Vulnerability Trend
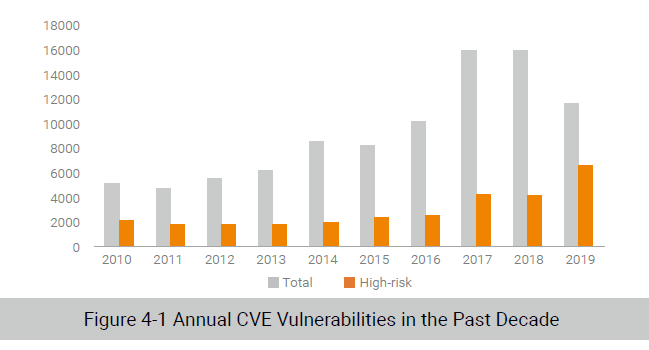
By November 27, 2019, the National Vulnerability Database (NVD) had recorded 11,633 CVE vulnerabilities disclosed in 2019, including 6549 high-risk ones. The annual total number decreased year by year in the past three years compared with 15,881 in 2017 and 15,861 in 2018, but that of high-risk ones was on the rise.
According to the classification criteria of Common Weakness Enumeration (CWE), the following categories of vulnerabilities took top 10 spots on the 2019 list.
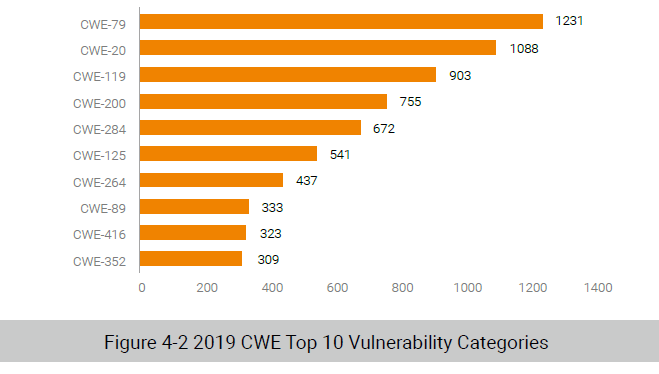
CWE-119 (Improper Restriction of Operations within the Bounds of a Memory Buffer), CWE-125 (Out of-bounds Read), and CWE-416 (Use After Free) are all related to out-of-bounds memory operations, together contributing 1767 vulnerabilities, which could be exploited to execute arbitrary code. These categories are often seen in browsers and Office software and also the major targets and weapons of APT attackers. CWE-264 (Permissions, Privileges, and Access Controls) and CWE-284 (Improper Access Control) are related to privileges, under which 1109 vulnerabilities were disclosed in 2019, mainly in server operating systems, database applications, and some widely adopted open-source content management systems (CMSs). Traditional web attack methods are never forgotten. CWE-79 (Cross-site Scripting (XSS)), CWE-89 (SQL Injection), and CWE-352 (Cross-Site Request Forgery (CSRF)) are often seen in servers and web applications, which could allow attackers to tamper with website data by injecting malicious scripts into web pages. CWE-200 (Information Exposure) is another category that has quite a few vulnerabilities found in the past year. By exploiting such a vulnerability, an attacker could obtain sensitive information, such as system configuration information and database information, which may aid in further attacks.
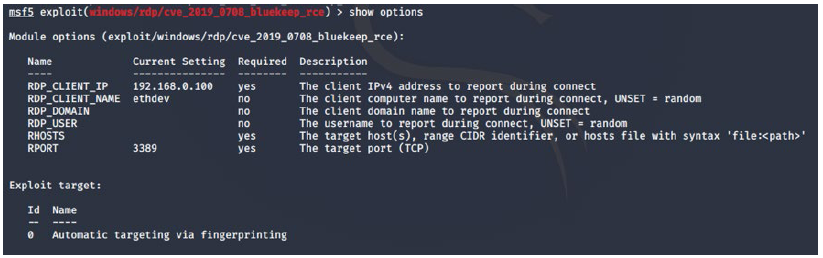
When it comes to topical vulnerabilities in 2019, the Microsoft remote desktop service vulnerability naturally jumps into our minds. On May 14, 2019, Microsoft released an emergency security alert, announcing remediation of a critical vulnerability (CVE-2019-0708) in Windows Remote Desktop Protocol (RDP). This vulnerability does not require authentication or user interaction and so is “wormable”. Specifically, this is a use-after-free vulnerability. When an RDP connection is set up, the RDP server creates an MS_T120 static virtual channel by default, which is bound to the 0x1F channel index. Then, if the RDP client requests binding of the MS_T120 channel to a specified channel index, the MS_T120 channel will be bound to two indexes, leading to two independent references. This way, when the client requests freeing of the MS_T120 channel, the related references will be deleted to free the object. The truth is that, when the RDP connection is closed, the MS_T120 channel of 0x1F will also be freed. As this object space has been freed before, referencing it again will trigger the use-after-free vulnerability.
