1.   Introduction
AI/ML is a hot topic in RSA Conference 2019. Current artificial intelligence (AI) can be roughly divided into perceptual intelligence (capabilities of perceiving images, audio, and video) and cognitive intelligence (knowledge-based reasoning and causal analysis). Most algorithms in use nowadays are perceptual.
How to equip AI systems with cognitive intelligence is still a nut that is hard to crack. As the first step towards this end, a knowledge base must be built. For example, to track an advanced persistent threat (APT), the defender hopes to infer the threat actor’s motive by cognitive intelligence that will enable automatic track of samples and variants. To achieve this purpose, an effective method is to use knowledge base modeling for threats.
The MITRE Corporation (MITRE) is an organization that has done well in this aspect. Initially, it was mainly responsible for doing threat modeling for the Department of Defense of the USA, with a view to intelligence analysis for anti-terrorism (according to a US government’s Act on enhancing the intelligence work after the 9/11 terrorist attack). Gradually, MITRE’s missions have been extended to the cybersecurity realm. The organization’s most distinctive work is classified modeling. A typical example of this is Structured Threat Information Expression (STIX), whose first version (STIX 1.0) reflects the requirements for anti-terrorism intelligence analysis. When working on STIX 2.0, MITRE found that tactics, techniques, and procedures (TTPs) alone could hardly describe cyberattacks and malicious code.
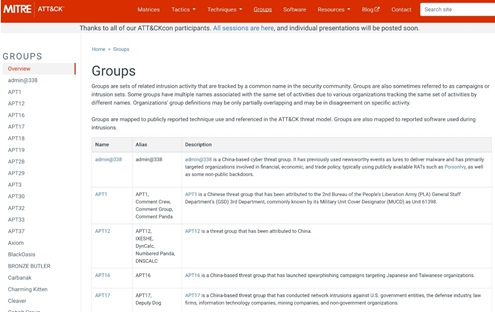
Therefore, the new version introduced two relatively independent representations for cyberattacks and malicious code, namely Common Attack Pattern Enumeration and Classification (CAPEC) and Malware Attribute Enumeration and Characterization (MAEC). However, the two representations are too abstruse to understand, so MITRE published the ATT&CK model and modeling dictionary in 2015 to optimize attack characterization. The model is more definite and expressive, incorporating CAPEC and MAEC to facilitate representation and sharing, security automation, and adoption of new AI technologies such as the knowledge graph. At its official website, MITRE enumerates TTP examples from 79 APT attack organizations (188 aliases). NSFOCUS is also working on a similar project and has built an even larger knowledge graph for automated track of APT organizations.
At RSA Conference 2019, Freddy Dezeure, CEO of Freddy Dezeure BVBA, and Rich Struse, Chief Strategist at Cyber Threat Intelligence of MITRE, detailed how to use the ATT&CK model to establish and improve the defense system in their joint presentation titled ATT&CK in Practice: A Primer to Improve Your Cyber Defense; Jared Myers, a senior threat researcher at Carbon Black, described how to use the ATT&CK model to hunt threats in his presentation titled How to Evolve Threat Hunting by Using the MITRE ATT&CK Framework.
2.   Tech-Savvy and Agile Adversaries
Freddy Dezeure started his presentation with an account of the destructive ransomware Petya. With an impact comparing with that of WannaCry, another notorious ransomware family, Petya broke out in June, affecting a number of countries. As a type of ransomware, Petya has an obviously destructive intent. However, its initial infection was achieved via some accounting software. After that, it exploited a leaked NSA tool (EternalBlue) for spreading. From this information, Freddy Dezeure drew an inference that future adversaries will be more agile and adaptive.
- Adversary infrastructure will be more adaptive to more different target environments.
- Attackers, after breaching a network, will blend in with legitimate users for the purpose of using legitimate infrastructure components, abusing legitimate credentials, or replicating legitimate user behavior.
- Attackers are quick in improving their capabilities and have a fast uptake of new vulnerabilities and leaked tools.
