Background
On October 7th, accompanied by the launch of thousands of rockets, the Palestinian Islamic Resistance Movement (Hamas) declared a military operation against Israel.
As real-world conflict escalated, hacktivist organizations from various countries, including Russia, India, Indonesia, and Iraq, began engaging in continuous cyber warfare within the cyberspace domains of both sides. The primary methods of attack involve Distributed Denial of Service (DDoS), data theft, website defacement, and other cyber attack techniques. In addition to executing cyber attacks, hacktivist groups supported by various factions also use text, images, and videos to propagate narratives favorable to their own side, influencing public opinion.
According to NSFOCUS Security Labs, as of October 13th, a total of 55 groups have participated in attacks, with the majority being pro-Palestinian hacker groups. This includes 43 pro-Palestinian cybercriminal groups, including Killnet, targeting Israeli critical infrastructure in sectors such as government, finance, and communications. There are comparatively fewer pro-Israeli organizations, with a total of 12, mainly led by organizations like India Cyber Force and UCC, directing their attacks toward Palestinian critical infrastructure.
Attack Overview
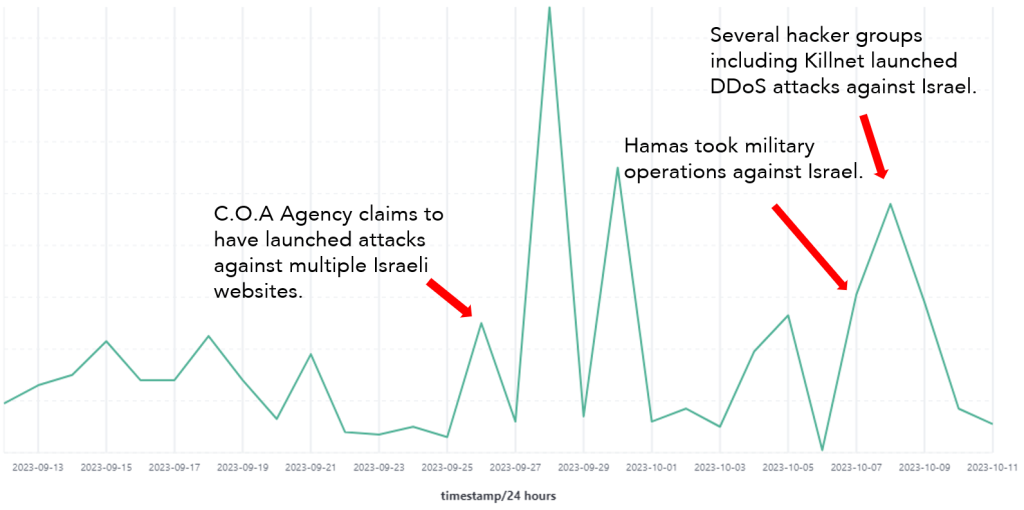
Overview of DDoS Attacks Against Israel
DDoS attacks targeting Israel exhibited a noticeable upward trend starting from September 26th, reaching its peak on the 28th. Subsequently, on October 8th and 9th, Hamas initiated military actions against Israel, leading pro-Palestinian hacker groups to intensify their attacks on Israeli websites, expanding the scope of the attacks.
The DDoS attack activity on September 26th may be related to the Cyber Operations Alliance (C.O.A Agency), which claimed responsibility for conducting DDoS attacks on multiple Israeli websites. The attacks on October 8th and 9th were associated with several hacker groups, including Killnet.
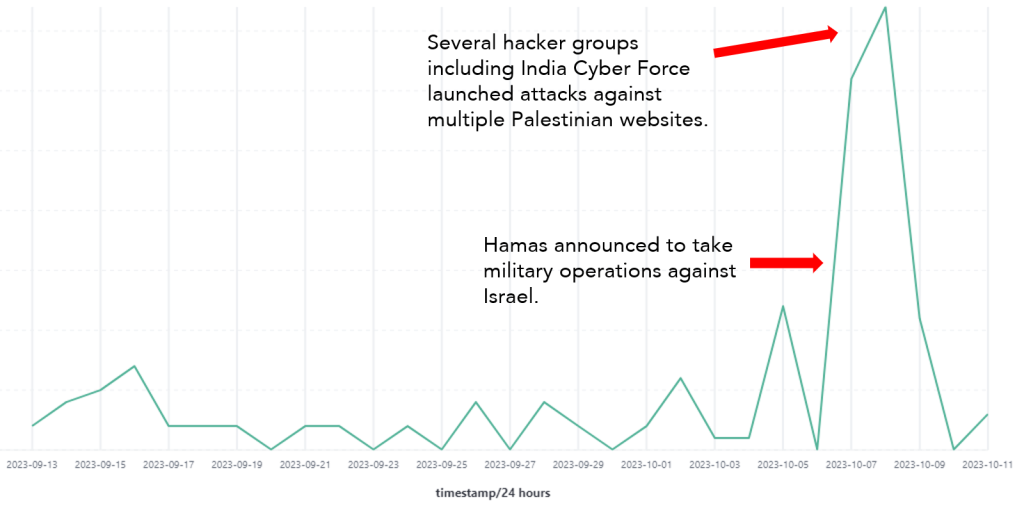
Overview of DDoS Attacks Against Palestine
DDoS attacks against Palestine experienced a significant increase on October 8th and 9th, with pro-Israel organizations such as India Cyber Force and Garuna Ops claiming responsibility and conducting DDoS attacks on Palestinian network infrastructure.
