Recently, by using the Attack Trend Monitoring system (ATM), the NSFOCUS security team has discovered an Apache Axis remote command execution vulnerability, which allows attackers to obtain privileges of the target server and remotely execute commands without authorization by sending a crafted HTTP-POST request.
Apache Axis is an open-source XML-based web service framework. It consists of a Java and a C++ implementation of the SOAP server, and various utilities and APIs for generating and deploying web service applications. Using Apache Axis, developers can create interoperable and distributed computing applications.
-
Scope of Impact
Affected Versions
- Apache Axis <= 1.4
-
Vulnerability Check
3.1 Manual Check
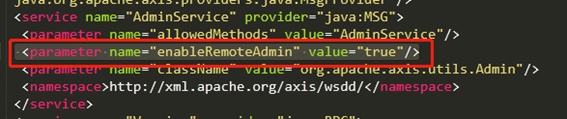
Axis users can locate the server-config.wsdd file in the website directory and then open it with a text editor. If the value of enableRemoteAdmin is true, it indicates that this vulnerability exists.
-
Vulnerability Protection
Protection with Security Products
4.1.1 Customer-Side Product Protection
To defend against this vulnerability, NSFOCUS has released rule update packages for its security products. Users are strongly recommended to update rule bases to the latest version to ensure that these security products can effectively protect against this vulnerability. The following table lists rule base versions of NSFOCUS security products.
| Product | Rule Base Version | Update Package Download Link | Rule ID |
| NIPS | 5.6.8.784 | http://update.nsfocus.com/update/downloads/id/29480 | 24508 |
| 5.6.9.20521 | http://update.nsfocus.com/update/downloads/id/29486 | ||
| 5.6.10.20521 | 9http://update.nsfocus.com/update/downloads/id/29487 | ||
| WAF | 6.0.7.0.41869 | http://update.nsfocus.com/update/downloads/id/29482 | 27526167
27526168 |
| 6.0.5.1.41873 | http://update.nsfocus.com/update/downloads/id/29484 | ||
| 6.0.4.1.41873 | http://update.nsfocus.com/update/downloads/id/29485 |
For how to update rule bases, click the following links:
NIPS: https://mp.weixin.qq.com/s/JsRktENQNj1TdZSU62N0Ww
WAF: https://mp.weixin.qq.com/s/oubjPqR4DURWPvrQ9W9mWA
- Workarounds
4.2.1 Deleting Axis
If Axis is not needed in the current system, delete the axis.jar file in the lib directory. Users are advised to back up the file before deleting it, so as to avoid service interruption.
4.2.2 Disabling Axis Remote Management
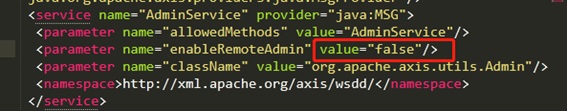
Locate the server-config.wsdd file in the website directory and open it with a text editor. Then set enableRemoteAdmin to false.
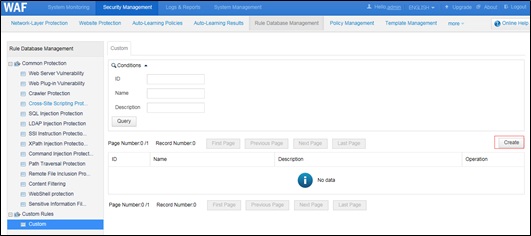
4.2.3 Custom Protection Rule on NSFOCUS WAF
NSFOCUS Web Application Firewall (WAF) users can set a custom rule for temporary protection. The procedure is as follows:
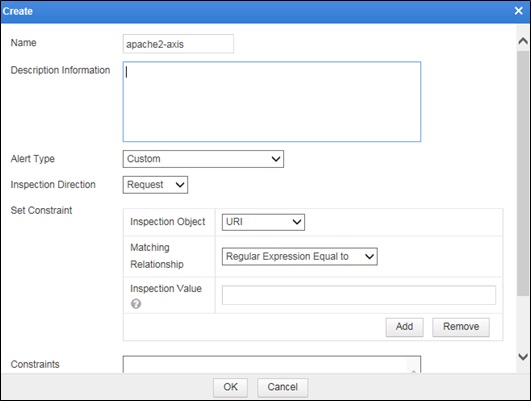
Choose Security Management > Rule Database Management > Custom Rules > Custom and click Create.
In the dialog box that appears, set Inspection Object to URI, Matching Relationship to Regular Expression Equal to, and Inspection Value to /services/(AdminService|FreeMarkerService.
Apply this custom rule to virtual websites (if any).
The verification is as follows:
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.