A BGP hijacking event happened again! Following the event that the traffic supposed to be destined for Europe was leaked to China Telecom (June 9, 2019), another BGP hijacking occurred yesterday (June 25, 2019). Since Verizon, by mistake, accepted network misconfigurations by a minor Internet Service Provider (ISP), multiple Internet systems have fallen into a black hole. For example, Cloudflare, Facebook, and Amazon Web Services (AWS) among other companies experienced system failures. This raised public concerns of Border Gateway Protocol which a routing protocol for the Internet.
In fact, this is a large network security issue often talked about. BGP hijacking events, though less frequently than other security events, basically occurred each year to have a significant impact. There are few means and tools to detect and track this kind of events in China. Today, we will dwell upon BGP hijacking issues.
I What Is BGP Hijacking?
BGP is a dynamic routing protocol. Simply put, BGP is a protocol for backbone routers to synchronize routes. In other words, backbone routers around the globe forward network traffic mainly based on BGP routing tables. No wonder BGP counts a great deal.
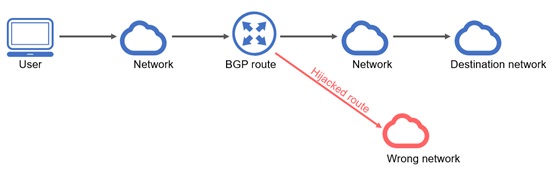
BGP hijacking is an act of an attacker exploiting defects (insufficient authentication on unconditional trust between BGP neighbors) in BGP to maliciously alter the routing table for ill intentions. This can be compared to this case where an attacker stealthily alerts your navigation map when you are driving in navigation mode, directing you to follow the path predefined by the attacker. In such as case, you may reach unexpected destinations if you are not familiar with road conditions. In the cyberspace, BGP routing tables are equivalent to network maps. Acts of maliciously alerting BGP routing tables are called BGP hijackings.
You can imagine that if you, following a problematic navigation map, drive to a place with nobody or with terrorists, you will feel horrible. This is the same case for network traffic. If routes along with traffic is transmitted are alerted maliciously, “special things” are likely to occur, such as access to a forged online bank, Taobao website, or e-government website, where a public loss may be incurred.
Next, we will use an example to explain how a BGP hijacking is implemented.
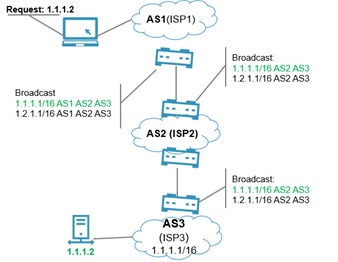
As shown in the first figure, the user has proper access to 1.1.1.2 through AS1, AS2, and AS3.
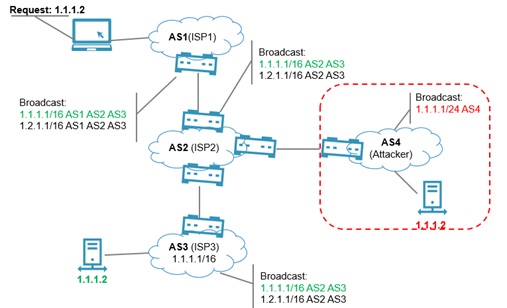
As shown in the second figure, AS 4 has a BGP neighborship with AS 2 and broadcasts 1.1.1.1/24. According to the longest prefix matching rule, requests will arrive at AS 4 through AS 1 and AS 2.
II Which BGP Hijacking Events Are Reported?
In this bustling world, all are pursuing their own interest. Then, what is the purpose of attacks with BGP hijackings?
As mentioned above, once large network routes are altered, any traffic can be hijacked to attacker-controlled destinations for malicious intents. BGP hijacking events reported in recent years can be classified as follows:
-
BGP hijackings for economic interests
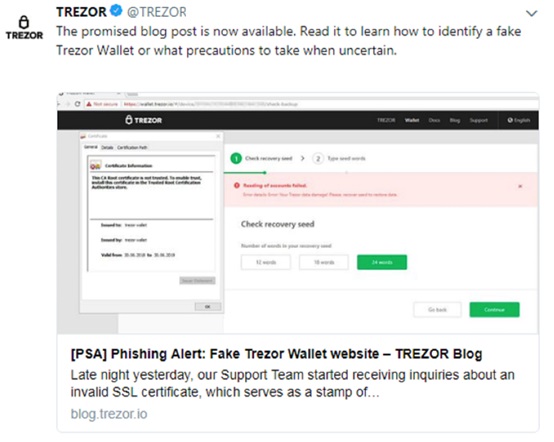
In July 2018, the Bitcoin website TREZOR believed that its traffic was hijacked to a phishing website, as shown in the following figure.
