The RSA Conference 2024 will kick off on May 6. Known as the “Oscars of Cybersecurity,†the RSAC Innovation Sandbox has become a benchmark for innovation in the cybersecurity industry.
Today, let’s get to know the company VulnCheck.
Introduction of VulnCheck
VulnCheck is a vulnerability intelligence company that primarily helps businesses, government agencies, and cybersecurity vendors address the challenge of vulnerability prioritization. The VulnCheck platform offers comprehensive, real-time vulnerability and intelligence, automatically associating it with unique proprietary vulnerabilities and threat intelligence to automate the prioritization of vulnerabilities, thereby assisting cybersecurity teams to get ahead of their adversaries.
VulnCheck was founded in 2021 and is headquartered in Lexington, USA. In February 2023, it secured $3.2 million in seed funding.
Anthony Bettini is the CEO and founder of VulnCheck. VulnCheck is the third company founded by Anthony. His first startup, Appthority, a mobile security company, was launched at the RSA Innovation Sandbox, won the “Most Innovative Company of the Year” award, and was later acquired by Symantec. He then founded FlawCheck, a container security startup focused on Docker, which was also acquired by Tenable.
Ralph Logan is the Chief Strategy Officer of VulnCheck. He has held several positions in the intelligence community and is also the founder and CEO of a cybersecurity services company. He will help formulate VulnCheck’s overall strategy and operational approach to grow the business.
Jacob Baines is the Chief Technology Officer of VulnCheck. He has held several leadership positions in vulnerability research, vulnerability exploitation and development, and vulnerability detection at Rapid7, Dragos, Dark Wolf, and Tenable. Jacob has presented his research at conferences such as Black Hat, DEFCON, and InfoSecurity Europe. He also has an extensive background in the intelligence community, having been involved in reverse engineering, vulnerability research, and the development of CNO (Computer Network Operations) tools. He is responsible for VulnCheck’s overall technology and research strategy.
Background
According to the 2023 Threat Landscape Year in Review report released by the security company Qualys, a total of 26,447 vulnerabilities were disclosed in 2023, an average of 72.46 CVEs per day, the highest in history, which is a 5.2% increase from the 25,050 vulnerabilities disclosed in 2022. Among the disclosed vulnerabilities, more than 7,000 have “PoC (Proof of Concept) code,” 206 have available weaponized exploit code, and 115 have been “widely exploited” by threat actors. At Mandiant’s keynote presentation at RSAC in April, they disclosed that 32% of breaches tracked in 2022 were the result of exploits – that is the first time that the top root source of breaches has NOT been phishing.
The CISA (Cybersecurity and Infrastructure Security Agency) statistics indicate that only 4% of the total number of CVEs have been publicly exploited. A large number of vulnerabilities may just be a number. In the internationally accepted vulnerability assessment methods, the exploitability of the vulnerability has become an important evaluation index. For a cybersecurity operator, they may not necessarily become the target of a 0-day vulnerability attack, but if the vulnerabilities they have are proven to be successfully exploited elsewhere and are not patched in time, the risk of being attacked is huge. Therefore, how to select exploitable vulnerabilities from millions of vulnerabilities has become a difficult problem in the industry.
This is where VulnCheck is leveraging the expertise of some of the foremost security researchers in the world to build a real-time solution that does not require the build-out of scripts against the CISA KEV, featuring 5X more exploits vs any other solution and is building out a way for cybersecurity firms, government agencies and enterprise organizations to automatically enrich detections with the richest data set available.
Product Introduction
VulnCheck currently offers five products: two commercial products, Exploit & Vulnerability Intelligence and Initial Access Intelligence, and three free community products: VulnCheck KEV, NIST NVD++, and VulnCheck XDB.
1. Exploit & Vulnerability Intelligence
The Exploit & Vulnerability Intelligence product helps users make better and faster decisions on which vulnerabilities need to be fixed immediately. Unlike other solutions that are purely focused on vulnerabilities, VulnCheck combines exploitation intelligence with vulnerability intelligence. By combining the two, users can gain better insights into vulnerability prioritization and remediation.
According to the official website introduction, the product has the following four major advantages:
- Respond faster by having information on average 14 days ahead of the NIST NVD.
- The industry’s largest collection of exploit proof of concept code and evidence of exploitation in the wild.
- A complete exploitation timeline covering when the vulnerability was first disclosed, when evidence of exploitation was first discovered, and when the vulnerability was remediated.
- Prioritize remediation efforts on the most critical vulnerabilities, those that are actively being exploited in the wild.
>> More sources of intelligence
VulnCheck’s Exploit & Vulnerability Intelligence continuously tracks hundreds of specific threat actors who have been reported to exploit certain vulnerabilities in the wild. VulnCheck collects threat actor information from various sources and then associates this information with the industry’s most user-friendly vulnerability intelligence product. However, different suppliers name threat actors in different ways, making it more challenging to associate threat actors. VulnCheck helps users easily find threat actors by supporting multiple naming schemes.
