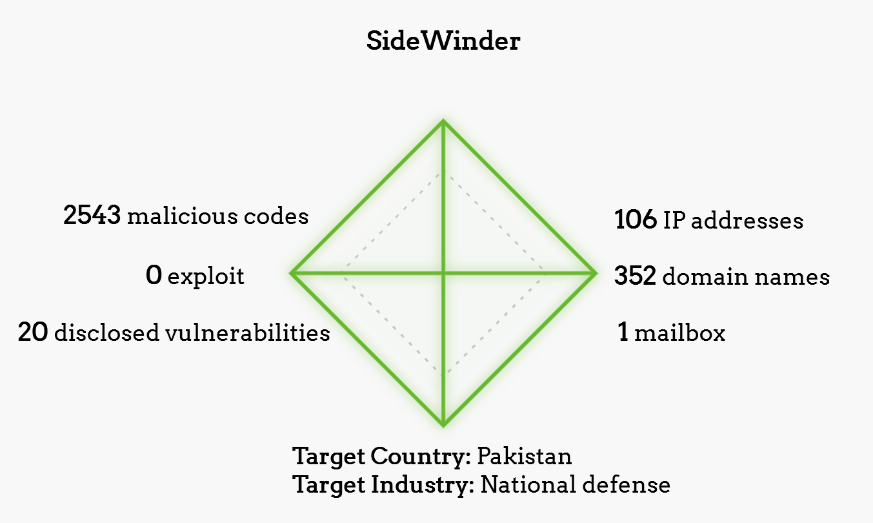
SideWinder
First Discovery Time: 2020-02-12 03:10:54
Description: An actor mainly targeting Pakistan military targets, active since at least 2012.
Geolocation of Threat Actor: IndiaÂ
About NSFOCUS Security Labs
NSFOCUS Security Labs (NSL) is an internationally-recognized cybersecurity research and threat response center at the forefront of vulnerability assessment, threat hunting and mitigation research.