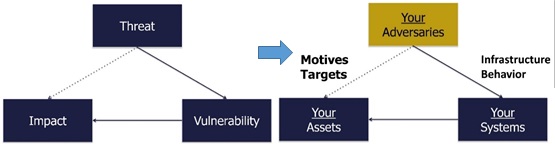
To cope with this situation, Freddy Dezeure recommended use of threat models to analyze problems. In a risk-based model, a threat enters a network or system via a vulnerability and then causes a negative impact such as extortion or data theft. To raise the research one level up, Freddy Dezeure switched the focus from threats to threat actors, that is, adversaries, who perform some operations by exploiting vulnerabilities to breach systems, with the intent of maliciously manipulating valuable assets.
Based on this threat model, defenders should perform the following three steps:
- Identify critical assets and know who would be interested in them and why.
- Maximize the benefit of observing adversaries’ infrastructure by increasing the quality and timeliness of indicators of compromise (IoCs) and making them actionable (course of action, COA).
- Observe adversaries’ TTPs and deploy them in prevention, detection, and response.
Freddy Dezeure put particular emphasis on the third step, which is crucial to the entire process of implementation. To successfully carry out the required actions, the ATT&CK model needs to be used for detection and prevention of and response to adversary TTPs.
3.   What Is ATT&CK?
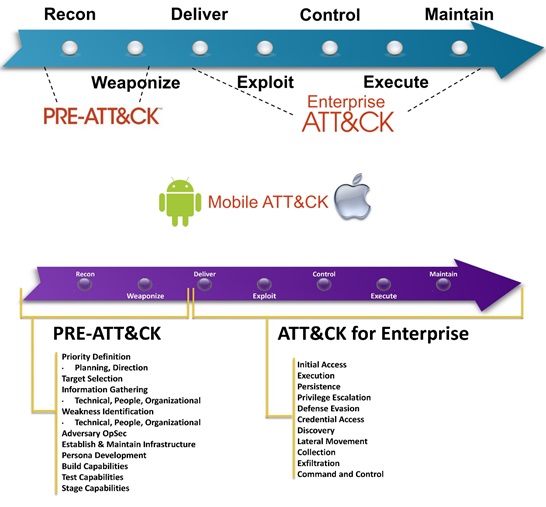
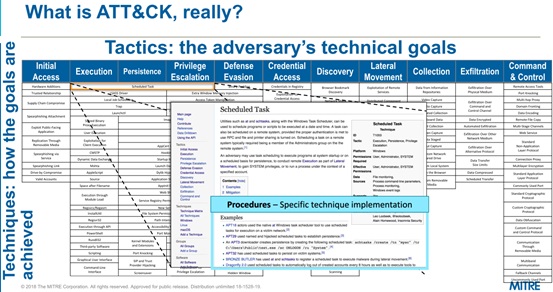
ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge)is a model and knowledge base of adversary behavior throughout the lifecycle of attacks. It originates from a project focused on enumeration and classification of TTPs used to compromise Microsoft Windows systems to improve detection of malicious activities. Currently, the ATT&CK model is divided into three parts: Pre-ATT&CK, ATT&CK for Enterprise, and ATT&CK for Mobile. The first part covers the first two phases of the kill chain and the second part covers the remaining five kill chain phases.
Pre-ATT&CK tactics include priority definition, target selection, information gathering, weakness identification, adversary OpSec, infrastructure establishing and maintaining, persona development, and capability building, testing, and staging.
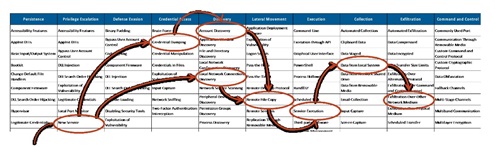
ATT&CK for Enterprise tactics include initial access, execution, persistence, privilege escalation, defense evasion, credential access, discovery, lateral movement, collection, exfiltration, and command and control (C&C).