Key Attack Events Monitoring
Monitoring of Attacks Targeting Israel
In cyberspace, NSFOCUS’s global threat hunting system has detected a series of DDoS attack activities against Israel. The primary targets are government, judicial, military, power, and other critical websites. In addition, email services and DNS services have also been targeted.
Furthermore, according to the monitoring, it’s evident that DDoS attack methods have evolved. To bypass or evade DDoS defense devices’ detection, the attack targets not only focus on open service ports but also use random high-numbered ports as targets. The port range falls between 1026 and 65525.
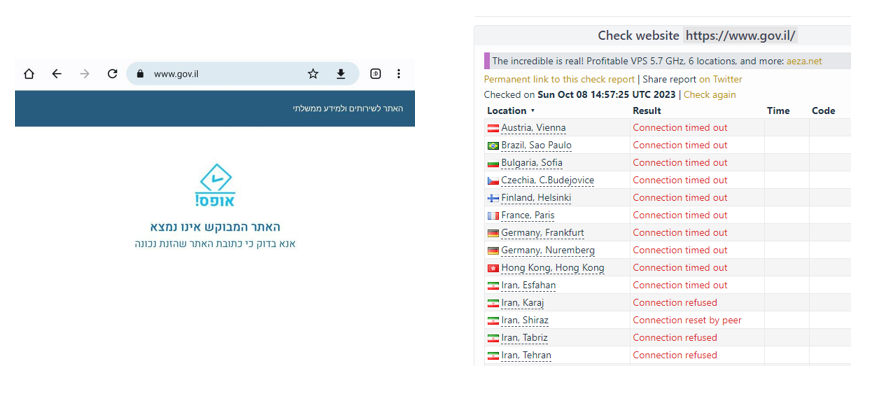
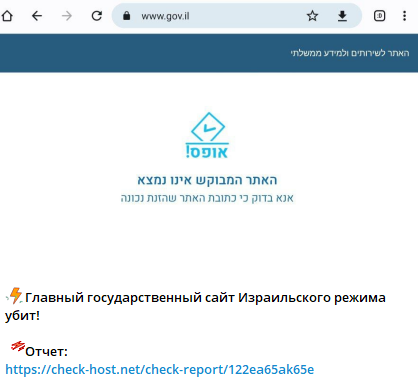
Attacks on Israeli Government Official Websites
At 4:53 AM, 23:43 PM on October 8 (Beijing time), and 12:23 AM on October 9, DDoS attacks were observed on the official Israeli government website (www.gov.il). The main targets of the attack were ports 53 (DNS service) and 443 (Web service). To avoid detection, the attack also targeted random high-numbered ports, including ports 47884, 33166, 45224, and others.
This may be related to the Killnet organization, which claimed to attack the website at 10:59 PM on October 8, causing it to go offline. This corresponds with the monitoring of the organization’s attack targets.
Attacks on the Israeli Defense Forces Email System
Email systems play a crucial role in communication, especially for key units. During wartime, frequent and critical information exchange is essential. Email system disruption can result in immeasurable losses.
On October 9, at 12:36 AM and 12:18 PM (Beijing time), the Israeli Defense Forces’ email system was subjected to two DDoS attacks. The second attack lasted until 8:01 PM and exhibited strong targeting. It continuously attacked mail.idf.gov.il and mail1.idf.gov.il, targeting the SMTP service (port 25/TCP). The aim was to disrupt the enemy’s communication system during wartime, temporarily rendering their communication “blind”.
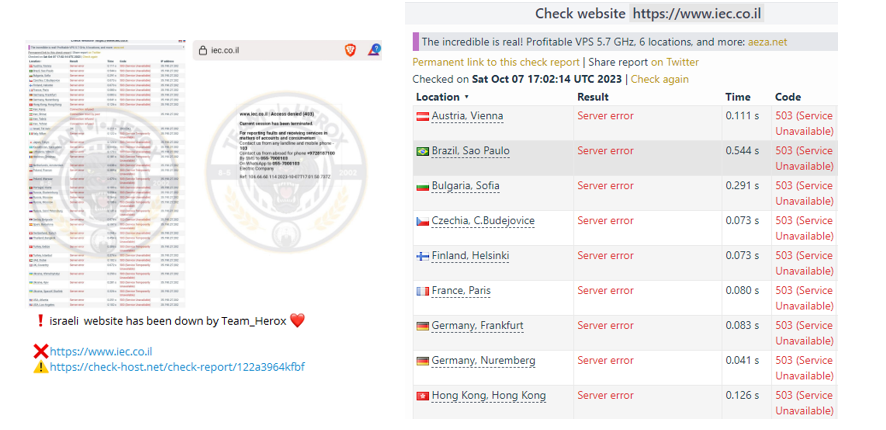
Attacks on the DNS Service of the Israel Electric Company
The Israel Electric Company (IEC is the largest electricity provider in Israel and the Palestinian territories. IEC is responsible for constructing, maintaining, and operating power plants, substations, and power distribution networks in Israel, with its installed capacity making up approximately 75% of the country’s total power generation. It transmits and distributes nearly all the electricity used in Israel, including that generated by other producers, highlighting its significance.