In addition, VulnCheck also tracks dozens of vendor and government recommendations, then combines this data with existing vulnerability intelligence. Since there is a lag in the publication of CVEs by NIST in the NVD, and VulnCheck’s Exploit & Vulnerability Intelligence product monitors sources far beyond the NVD, this allows the product to obtain vulnerability information earlier than the NIST NVD, that is, on average, 14 days ahead of the NIST NVD.
>>More extensive intelligence content
Overall, VulnCheck’s Exploit & Vulnerability Intelligence product includes the following information for each vulnerability: vulnerability aliases, CVSS temporal scores, vulnerability classification data, vendor and government recommendations. Unlike other vulnerability databases, VulnCheck also includes broader and more up-to-date information related to the vulnerability, including:
- Vulnerabilities in open source packages/dependencies
- Vulnerabilities in ICS/OT, IoMT, IoT, mobile devices, etc.
VulnCheck Exploit & Vulnerability Intelligence also includes unique fields, typically unavailable in other alternative sources, such as:
- Vulnerability Status
- Categorization (e.g., ICS/OT, IoMT, IoT, Mobile, Server Software, etc.)
- MITRE ATT&CK mapping
- MITRE Attack Patterns (CAPEC) mapping
- CWE associations for pre-2008 CVEs
- More vendor references
- More exploit references
- Fewer broken links
- Cleaner CPE data
- Ability to query by Package URL (purl)
2. Initial Access Intelligence
Initial Access Intelligence provides users with internally developed vulnerability PoCs, PCAP files, Suricata and Snort signatures for detecting vulnerabilities, YARA rules (if available), CPE strings, version scanners, mapping to GreyNoise tags, and internet-level exposure measurement of potentially vulnerable systems using Censys and Shodan. With these capabilities, Initial Access Intelligence can help users defend against initial access vulnerabilities that have been exploited or may be exploited soon.
The Initial Access Intelligence product has the following four major advantages:
- Focused on What Matters
- Exclusively Initial Access
- Detection Artifacts Early
- Private Exploit PoCs
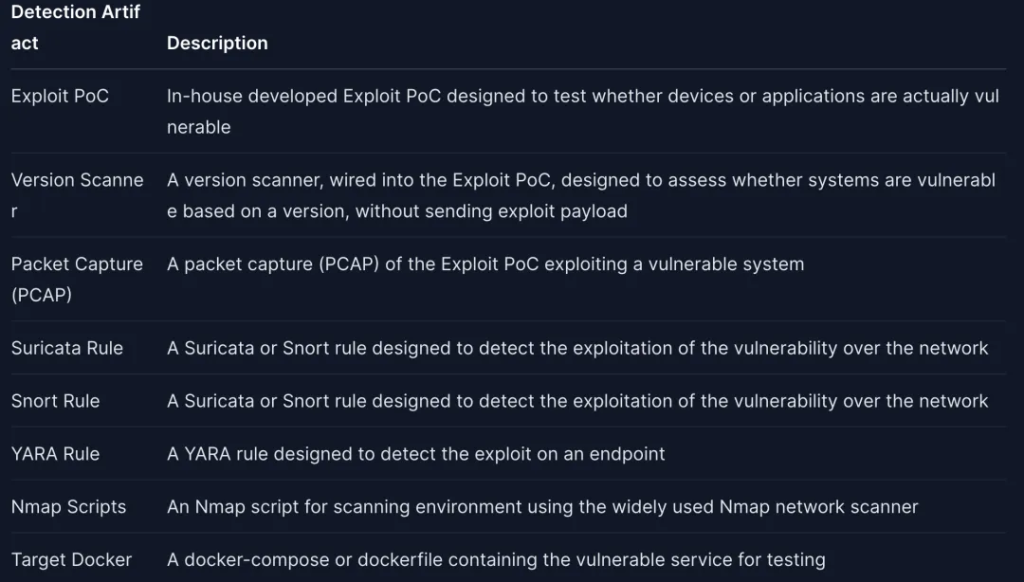
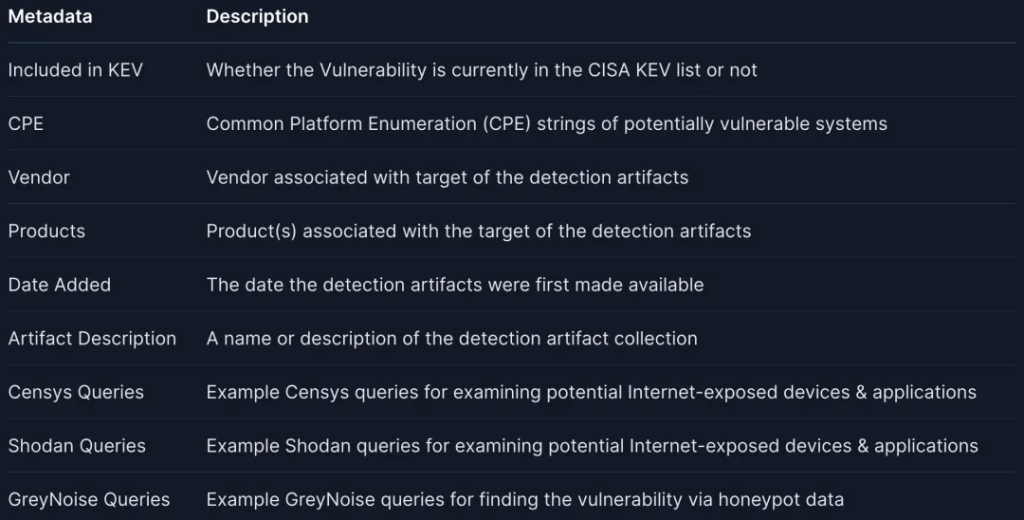
As shown in Figures 3 and 4, Initial Access Intelligence provides the following detection tools and metadata on the potential exposure of vulnerabilities to provide a detailed description of the vulnerability:
In addition, VulnCheck’s Initial Access Intelligence product also tracks potentially vulnerable systems that may become targets for initial access attacks, as well as tracks command and control (C2) attacker infrastructures. VulnCheck fingerprints dozens of types of C2 attacker infrastructures, combining these fingerprints with existing internet infrastructure mapping techniques (such as Shodan or Censys) and scanners developed by VulnCheck to maintain a list of malicious IP addresses.
3. Free Community Products
1). VulnCheck KEV: Helps businesses, government agencies, and vendors easily understand which vulnerabilities have been exploited. Compared to the CISA’s KEV catalog, VulnCheck tracks an additional 876 (or 81.04%) exploited vulnerabilities and provides alerts to customers an average of 27 days before the missing vulnerabilities are added to the CISA KEV catalog.
