On June 21, Red Hat officially released a security bulletin to announce the fix for a vulnerability in jackson-dababind. This vulnerability with a CVSS score of 8.1 affects multiple Red Hat products and a sophisticated exploit using this vulnerability is observed in the wild. On July 22, a security researcher named Andrea Brancaleoni published an article to analyze this vulnerability.
This vulnerability is caused by Jackson’s incomplete blacklist. An application that uses jackson-databind will become vulnerable when the enableDefaultTyping method is called via the ObjectMapper object within the application. An attacker can thus compromise the application by sending maliciously crafted JSON input to gain direct control over a server.
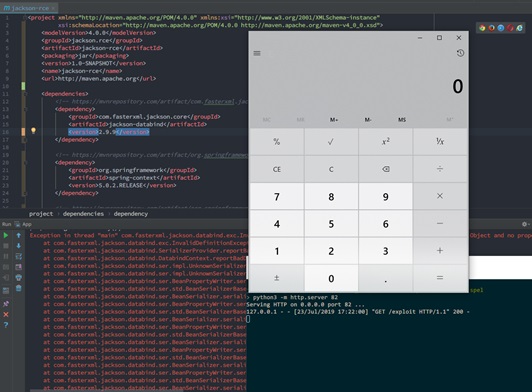
Currently, a proof of concept (POC) exploit for this vulnerability has been publicly available. All users who are affected by this vulnerability should upgrade to the latest versions as soon as possible to fix this issue. The following is a successful exploitation of this vulnerability.
Reference:
https://blog.doyensec.com/2019/07/22/jackson-gadgets.html
2.Scope of Impact
Affected Versions
- Jackson-databind 2.X < 2.9.9.1
Unaffected Versions
- Jackson-databind 2.9.9.1
- Jackson-databind 2.10
3.Vulnerability Detection
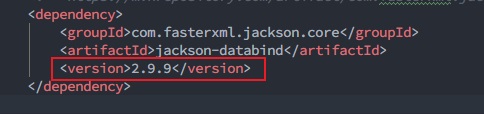
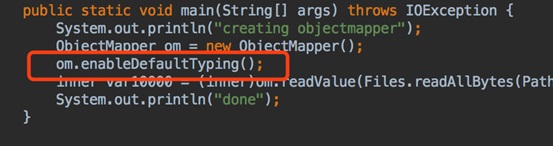
If the enableDefaultTyping method is called via the ObjectMapper object within an application that uses the jackson-databind component, this application will become vulnerable. Developers are advised to check whether the jackson-databind component is used in applications, and if so, to further check its version number and whether the enableDefaultTyping method is called in the code. The following uses the Maven project as an example to show how to check the use of jackson-databind.
Check whether jackson-databind is included in xml and, if so, whether its version is earlier than 2.9.9.1.
If the answers to the preceding two questions are both “Yes”, check whether the enableDefaultTyping method is called in the code. If so, it is recommended that the component be upgraded immediately and the web application be restarted.
4.Mitigation
-
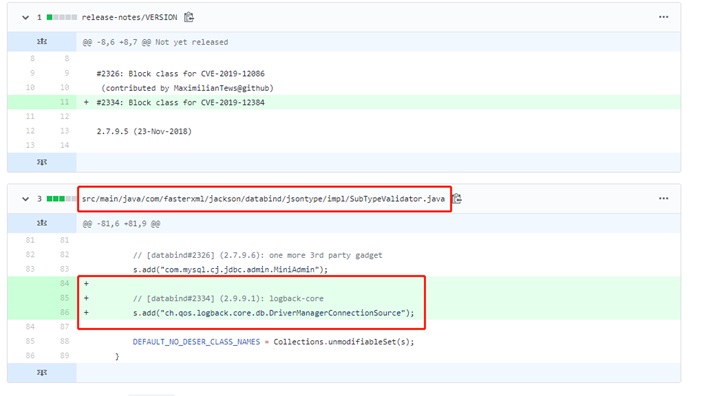
Official Fix
The vendor has fixed this vulnerability in jackson-databind 2.9.9.1. Users of this software are advised to upgrade to 2.9.9.1 or later as soon as possible to protect against this vulnerability:
Download link: https://github.com/FasterXML/jackson-databind/releases
Developers can upgrade and compile jackson-databind by configuring Maven as follows:
| <!– https://mvnrepository.com/artifact/com.fasterxml.jackson.core/jackson-databind –>
<dependency> <groupId>com.fasterxml.jackson.core</groupId> <artifactId>jackson-databind</artifactId> <version>2.9.9.1</version> </dependency> |
The new major version (3.x) of jackson-databind will address this issue via a new API layer that provides a way to achieve whitelisting-based serialization for these polymorph classes.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.