Additionally, the DNS service plays a crucial role in domain name resolution. When it is disrupted, the impact is significant, as it prevents all users who rely on that DNS from resolving any websites, affecting website access in an entire region or even the entire country. An attack on the DNS service of this company can disrupt the internal network of the power system.
NSFOCUS’s global threat hunting system confirmed the attack claim made by the TEAM HEROX organization, which attacked the company’s website and caused its service unavailable.
On October 9, at 2:16:05 AM (Beijing time), monitoring detected the attack organization using 79-byte UDP packets from global nodes to attack the IEC’s DNS service (ns1.iec.co.il) on port 53/UDP.
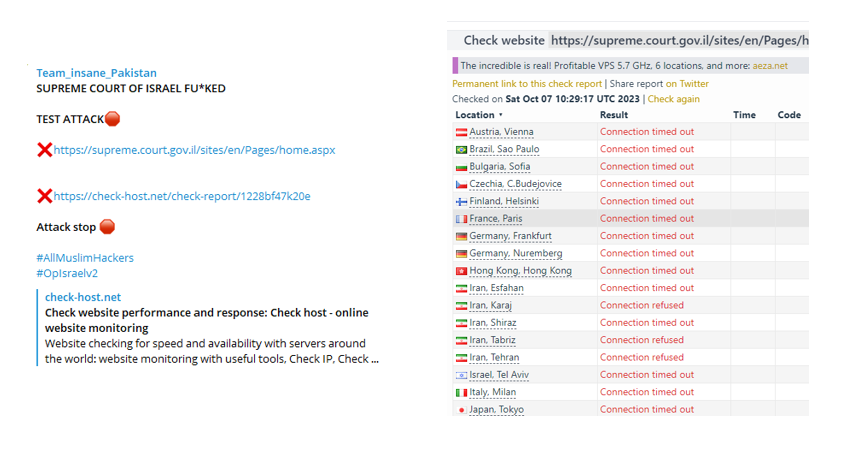
Attacks on the Israeli Supreme Court Website
On September 29th at 13:03:33 Beijing time, the Israeli Supreme Court website (supreme.court.gov.il) on port 443 experienced a DDoS attack lasting for over one hour. On October 7th, the same website faced an attack from Team Insane Pakistan.
The Israeli Supreme Court is the highest judicial authority within the Israeli legal system, located in Jerusalem. In the past, it has handled numerous lawsuits related to the Israeli-Palestinian conflict, the rights of Arab-Israelis, and differential treatment of Jewish communities. Additionally, the Supreme Court has the authority to intervene in the military actions of the Israel Defense Forces, which might be a reason for the attacks on the website.
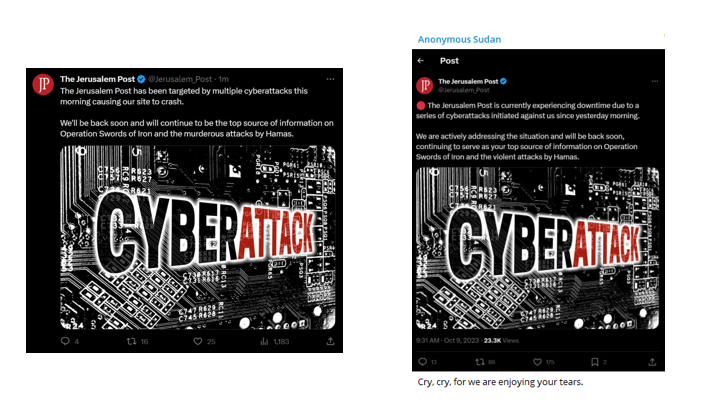
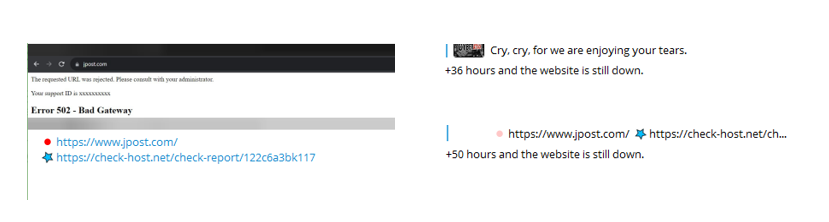
Attacks on the Jerusalem Post Website
News websites are crucial sources for the public to receive information, especially during significant events. DDoS attacks on such websites can disrupt public access to information and their understanding of current events.
