The RSA Conference 2024 will kick off on May 6. Known as the “Oscars of Cybersecurity,†the RSAC Innovation Sandbox has become a benchmark for innovation in the cybersecurity industry.
Today, let’s get to know the company P0 Security.
Introduction of P0 Security
P0 Security was established in California in 2022. The company provides services for security engineers to secure access and configure permissions to their company’s cloud resources. Engineers can use P0 Security to identify cloud identities (humans or machines) with privileged access and to flag risks. P0 Security also focuses on the user experience of developers by automating the setting of fine-grained, timely, and short-term access privileges for cloud resources and granting them to users. The company secured $5 million in funding in its founding year.
Currently, P0 Security has a team of about 10 people, with three co-founders as shown in Figure 2. From left to right, Shashwat Sehgal, the CEO and founder, graduated from the Indian Institute of Technology in Delhi in 2007 and has previously worked as a director of product management and observability at Splunk. Gergely Danyi, the co-founder and CTO of P0 Security, has served as a chief software engineer at Splunk and studied at the University of Corvinus in Budapest. Nathan Brahms, the co-founder and VP of Engineering at P0 Security, has held the position of VP of Engineering at r2c and studied at Harvard University.
Background
In the era of cloud computing, Identity and Access Management (IAM) is a crucial component for managing access permissions to cloud computing resources. Improper control over IAM can lead to several issues:
- Data Breaches: If IAM credentials are compromised, attackers may use them to access sensitive data or perform unauthorized operations.
- Resource Misuse: Users may incorrectly configure IAM roles or permissions, granting certain users or services more privileges than necessary.
- Security Vulnerabilities: Incorrect IAM settings can result in security vulnerabilities, such as unauthorized users accessing sensitive data or performing dangerous operations.
- Compliance Issues: Poor IAM control can lead to compliance issues, such as violations of data privacy regulations (e.g., GDPR) or financial regulatory requirements.
- Data Loss: Accidental deletion of IAM entities (such as roles or users) by users can result in data loss or system disruption.
Although the use of cloud services has greatly improved the efficiency of development and operations, users have always faced challenges in ensuring access to their critical infrastructure and data. The nature of these challenges has changed significantly over time. Traditional access protection methods rely on network boundaries. However, in a cloud-native environment, the number of resources where sensitive data may exist has grown explosively. Additionally, the number of identities, especially non-human (machine) identities, has also grown explosively. Consequently, the number of access paths to sensitive data and infrastructure has increased exponentially. This has rendered traditional access protection methods ineffective. According to a striking statistic, 70% of cloud security incidents were related to IAM misconfiguration in 2022, highlighting the importance of protecting IAM identities in company infrastructure security more than ever before.
Yet, organizations struggle to govern access effectively. Legacy IGA vendors are hard to use and involve lengthy and expensive implementation cycles. Other vendors (CIEM, CSPM, DSPM) provide a lot of noisy alerts, and security teams are rightly hesitant to use their recommendations to govern access, which might affect a developer workflow, or take down a production service.
P0 Security Products and Solutions
>> Product Introduction
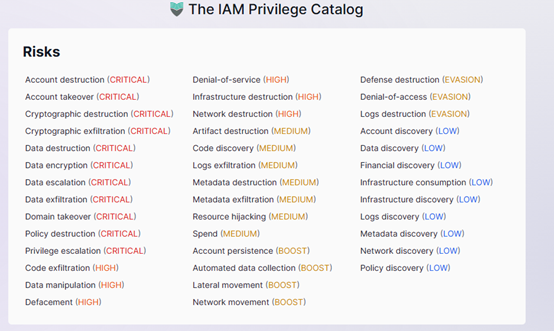
P0 Security’s IAM product primarily includes a detailed permissions catalog that maps IAM permissions across various cloud services and their potential misuse risks. This catalog is designed to help organizations identify identities that may be at risk. Specifically, it includes a catalog of common permission risks, each assigned a risk level, and a detailed IAM system permissions catalog that explains potential misuse and the scope of impact.
