What Is DDoS?
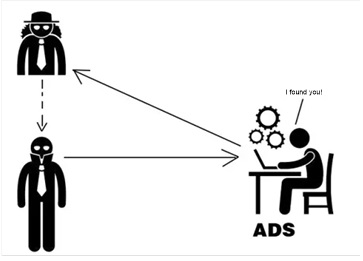
Look at the following example:
Assume that you run a shop that is doing well.
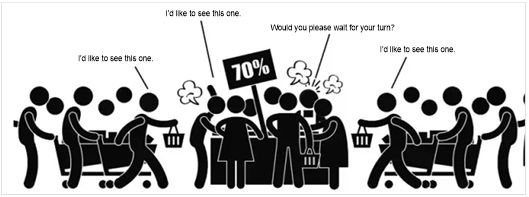
At this time, your neighbor, Mr. Wang (or whatever his name is), whose business is slack, looks at you as an eyesore.
Therefore, he hires a group of hooligans.
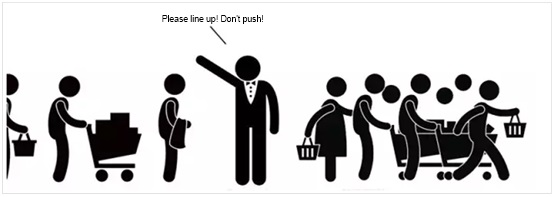
Then you find that your shop is crowded with customers, who look around and ask lots of questions, but do not buy anything at all. Worse still, they just linger there and do not leave.
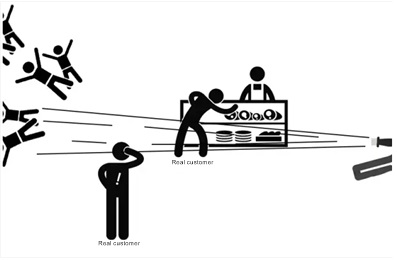
Your shop is so overcrowded that your real customers cannot get inside there. These fake customers come to the shop for evil intentions, like blocking the door, taking up space, and chatting with shop assistants. This is just what a DDoS attack looks like, which is initiated by hackers through zombies with a Trojan backdoor on the network. It disguises itself as normal traffic data, making it impossible for traditional firewalls or other protective devices to identify which traffic is illegitimate.
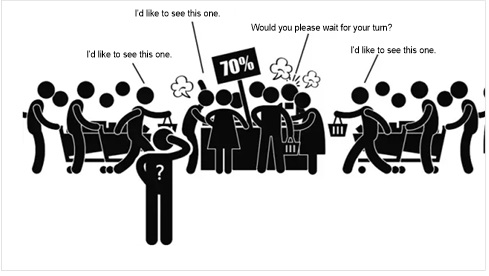
Therefore, you need a professional to clean up the scene.
This is why NSFOCUS Anti-DDoS System (ADS) is launched.
How Does NSFOCUS ADS Accurately Identify Illegitimate Traffic?
- Anti-spoofing: NSFOCUS ADS checks the authenticity of IP addresses and ports of packets and conducts reverse detection.
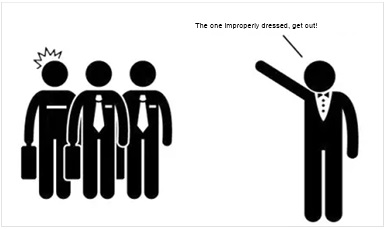
- Protocol stack behavior pattern analysis: Each type of packets should conform to the RFC standards which specify a standard method of encapsulating packets. It’s just like the dress code that each employee in the company should abide by. As long as there are packets that fail to comply with such standards, NSFOCUS ADS will identify and filter out them.
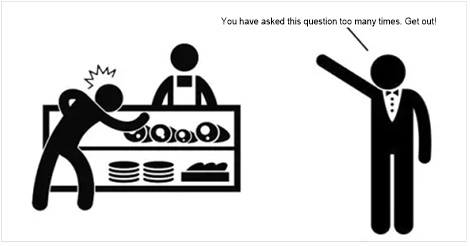
- Specific application protection: Illegitimate traffic always has certain characteristics. It seems like you mingle with a group of customers, your illegitimate behavior such as asking the shop assistant the same question too many times and repeating the same action will make you exposed and discovered.
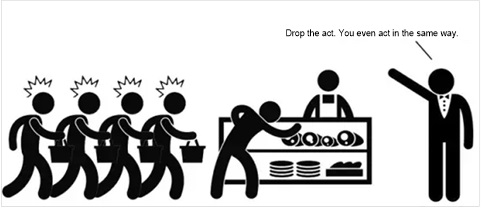
- User behavior pattern analysis: Legitimate traffic is generated by normal users whose behavior has no dramatic characteristics. It just like customers who get into a shop, have a casual look, ask the price, make comparisons or chat with the shop assistantwhen having no idea what to buy. By contrast, all illegitimate traffic is sent to access a certain point in a massive way, acting in concert to accomplish a malicious purpose. Therefore, those illegitimate traffic has distinctive characteristics and can be detected by NSFOCUS ADS.