The Jerusalem Post (www.jpost.com) is the most widely circulated English newspaper in Israel and serves as an important international media outlet. It is more susceptible to DDoS attacks. On October 9th at 01:35:25 Beijing time, the website on port 443 experienced a DDoS attack using global DDoS reflection nodes, lasting for over 24 hours. The website’s official Twitter account confirmed multiple DDoS attacks and service interruptions, which aligns with the claims of an attack on the website made by the Anonymous Sudan organization on their Telegram channel.
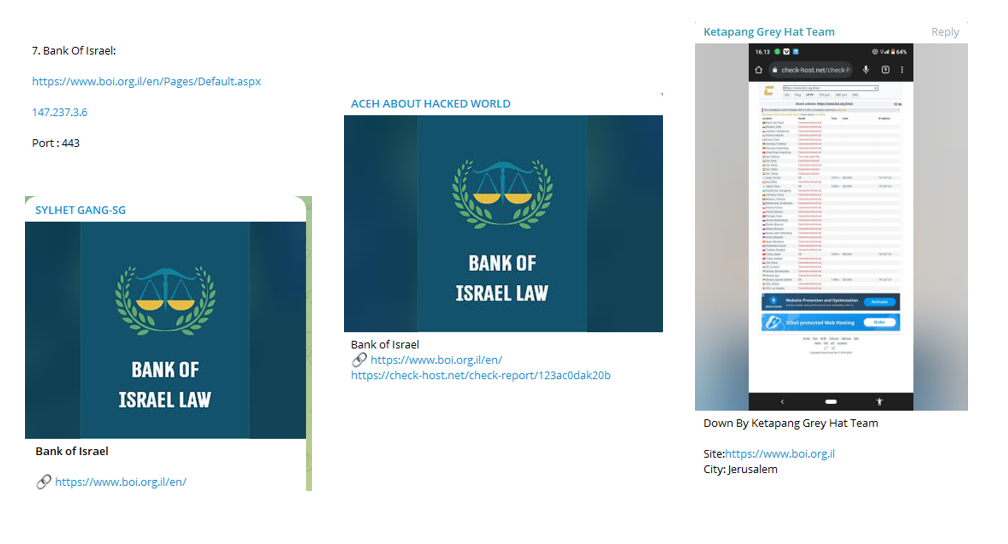
Attacks on Israeli Banks
On October 9th at 00:04:30 Beijing time, it was observed that the website of Israeli banks (www.boi.org.il) on port 443 was subjected to a DDoS attack, lasting for 1 hour and 3 minutes.
This website experienced attacks from multiple hacker organizations, including Team Insane Pakistan, SYLHET GANG-SG, ACEH ABOUT HACKED WORLD, Ketapang Greyhat Team, and others. This aligns with the monitoring data indicating such attacks.
The Bank of Israel is the central bank of the State of Israel. It was established in 1954 and is located in the ancient town of Binyamin in Jerusalem, near the Knesset (Israeli Parliament), the Supreme Court, and government offices. The Bank of Israel operates independently, with its goals and operational methods defined in the Bank of Israel Law 5770-2010. Its objectives include maintaining price stability, supporting government objectives, especially in terms of growth and employment, and ensuring the stability of the financial system.
Attacks on the Israel Internet Association Website
On October 9th at 05:18:37 Beijing time, it was observed that the website of the Israel Internet Association (register.isoc.org.il) on port 443 was subjected to a DDoS attack. To avoid detection, the attack also targeted port 43, lasting for 1 hour and 10 minutes.
The Israel Internet Association is dedicated to promoting the Internet and its integration into Israel’s technological, research, educational, social, and business infrastructure. It is responsible for managing the registration of “.il” and “.ישר×ל” domain names, as well as the ongoing operation of the Israel Internet Exchange (IIX). This allows secure, fast, and unrestricted access to Israeli and global websites and online services from anywhere at any time.
Monitoring of Attacks on Palestine
In cyberspace, NSFOCUS’s Global Threat Hunting System detected a series of DDoS attack activities targeting Palestine, primarily focusing on government and telecommunication websites.
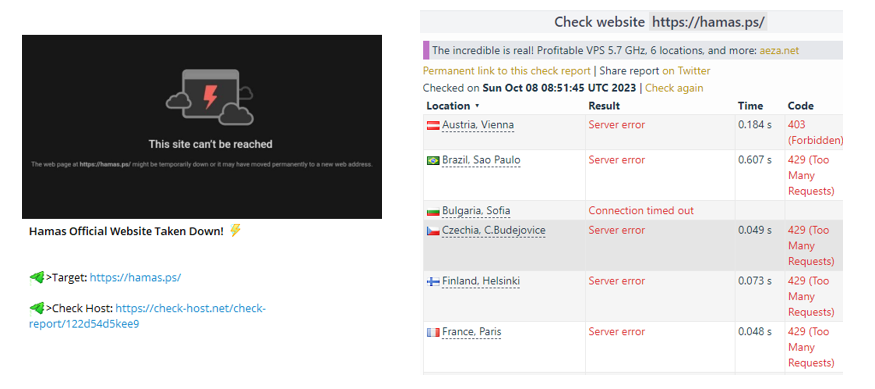
Attacks on Hamas Official Website
As the initiator of the conflict, it is expected that Hamas-related network infrastructure would be among the primary targets. The Global Threat Hunting System observed multiple DDoS attacks on the organization’s official website. These attacks occurred on October 8th at 05:34:44 AM and on October 9th at 12:34:57 AM Beijing time. The attacks targeted port 443 of the Hamas official website (hamas.ps). During the attacks, each attack packet used random high-numbered ports, including 51204, 27653, and 51207. The attacks lasted for 25 minutes.
