Intro
2021 witnessed a complex and changeable network security situation. Large-scale and targeted cyber attacks continue to grow. Critical information infrastructure is still the hardest hit area. Data leakages and industrial supply chain attacks occur frequently. While emerging technologies such as Big Data, Internet of Things, Artificial Intelligence and Mobile Payment boost the transformation and upgrading of digital business, new security risks are also exposed.
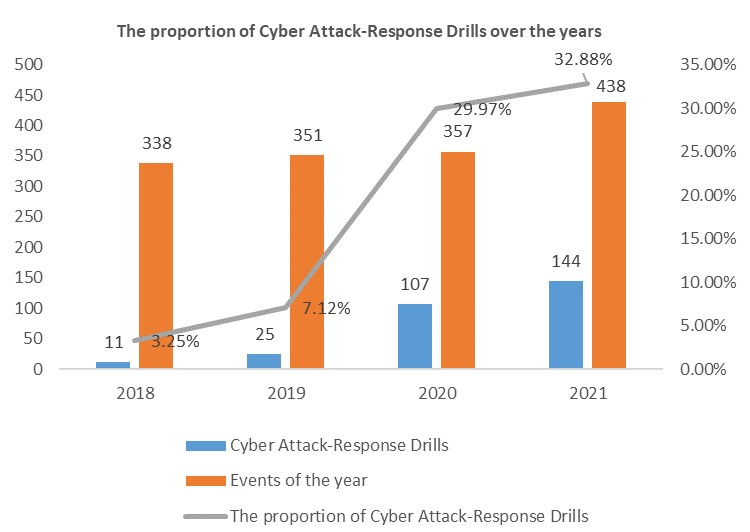
In 2021, the total number of security emergencies that NSFOCUS responded to is 438, a 20% increase from the previous year. In the first quarter, the number of incidents remained at a normal level, but increased by 286% in April compared with that in March, and then returned to the normal level since May. Overall, it showed a flat trend. The top 5 security events are phishing attacks, backdoor incidents, blackmail software, virtual mining and Trojan horse programs.
By summarizing the security events in 2021, we have the following findings:
Critical information infrastructure is the key target of network attacks
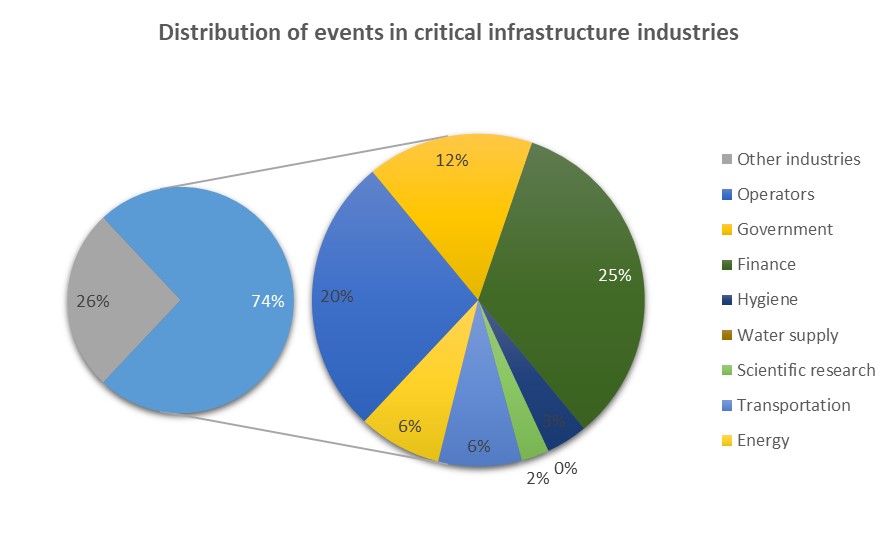
According to the records of security incidents in 2021, the industries involved critical infrastructure are still the key targets of network attacks, and relevant security incidents account for 74%. Public communication and information services, energy, transportation, water conservancy, finance, public services, e-government, Defense Tech and other critical information infrastructure related industries are still continuously attacked by hackers.