2). NIST NVD++: Due to various issues when using the NIST NVD, such as frequent timeouts or 503 service unavailable errors when accessing the NVD 2.0 API, VulnCheck has migrated to NVD++ and established its own community.
3). VulnCheck XDB: This is the most comprehensive repository of exploits and proof-of-concepts hosted on git repositories. XDB simplifies the process of obtaining vulnerability information by monitoring the sources where vulnerabilities first appear, i.e., git repositories.
Conclusion
VulnCheck is a vulnerability intelligence company headquartered in Lexington, USA, founded in 2021. Their main business is to help businesses, government agencies, and cybersecurity vendors address the challenge of vulnerability prioritization. By providing comprehensive, real-time vulnerability and intelligence, and automatically associating proprietary vulnerabilities and threat intelligence, VulnCheck assists cybersecurity teams in surpassing their competitors.
The company’s founder team includes CEO Anthony Bettini, Chief Strategy Officer Ralph Logan, and Chief Technology Officer Jacob Baines, all of whom have extensive experience in the security field. VulnCheck’s products include commercial products Exploit & Vulnerability Intelligence and Initial Access Intelligence, as well as free community products VulnCheck KEV, NIST NVD++, and VulnCheck XDB. These products help users better understand vulnerabilities and threats, and strengthen network security defenses.
From our perspective, vulnerability management and intelligence are established areas within cybersecurity research. The key to success for vendors lies in meticulous attention to detail. Those who excel at gathering extensive intelligence data, linking it effectively, and offering users more accessible and superior services through additional security tools will likely prevail in the market competition.
More RSAC 2024 Innovation Sandbox Finalist Introduction:
- RSAC 2024 Innovation Sandbox | The Future Frontline: Harmonic Security’s Data Protection in the AI Era
- RSAC 2024 Innovation Sandbox | Bedrock Security: A Seamless and Efficient Data Security Solution
- RSAC 2024 Innovation Sandbox | Antimatter: A Comprehensive Data Security Management Tool
- RSAC 2024 Innovation Sandbox | Mitiga: A New Generation of Cloud and SaaS Incident Response Solutions
- RSAC 2024 Innovation Sandbox | RAD Security: New Solutions for Cloud-Native Anomaly Detection and Response
References
[1] https://vulncheck.com/company/about
[2] https://vulncheck.com/product/exploit-intelligence
[3] https://vulncheck.com/product/initial-access-intelligence
[4] 2023 Threat Landscape Year in Review: If Everything Is Critical, Nothing Is
[5] Reducing the Significant Risk of Known Exploited Vulnerabilities
[6] https://www.secrss.com/articles/46094
[7] https://vulncheck.com/blog/2022-cisa-kev-review
[9] https://docs.vulncheck.com/products/initial-access-intelligence/detection-artifacts
[10] VulnCheck Launches XDB: The Most Comprehensive Hub of Exploits for Modern Security Teams
[11] https://www.vulinsight.com.cn/#/product
[12] https://docs.vulncheck.com/products/exploit-and-vulnerability-intelligence/threat-actor-naming