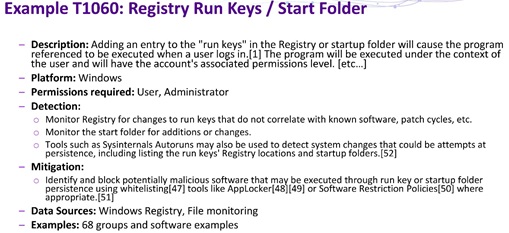
One technique may be used in multiple tactics. Procedures are implementation of a specific technique. For example, the “scheduled task” (T1053) technique can be used in execution, persistence, and privilege escalation. Freddy Dezeure used historical attacks of APT organizations to illustrate procedures. For example, APT3 used the schtasks /create /tn “mysc” /tr C:\Users\Public\test.exe /sc ONLOGON /ru “System” command to create scheduled tasks. A specific technique also contains other information, such as the targeted platform (Windows, Linux, or MacOS), privileges required for execution, detection method, and mitigation method.
MITRE ATT&CK enumerates and classifies these techniques to facilitate subsequent “understanding” of adversary behavior, for example, labeling critical assets that attackers are interested in, tracking techniques that attackers may use, or using threat intelligence to continuously observe attackers. MITRE ATT&CK also groups APT organizations and characterizes their TTPs.
According to Freddy Dezeure, ATT&CK, compared with other models, has its key added values in provisioning of common taxonomy that implements and covers specific techniques as required. It is not necessary to implement the entire matrix provided by the model, but is important to prioritize prevention, detection, and response measures. Besides, ATT&CK uses a common language to describe TTPs, provides a knowledge base of observed TTPs, and is continuously updated. It is vendor-agnostic and has been widely adopted by open-source communities.
4.   Practice
4.1Â Â Â Â Â Improving Prevention
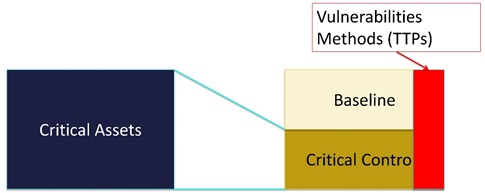
As for how to apply ATT&CK to actual defenses, Freddy Dezeure thought that it was important to first understand controllable parts on the defensive side. Attackers usually exploit vulnerabilities to breach a system. If they manipulate critical assets, some of their actions will trigger critical controls. Then by adapting and validating these critical controls, we will probably be able to capture attackers’ malevolent behavior.
To validate critical controls, we need to first check our own detection capabilities of:
- Identifying attack behavior from collected logs
- Designing an analytics system to analyze attacker-related knowledge, or referring to information gained from open-source communities
- Deploying an analytics program to detect and capture attack behavior as well as improving capabilities
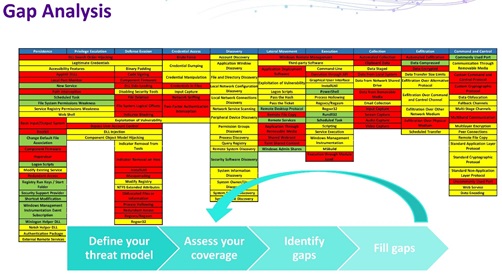
The next step is to analyze techniques used by known attacker groups and find out which techniques would impose the highest impact on critical assets.
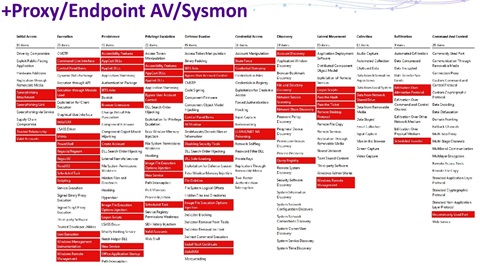
Subsequently, we should check whether our own detection capabilities are enough to cover key techniques, for example, whether the use of proxies, endpoint antivirus software, or system monitor logs can meet our own requirements.
Finally, an analytic procedure suitable for our own need should be established:
- Research those “techniques” that we are interested in and read related documents. Refer to current analysis or source code from open-source communities to distinguish between possibly legitimate and malicious behaviors.
