NIPS aims to accurately monitor abnormal network traffic, automatically blocking various types of aggressive traffic in real-time, particularly application layer threats. It aims to take proactive measures instead of merely providing alerts at the time of or after detecting malicious traffic. When malicious traffic is detected and blocked, a threat log is recorded and displayed on the NIPS webpage for users to view, analyze, and trace the source.
The following describes how to troubleshoot the situation where the device fails to generate threat logs.
1. Check whether traffic passing NIPS
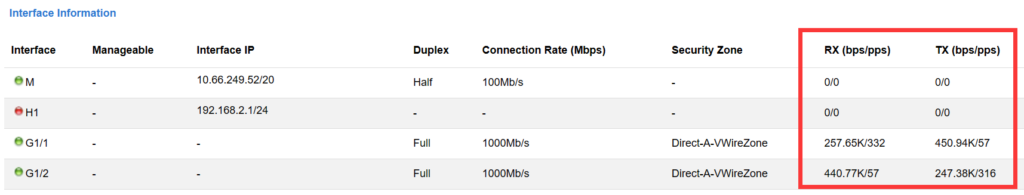
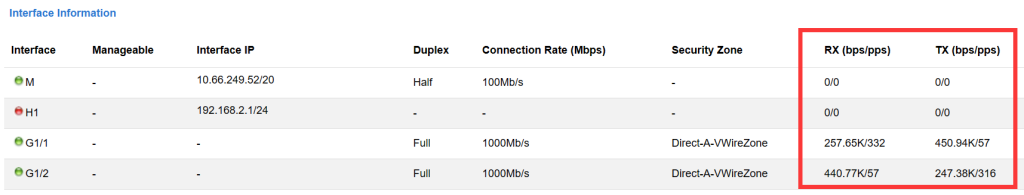
To confirm whether the interface has traffic, you can view it on the NIPS webpage Home -> State -> Interface Information.
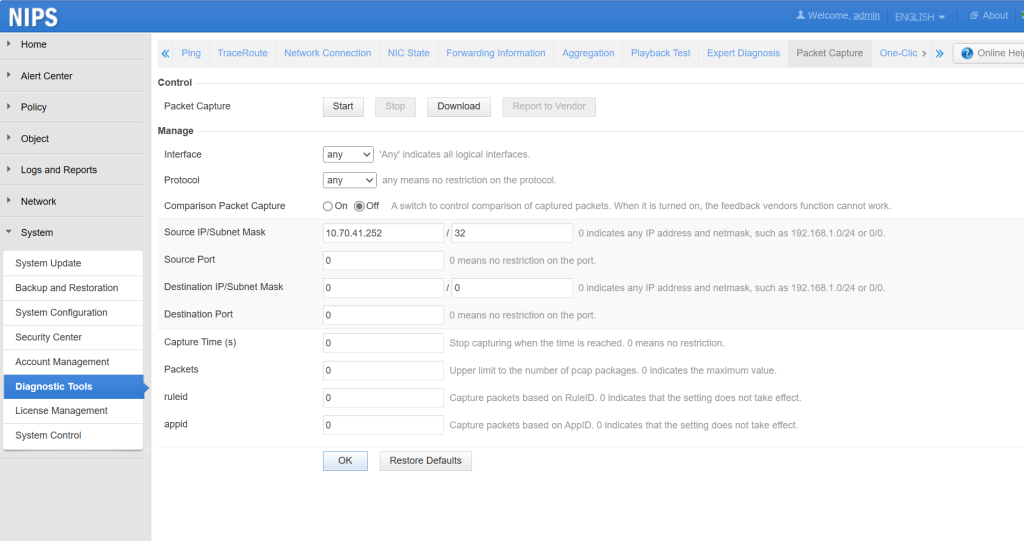
Confirm whether the IP traffic has passed through the device by capturing packets to analyze in System -> Diagnostic Tools -> Packet Capture.
2. Check whether the engine status is normal
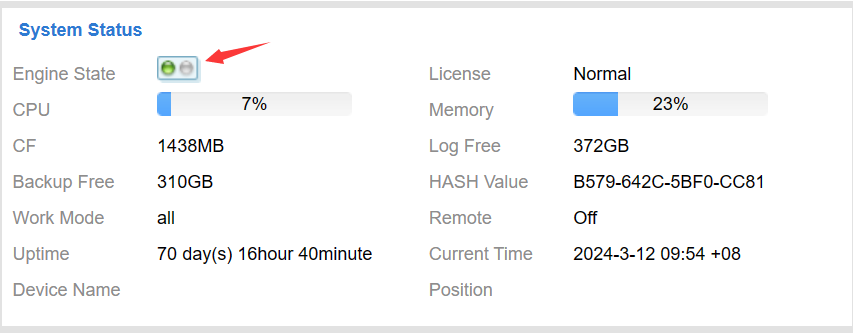
View the engine running status on the webpage Home > State > System Status > Engine State. The following figure shows the normal state: The green color of the engine indicates normal running.
Note: If the engine is not running properly, it is recommended to contact technical support (email: support@nsfocusglobal.com) for assistance.
