Overview Recently, Apache Dubbo was reported to contain a remote code execution vulnerability (CVE-2020-1948) resulting from deserialization. Apache Dubbo is a high-performance Java RPC framework. The vulnerability exists in hessian, a default deserialization tool used by Apache Dubbo. An attacker may trigger it by sending malicious RPC requests which usually...
Blog
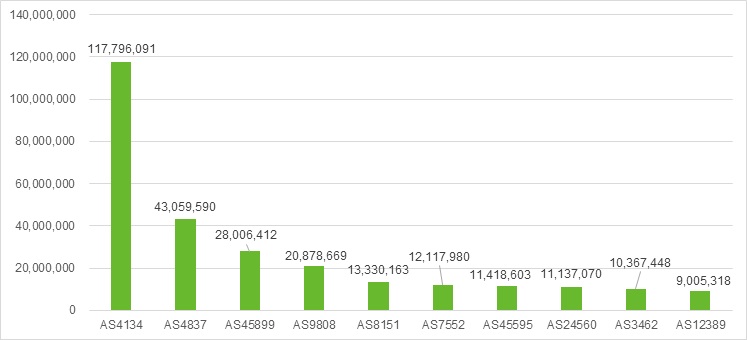
IP Reputation Report-06282020
1ã€Top 10 countries in attack counts: (mais…)
2019 Cybersecurity Insights -6
Deserialization vulnerabilities are still frequently exploited for web attacks and special attention should be paid to the security of mainstream frameworks. This section describes web vulnerabilities that had an extensive impact in 2019: WebLogic In 2017, Oracle released an official patch that fixed the XMLDecoder vulnerability (CVE-2017-10352) in WebLogic Server....
2019 Cybersecurity Insights -5
Web Attack Trend Websites, which enterprises or individuals use to provide services for users, are usually the first choice of hackers during attacks. Web attacks in 2019 clung to traditional patterns and methods, including server information disclosure, resource leeching, cross-origin resource sharing (CORS), SQL injection, and cookie poisoning, which together...
2019 Cybersecurity Insights -4
Vulnerability Trend By November 27, 2019, the National Vulnerability Database (NVD) had recorded 11,633 CVE vulnerabilities disclosed in 2019, including 6549 high-risk ones. The annual total number decreased year by year in the past three years compared with 15,881 in 2017 and 15,861 in 2018, but that of high-risk ones...
Microsoft’s Security Patches for June 2020 Fix 130 Security Vulnerabilities
Overview Microsoft released the June 2020 security patches on Tuesday that fix 130 vulnerabilities ranging from simple spoofing attacks to remote code execution in various products, including Adobe Flash Player, Android App, Apps, Azure DevOps, Diagnostics Hub, HoloLens, Internet Explorer, Microsoft Browsers, Microsoft Edge, Microsoft Edge (Chromium-based) in IE Mode,...