Security incidents in financial industry accounted for the first place for four consecutive years
Due to the huge system, complex businesses, large transaction volume and high concurrency of financial industry, it is easy to have security flaws in the system and process, which provides an opportunity for hackers for the purpose of economic interests, and the financial industry has also become a high incidence area. In 2021, the security incidents in financial industry NSFOCUS handled accounted for 25%, which decreased significantly compared with the data of 2018 (40%), 2019 (30%) and 2020 (35%) in the past three years, but still ranked first.
“Actual combat” is the trend of network attack and defense
With the increasing number of all-round, practical and confrontational Cyber Attack-Response Drills, the proportion of responses to drill requests in the total emergency responses has increased annually. Due to the improvement of security awareness and the growing scale of attack and defense drills, the number of both basic and disclosed vulnerabilities has decreased in the emergency response during Cyber Attack-Response Drills, while the utilization of 0-day and 1-day vulnerabilities has increased, so do the threshold of vulnerability utilization and attack cost.
Driven by interests, the risk of enterprise data disclosure has increased significantly
In recent years, the number of events involving data leakage NSFOCUS handled has increased, among which Telecom fraud has led to serious personal information data leakage. Enterprises do not keep the user’s personal information properly. The information is sold after being obtained by attackers and finally flows to Telecom fraud, which in turn stimulates the attacks for users’ information, forming a vicious circle.
Phishing is still the mainstream means of penetration
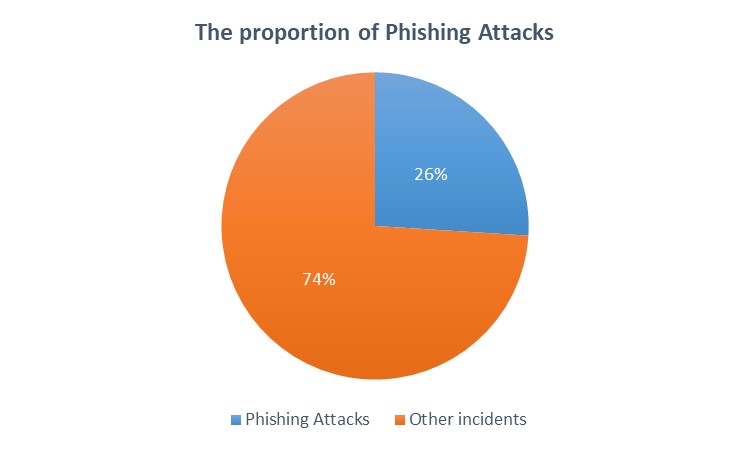
Due to the weakness of human nature, people are always the Achilles’ heel in security protection. Among the emergencies handled by NSFOCUS in 2021, phishing incidents (phishing attacks, phishing websites, phishing emails, etc.) accounted for 26%. The victims are mostly people with weak preventive awareness and unfamiliar with the login operation of mobile banking or online banking.
Extortion attacks become diversified and complicated
According to the observation of blackmail events in 2021, it is found that the means of extortion attacks tend to be diversified and complex. Ransomware technology includes credential access, horizontal movement, detection, persistence, defense evasion, etc. It should be noted that 49% of ransomware is capable of defense evasion. It can be speculated that today’s ransomware attacks are not only limited to simple scanning, brute force and encryption, but also use more complex means to hide themselves and obtain high profits.
Hacker attacks on decentralized financial system affect interests of mining groups
According to the analysis of security emergencies of NSFOCUS in 2021, mining viruses still invade mainly by means of Redis / SSH / SQL Server / RDP and other weak password blasting, and the related security events increased by 125% compared with last year. However, when the mining gangs deliberately attacked others to make profits, their “wallet” is also a target for some hackers. According to the reported statistics, the attacks on decentralized financial system accounted for 76% of all major hacker attacks in 2021.
Cloud security incidents are increasing
In 2021, COVID-19 prompted enterprises to move their business to the cloud. In the past three years, the number of security incidents in cloud environment has continued to grow. Through the statistics of events in 2021, it is found that the security events caused by cloud intrusion are mainly mining software (29%), backdoor (19%) and blackmail software (15%).