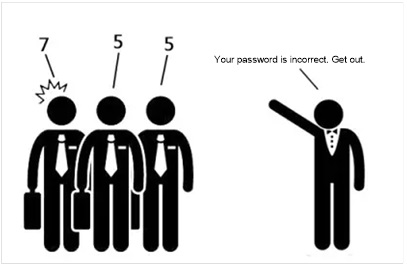
- Dynamic fingerprint recognition: All legitimate traffic is secured with encryption algorithms. This is just like each packet that is authenticated with an assigned password before being accepted by the server. Packets without a password or with an incorrect password will be directly filtered out by NSFOCUS ADS.
- Bandwidth control: When there is too much access data, NSFOCUS ADS can limit the maximum output traffic to reduce the pressure on the downstream network system.
Three-in-One Deployment of NSFOCUS ADS
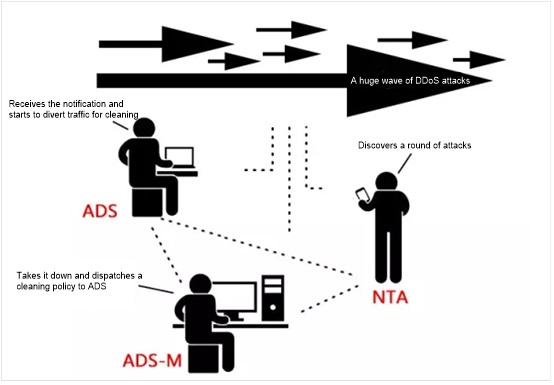
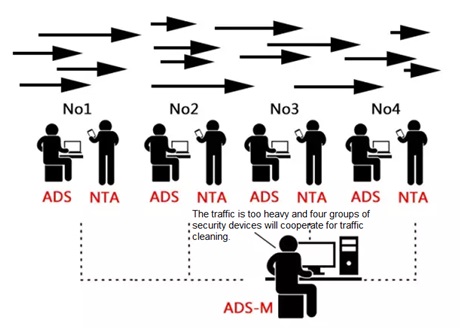
NSFOCUS ADS can be deployed in out-of-path mode. Generally, it continuously monitors the network and diverts the traffic for cleaning only when abnormal traffic is spotted. After cleaning, ADS inserts the handled traffic back to the network system. NSFOCUS ADS, NSFOCUS NTA, and NSFOCUS ADS M constitute NSFOCUS’s three-in-one cleaning solution.
If the customer’s network environment is complicated and suffers an attack characterized by a large number of packets, NSFOCUS’s three-in-one solution can give a good account of itself in such a scenario: In this solution, ADS can generate intelligent cleaning policies which enable it to work to its best and NSFOCUS ADS M can make a correlative analysis of and handle ADS’s status data.
In a large-scale network environment such as a Metropolitan Area Network (MAN) or Internet data center (IDC), these devices can be deployed in several groups to handle the volumetric attacks in a load balancing way.
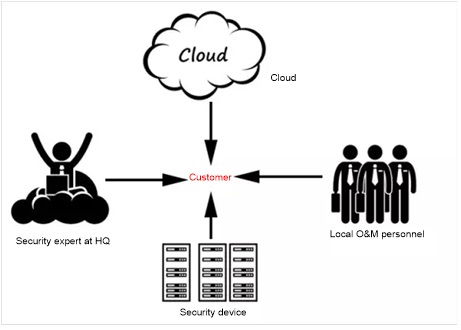
Also, NSFOCUS has built a security system integrating the cloud, remote/local experts, and devices. After buying the product, what you get is far beyond the product. The local  or remote security experts can provide prompt response and the policies on the cloud can be synchronized to all security devices timely. In other words, all-round protection is implemented.
Postscript
As DDoS attack tools increasingly prevail and grow stronger, more security threats are emerging on the Internet. As the customer business systems rely more on networks, it is predictable that more DDoS attack events will occur on an even large scale and cause more severe losses. Since the losses caused by DDoS attacks are still on the rise, it is an immediate concern for carriers, enterprises or governments to employ protection policies to secure their investments, profits, and services.
NSFOCUS ADS provides industry-leading DDoS attack monitoring and protection capabilities. Via multiple analysis and detection mechanisms and flexible deployment modes, NSFOCUS ADS can effectively block DDoS attacks and ensure proper transmission of legitimate traffic, thereby playing an important role in assuring the continuity and integrity of business systems.