When you configure a protection policy for your protected website and set the protection action to block, NSFOCUS WAF supports three methods to execute blocking actions: Source IP Block, Session Block, and UA Block. Session Block and UA Block are newly added on system version 6073. Each block supports three forms: Never, Permanently block, and Block as customized.
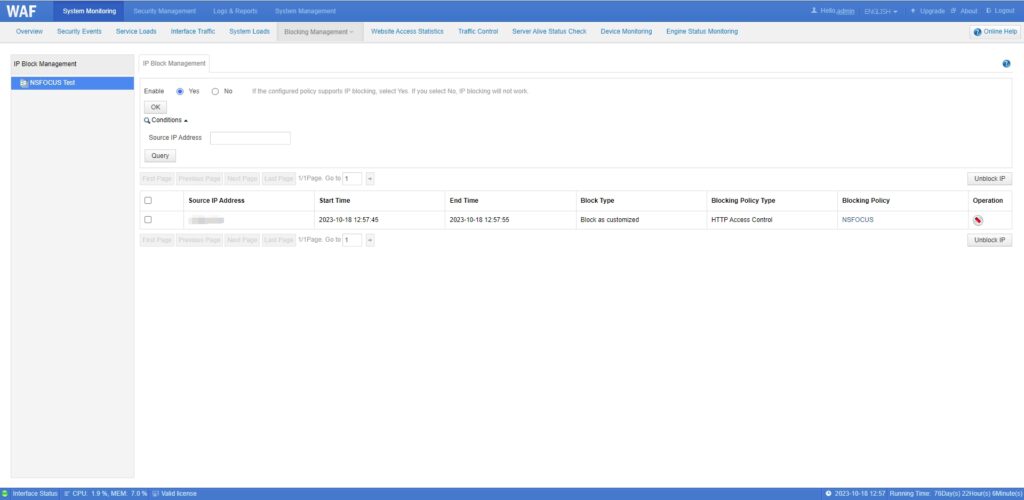
- Source IP Block
If a request triggers the source IP block, NSFOCUS WAF will add the client IP address of the web security logs to the IP block list. NSFOCUS WAF will detect the source IP addresses of the following HTTP or HTTPS requests, requests from the IP addresses on the block list will be interrupted. If not match, the requests will go through other protection policies.
Tips:
If NSFOCUS WAF enables proxy mode, the source IP address on the proxy header will be blocked.
By default, at most 80000 IP addresses can be blocked.
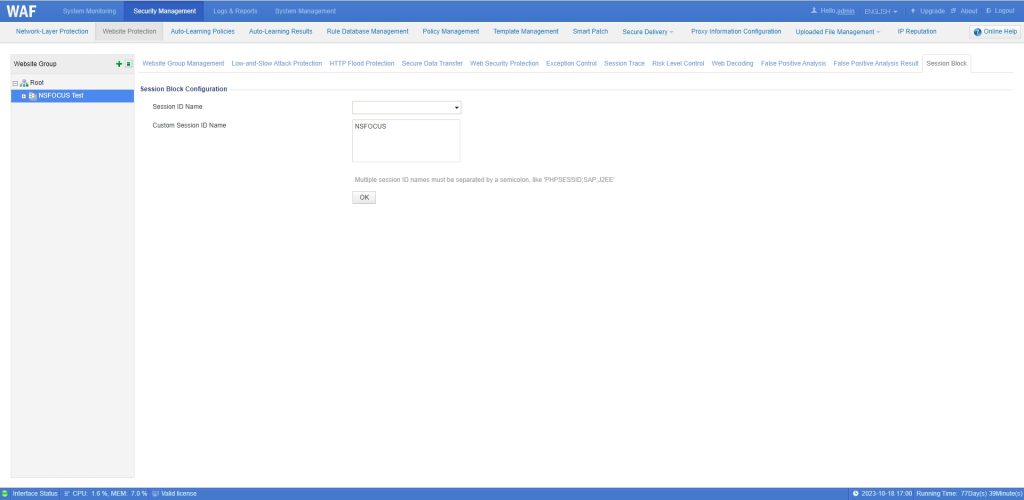
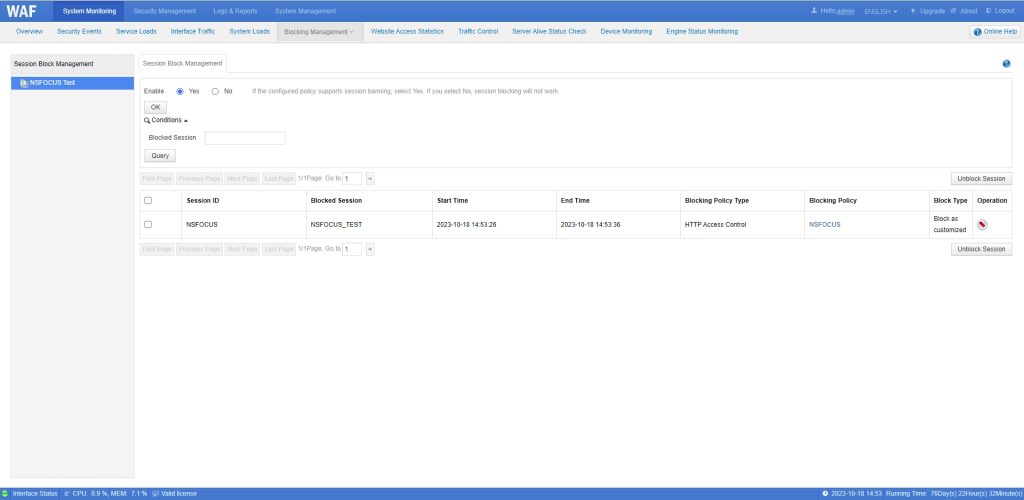
- Session Block
