In early March, NSFOCUS Cloud Scrubbing SOC team discovered that one of our customers in Latin America suffered a volumetric, multi-vector distributed denial-of-service (DDoS) attack. NSFOCUS Cloud DPS prevented this attack successfully. The captured entire attack and defense process is as follows:
March 3, 10:00 a.m. GMT+8
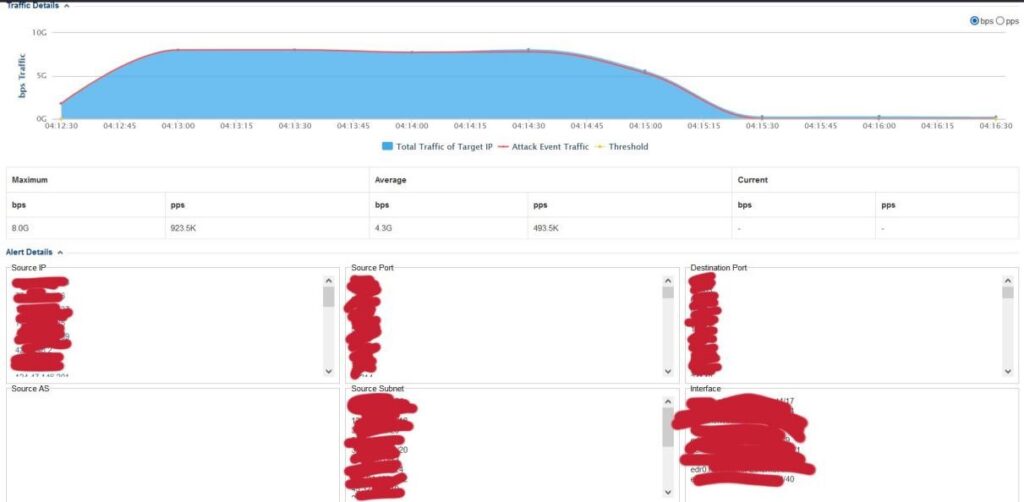
NSFOCUS cloud-based Network Traffic Analyzer (NTA) detected a burst of traffic flooding to one of our Telco customers in South America.
The DDoS attack this time is large scaled with its traffic exceeding the limit set in protection policies previously. NSFOCUS NTA sent an alert to NSFOCUS Cloud DPS to trigger attack traffic scrubbing immediately. Â
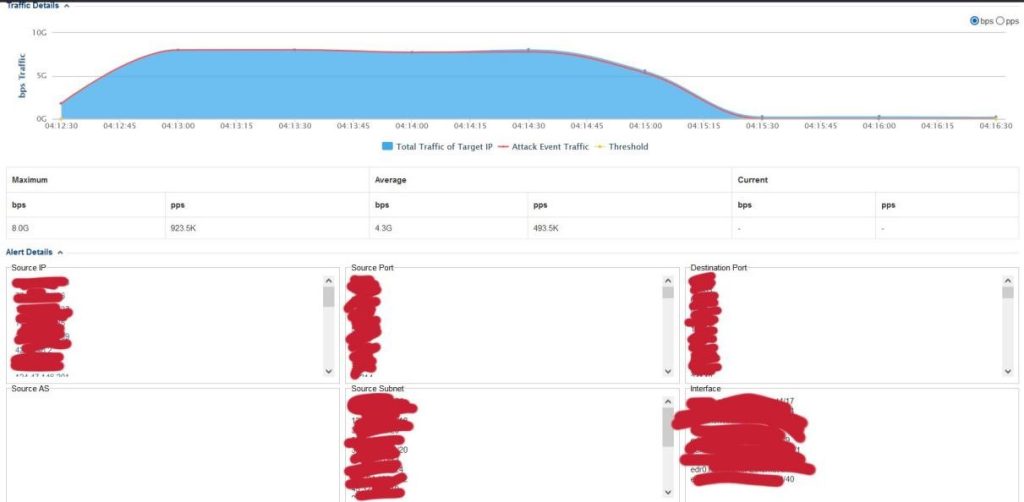
March 3, 12:00 p.m. GMT+8
The attack traffic reached the peak of 66.9 Gbps. With real-time detection and protection of NSFOCUS Anti-DDoS solution, all of attack traffic was filtered out while 1Gbps clean traffic was sent back to the customer’s original path.
