Santa Clara, Calif. March 16, 2023 – NSFOCUS, a global provider of intelligent hybrid security solutions, today released its “2022 Global DDoS Attack Landscape Report†which includes many findings to help organizations and users defend against DDoS attacks.
According to the report, The DDoS attack landscape remains challenging. The increasing number of DDoS attacks in 2022 is particularly significant, the number of terabit-level attacks increased to approximately 40 and attacks greater than 100 Gbps reached a record high with an attack exceeding 100 Gbps occurring every hour. Cybercriminals have become more and more strategic and tended to have clear targets. The analysis of the attack frequency reveals that the number of repeatedly attacked IP addresses in 2022 was significantly greater than that in 2021, which means a victim is likely to be attacked repeatedly by DDoS attacks once identified as a target. Obviously, the constantly changing threat landscape brings new challenges to DDoS protection.
The report also highlights that UDP-based DDoS attacks are the most commonly used attack method by cybercriminals, making up approximately 60% of total DDoS threat events in 2022. Notably, almost all terabit-level DDoS attacks are UDP-based attacks, including two third of non-reflective UDP attacks. It proves that today’s threat actors have controlled extremely abundant attack resources and can launch terabit attacks without needing UDP reflection to amplify traffic. All industries should expect these trends and the frequently occurring massive DDoS attack has been beyond the ability of on-premises solutions.
In addition to the network-layer attacks, the application-layer DDoS attacks should be paid more attention to. Compared with network-layer DDoS attacks, application-layer DDoS attacks are more difficult to detect and defend against because they establish reliable TCP connections, and the attack source IP addresses cannot be forged. If vast numbers of application-layer attack source IP addresses remain active in a region, it indicates that botnets are active there.
The same as in the previous annual DDoS attack landscape reports, NSFOCUS continuously tracks the activities of botnet families. According to the report, Mirai remains the most dangerous botnet in 2022, accounting for over half of all botnet activities and having the most significant number of compromised machines. The Gafgyt and BillGates botnets ranked second and third, respectively. The botnets were found to exploit critical vulnerabilities in Linux/IoT systems, with Mirai and Gafgyt exploiting nearly 100% of the top 20 vulnerabilities. Mirai also had the largest number of command-and-control servers. The botnets targeted the United States most frequently, with China and Germany also being targeted.
Download the Full Report to learn more.
Recommendation After the Report
A proactive approach to DDoS defense is essential to ensure that an organization’s critical services and infrastructure are well protected.
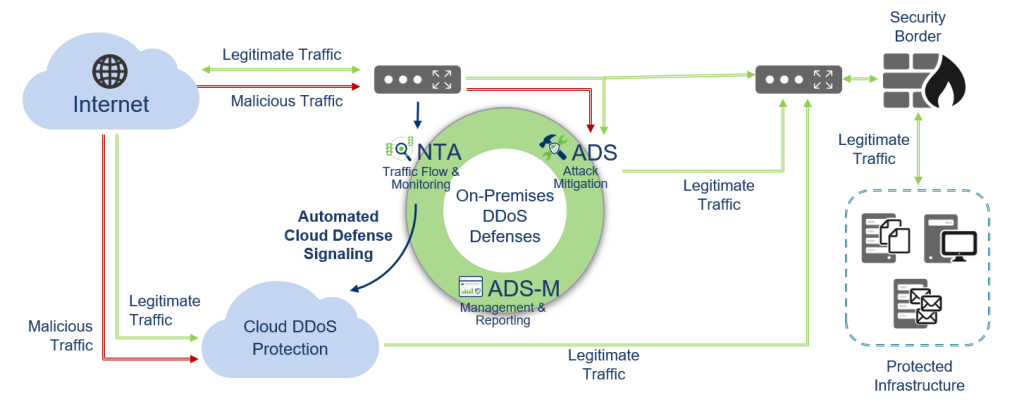
Skillful cybercriminals continuously evolve and adapt their tactics, and keep enhancing their attack capabilities. Defenders are difficult to predict their attack methods. NSFOCUS advocates that organizations should build a complete DDoS defense system in advance, not only for protection against common DDoS attacks with on-premises DDoS protection devices, but also for large-scale traffic protection with cloud-based DDoS scrubbing services that would be completely beyond the capabilities of an individual organization. The large-scale economy of a scrubbing provider can bring its clients a far more cost-effective DDoS protection approach.
NSFOCUS intelligent hybrid DDoS mitigation solution provides customers a better combination of on-premises protection, cloud-based services, and 24/7 support services.
Cloud Scrubbing Center
With 8 global Scrubbing Centers carrying Terabite level capacity. NSFOCUS Cloud DPS ensures its customers will be protected against even the largest DDoS attacks in history. By using the Anycast technology, NSFOCUS is capable of combining near-source traffic scrubbing with service nodes across the globe.
How It Works
NSFOCUS Network Traffic Analyzer (NTA) monitors network activities by receiving and analyzing traffic flow from border/edge routers. It uses an innovative, multi-stage DDoS detection engine with more than 30 vectors to identify DDoS attacks from other traffic streams accurately. Besides, the NTA supports multiple response actions, including BGP diversion, ADS diversion, FlowSpec BGP, and Remotely Triggered Black Hole (RTBH).
When the NTA detects a DDoS attack, it will execute according to the predefined traffic threshold and action policies. Different protection groups can set different policies. If the attack is within the bandwidth and mitigation capacity, NTA diverts the abnormal traffic only to the NSFOCUS Anti-DDoS System (ADS) for mitigation, not affecting the other normal traffic. After a multi-layered verification and challenge, the ADS blocks the malicious traffic and injects the legitimate traffic back into the original path. When the NTA sees the attack stops, it will also stop the traffic diversion. If a volumetric attack happens and exceeds the threshold, the NTA announces a BGP route to divert the traffic to the cloud scrubbing center. After mitigation, the clean traffic will route back to the customers.
Single Pane Of Glass
The customer portal on the active defense business operations system ( ADBOS) allows users to view the mitigation effect and traffic analysis of both on-premises appliances and cloud services through a single pane of glass. Multi-tenant design is user-friendly for service providers and reselling, and the Restful API also enables integration with 3rd party platforms.
Managed Security Service
Managed Security Service (MSS) is available to help customers relieve from cybersecurity issues and fully focus on their own business. With a globally located MSS team, customer business will be under 24/7 protection and support without hiring extra employees. The MSS team provides continuous protection policy optimization during the whole service period to make them always best-fit for customers’ business and attack defense.