- Use techniques that we are interested in to simulate attacks and then check whether and how these attacks are logged.
- Write query statements to search logs for events. Continuously test and iterate the function. Use related techniques to simulate various attacks so as to reduce false positives.
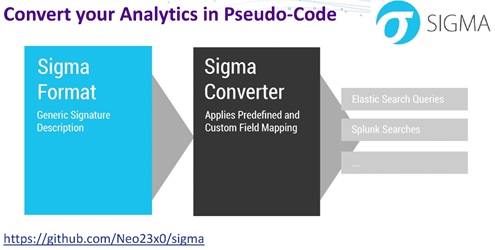
In log event search, Freddy Dezeure gave a brief account of the open-source project Sigma. Currently, IoCs and YARA rules are playing a major role in detection of malicious files and network connections, but there is no specific or generic detection method in log events. People collect log data for analysis. They usually start from reading a large number of documents before building their own search methods and rules for log data. Because of lacking a standardized format, they cannot share their work with others.
Sigma is a generic and open signature format, allowing people to describe relevant log events in a straightforward manner. Its rule format is very flexible, easy to write, and applicable to any type of log files. The main purpose of this project is to provide a structured form in which researchers or analysts can describe their previously developed detection methods and make them shareable with others. Writing rules and conducting searches in Sigma can avoid vendor lock-in. The current Sigma project provides log rules for APTs, applications, Linux, Windows, networks, proxies, and web.
In terms of adversary emulation, Freddy Dezeure introduced four ATT&CK-based attack test tools:
- MITRE Caldera: an automated adversary emulation system, which can perform malicious activities after compromising a Windows enterprise network.
- Endgame RTA: a Windows-specific Python script framework designed to allow blue teams to test their detection capabilities against malicious tradecraft, modeled after ATT&CK. It can generate evidence of over 50 different ATT&CK tactics, as well as a compiled binary application that performs activities as needed.
- Red Canary Atomic Red Team: a collection of atomic and highly portable, open-source tests that exercise the same techniques used by adversaries (all mapped to ATT&CK). These tests can be used to verify detection and response techniques and procedures.
- Uber Metta: An information security preparedness tool to do adversarial simulation. The project parses YAML files with actions and uses celery to queue these actions and automatically execute them.
Actions performed by MITRE Caldera are generated by the planning system in cooperation with the preconfigured ATT&CK model. The advantage of doing so lies in the flexibility in the emulation of adversary operations without needing to follow any required operation sequences. Automated emulation can safely replicate realistic adversary behavior without causing any damage to assets. Besides, it allows repeatable testing and verification of prevention and detection capabilities.
Repeated adversary emulation and testing can effectively improve detection capabilities of the analysis program, constantly expand the technical coverage, and steadily narrowing the gap between defenders and attackers.
4.2Â Â Â Â Â Hunting Threats
ATT&CK can also be used for threat hunting. Jared Myers, a senior threat researcher from Carbon Black, discussed how to use ATT&CK to hunt threats in his presentation How to Evolve Threat Hunting by Using the MITRE ATT&CK Framework.
According to Jared Myers, many enterprises have realized that it is important for them to know when, rather than if, their assets will be attacked. Therefore, the tools they need should not only detect and respond to threats but also hunt and capture threats to promptly identify potential dangers within their organizations.
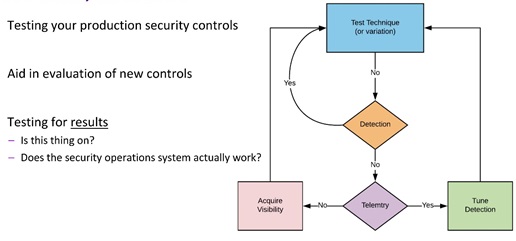
The analytics system should do more than protective purposes to include threat hunting:
- Can use tools to detect high-quality alerts on objects previously covered by other techniques.
- Focus on points that are hard to detect.
- Broaden the analysis scope. For example, a universal method may be used for a variety of purposes, or other tactics or techniques may be used for a specific purpose.