This aligns with the related statement from the India Cyber Force organization on Telegram, which declared on October 8th at 4:58:00 PM that they had successfully rendered the website inoperative.
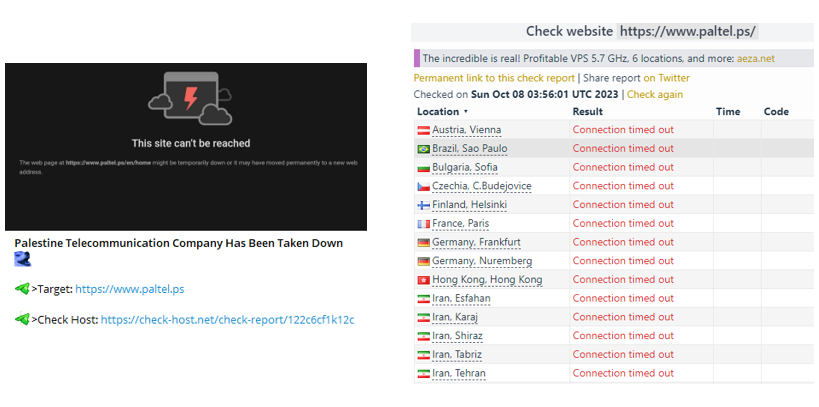
Attacks on the Palestine Telecommunications Company Website
Telecommunication companies play a vital role in facilitating communication, and during times of conflict, they become significant targets. When such a company ceases its services, it can have a significant impact on national operations. The India Cyber Force organization targeted this website and claimed to have paralyzed it on October 9th at 12:05.
On October 9th at 02:23:46 Beijing time, NSFOCUS’s global threat hunting system observed multiple port attacks on the company’s website, including ports 53, 80, and 443, among other important ports. The attack targets varied in port sequence, focusing on ports 53, 443, and 80.
Monitoring of Threat Actors
NSFOCUS’s global threat hunting system conducted continuous foreign monitoring of the cyberspace conflict between Israel and Palestine. In this conflict, hacktivist actions involve network attacks, and the cyberspace battle is divided into two camps: pro-Palestinian organizations and pro-Israel organizations. DDoS attacks are primarily used by both sides to paralyze their attack targets, rendering them unable to provide services. The main targets of these attacks are government websites, with military, intelligence, education, and financial sites also affected. For instance, Anonymous Sudan claimed responsibility for an attack on the Israeli Iron Dome system, a mobile all-weather air defense system designed to intercept rockets within a range of 5 to 70 kilometers.
As of October 13, there are a total of 43 pro-Palestinian organizations and 12 pro-Israel organizations, originating from various countries.
Overview of Pro-Palestinian Organizations and Attack Targets
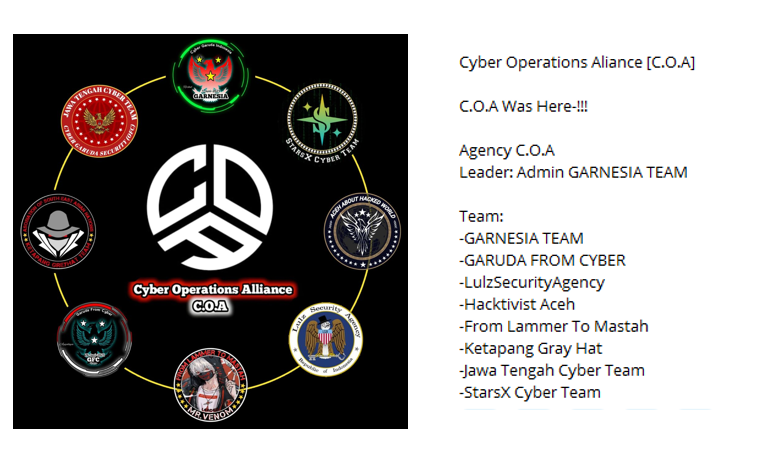
Several hacker groups openly support Hamas and have carried out DDoS attacks mainly targeting Israeli government websites. These hacker groups primarily consist of two major entities: the Killnet Hacker Group and the C.O.A Agency.
- Killnet Hacker Group: This group includes Killnet, Anonymous Sudan, and ЛЕГИОР– КИБЕРСПЕЦÐÐЗ РФ V2 (Cyber Special Forces) organization.
- C.O.A Agency: Comprises 8 different hacker groups.
