Overview
Recently, NSFOCUS CERT found that Oracle officially issued a security notice to fix a remote code execution vulnerability in Oracle WebLogic Server (CVE-2023-21931). Due to a flaw in the getObject Instance () method of the WLNamingManager class in WebLogic, in the default configuration, unauthenticated remote attackers can pass in specific objects through T3/IIOP, ultimately enabling the execution of arbitrary code on the target system. At present, the technical details of the vulnerability have been publicly disclosed. Please take measures to protect the affected users as soon as possible.
WebLogic is a Java EE application server developed by BEA Systems and now owned by Oracle. It provides a complete Java EE platform and a wide range of services and functions, such as web servers, EJBs containers, JMS message queues, transaction management, security, etc., and has high scalability and stability.
Reference link:
https://www.oracle.com/security-alerts/cpuapr2023.html
Scope of Impact
- Weblogic 12.2.1.3.0
- Weblogic 12.2.1.4.0
- Weblogic 14.1.1.0.0
Detection
Local detection
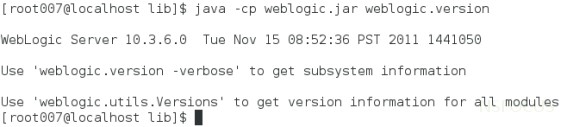
You can use the following command to troubleshoot the installation of WebLogic versions and patches.
| $ cd /Oracle/Middleware/wlserver_ 10.3/server/lib $ java -cp weblogic.jar weblogic.version |
If there is no information on patch installation in the displayed results, it indicates a risk, as shown in the following figure:
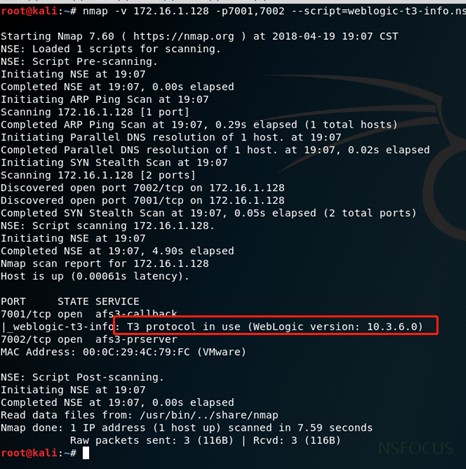
T3 protocol detection
The Nmap tool provides a scanning script for the WebLogic T3 protocol, which can detect WebLogic hosts that have T3 services enabled. The command is as follows:
| Nmap – n – v – Pn – sV [host or segment address] – p70017002– script=weblogic t3 info. nse |
As shown in the red box below, the target has enabled the T3 protocol and the WebLogic version is within the affected range. If the relevant personnel have not installed the official security patch, there is a risk of vulnerability.
Mitigation
Patch update
Currently, Oracle has released patches to fix the vulnerabilities. Users are advised to refer to the official announcement and download updated patches for the affected products in a timely manner. They should also refer to the readme file in the patch installation package for installation and updates to ensure long-term effective protection.
Note: The official Oracle patch requires users to hold a licensed account for the genuine software and log in using that account https://support.oracle.com Afterwards, you can download the latest patch.
Temporary protective measures
If users are temporarily unable to install updated patches, the following measures can be taken to temporarily protect high-risk vulnerabilities.
1) Restrict T3 protocol access
Users can temporarily block attacks that exploit T3 protocol vulnerabilities by controlling access to the T3 protocol. WebLogic Server provides a default connection filter called weblogic.security.net.ConnectionFilterImpl. This connection filter accepts all incoming connections and can configure rules to control access to T3 and T3s protocols. The detailed steps are as follows:
1. Enter the WebLogic console and enter the base_ In the configuration page of domain, enter the “Security” tab page, click “Filter” to enter the connection filter configuration.
2. In the connection filter, enter: weblogic.security.net.ConnectionFilterImpl, refer to the following notation, and configure rules in the connection filter rules that match the actual situation of the enterprise:
| 127.0.0.1 * * allow t3 t3s Local IP * * allow t3 t3s Allowed IP * * allow t3 t3s * * * deny t3 t3s |
| The format of the connection filter rule is as follows: target localAddress localPort action protocols, where: – Target specifies one or more servers to filter. – LocalAddress can define the host address of the server. (If specified as an asterisk (*), the matching – result returned will be all local IP addresses.) – LocalPort defines the port on which the server is listening. If an asterisk is specified, the matching result will be all available ports on the server. – Action specifies the action to be performed. (The value must be ‘allow’ or ‘deny’.) Protocols is a list of protocol names to match. (One of the following protocols must be specified: http, https, t3, t3s, giop, giops, dcom, or ftp.) If no protocol is defined, all protocols will match a rule. |
3. If the rule does not take effect after saving, it is recommended to restart the WebLogic service (restarting the WebLogic service will cause business interruption, and it is recommended that relevant personnel evaluate the risk before proceeding with the operation). Taking the Windows environment as an example, the steps to restart the service are as follows:
Enter the bin directory in the directory where the domain is located, and run the stopWebLogic.cmd file to terminate the WebLogic service on Windows systems, while running the stopWebLogic.sh file on Linux systems.
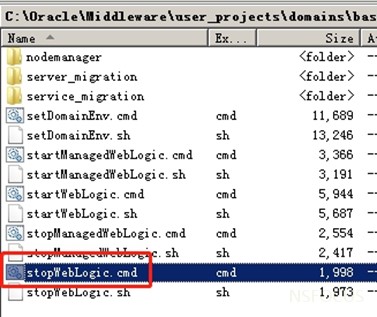
After the termination script execution is completed, run the startWebLogic.cmd or startWebLogic.sh file to start WebLogic and complete the WebLogic service restart.
2) Disable IIOP protocol
Users can block attacks that exploit vulnerabilities in the IIOP protocol by turning off the IIOP protocol, as follows:
In the WebLogic console, select “Services” ->”AdminServer” ->”Protocol” and uncheck “Enable IIOP”. And restart the WebLogic project to make the configuration take effect.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.