March 3, 1:00 p.m. GMT+8
The attacker’s subsequent DDoS attack failed as NSFOCUS’s defense had been put in place effectively. While the customer’s business kept continue all the time during the attack, the attacker finally gave up the attack. This attack lasted over three hours, with total attack traffic up to 1TB. NSFOCUS’s outstanding security products, security operations team, and incident emergency response team once again won a great battle against the attacker by working seamlessly.Â
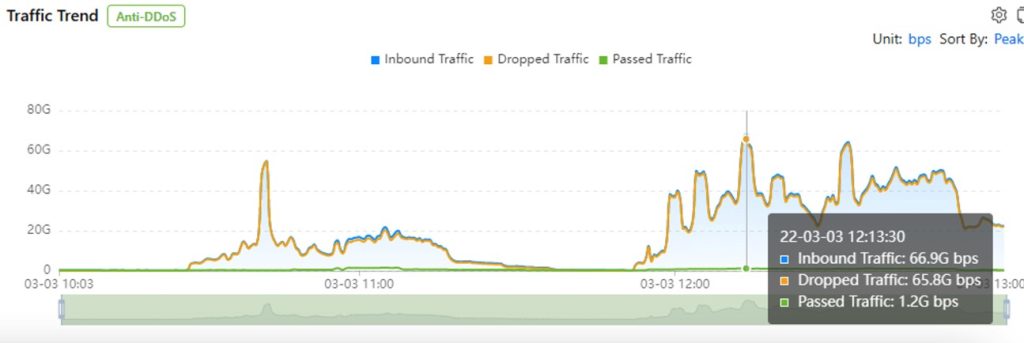
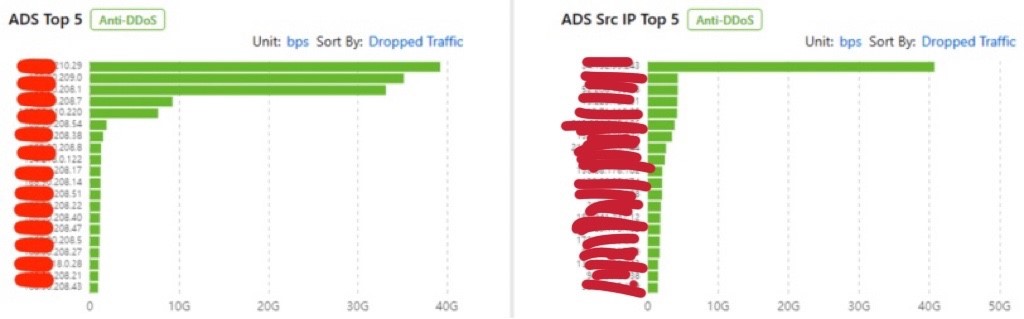
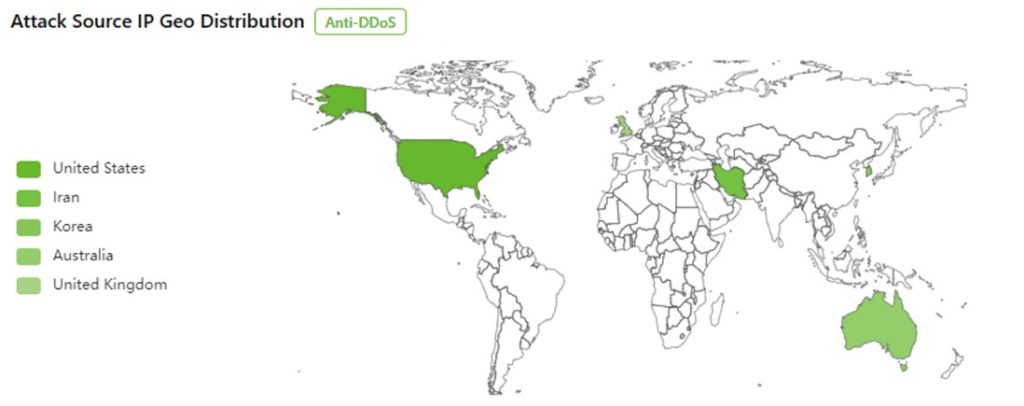
After the attack, the NSFOCUS Security Labs traced back the attack sources and found that carpet-bombing vector was also used together with UDP amplification.
The carpet-bombing attack targets a range of addresses or subnets of an organization within a very short period of time. it can easily evade detection because the attack traffic received by each individual IP address is too low to trigger the baseline in typical DDoS mitigation solutions. But the total attack traffic may be volumetric and massively impact a victim’s network. Fortunately, NSFOCUS has fine-tuned protection policies specific to the telco industry. Coupled with the advanced protection algorithms, NSFOCUS is fully capable of fending off the multi-vector attacks for our customers.
