Overview
Recently, NSFOCUS CERT detected that Spring Cloud officially fixed a SPEL expression injection vulnerability in Spring Cloud Function, because the parameter “spring.cloud.function.routing-expression” in the request header is processed as a Spel expression by the apply method of the RoutingFunction class in Spring Cloud Function, resulting in a Spel expression injection vulnerability, which can be exploited by an attacker to remotely execute arbitrary code. At present, the vulnerability PoC has been disclosed, and relevant users are requested to take measures to protect it.
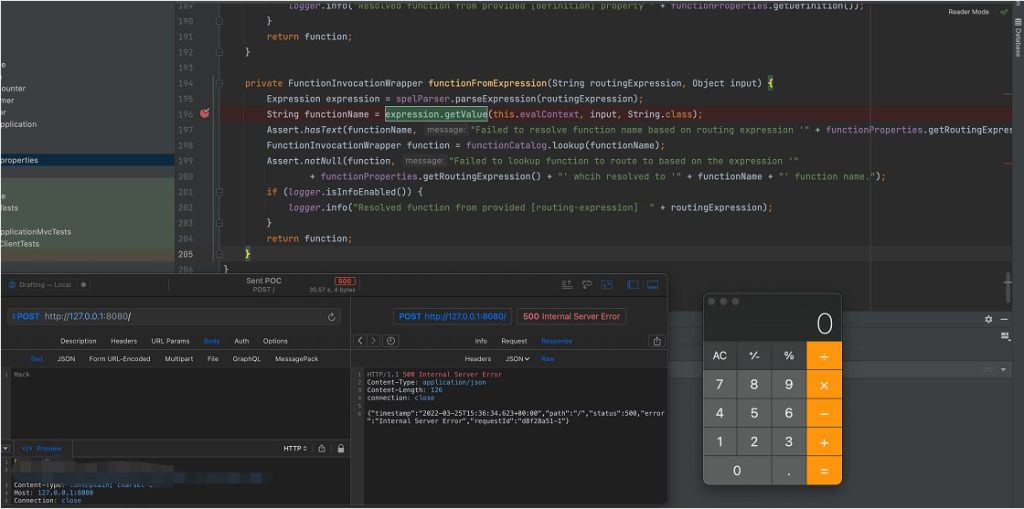
Spring Cloud Function is a Spring Boot-based functional computing framework that abstracts all transport details and infrastructure, allowing developers to keep all familiar tools and processes and focus on business logic. NSFOCUS has successfully reproduced this vulnerability immediately:
Reference link:
Scope of Impact
Affected version
- 3.0.0.RELEASE <= Spring Cloud Function <= 3.2.2
Note: Publish date is from November 22, 2019 to February 17, 2022
Vulnerability Detection
Users can check the reference to the spring-cloud-function component in the application and check the current version:
If the program is packaged with Maven, you can check whether the relevant components are introduced in the pom.xml file of the project:
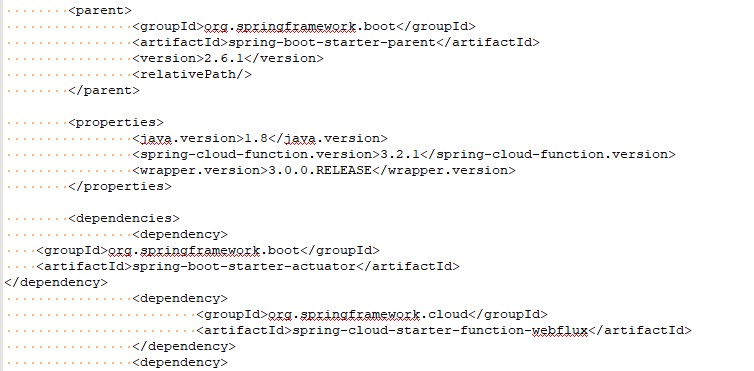
For project code that uses the org.springframework.cloud:spring-cloud-function-context component, you can use the following command to view the version:
grep -A 2’spring-cloud-function-context’pom.xml
If the current version is affected, there is a security risk.
Mitigation
At present, the official patch has been released for this vulnerability. Please update the affected users as soon as possible for protection.
Official link: https://github.com/spring-cloud/spring-cloud-function/commit/0e89ee27b2e76138c16bcba6f4bca906c4f3744f
Note: There is currently no official release of the new version, please continue to pay attention and update in time: https://github.com/spring-cloud/spring-cloud-function/tags
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.