3. Check NIPS policies
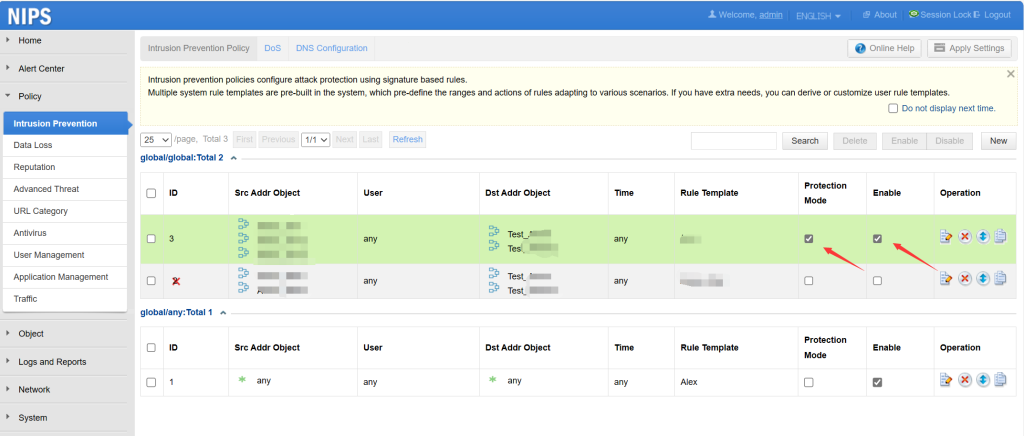
Check whether the policies in the Policy -> Intrusion Prevention are correctly configured, whether ‘Protection Mode’ and ‘Enable’ are clicked, and whether the security zone and address contain the traffic that needs to be checked.
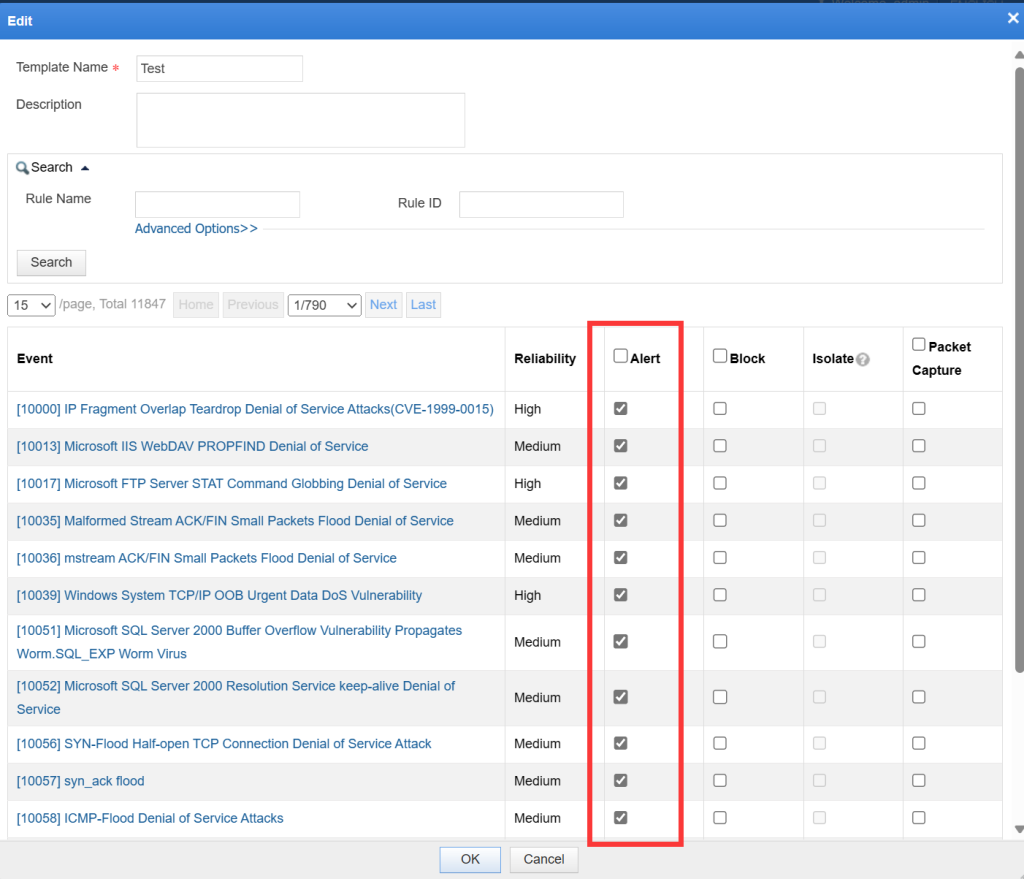
Check whether the action in the Object -> Rule -> Corresponding Rule Template is correct. For example, if not enabled Alert in the applied template, corresponding logs will not be generated.
