Intro
The world of cybersecurity is rapidly changing and technologies continue to evolve and innovate. While emerging technologies on big data, Internet of Things, artificial intelligence, mobile payment, just name a few, are helping digital transformation, new security risks expose constantly.
Security incidents handled by NSFOCUS emergency response team in 2021 reaches 438, an increase of 20% compared to the previous year. From the perspective of victims, it is clearly shown that the critical infrastructure is still the main target. From the perspective of attackers, driven by interests, underground economy such as data theft, extortion, and mining continue to escalate while phishing attacks have become a powerful tool for network intrusion.
Here are some highlights from 2021 emergency incident observations.
Targeted phishing attacks continue to grow and become more targeted
The existence of human weakness makes people always the weakest point in security protection. For attackers, people are the most vulnerable in attacks. Among over 400 emergency incidents handled by NSFOCUS in 2021, phishing incidents (phishing attacks, phishing websites, phishing emails, etc.) accounted for 26%. Although people’s awareness of phishing prevention is gradually increasing, phishing attack vectors are also advancing constantly. As can be seen from the emergency cases in 2021, phishing attacks are still on a tear.
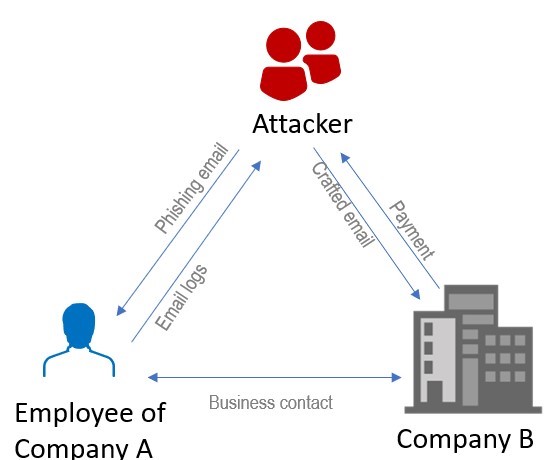
In terms of phishing attack vectors, attackers are not satisfied with wide-spread spams any more, but prefer to spear phishing, a measure more “technical†in social engineering and scams, that is, crafting highly precise and compelling emails to individuals performing specific tasks within a specific organization after obtaining, their sensitive data (such as their personally identifiable information or network access credentials). Once the target victim clicks the malicious link or opens the attachment, the attack conditions will be triggered for the attacker to complete the following illegal activities. In some emergency cases, attackers intruded investment companies and service companies by brute force or purchasing account passwords that have leaked, and then obtained mail permissions of their staff like account managers and customer support team members to collect customers’ information for phishing attempts. The phishing emails they sent may contain fake corporate website links, attachments with malicious code, or fake payment methods.
Attacks against security researchers are mainly implemented through social engineering. Take an example in 2021, the Lazarus APT organization created fake security researchers’ accounts on many social platforms. They firstly increased their visibility and enhanced the credibility of these accounts, and then started contacting some security researchers and launched two attacks by sending them malicious samples.
These sophisticated and targeted attack methods are getting popular with threat actors as they found that, instead sending tons of spams, the well-crafted spear phishing will bring them more profits.
Supply chain threats are projected to escalate
The globalization is also driving the globalization of supply chains, which not only expands the attack surface of attackers on the Internet, but also increases the potential scope of impact and the degree of harm that these attacks can cause. Due to devastating impacts, more and more attackers or APT organizations will be involved in such attacks in the interconnected cyber world.
The software supply chain can be divided into three major phases: development, delivery, and operation. When a security vulnerability discovered in products of upstream developers, not only these developers but also many third-party customers are affected, and the damage can be extremely extensive. It can even hide itself with the help of the developer’s signature, which is difficult to prevent. Attackers have also noticed the advantages of supply chain attacks, resulting in frequent attacks such as ” SolarWinds†supply chain attack in recent years.
Many application systems, for example Fastjson, Shiro and Chromium, are developed based on open source or commercial framework components. Once such mainstream frameworks are exposed to have vulnerabilities, the impact will be very extensive You may remember the Chromium kernel with two RCE vulnerabilities indirectly affects multiple browsers and widely used commercial software in 2021. Vulnerabilities can be exploited in many ways at any stage, which can easily lead to software supply chain attacks.
On December 9, 2021, the NSFOCUS Emergency Response Center detected that the epic vulnerability log4shell was disclosed online. Since the lookup function of Apache Log4j is capable of recursive parsing, JNDI injection can be implemented during log recording without authentication. Attackers can control part of the log content by sending a well-crafted data request packet. When the program logs the data entered by the user, this vulnerability will be triggered, thereby executing arbitrary code on the target server.
Apache Log4j2 is an open-source Java logging framework that is widely used in middleware, development frameworks and web applications to record log information. According to the MVN Repository, there are over 7,000 projects that directly reference log4j2 and more than 160,000 projects that indirectly reference Log4j2. This stirred an uproar in the security and IT industries, and many software vendors were affected, causing rethinking and worries about supply chain security.
