What is a Random Subdomain Attack?
A Random subdomain attack is also known as a pseudo-random subdomain (PRSD) attack due to the use of pseudo-random algorithms. A PRSD attack is an approach of double attack against both DNS caching servers of Internet service providers (ISPs) and local authoritative servers of customers. During such an attack, the attacker directs its controlled compromised hosts to send numerous requests for fictitious subdomains. Then, the DNS caching servers and authoritative servers will see their bandwidth saturated by a high volume of traffic and finally become unavailable due to resource exhaustion. In response to this type of attack, the technical team of NSFOCUS ADS, drawing on its rich practical experience, proposed solutions to dealing with PRSDs.
Procedures of the PRSD attack
Here we give an example to describe the procedures of the PRSD attack. Assuming an attacker attempts to target a bank’s authoritative server, ns.bank.com, by crafting a large number of requests to false subdomains:
aaa1234.bank.com
bbb1234.bank.com
ccc1234.bank.com
ddd1234.bank.com
…
The attack procedures are as follows:
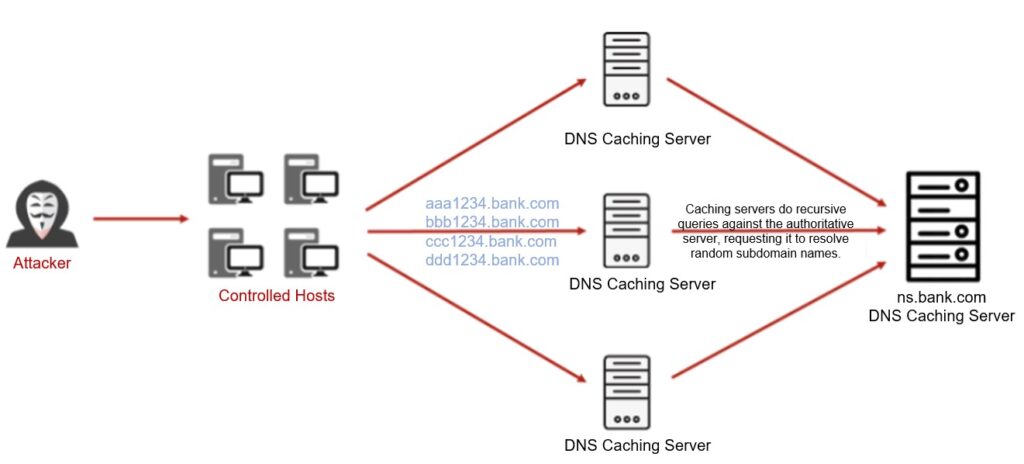
Step 1: The attacker instructs its controlled hosts to send plenty of requests to illegitimate subdomains to DNS caching servers of an ISP.
Step 2: Upon receiving the requests, the DNS caching servers will perform a DNS lookup, searching local DNS records. Finding no matching local records, the servers will recursively send requests to the authoritative server.
Step 3: DNS query requests from various DNS caching servers are flooded to the authoritative server.
Step 4: DNS caching servers and the authoritative server respectively receive a substantial number of requests, producing a burst in the network traffic that might go beyond the bandwidth limit. In addition, the servers get overloaded and even collapse.
Difficulties in Protection
(1) In subdomain names, prefixes or infixes may be constantly changing.
(2) Multiple suffixes may be targeted. The corresponding prefix may not change that frequently. However, these slight prefix changes combined with suffixes will lead to the generation of a great many false domain names.
Recommendations for Protection Against PRSD Attacks
In view of the PRSD attack chain, both DNS cache servers of the ISPs and DNS authoritative servers of the customers will be affected. We will explain how NSFOCUS protects these two kinds of DNS servers respectively.