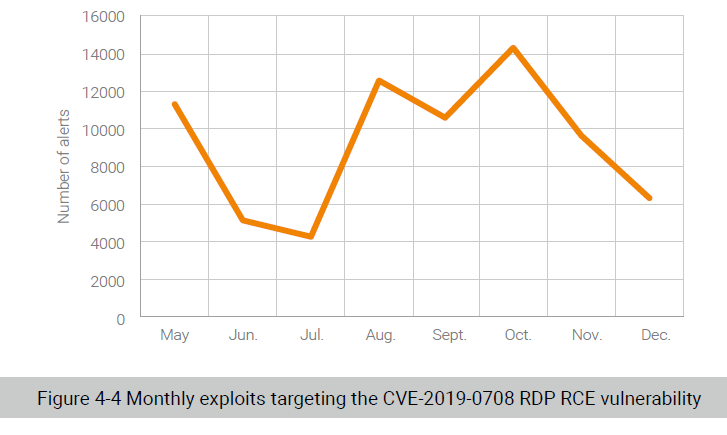
On September 7, 2019, Metasploit made the exploit module of this vulnerability, cve_2019_0708_bluekeep_rce.rb, known to the public. This module targets 64-bit Windows 7 and Windows Server 2008 R2. From the options shown in the following figure, obviously, an attacker could launch a targeted attack by setting RHOSTS, RPORT, and target. By far, our devices have generated 56,827 alerts on attacks launched by exploiting this vulnerability.
Exploit Trends
Server Exploits
Server vulnerabilities mainly reside in system services and programs that run on a server to support or deliver network management and actual business. Related exploits mainly target web servers, including Apache, Tomcat, and WebLogic. Most websites hold valuable information, such as credit card numbers, email addresses, and passwords, making them attractive targets for attackers.
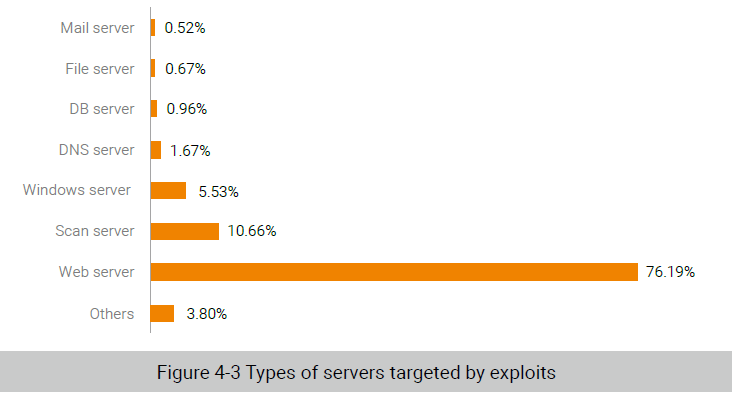
What comes in second is the scan server, followed by the Windows server. The related exploits mainly target such network services as the Server Message Block (SMB), Remote Procedure Call (RPC), Internet Information Services (IIS), and RDP. The exploit of the MS17-010 SMB remote vulnerabilities, since its disclosure by Shadow Brokers, has been integrated into a number of worm families. In the past two years, this exploit has topped the list of all Windows server-related exploits detected by our devices. Unlike previous years, 2019 saw a breakout of RDP exploits, represented by those targeting the CVE-2019-0708 vulnerability.
Application Exploits
Application software provides document, multimedia, host management, and other functions. Typical examples of such software are clients (such as browsers and email clients), antivirus software, office suites, Flash players, and PDF readers. Exploits targeting applications are conducted by delivering malicious programs via phishing emails that contain malicious links or attachments. Once a user clicks such a link or opens such an attachment, the vulnerability in the target program will be triggered, causing the device to be infected and information to be disclosed.
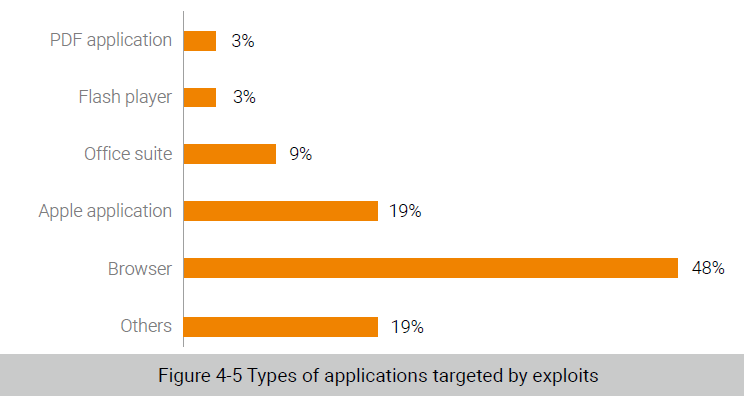
Of all application exploits, browser exploits accounted for 48%, most of which targeted Microsoft’s Internet Explorer/Edge and Google Chrome. Vulnerabilities in browsers are mainly caused by improper handling of memory objects by scripting engines, including JavaScript, VBScript, WebKit, and the newcomer WebAssembly.
Exploits of vulnerabilities in Apple applications increased to 19% from 0.6% in 2018. On August 29, 2019, Google’s security team Project Zero disclosed five exploit chains and 14 related vulnerabilities in Apple systems from iOS 10 to the latest iOS 12. From the system time, it can be inferred that these attackers had been active for at least two years.
Office vulnerabilities are one of hackers’ favorite targets. Most APT groups also choose to exploit highrisk vulnerabilities in Office. Most security events breaking out in the past few years have been found to exploit the OLE2Link object logic vulnerability, EQNEDT32.EXE vulnerability, and Encapsulated PostScript (EPS) vulnerability. Besides, hackers could attack their targets via a Word attachment that contains malicious Flash animations. Though small in number, vulnerabilities in Flash can pose a serious threat as they are frequently exploited. What is worse is that related exploit techniques have been further improved since Hacking Team disclosed the two zero-day vulnerabilities, CVE-2015-5122 and CVE-2015-5199.
To be continued.