Ransom attack vectors become diversified
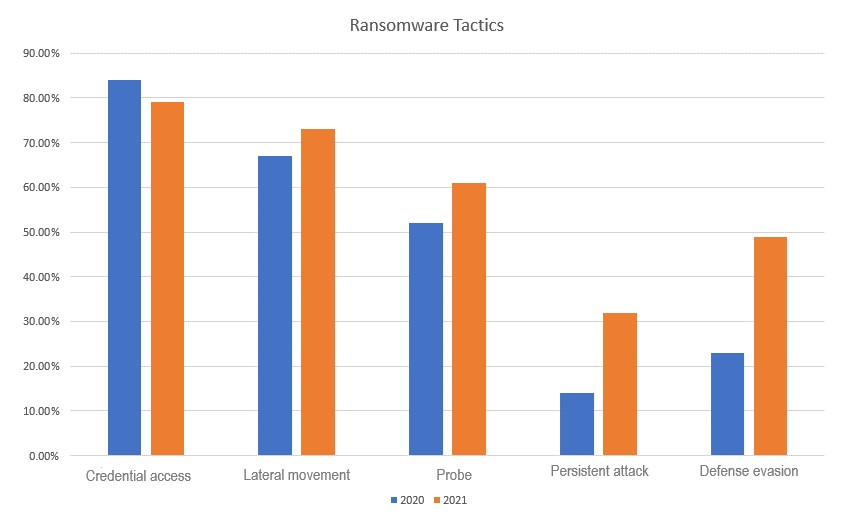
Through the observation of extortion events in 2021, it is found that the means of extortion attacks tend to be diversified and complicated. Techniques and tactics using ransomware include credential access, lateral movement, probe, persistent attack, defense evasion, etc. It should be noted that 49% of ransomware attacks have signs of defense evasion, indicating that today’s ransomware attacks are not limited to simple scanning and encrypting, but leveraging more sophisticated attack methods to expand the profits while being well concealed.
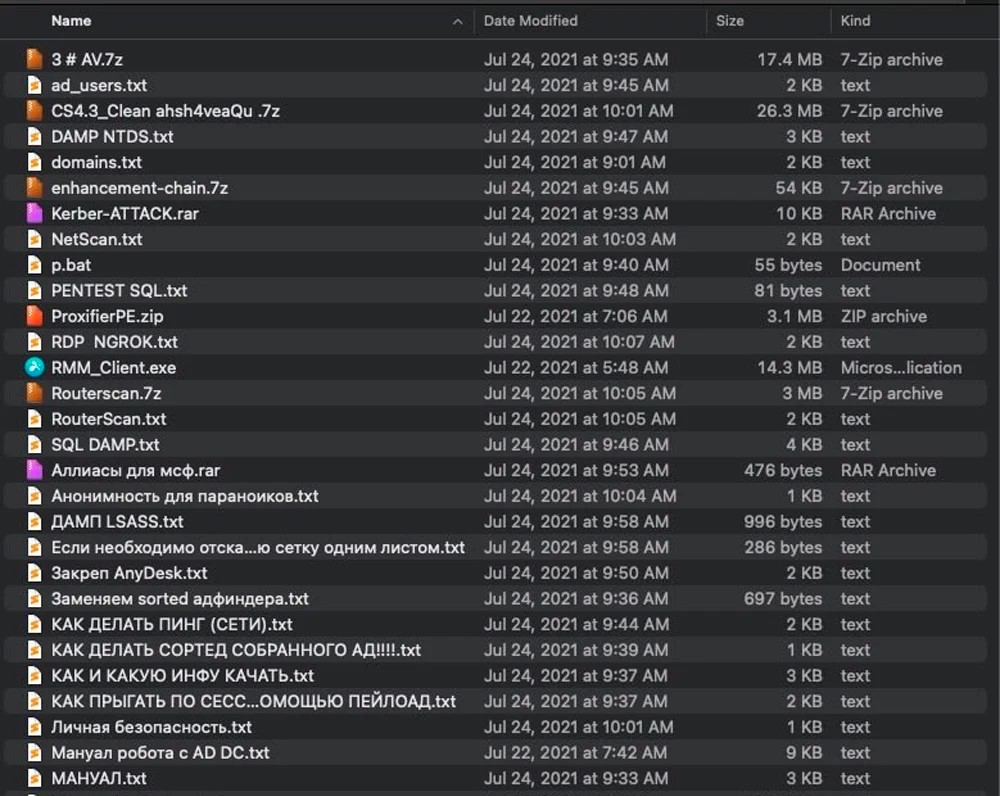
Conti ransomware operates on a ransomware-as-a-service (RaaS) model, with a core team responsible for managing malware and Tor sites, while recruited affiliates are responsible for breaching networks and encrypted devices. In August 2021, a member of the Conti ransomware affiliate leaked information about the ransomware gang ‘s attack information, including the IP address of a Command & Control Server and a 113Mb-size archive containing many tools and training materials for conducting ransomware attacks.
The content includes intranet scanning, privilege escalation, domain controller takeover, configuration and use of Cobalt Strike, data leakage by configuring Rclone and MEGA, AnyDesk configuration, tunnel usage, password dumping, disabling Windows Defender, etc. The manual also teaches in detail how to upload data and which data to choose to upload. The “standardized ” extortion teaching materials reflect the industrialized operation mode and weaponized offensive and defensive tactics used by threat actors in the underground economy today.