Deserialization vulnerabilities are still frequently exploited for web attacks and special attention should be paid to the security of mainstream frameworks.
This section describes web vulnerabilities that had an extensive impact in 2019:
WebLogic
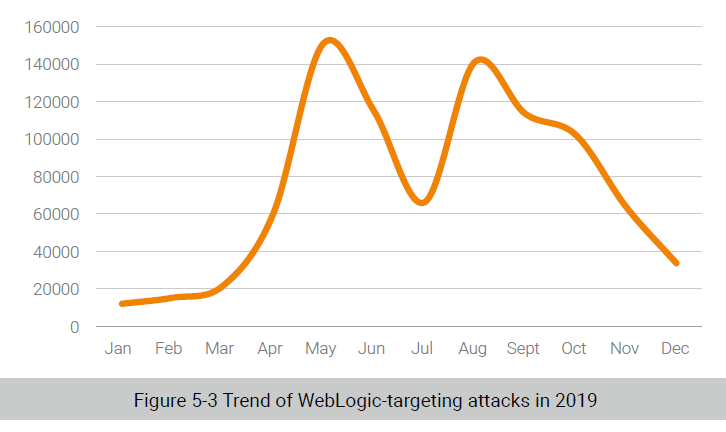
In 2017, Oracle released an official patch that fixed the XMLDecoder vulnerability (CVE-2017-10352) in WebLogic Server. This patch was evaded twice by exploits targeting two vulnerabilities (CVE-2019-2725 and CVE-2019-2729), sparking new rounds of WebLogic-targeting attacks. The two vulnerabilities reside in components built in WebLogic and could be exploited without authentication. With carefully crafted XML data in the SOAP format, an attacker could trigger the two vulnerabilities via an HTTP request. The two vulnerabilities, due to the high exploitability, are favored by hacking groups. According to statistics, after Oracle released the official security patch in April, the proof of concept (PoC) of the vulnerability (CVE-2019-2725) was publically available, encouraging a marked increase in attacks against WebLogic. Later, researchers discovered that the security patch was circumvented by an exploit (CVE-2019-2729). Obviously, the official remediation did not work, resulting in attacks reaching the culmination in May.
JSON framework
In 2019, vulnerabilities were frequently disclosed in third-party JSON libraries for Java. Most JavaWeb applications have employed the efficient third-party JSON libraries for JSON data parsing, but version upgrades of the libraries are often overlooked during the running of applications. Thus, particular attention should be given to the security of third-party libraries.
- Fastjson is an open-source JSON parsing library provided by Alibaba. This library works efficiently and therefore is widely used. On one hand, security issues with Fastjson due to untrusted deserialization have been fixed multiple times since 2017. On the other hand, related remediation patches were evaded constantly. In 2019 alone, 36 blacklisted entries were newly added for Fastjson to prevent insecure deserialization, suggesting the continuously escalating battle between remediation and evasion. Users should check the official security bulletins from time to time to get the related patch as soon as possible and strictly control the switch of the AutoType function, leaving it disabled.
- Likewise, the Jackson library lacks proper sanitization of user input, which could be exploited for malicious parsing of related classes, thus leading to arbitrary code execution. In 2019, six blacklisted classes were newly added for Jackson. Users should upgrade to the latest version as soon as possible to prevent this kind of attacks.
Others
- ThinkPHP 5.x was reported to contain a remote code execution vulnerability requiring no authentication to exploit. This vulnerability had an extensive impact in China as a large number of websites were hit by hackers through injection of malware such as cryptomining scripts and malicious trojans.
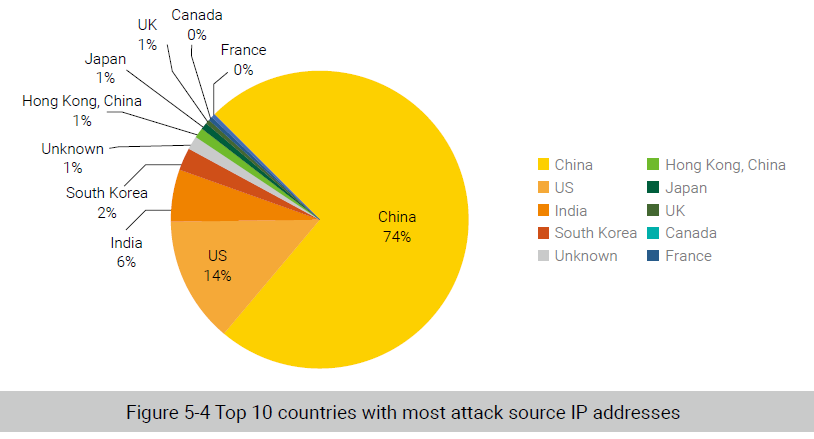
From the above figure, we can see that 75% of attackers hitting ThinkPHP were sourced from China. This is because the ThinkPHP framework is more popular in China, according to the distribution of attack source IP addresses.
Nearly 50% of victims were from Beijing, followed by Shanghai, Fujian, and Jiangsu provinces.
- Jenkins is the most popular application for continuous integration. At the end of 2018, a remote code execution vulnerability requiring no authentication to exploit was disclosed in Jenkins. Since then, the popular Script Security plug-in installed by default in Jenkins has been repeatedly reported to contain a sandbox bypass issue. In response to such issues, security updates have been released, with the latest one seen in November 2019. As Jenkins is widely used in intranets, administrators should keep a close eye on security issues with Jenkins and its plug-ins.
- Apache Solr was reported to contain five high-risk vulnerabilities, including deserialization, command injection, denial-of-service, and template injection vulnerabilities. Obviously, close attention should be paid to the security of Apache Solr, a widely used indexing/search integration application.
- Traditional office automation (OA) systems have gained renewed attention. Weaver OA, Seeyon OA, and Office Anywhere were found to contain high-risk vulnerabilities that were widely exploited during penetration tests. Apparently, the security of traditional OA systems still cannot be overlooked.
Sum-up: The year of 2019 saw multiple remote code execution vulnerabilities that required no authentication to exploit, including the WebLogic XMLDecoder deserialization vulnerability, ThinkPHP remote code execution vulnerability, Apache Solr remote code execution vulnerability, and Atlassian Jira template injection vulnerability. These vulnerabilities were most favored by hacking groups that integrated the exploit code in a mature attack framework or a trojan to make it easier to take advantage of such vulnerabilities. Also, the time between vulnerability PoC announcement and mass exploitation is shortened, posing a greater challenge to security vendors’ protection capability.
To be continued.