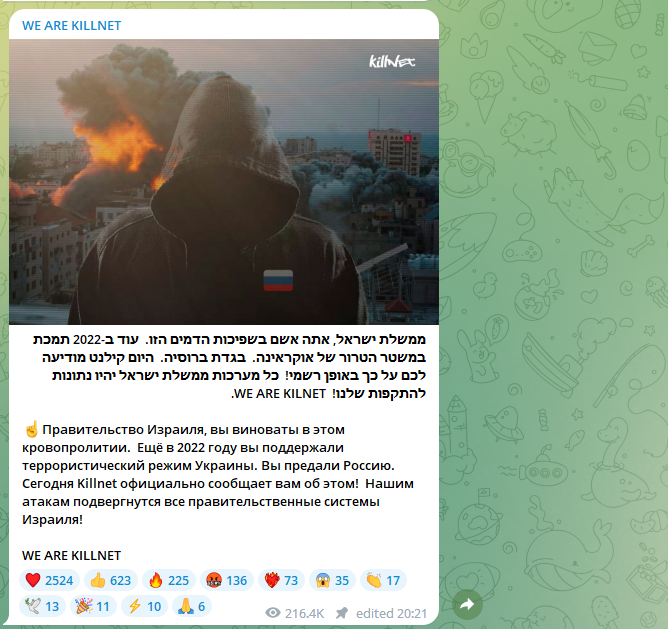
Killnet Organization and Their Activities
Killnet is a pro-Russian hacker organization known for conducting DoS (Denial of Service) and DDoS (Distributed Denial of Service) attacks against government institutions and private companies from various countries during Russian-Ukrainian conflict in 2022.
On October 8th, Killnet posted comments on their Telegram social platform account, indicating their intention to attack Israeli government websites. This was subsequently shared on the ЛЕГИОР– КИБЕРСПЕЦÐÐЗ РФ V2 (Cyber Special Forces) Telegram channel, indicating the participation of ЛЕГИОР– КИБЕРСПЕЦÐÐЗ РФ V2 in the attacks on Israel.
Shortly afterward, they posted screenshots of breached targets, including the Israeli government’s official website.
On the evening of October 8th at 23:13, Killnet announced plans to coordinate an attack with Anonymous Sudan, which was subsequently shared on Anonymous Sudan’s Telegram channel.
On the early morning of October 9th, while conducting cyberattacks, Killnet also published an article to shape public opinion, claiming that their attacks were for “peace” and only targeted the Israeli government. After breaching websites, they sent out messages for a ceasefire, attracting public attention.
At 03:55 on October 9th, Killnet launched a successful attack on the Israeli Security Agency, Shabak. Shabak is part of the Israeli intelligence system and is responsible for counterintelligence activities and ensuring internal security, functioning similarly to the FBI and FSB.
Table 4.1 Killnet’s Attack Targets
| Target | Website | Type |
| Israeli government official websites | https://www.gov.il | Government |
| Shabak official website | https://shabak.gov.il | Military |
| Freelance service provider recommendation | https://www.interman.co.il | Public Service |
| Kitchen customization and design | https://chenkitchens.co.il | Public Service |
| Information systems implementation training | https://khl.co.il | Public Service |
| Wine sales | https://wewines.co.il | Public Service |
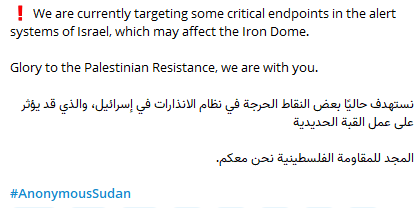
Anonymous Sudan Organization and Their Activities
“Anonymous Sudan” is a group of hacktivists who claim to be from Sudan and are motivated by religious and political reasons. Since January 2023, they have been conducting DDoS attacks driven by religious motives against several Western countries. Due to a shared target during an attack in Sweden, Killnet officially declared “Anonymous Sudan” as part of their cluster of hacktivists targeting Western countries and countries opposing Russia. Subsequently, “Anonymous Sudan” has used Killnet’s reputation and influence to develop its members and has become one of the most prominent hacktivist organizations in 2023.
Similar to the Killnet organization, Anonymous Sudan launched attacks on October 8th at 01:41, primarily targeting critical endpoints within the Israeli alert system and claiming potential impacts on the Iron Dome.
Ten hours later, the organization attacked the Jerusalem Post, causing it to be paralyzed. Subsequently, on October 9th, they conducted multiple rounds of attacks, rendering the website unable to provide normal services for over 50 hours. NSFOCUS’s global threat hunting system monitored these attack activities.
Table 4.2 Anonymous Sudan’s Attack Target
| Target | Website | Type |
| Jerusalem Post | https://www.jpost.com/ | Media |
ЛЕГИОР– КИБЕРСПЕЦÐÐЗ РФ V2 (Cyber Special Forces) Organization and Their Activities
This organization created its Telegram channel on August 5, 2023, and publicly announced itself, claiming to consist of Russians and recruiting new members. It is affiliated with the Killnet group and primarily employs DDoS attacks.
