Incident Review
In February 2019, our monitoring found that some domestic users, when accessing certain websites through their home routers, were hijacked to pornographic and gambling websites. According to our sample inspection, more than 4 million IP addresses were hijacked to about 190 domain names concerning pornography and gambling during this incident. These victim users were supposed to open their intended websites, but redirected to another unexpected page.
In such a situation, most users’ first reaction is often “Is my computer infected with a virus?” In fact, a virus can cause access problems on only one computer, while such “hijacking” can affect hundreds of computers at the same time. To make clear this issue, let’s first see how domain names work.
How Domain Names Work?
As we all know, a domain name is the website address typed in the address bar of a browser when we visit a website. In fact, every website server has its own IP address which is not easy to remember. For example, the IP address of NSFOCUS’s website server is 47.88.23.30 (here CDN is ignored because the IP address may be different if the CDN is used). It is troublesome to type http://47.88.23.30 to visit the website each time, and therefore https://www.nsfocus.com.cn is used to represent the website.
However, visiting a server on the Internet is essentially connecting to the IP address of the server. Therefore, domain name resolution is a process to translate a domain name into the corresponding IP address, and the process needs to be done with a domain name system (DNS). Figuratively speaking, DNS is just like an address book in which a one-to-one mapping is formulated between hard-to-remember numbers (IP addresses) and easy-to-remember names (domain names).
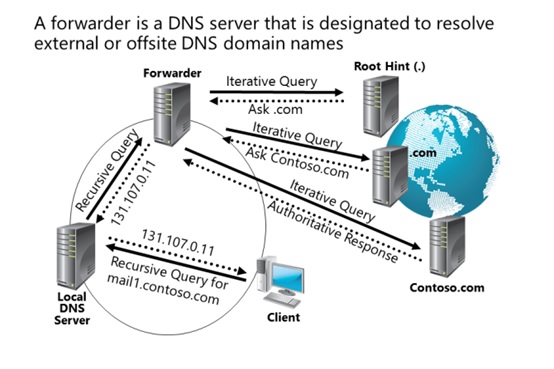
Then, how does DNS work? It is well known that there are countless websites on the Internet, and almost every day Some go live and some go out of service. Therefore, it is obviously impossible to use a DNS server to store the “address book” of all websites. For this reason, we will adopt iteration and recursion to resolve domain name. The DNS server configured on our computer (client) is usually a recursive DNS server. As soon as receiving a DNS query request from a computer, the recursive DNS server looks for the corresponding IP address before returned it to the computer. DNS servers, however, usually perform domain name queries in an iterative manner. Here, we take “blog.nsfocus.com” as an example to describe the DNS query process.
- The computer (client) sends a query request to DNS server S. This server first checks its own cache and returns the result if corresponding records exists.
- If not, server S first sends a query request to root domain name server A. Server A replies, “For .com domain names, please query top-level domain name server B.”
- Server S sends a query request to top-level domain name server B. Server B replies, “For the domain name nsfocus.com, please query second-level domain name server C”.
- Server S sends a query request to server C which will then replies, “I find it. The IP address is *. *. *. *” (Record A). After that, server S stores this correspondence between the domain name and the IP address in the cache and returns it to the computer.
How Domain Name Hijacking Works
-
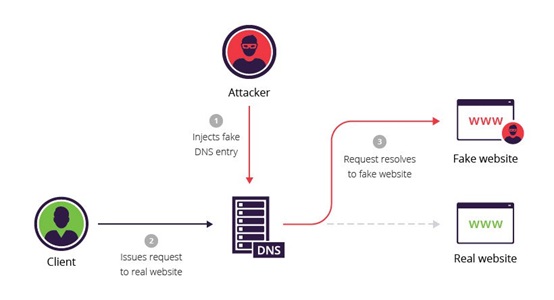
DNS cache pollution
Domain name hijacking refers to a process in which an attacker intentionally crafts some improper DNS packets to attack a specific DNS server to induce the server to cache fake correspondences between IP addresses and domain names. In this case, when a user queries a domain name whose fake correspondence is already cached in the DNS server, the server no longer sends iterative queries to other servers, but returns the existing records. This process is also dubbed “DNS cache pollution” or “DNS cache poisoning”.
-
Tampering with the default DNS address
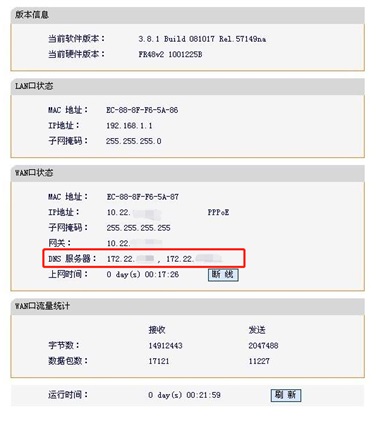
In addition, there is another way of domain name hijacking, in which an attacker exploits vulnerabilities in a computer or home router to change the default DNS server setting on the computer or router. This incident announced by CNCERT is an attack of this kind.