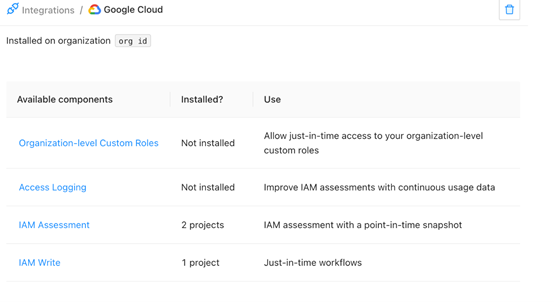
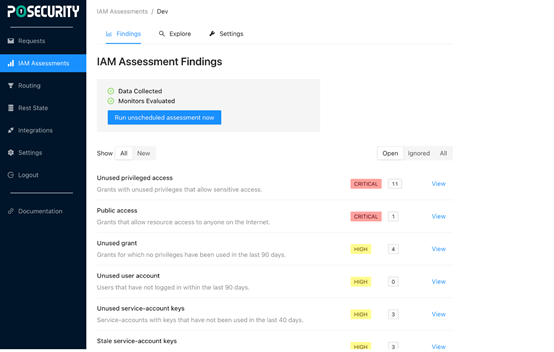
Additionally, P0 provides an IAM audit tool specifically for identifying security issues in Google Cloud users’ IAM configurations, integrating data from identity providers, IAM policies, and cloud access logs to help users check for potential security issues. These tools and catalogs not only help understand the security posture of specific IAM configurations but also determine the impact of IAM configuration changes on organizational security posture and create organizational access policies that restrict or prevent certain threat vectors. Users can also convert the catalog into JSON format using provided scripts for use in other systems or processes. The overall product is currently presented in a web-based format, as shown in Figure 3, where users can select current services and proceed with installation.
>>Features
Currently, P0 Security can discover and grant fine-grained least privilege access to the following: Google Cloud, AWS, Azure, K8s, Snowflake, PostgreSQL, Okta, etc.
As shown in Figure 4, P0 Security supports the detection of IAM permission risk scenarios. Taking the Account Destruction risk as an example, this risk allows attackers to delete accounts in the system, potentially disrupting organizational operations, disrupting normal business processes, or causing significant production responsibility. In Google Cloud IAM identities, it corresponds to the permissions ‘cloudsql.users.delete’ and ‘iam.serviceAccounts.delete’.
>>Competitive Analysis
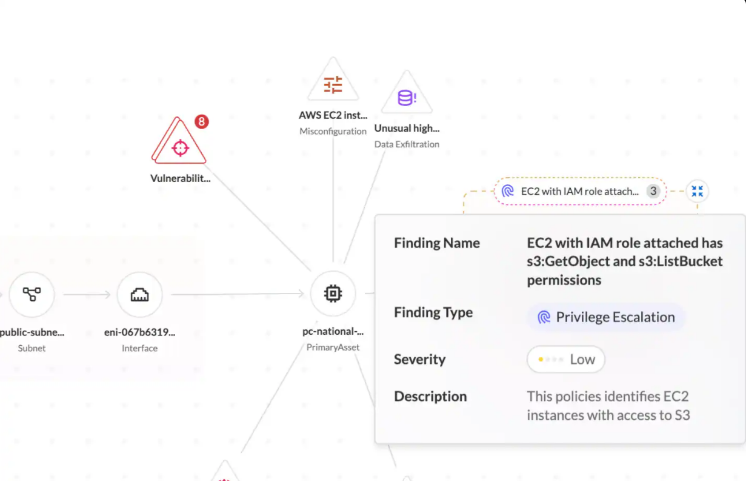
Cloud Infrastructure Entitlement Management (CIEM) and P0 Security’s product features are highly overlapping. Several leading security vendors have launched related IAM identity management services. Taking Palo Alto Networks as an example, the company’s CIEM under the Prisma Cloud service can discover improper IAM authorizations, as shown in Figure 5. Compared to P0 Security’s product, we believe that Prisma Cloud has richer support for public cloud services and a more beautifully designed presentation interface.