In practice, repeated testing and iterations are also required for improvement of the capabilities of detecting unknown threats.
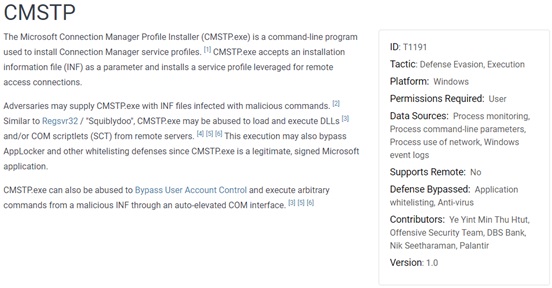
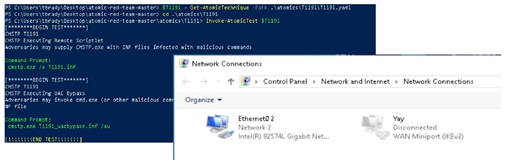
Jared Myers used T1191 CMSTP as an example to illustrate his ideas. Before research, we can get familiar with the MITRE Wiki for T1191.
He shared his ideas on use of CMSTP for threat hunting, indicating that attackers may adapt their tradecraft to less-known execution techniques. Therefore, we should first check whether there are leading indicators of malicious behavior, for example:
- Whether network connections are established
- Whether child processes are spawned out of temp directories, command-interps, and so on
- Whether child processes are spawned from dllhost cmstp COM objects
Then we should conduct our research around “what” and “how”, for example:
- Is the binary signed?
- Does the binary ship in every version of modern Windows?
- Can the binary execute remote payloads?
- Does the binary allow auto-elevation of process execution?
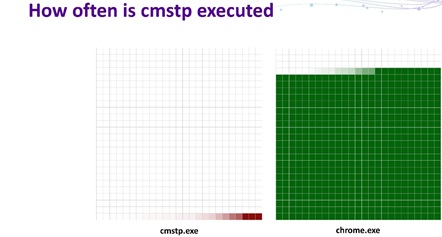
Alternatively, we can perform the analysis from the execution frequency of the binary.
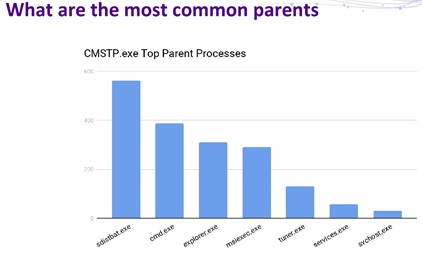
Another analysis method is to find out the most common parents that have invoked CMSTP.
Atomic Red Team can also be used for internal unit tests.
5.   NSFOCUS’s ATT&CK Modeling Practice
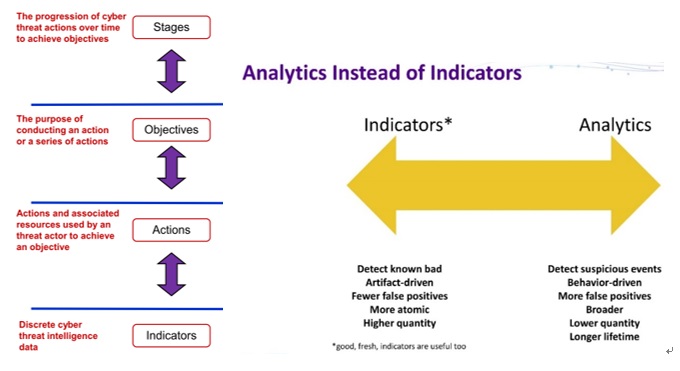
From the perspective of layers, ATT&CK modeling is focused on behavior, while alerting by traditional protective devices mainly takes place at the indicator layer. Indicators can detect known malicious data. Driven by artifacts, this type of detection is characterized by a low rate of false positives. However, owing to the fine granularity, alerts generated can be very large in number. In contrast, analytics at the behavior layer is aimed at suspicious events. Driven by behavior, this type of detection has a higher rate of false positives. Also, the coarser granularity leads to a smaller number of events and a longer lifetime. Modeling at the behavior layer can, on the one hand, make full use of TTPs in threat intelligence for knowledge sharing, and on the other hand create adversary profiles at a higher level, thus freeing defenders from trivial techniques and indicator rules.