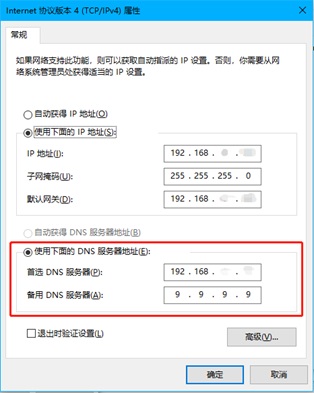
For the default DNS address of a computer, we can set it in the networking property dialog box as shown in the following figure:
For the default DNS address of the router, we can set it on the administrator configuration page of the router as shown in the following figure:
If the DNS server specified above is changed to one controlled by an attacker, the user’s query requests will be directed to the malicious server, leading to a serious security impact.
Three Different Types of Attack
Once the DNS server setting is tampered with on the user’s computer or router, the user’s request to query related domain names will be directed to a malicious server controlled by the attacker. However, whether the server will further send query requests or directly return the wrong correspondence depends on the specific needs of the attacker.
Now, we will explain how an attacker achieves malicious purposes through a DNS hijacking. In terms of the degree of harm and discovery difficulty, we divide DNS hijackings into three levels: entry level, advanced level, and expert level.
-
Entry level: Do not hesitate to come to our website.
Attackers of this type hope to redirect as many access requests as possible to their websites or servers by casting their net widely. The attack case described in this document is an example of such attack. More often than not, attackers with DNS hijackings intend to attract traffic to their websites in order to rake in more profits from advertisement browsing. What’s more, attackers can also divert users to malicious websites controlled by them and infect the victims with viruses in a bid to carry out further attacks.
Attacks of the entry level are easy to launch and identify. Once a user finds that he or she is diverted to a certain website no matter what domain name he or she accesses, the user should consider whether he or she is hit by such attack and check whether the default DNS settings on the computer and router have been manipulated.
-
Advanced level: Welcome to our website before access to your intended website?
Compared with the entry level, attacks of the advanced level are conducted in a more stealthy way. In such an attack, a user that attempts to access a desired website, is first brought to a web page crafted by the attacker, and then redirected to the website he or she is supposed to visit. The user, when being directed to the malicious web page, may trigger operations such as malicious program download and malicious script code execution.
As the user is diverted to another web page, his or her network access will slow down. If the user carefully watches the domain name, he or she will find that the domain name is changed for a little while. Judging from the domain name change, the user can identify the potential attack of the advanced level.
-
Expert level: Lurking in the dark to hit at the right moment
This type of attack, characterized by high elusiveness, is usually difficult to spot. In such an attack, a DNS server, even after being tampered with by an attacker, can still deal with most query requests and return correct query results. Once a user attempts to visit a certain website (for example, an e-banking website), he or she will be diverted to the IP address of the malicious server of the attacker. Meanwhile, the attacker carefully crafts a nearly identical web page to make it less likely to be seen through.
In this case, if a user who is supposed to visit a certain bank website enters his or her bank account information on the malicious website returned by a malicious DNS server, such account credentials will be submitted to the malicious website crafted by the attacker. With those account information in hands, the attacker can further steal the user’s property.
Defense Suggestions
At this time, we may think that DNS is inevitably an easy target of attacks. To reduce the risk of being hit by such attacks, we need to have proper security precautions in place, in addition to developing strong security awareness. Thus, NSFOCUS’s information security management department offers the following defense suggestions:
- Set a secure DNS server on the computer and router. For personal computers, we recommend you to choose 8.8.8.8 (provided by Google), 9.9.9.9 (provided by IBM) and 114.114.114 (provided by 114DNS of China). For working computers, we advise you to set the master DNS server to the DNS server (192.168. *. *) used by your company and the standby DNS server to one of public DNS servers above.
- Install computer security patches in time to prevent malicious programs from leveraging known computer vulnerabilities to execute DNS tampering.
- Regularly check and update the firmware of your home router. Remember not to use routers with many vulnerabilities, in case malicious programs leverage those vulnerabilities to manipulate your DNS settings.
- Change the default password of your home router to a more complex password, in case malware or attackers to log in to the background management page to manipulate your configurations.
When visiting an e-banking website or a website that contains sensitive information, we should carefully check whether the domain name is correct within the URL of the page loaded in the browser. Also, we should check whether unexpected contents (including pop-up pages like floating windows, advertisements, roughly made “bank reminders”) are shown on the page displayed in the browser. If anything abnormal is discovered, please check whether DNS settings has been manipulated, in accordance with the troubleshooting process mentioned above. Alternatively, you can seek professional assistance.