Within 5 minutes of Killnet’s announcement of attacking Israel, ЛЕГИОР– КИБЕРСПЕЦÐÐЗ РФ V2 organization shared related statements and joined in the attacks on Israel. This organization mainly targets bank websites.
On October 9th, they attacked multiple bank websites, including Bank Mercantile Discount Ltd (mercantile.co.il), Discount Bank (discountbank.co.il), and Bank of Jerusalem (bankjerusalem.co.il).
Table 4.3 ЛЕГИОР– КИБЕРСПЕЦÐÐЗ РФ V2’s Attack Targets
| Target | Website | Type |
| Bank Mercantile Discount Ltd | https://discountbank.co.il/ | Bank |
| Discount Bank | https://mercantile.co.il/ | Bank |
| Bank of Jerusalem | https://bankjerusalem.co.il/ | Bank |
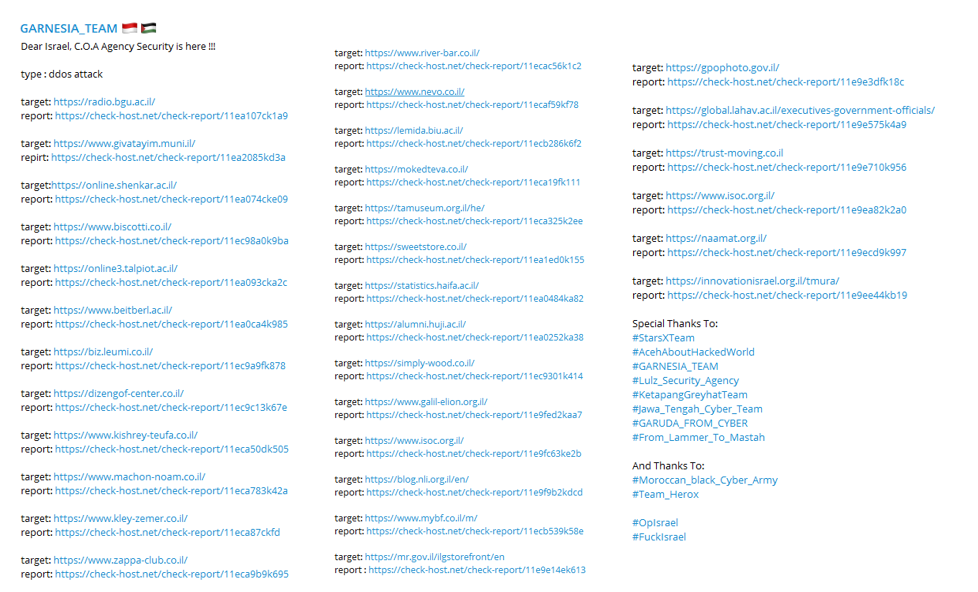
C.O.A Agency and Their Activities
C.O.A Agency, composed of 8 hacker organizations, was formed on September 24, 2023. They primarily conducted DDoS attacks targeting India. On September 26, they began their attacks against Israel and officially declared their support for Palestine’s involvement in attacks against Israel on October 8.
Their attack targets encompass various sectors, including government, healthcare, and education.
Table 4.4 C.O.A Agency’s Attack Targets
| Target | Website | Type |
| Government service appointment website | https://govisit.gov.il/ | Government |
| National Rights Index website | https://mybenefits.gov.il/ | Government |
| Israeli Ministry of Agriculture and Rural Development | https://agri.gov.il/ | Government |
| Israeli Tax Authority | https://www.shaam.gov.il/ | Government |
| Healthcare Center | https://www.poria.health.gov.il/ | Healthcare |
| Israeli Education | http://apps.education.gov.il/ | Education |
| Teacher Portal | https://poh.education.gov.il/ | Education |
| Peace Now website | https://peacenow.org.il/ | Society |
| Israeli Accessibility Association | https://www.aisrael.org | Society |
Overview of Pro-Israel Organizations and Attack Targets
Several hacker criminal groups, including India Cyber Force, openly supported Israel and, on October 8th, claimed that they would carry out cyberattacks on the Palestinian region.
India Cyber Force Organization and Attack Activities
India Cyber Force is an Indian hacker organization that claims to be the official network defense unit of the Indian Army.
On October 8th, they announced that they would launch cyberattacks on the Palestinian region.
Subsequently, within two days, they successfully carried out attacks on several critical Palestinian websites, including those in the government, communication, and financial sectors. Additionally, the organization compromised over 200 network devices in Palestine, including devices from schools and hospitals.