If a request triggers the Session block, NSFOCUS WAF will add the key and value of the cookies header to the block list. NSFOCUS WAF will detect the cookies header of the following HTTP or HTTPS requests, requests with the same key and value on the block list will be interrupted. If not match, the requests will go through other protection policies.
You can configure the session ID to be detected for each website group. Cookies that do not belong to the session ID do not participate in the detection and are not added to the session block list.
Tips:
By default, at most 10000 sessions can be blocked.
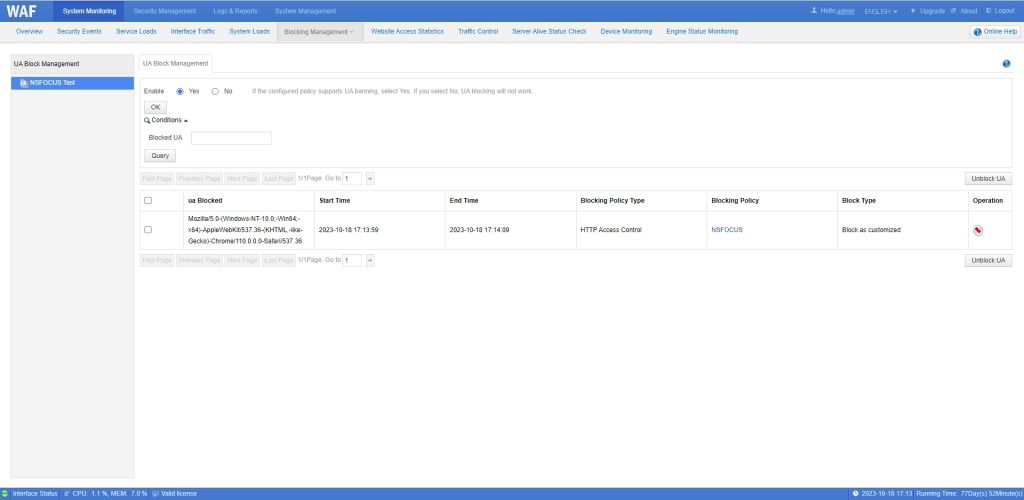
- UA Block
If a request triggers the UA block, NSFOCUS WAF will add the value of the User-Agent header to the block list. NSFOCUS WAF will detect the User-Agent header of the following HTTP or HTTPS requests, requests with the same User-Agent on the block list will be interrupted. If not match, the requests will go through other protection policies.
Tips:
Since the User-Agent entry string usually contains spaces, but the blocked list file is divided by space, in order to avoid data storage reading errors, the User-Agent space is replaced by a short horizontal “-” when storing.
By default, at most 10000 sessions can be blocked.