Service providers on the upstream side have become the main targets of hackers
The software supply chain can be divided into three major parts: development, delivery and operation. When there are security vulnerabilities in products of upstream developers, not only the developers but also many third-party customers will be affected, which can cause a wide range of damage. The vulnerabilities are even hard to prevent for successfully hiding themselves thanks to the developer’s signature. Hackers also notice the advantages of supply chain attacks, which causes attacks such as “SolarWinds supply chain attacks” occur frequently in recent years.
Security Recommendations
By analyzing the sources of security incidents, we found that the vast majority of incidents are related to the enterprise’s basic network security protection measures and management system. Therefore, we sorted out the following security protection suggestions for reference:
1) Safety awareness training
A research report shows that about 60% of the network attacks come from somewhere within the enterprise, and the vast majority of internal attacks are caused by employees being taken advantage of and controlled by external attackers. Methods of attackers include phishing emails, Watering hole, mobile text messages, social software, public WiFi, etc. Enterprises can strengthen security awareness of all employees through regular security awareness training and emergency drills.
2) Strengthen the management of password complexity
Weak password is a lingering problem. It is the vulnerability most easily ignored by enterprises and favored by attackers. For all IT assets of enterprises, it is necessary to set standards of password configuration to ensure complexity. Enterprises can also establish relevant specifications of security operation, business online process, baseline configuration verification to avoid the problem.
3) Make regular backup of important data
As a way of obtaining benefits directly, blackmail software is favored by attackers because of its remarkable attack effect, low attack cost and transaction anonymity. In addition to basic security protection, enterprises or individuals are recommended to backup data through private cloud, storage devices, network synchronization, etc.. This is the most effective countermeasure.
4) Strengthen vulnerability’s lifecycle management
Network attack methods and security vulnerabilities are constantly changing. The rapid change is also a significant feature of network security industry. Enterprises should take vulnerability management as a daily and continuous work, and establish detailed process standards, including development, vulnerability detection, vulnerability troubleshooting, vulnerability validation, etc. In addition, it is necessary to conduct Gray Box Testing regularly to detect the potential security vulnerabilities in the system, applications and network.
5) Strengthen the management of network boundary asset
We found that in most typical security incidents, attackers used the network boundary assets as a springboard to carry out horizontal expansion attacks on the internal network, causing a significant impact. Enterprises’ boundary assets exposed to the Internet for some businesses are often regarded as the primary goal of breaking through enterprise security protection by attackers. Enterprises can strengthen network boundary management through security domain division, firewall ACL refinement, application vulnerability protection and so on.
6) Monitor and prevent Internet sensitive information disclosure
Information collection plays a vital part in Black Box Testing. In addition to using search engines and big data to collect target exposed assets on the Internet, attackers will also collect leaked sensitive information, such as mailbox passwords, database configuration, application system source code, etc, through online disks, libraries, Git Hub and other channels. Enterprises should establish a long-term mechanism. While restricting employees’ behavior through management system, they also need to monitor the exposure of sensitive information on the Internet through technical means.
7) Focus on security risks of supply chain attacks
As a highly covert attack, supply chain attack may eventually affect even hundreds of millions of target users. The supply chain risks faced by enterprises mainly exist in multiple stages such as equipment procurement, software development, product delivery, and system operation and maintenance. IT supply chain security is a wide-ranging and complex system. Therefore, problems at any stage are bound to affect the security of the upstream and downstream sides of the supply chain. Enterprises should establish a management system of product procurement and supply chain manufacturer, a management system of application development life cycle safety, a notification mechanism for upstream and downstream security threat, etc. to grasp the security risks timely, and improve the efficiency of communication, coordination and emergency response.
8) Deploy threat traceability audit platform
The security equipment deployed at a single point cannot be managed and analyzed centrally, so it is often unable to detect attacks timely. Also, due to the lack of logs, samples and other key data, it is unable to make further traceability analysis. For business systems with high security protection requirements, malicious network attacks can be found in time by deploying situational awareness platform and combining with threat intelligence data. In addition, the full-flow storage and analysis platform can provide enterprises with the ability to capture unknown attacks and trace security events.