1 Vulnerability Overview
Recently, The Apache Software Foundation announced the existence of a denial-of-service (DoS) vulnerability in Apache Tomcat HTTP/2. Specifically, the HTTP/2 implementation accepts streams with excessive numbers of SETTINGS frames and also permits clients to keep streams open without reading/writing request/response data. Thus, too many connection requests from clients can cause server-side thread exhaustion. Successful exploitation of this vulnerability would result in a denial of service on the target.
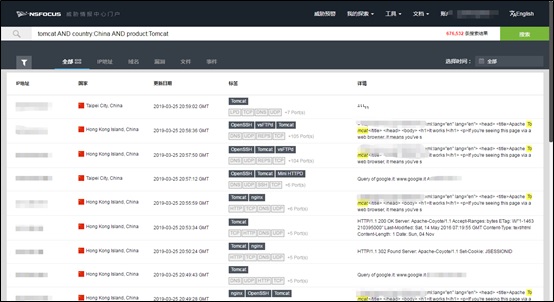
Tomcat is an important project of The Apache Software Foundation. Owing to its stable performance and availability for free use, it is quite a popular web application server. Considering the widespread deployment of Tomcat, the vulnerability in question affects a large number of users. Enterprises using Tomcat should attach importance to this issue. According to data from NSFOCUS Threat Intelligence center (NTI), the number of Tomcat-enabled assets publicly available in China exceeds 600,000.
Reference link:
https://www.mail-archive.com/announce@apache.org/msg05156.html
2 Scope of Impact
- Affected Versions
- 0.0.M1 < Apache Tomcat < 9.0.14
- 5.0 < Apache Tomcat < 8.5.37
- Unaffected Versions
- Apache Tomcat 9.0.16
- Apache Tomcat 8.5.38
3 Check for the Vulnerability
3.1 Version Check
Generally, the file name of a Tomcat installation package downloaded from the official website of Apache Tomcat contains the version number. Users can find out the current version number by checking the decompressed folder name.
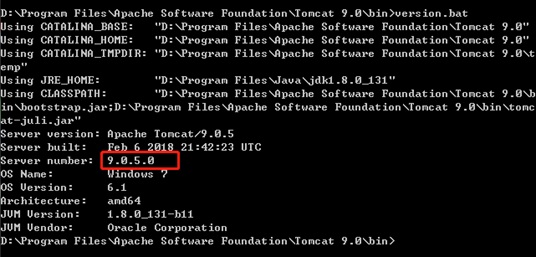
If the decompressed Tomcat folder name was changed, or the package was installed with Windows Service Installer, users can query the current version number by using the version module that comes with the software. For a Windows system, in the command line window, enter the path to the bin folder of the Tomcat installation package and type the version.bat (version.sh for Linux) command. Then the current version number of Tomcat is displayed.
If the version of your installation is within the affected scope, please upgrade it as soon as possible.
4 Vulnerability Protection
4.1 Version Upgrade
The Apache Software Foundation has fixed this vulnerability in the new releases of Apache Tomcat 9.0.16 and 8.5.38. If you are affected by this vulnerability, please upgrade your installations as soon as possible. For the links to the downloadable new releases, see the following table. You can download an appropriate installation package according to your system environment.
| Version | Download Link |
| Apache Tomcat 9.0.16 | https://tomcat.apache.org/download-90.cgi |
| Apache Tomcat 8.5.38 | https://tomcat.apache.org/download-80.cgi |
Note: Before upgrading the application, you should make a backup of data and the operating environment in case the upgrade renders the system unusable.
Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.