ISP: ADS deployment at the DNS caching server side
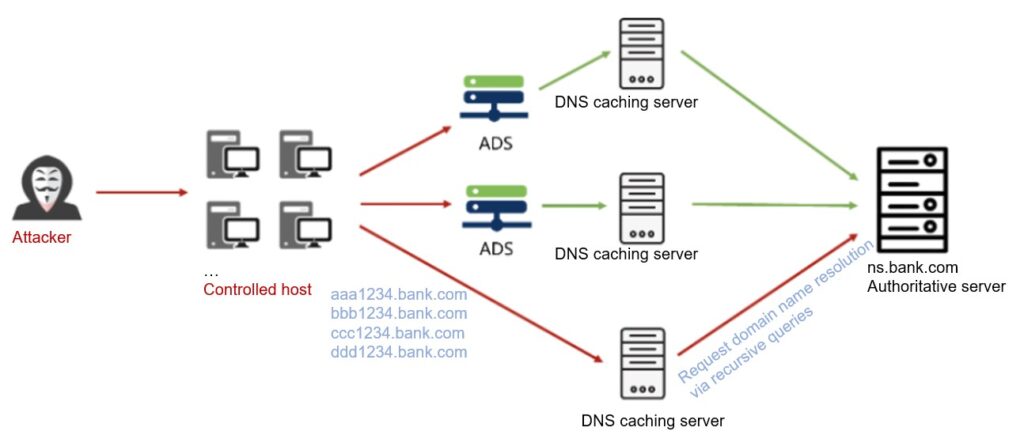
Protection Policies
1. ISP’s DNS caching servers provide query service for a massive domain names. Therefore, a whitelist for domain names is not efficient as this may easily cause false positives and false negatives.
2. As PRSD attacks are mostly carried out via packet sending tools, these packets do not have normal protocol behaviors and can be handled by ADS’s DNS protection algorithms.
3. Even if a source IP address of attack packets is passed through the ADS’s algorithms, the IP Behavior Control featuring on ADS can limit the traffic rate of this IP address. 4. If it is possible to locate signatures in attack packets through experts further analysis, for example, signatures in domain names or packet headers, DNS Keyword Checking on the ADS can identify these signatures and drop attack packets.
Customer: On-premises ADS deployment at the authoritative server side
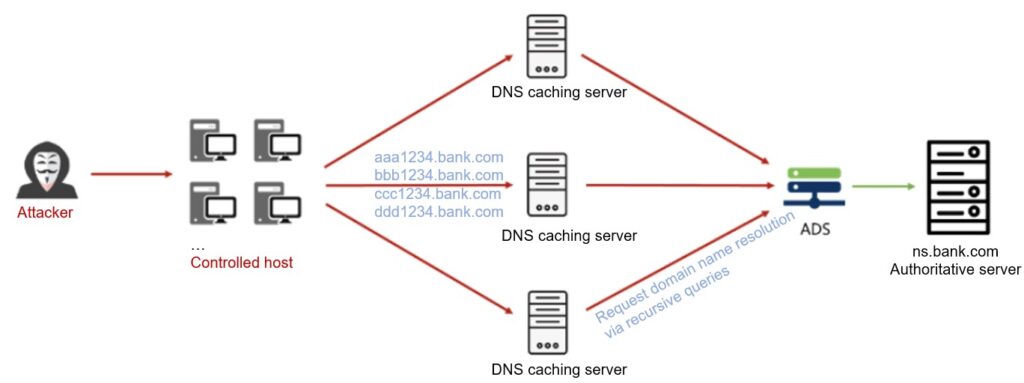
Protection Policies
1. We often use a CNAME algorithm to protect authoritative servers. However, in this case, the attack traffic to the authoritative servers are from legitimate DNS caching servers, which means such attacks won’t be stopped. The better way is to combine the CNAME algorithm and IP Behavior Control together to filter attack traffic. The CNAME algorithm screens out attack traffic from non-caching servers, while the IP Behavior Control rate-limits the traffic originated from a single caching server.
2. Also, we can use DNS protocol protection algorithms to limit the traffic rate from various dimensions, including by source IP address and destination IP address. 3. For less random subdomain names, we can extract attack signatures and block the attack traffic based on keywords.
-e1619596788284.jpg)