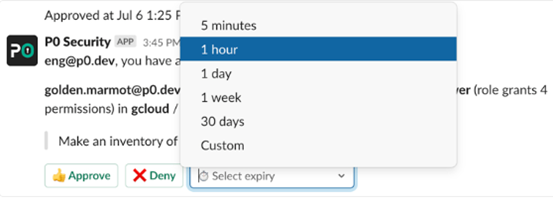
However, P0 Security’s advantage lies in its unobtrusive instant permission request and approval, as shown in Figure 6. Users can temporarily obtain a time-limited permission from the organization to operate the organization’s public cloud resources. This approval and timeliness effectively block the security risks brought by roles that are not used for a long time. That is, P0 Security can better manage the internal demand of the organization for cloud resources.
>>Deployment Method
The deployment method of P0 Security is very simple. Users can deploy it according to the operation document provided on its official website. It should be noted that users can choose whether to inject the P0 Security role into IAM to create temporary roles for users and other operations.
Secondly, P0 Security has currently integrated with Slack (an instant messaging office software), and users can see any user’s permission application within their organization on Slack. If a risk analysis of IAM roles is required, a single click can obtain a result sorted by priority, as shown in Figure 8.
>>Usage Recommendations
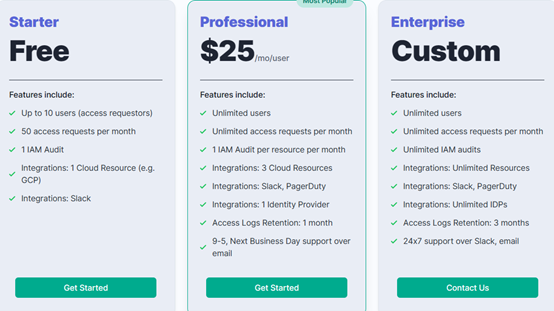
As shown in Figure 9, P0 Security offers a free limited-use version. If your company is not large and uses services from a single cloud provider, there is no need to upgrade to the professional version. Of course, the professional version is more aligned with actual production needs, such as increased support for Slack and support for multi-cloud scenarios.
Conclusion
Since the installation process directly provides access to public cloud resources to the P0 account, a potential attack is another P0 customer or attacker hijacking another customer’s P0 account, i.e., adding a new attack surface against user IAM.
Although domain restriction policies have prevented individuals outside the organization from obtaining access in this way, P0 still needs to protect against internal personnel within the organization, as individuals within the organization may attempt to set up another P0 tool with approval authority to grant themselves unauthorized access permissions. Currently, P0 Security ensures the administrator access permissions of the project by enforcing the configuration of project user permissions, and users need to submit authorized credentials to log in and use P0.
Additionally, security teams are increasingly recognizing that identity is the most important factor in protecting security. Targeted attacks and bypassing multi-factor authentication (MFA) once again prove that there are vulnerabilities in identity security. Faced with the complex cloud permission policies and the intricate settings of large organizations’ user groups and users, a simple and easy-to-use universal cross-cloud identity management is imperative. At the same time, the emergence of P0 Security indicates that current CIEM lacks support in the field of instant office, and users are more inclined to apply for the organization’s cloud infrastructure resources as they would for office supplies.
More RSAC 2024 Innovation Sandbox Finalist Introduction:
- RSAC 2024 Innovation Sandbox | The Future Frontline: Harmonic Security’s Data Protection in the AI Era
- RSAC 2024 Innovation Sandbox | Bedrock Security: A Seamless and Efficient Data Security Solution
- RSAC 2024 Innovation Sandbox | Antimatter: A Comprehensive Data Security Management Tool
- RSAC 2024 Innovation Sandbox | Mitiga: A New Generation of Cloud and SaaS Incident Response Solutions
- RSAC 2024 Innovation Sandbox | RAD Security: New Solutions for Cloud-Native Anomaly Detection and Response
- RSAC 2024 Innovation Sandbox | VulnCheck: A Solution to the Challenge of Vulnerability Prioritization
References
[3] https://www.r2conline.com/
[4] https://www.gartner.com/en/documents/3242920
[5] https://p0.dev/blog/rsa-innovation-sandbox-top-10
[6] https://www.paloaltonetworks.cn/prisma/cloud/cloud-infrastructure-entitlement-mgmt