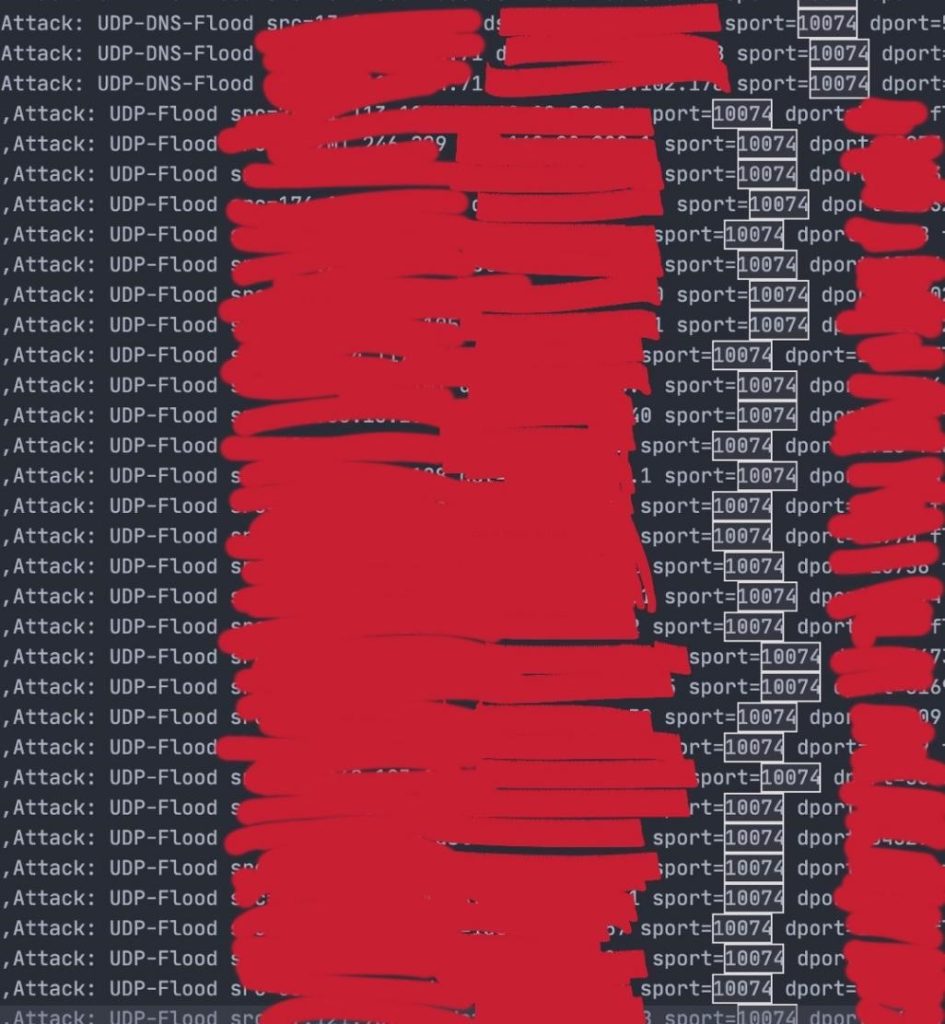
From the attack logs, we can see that the source port of the UDP reflection attack is 10074, which is in line with the characteristics of the recently discovered CVE-2022-26143, dubbed TP240PhoneHome, a vulnerability in the TP-240 (aka tp240dvr) component in Mitel MiCollab and MiVoice Business Express. This vulnerability allows remote attackers to obtain sensitive information and cause a denial of service (performance degradation and excessive outbound traffic). Theoretically, threat actors can use this vulnerability to launch denial-of-service (DDoS) attacks with record-breaking amplification ratio of 4,294,967,294 to 1. Mitel has released a security advisory warning its users that this vulnerability may cause significant outbound traffic impacting availability of other services when exploited.
NSFOCUS Cloud DDoS Protection Service offers terabit capacity to ensure customers can get sufficient network and mitigation capacity during mass-volume amplification attacks, without risking its traffic to be redirected to blackhole by force. Customer also enjoy always-on mitigation mode with no extra cost to gain minimum time-to-mitigate when carpet-bombing DDoS attacks arrive.
For more info about NSFOCUS Cloud DPS, contact us at https://nsfocusglobal.com/company-overview/contact-us/