Table 4.5 India Cyber Force’s Attack Targets
| Target | Website | Type |
| Hamas Official Website | https://hamas.ps/ | Governmental Group |
| Palestinian Government Postal Website | https://www.webmail.gov.ps/ | Government |
| Palestinian Telecommunications Company Website | https://www.paltel.ps | Communication |
| Palestinian National Bank Website | https://www.tnb.ps/en | Fincance |
| Ministry of Transportation and Communication Website | http://www.mot.gov.ps | Transportation |
| Ubuy Website | https://www.ubuy.com.ps/ | E-commerce |
Garuna Ops Organization and Attack Activities
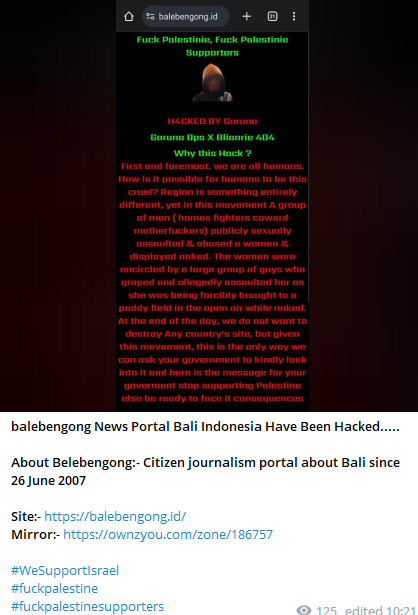
On October 8th, this organization issued a statement warning other countries that support Palestine and called for non-Muslim hackers to attack Palestine.
This attack organization primarily targets news websites in other countries, including Bali News and Bangladesh National Information Broadcasting Network, with the aim of shaping local public opinion.
Table 4.6 Garuna Ops’s Attack Targets
| Target | Website | Type |
| Bali News Website | https://balebengong.id/ | Media |
| Bangladesh National Information Broadcasting Network Website | http://www.bangladesh.gov.bd/ | Government |
UCC Organization and Attack Activities
On October 8th, the UCC organization forwarded the statement issued by the Garuna Ops organization on its Telegram channel and officially launched cyberattacks against Palestine on October 9th.
These attacks targeted various Palestinian entities, with a primary focus on DDoS attacks against government websites.
Table 4.7 UCC’s Attack Targets
| Target | Website | Type |
| Palestinian Ministry of Foreign Affairs and Expatriates Website | http://www.mofa.pna.ps | Government |
| Palestinian Government Website | https://www.palgov.ps/ | Government |
| Palestinian Social Solidarity Fund Website | http://www.takaful.gov.ps/ | Government |
| Palestinian Public Procurement Policy Higher Council Website | http://www.shiraa.gov.ps/ | Government |
| Palestinian Supreme Judicial Council Website | https://www.courts.gov.ps/ | Government |
| Palestinian Lireh Deir Ghazi Elementary School Website | http://awardedu.gov.ps/ | Education |
Conclusion
1. Communication Services and Network Infrastructure Are Main Targets of DDoS Attacks
Looking at the online competition between the two sides in the Israel-Palestine conflict, DDoS attacks target not only web servers but also DNS services and critical email services. Compared to traditional web service attacks, targeting DNS services and critical email services has a more significant impact. If DNS services are disrupted, it affects domain name resolution in the entire region, rendering various services such as websites and email inaccessible, causing interruptions in network communication. If critical email services are disrupted, it leads to communication interruptions, affecting the transmission of crucial information, temporarily causing “blindness” in communication.
2. Cyber Warfare Extends Beyond the Warring Parties, Often Triggering Chain Reactions
Cyber warfare is not confined by geographical boundaries and can be initiated at any time and place. This results in online warfare extending beyond the warring parties, with multiple hacker organizations from different countries participating in cyberattacks. In this conflict, hacker organizations from countries such as Russia, India, Pakistan, and Indonesia participated in the attacks. Once various hacker organizations align themselves, apart from attacking network facilities within the warring parties’ borders, the “war” of online attacks can spread to the countries of these hacker organizations, causing a series of attack responses and triggering chain reactions, resulting in more extensive attacks.
3. Cyberattacks and Information Warfare Intertwine, Good and Evil Coexist
Hacker organizations supporting both sides have carried out a series of malicious cyberattacks in the online space, including DDoS attacks, data theft, website defacement, etc., disrupting and damaging the network infrastructure of the opposing side. Their primary targets are crucial websites in sectors such as government and finance, implying a broad impact, potentially affecting entire countries. However, in addition to cyberattacks, these attacking organizations also publish articles and alter the content of the attacked websites to influence public opinion, claiming that their actions are just and that their “evil” cyberattacks are for the people and for “justice.”
4. Hacker Organizations Are Not Always Solitary Entities; They Quickly Form Temporary Interest Groups During the War
Looking at the online competition between various hacker organizations during the Israel-Palestine conflict, these organizations are not always solitary actors. Organizations with similar interests will show solidarity and quickly form interest groups during times of “war.” While these organizations usually operate independently, their shared interests during times of “war” lead to a rapid alliance, expanding their attack capabilities. Examples of such groups during the Israel-Palestine conflict include the Community Network Operations Alliance (C.O.A), Killnet, and Anonymous Sudan, among others. Additionally, many hacker organizations temporarily assemble and join attacks due to their interest demands.
About NSFOCUS Security Labs
Founded in 2000, the NSFOCUS Security Labs is an internationally recognized cyber-security research and threat response center at the forefront of vulnerability assessment, threat detection and mitigation research.
NSFOCUS Security Labs focuses on eight key research domains that address the most critical concerns in the cybersecurity industry.