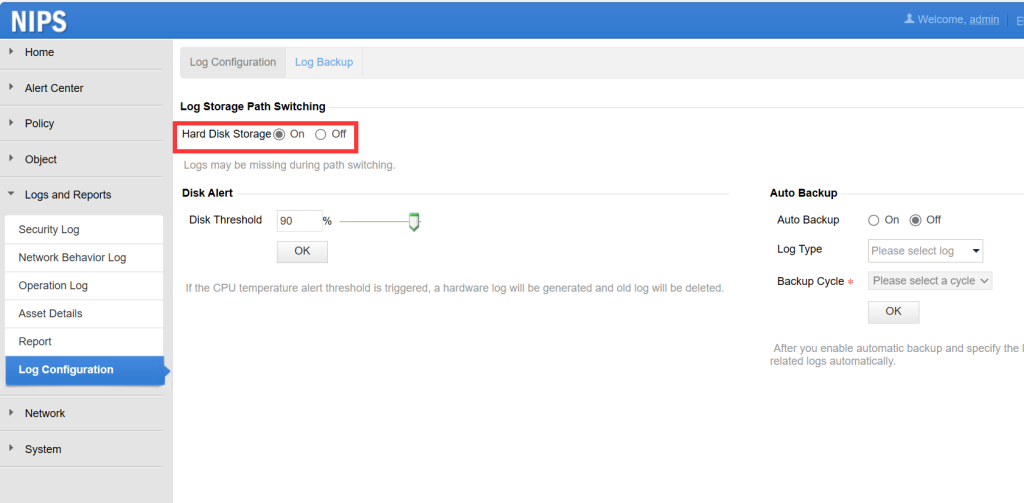
Check whether local storage of alert logs is enabled in Logs and Reports -> Log Configuration -> Log Storage Path Switching. Only after enabling it will logs be stored on the device.
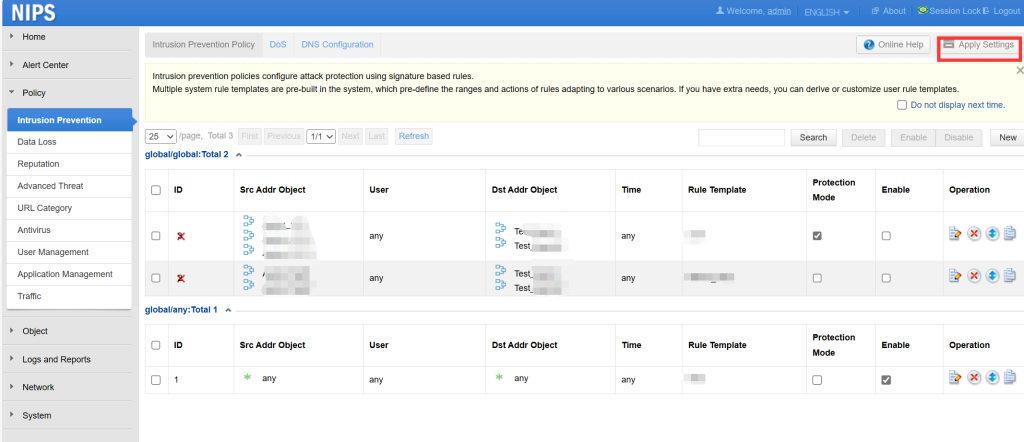
Check whether apply settings after configuring the policy
Note: Flashing ‘Apply Settings’ button in the upper right corner indicates that the configuration has not been applied.
Whether the corresponding IP is on the global blacklist or exception rules (Object -> Rule -> Exception Rule).
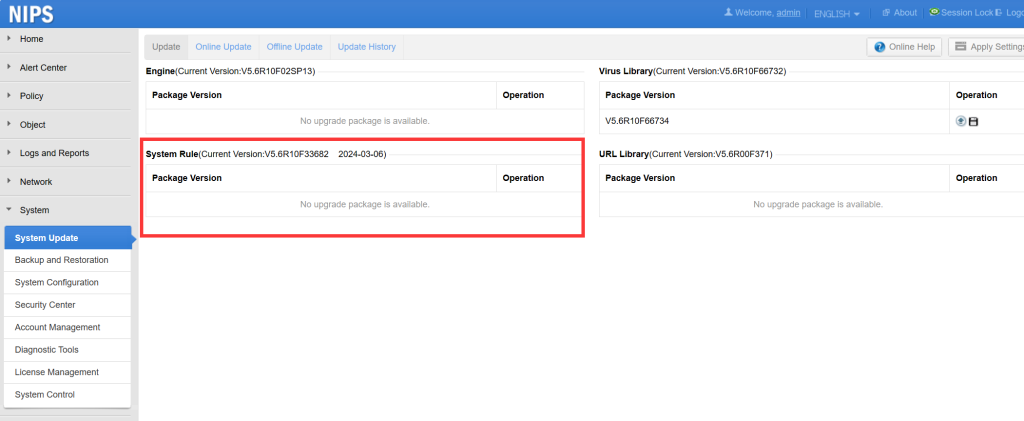
4. Check the rule library version
The characteristics of network attacks are constantly changing in real time, and rules are also being updated in real time. You are suggested to upgrade to the latest version of the device rule library to see if alerts can be triggered properly. The upgrade webpage can be found in System -> System Update.