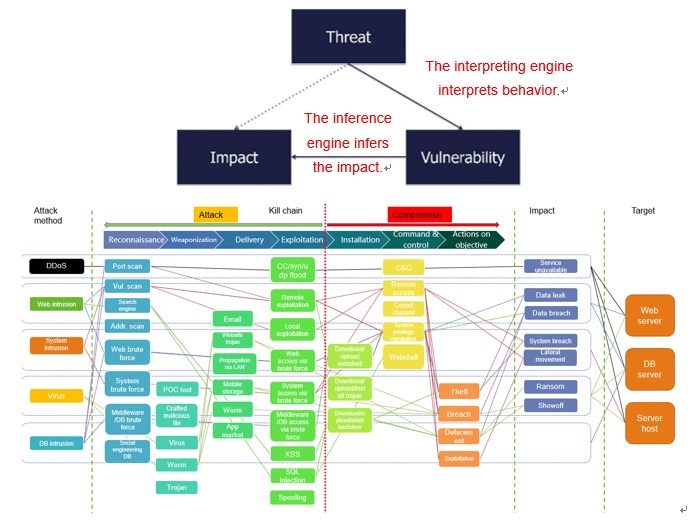
Similarly, NSFOCUS adopts an abstract approach to threat modeling that also revolves around behavior. To handle large quantities of alerts generated by protective devices, NSFOCUS’s threat model uses an interpreting engine to interpret massive alerts to corresponding attack behavior, mapped to who (threat) exploits what (vulnerability) for an attack in the risk model. The threat model also uses an inference engine to infer the impact to be caused by an attack, mapped to the impact caused by a vulnerability in the risk model. Besides, a kill chain model is employed to help determine the compromise status.
Considering the complexity of real-life network environments, behavior modeling alone is far from enough to analyze attacks. For this reason, NSFOCUS, based on a knowledge graph, has designed a number of subjects for modeling of various threats across the network. NSFOCUS’s threat model is compatible with MITRE’s models, including CAPEC, MAEC, and ATT&CK, and so can extract critical information from multi-source threat intelligence as knowledge to expand the knowledge graph.
In terms of capability improvement, NSFOCUS tests its products by reproducing real-world attack scenarios and simulating attacks in addition to arranging internal red team-blue team exercises to test its own defensive capabilities.
6.   Summary
In their ATT&CK in Practice: A Primer to Improve Your Cyber Defense, Freddy Dezeure and Rich Struse emphasized how to put the ATT&CK model in practice. The presentation first analyzes the necessity of threat modeling, identifying adversaries to be dealt with and critical assets to be protected, then details a procedure for building an analytics system by using the ATT&CK model, and finally provides methods for improving defensive capabilities as well as some useful tools and resources. Jared Myers’s How to Evolve Threat Hunting by Using the MITRE ATT&CK Framework is focused on use of the ATT&CK model to hunt threats.
He described how to detect unknown threats after a defensive system is in place and shared his ideas on related researches. By investigation and comparison, we find that NSFOCUS’s ideas about threat modeling and capability improvement are in agreement with ATT&CK, which, though different in functions because of different services to support, can inform us a lot about how to create an effective threat model.
7.   References
ATT&CK: https://attack.mitre.org/
SIGMA: https://github.com/Neo23x0/sigma
Mitre Caldera: https://github.com/mitre/caldera
Endgame Red Team Automation: https://github.com/endgameinc/RTA
Redcanary Atomic Red Team: https://www.redcanary.com/atomic-red-team/
Uber Metta: https://github.com/uber-common/metta
Advanced-Threat-Hunting-with-Carbon-Blac: http://the.report/assets/Advanced-Threat-Hunting-with-Carbon-Black.pdf