Also in July, 2018, traffic of three US payment companies, Datawire, Vantiv, and Mercury, was hijacked to malicious servers for attackers to steal data. Besides, two hijacking events occurred on July 10 and 13, in which the attacker hijacked Ukrainian traffic to Holland.
On April 24, 2018, Amazon suffered BGP route hijacking events that affected Australia and the USA, in which attackers were motivated to steal Bitcoins. The following figure shows the distribution of traffic in affected (yellow) and unaffected areas (green).
-
BGP hijackings owing to manual BGP misconfigurations
The YouTube hijacking event in 2018 is the most famous. At that time, to prevent a controversial video, Pakistan Telecommunication Company Limited (PTCL) advertised a route to divert YouTube’s global traffic to Pakistan, causing the website to be disrupted for about two hours.
In August 2018, Google admitted that due to their BGP configuration error, traffic that was supposed to be destined to ISPs such as Verizon went to Google, leading to approximately 8 million users disconnected from the Internet for 40 minutes, giving rise to a panic.
On November 6, 2017, Level 3’s configuration error resulted in a 90-minute widespread Internet outage in the USA and around the world.
-
BGP hijackings due to suspected human errors
On November 16, 2015, the Indian carrier BHARTI Airtel suffered a route leak that led over 2000 AS networks to fail for as long as nine hours in India, China, the USA, Japan, and Saudi Arabia.
On April 3, 2014, Indosat, an Indian carrier, experienced an extensive route hijacking, causing traffic sent from and to Indonesia, Thailand, and the USA to be blocked for three hours.
On February 27, 2012, the Australian carrier Telstra encountered a route leak, with the result that people in this country were cut off from the Internet for half an hour.
III Harm Done by BGP Hijacking Events
BGP hijacking events publicly reported are classified and some are enumerated in the preceding part of the text. We believe that there are definitely BGP hijacking events that are not detected or reported. Then, what harm can these events do to users?
- In anomalous traffic routing events, carriers seeing abnormal traffic are actually victims.
The mistransmission of volumetric traffic is actually a denial-of-service attack against the victim carrier because such heavy traffic not only occupies valuable network resources, but also causes network congestion, thus reducing the business processing speed or interrupting the network, and even affects other normal links, devices, networks, and business of the carrier.
- Malicious hijackings may incur a significant economic loss to enterprises and end users.
If normal traffic is hijacked to a phishing website or server, there is a possibility that data is stolen or typed with.
IV How to Prevent BGP Hijackings?
Since BGP hijackings bring severe issues, what precautions and tools can be used to prevent them?
-
Establishment and application of new specifications
In response to BGP route hijacking issues, the security industry currently advocates the Resource Public Key Infrastructure (RPKI) solution. Based on RPKI, IETF proposes Border Gateway Protocol Security (BGPsec), a full AS path validation mechanism. In a word, BGPsec is to advertise routes through BGP, with an authentication mechanism. This means that only authenticated routes are advertised. RPKI has been approved by Ministry of Industry and Information Technology (MIIT) and related projects have been reported for approval by MIIT. We believe that RPKI will be promoted and find wide application.
-
Data encryption
Data encryption, to a certain extent, compounds the difficulty in taking advantage of leaked data. Currently, Internet traffic shows a trend towards switching to HTTPS. However, once a route is hijacked, it is not impossible to decrypt traffic that is encrypted as it has been proven through practice. This topic was already presented at the BlackHat conference held in 2015 and I will not go into details here.
-
Traffic detection system for big networks
As route hijackings are intended to alter original routing paths, we can monitor large networks with route modeling and machine learning among other technologies, to discover route hijacking behavior promptly through analysis of route hijacking events using a network path model for large networks in normal conditions which is generated by a collection of algorithms.
Currently, there is no product available to detect and analyze BGP route security events in China. With luck, the next-generation NTA, after launched, may be the first product in China to include BGP route security analysis. For more information on NTA, you can contact the product manager (Peng Chang at mobile numbers 17628042978).